Vehicle Security: Risk Assessment in Transportation
Intelligent Transportation Systems (ITS) are critical infrastructure that are not immune to both physical and cyber threats. Vehicles are cyber/physical systems which are a core component of ITS, can be either a target or a launching point for an attack on the ITS network. Unknown vehicle security vulnerabilities trigger a race among adversaries to exploit the weaknesses and security experts to mitigate the vulnerability. In this study, we identified opportunities for adversaries to take control of the in-vehicle network, which can compromise the safety, privacy, reliability, efficiency, and security of the transportation system. This study contributes in three ways to the literature of ITS security and resiliency. First, we aggregate individual risks that are associated with hacking the in-vehicle network to determine system-level risk. Second, we employ a risk-based model to conduct a qualitative vulnerability-oriented risk assessment. Third, we identify the consequences of hacking the in-vehicle network through a risk-based approach, using an impact-likelihood matrix. The qualitative assessment communicates risk outcomes for policy analysis. The outcome of this study would be of interest and usefulness to policymakers and engineers concerned with the potential vulnerabilities of the critical infrastructures.
💡 Research Summary
The paper “Vehicle Security: Risk Assessment in Transportation” addresses the growing vulnerability of modern vehicles, which have evolved into complex cyber‑physical systems and now serve as both targets and launch pads for attacks on Intelligent Transportation Systems (ITS). Recognizing that statistical data on real‑world vehicle attacks are scarce, the authors adopt a qualitative, NIST SP 800‑30‑based risk assessment framework to evaluate threats, vulnerabilities, impacts, and likelihoods associated with in‑vehicle network compromises.
The authors first review a broad set of high‑profile hacking demonstrations, including the 2014 Jeep Cherokee remote exploit, Miller and Valsak’s attacks on Ford Escape, Toyota Prius, and the 2015 Tesla Model S sensor spoofing, as well as academic studies on CAN‑bus, OBD‑II, infotainment, Bluetooth, and telematics control units (TCU). From these cases they extract threat sources (e.g., skilled hackers, organized crime, insider actors) and threat events (physical access via OBD‑II, remote access through Wi‑Fi/Bluetooth, OTA update manipulation, CAN‑bus message injection).
Next, the paper catalogs vehicle vulnerabilities: the lack of authentication and encryption on CAN, the unrestricted nature of OBD‑II diagnostic ports, insecure firmware update mechanisms, over‑privileged third‑party apps in infotainment systems, and the exposure of vehicle‑to‑vehicle (V2V) and vehicle‑to‑infrastructure (V2I) communications. These are organized into a “vulnerability‑predisposing condition” matrix that distinguishes between physical and remote attack vectors.
Using the NIST risk model, the authors conduct a three‑step qualitative assessment: (1) identify threat sources and events, (2) identify system vulnerabilities and pre‑conditions, and (3) determine adverse impacts and magnitude. Impacts are classified into four domains—safety (brake/steering control), operations (engine, HVAC, dashboard), reliability (system availability), and security (privacy, data leakage). Each domain is rated as High, Medium, or Low for both impact and likelihood, producing a 4×4 impact‑likelihood matrix. The analysis reveals that remote CAN‑bus reprogramming and physical OBD‑II exploitation rank as the highest‑risk scenarios, combining high likelihood (due to readily available tools and expertise) with severe safety and operational impacts.
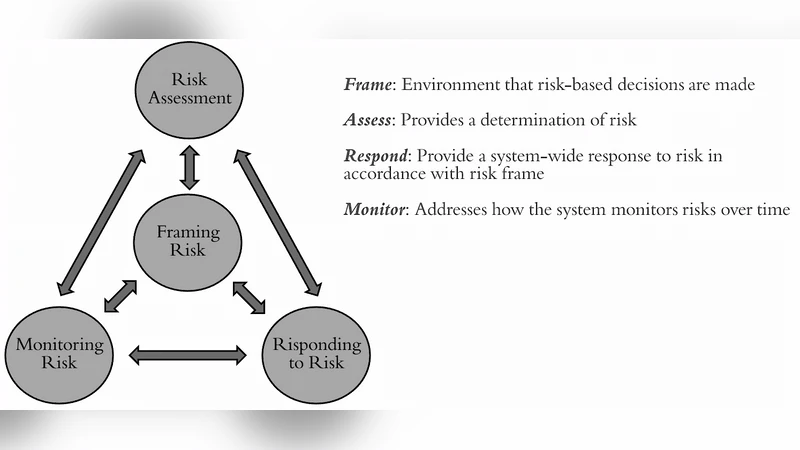
The study concludes with a risk‑management process comprising four stages: frame, assess, respond, and monitor. Recommendations include embedding security‑by‑design principles early in vehicle development, implementing authentication and encryption on in‑vehicle networks, deploying intrusion‑detection sensors, enforcing secure OTA update procedures, and conducting regular penetration testing and incident‑response drills. The authors also stress the need for continuous monitoring and policy‑level guidance, suggesting that qualitative risk outcomes be fed into simulation tools for policymakers to prioritize regulatory actions.
Overall, the paper contributes to ITS security literature by (1) aggregating individual vehicle‑network risks into a system‑level perspective, (2) applying a NIST‑based qualitative risk model suitable for contexts lacking quantitative data, and (3) presenting an impact‑likelihood matrix that clearly visualizes risk priorities for engineers and decision‑makers. It highlights the urgency of proactive, design‑time security measures to safeguard the safety, reliability, and resilience of the broader transportation infrastructure.
Comments & Academic Discussion
Loading comments...
Leave a Comment