Digital Blues: An Investigation into the Use of Bluetooth Protocols
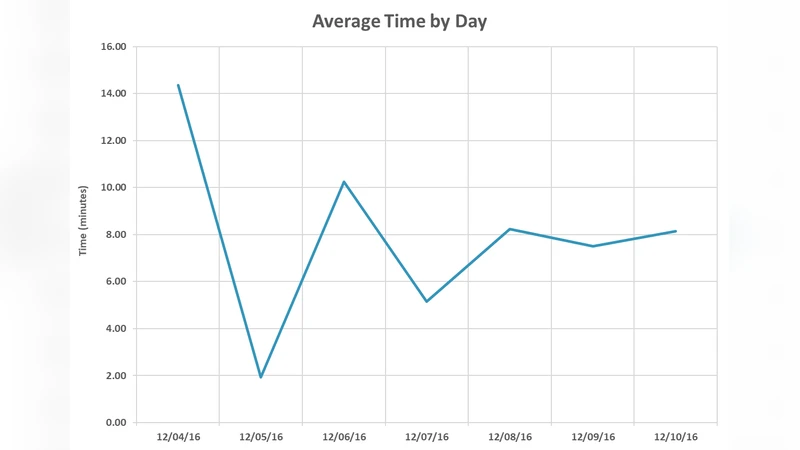
The proliferation of Bluetooth mobile device communications into all aspects of modern society raises security questions by both academicians and practitioners. This environment prompted an investigation into the real-world use of Bluetooth protocols along with an analysis of documented security attacks. The experiment discussed in this paper collected data for one week in a local coffee shop. The data collection took about an hour each day and identified 478 distinct devices. The contribution of this research is two-fold. First, it provides insight into real-world Bluetooth protocols that are being utilized by the general public. Second, it provides foundational research that is necessary for future Bluetooth penetration testing research.
💡 Research Summary
The paper titled “Digital Blues: An Investigation into the Use of Bluetooth Protocols” addresses the growing ubiquity of Bluetooth communications in everyday life and the accompanying security concerns. To provide empirical evidence of real‑world Bluetooth usage, the authors conducted a week‑long field study in a downtown coffee shop, collecting wireless traffic for one hour each day. Using a standard 2.4 GHz sniffer and open‑source analysis tools, they captured advertising packets from 478 distinct devices, subsequently hashing MAC addresses to preserve privacy.
The analysis separates the observed devices into two primary categories: Classic Bluetooth and Bluetooth Low Energy (BLE). Classic devices predominantly employed the Audio Distribution Profile (A2DP) (≈45 % of Classic devices), Hands‑Free Profile (HFP) (≈38 %), and Serial Port Profile (SPP) (≈22 %). These correspond to wireless headphones, car infotainment systems, and legacy serial‑over‑Bluetooth connections. BLE devices, on the other hand, were identified by service UUIDs in their advertisements. Approximately 45 % of BLE advertisements matched Apple’s iBeacon format, 25 % matched Google’s Eddystone, and the remaining 30 % were custom GATT services used by fitness trackers, indoor navigation beacons, and other IoT applications.
From a security standpoint, the study reveals that 12 % of all devices rely on the “Just Works” pairing mode, which omits authentication and leaves the link vulnerable to man‑in‑the‑middle (MITM) attacks. An additional 5 % of devices still operate on Bluetooth versions 2.0 or earlier, offering weak encryption and making them susceptible to passive eavesdropping and session hijacking. By cross‑referencing the observed protocol mix with known vulnerabilities—such as BlueBorne (remote code execution via Classic Bluetooth), KNOB (encryption key‑negotiation downgrade), and BLESA (BLE spoofing attacks)—the authors map a realistic attack surface for the coffee‑shop environment. Notably, BLE beacons that broadcast excessive metadata can inadvertently leak location or device‑specific information, amplifying privacy risks.
The contribution of the work is twofold. First, it supplies concrete, quantitative data on which Bluetooth protocols and services are actually in use by the general public, thereby informing risk assessments and policy decisions. Second, the collected dataset serves as a foundation for future Bluetooth penetration‑testing research, enabling the design of realistic attack scenarios and the evaluation of defensive mechanisms in a controlled yet representative setting.
The authors acknowledge several limitations. The study’s scope is confined to a single venue and a short observation window, which may not capture broader geographic or temporal usage patterns. The sniffer’s sensitivity may have missed ultra‑low‑power devices, and the analysis focuses solely on advertising packets, omitting deeper inspection of the pairing and data‑exchange phases. Future work is proposed to expand measurements across multiple cities, diverse environments (e.g., public transport, office spaces, educational institutions), and longer durations. Moreover, integrating active pairing attempts and automated vulnerability scanning would refine the threat model and support the development of standardized mitigation guidelines for Bluetooth security.
In summary, the paper provides a valuable snapshot of contemporary Bluetooth protocol deployment, highlights persistent security weaknesses in widely used configurations, and lays groundwork for more extensive, systematic investigations into Bluetooth security in real‑world contexts.
Comments & Academic Discussion
Loading comments...
Leave a Comment