ABE-Cities: An Attribute-Based Encryption System for Smart Cities
In the near future, a technological revolution will involve our cities, where a variety of smart services based on the Internet of Things will be developed to facilitate the needs of the citizens. Sensing devices are already being deployed in urban environments, and they will generate huge amounts of data. Such data are typically outsourced to some cloud storage because this lowers capital and operating expenses and guarantees high availability. However, cloud storage may have incentives to release stored data to unauthorized entities. In this work we present ABE-Cities, an encryption scheme for urban sensing which solves the above problems while ensuring fine-grained access control on data by means of Attribute-Based Encryption (ABE). Basically, ABE-Cities encrypts data before storing it in the cloud and provides users with keys able to decrypt only those portions of data the user is authorized to access. In ABE-Cities, the sensing devices perform only lightweight symmetric cryptography operations, thus they can also be resource-constrained. ABE-Cities provides planned expiration of keys, as well as their unplanned revocation. We propose methods to make the key revocation efficient, and we show by simulations the overall efficiency of ABE-Cities.
💡 Research Summary
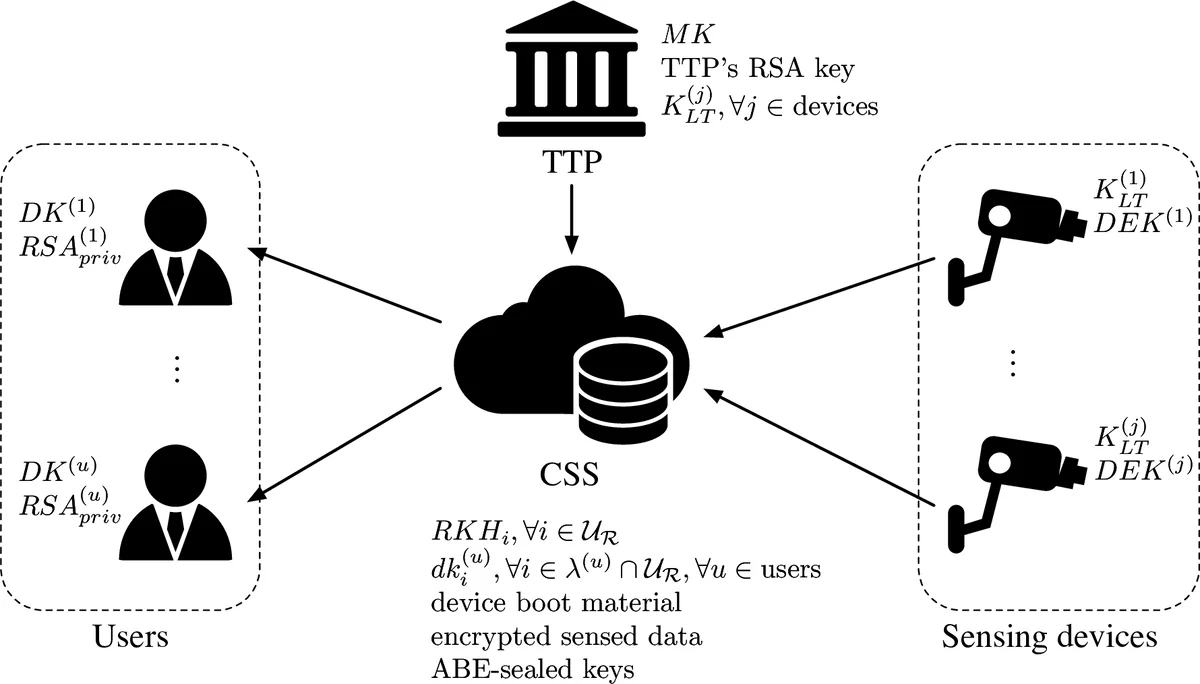
The paper introduces ABE‑Cities, a novel encryption framework designed to protect data generated by urban sensing devices in smart‑city environments while providing fine‑grained, attribute‑based access control. The authors observe that massive amounts of IoT data are increasingly outsourced to cloud storage services (CSS) for cost and availability reasons, but this introduces a trust problem: the cloud is typically modeled as “honest‑but‑curious” and may attempt to read stored information. To mitigate this risk, ABE‑Cities encrypts data before it reaches the cloud and uses a Key‑Policy Attribute‑Based Encryption (KP‑ABE) scheme to enforce who can decrypt which pieces of data.
Key architectural elements:
- Lightweight data producers – Sensors and other IoT devices only perform symmetric encryption (e.g., AES) on the raw measurements. The resulting ciphertext is tagged with a set of public attributes (location, time, sensor type, etc.) that describe the data. No pairing‑based or public‑key operations are required on the device, making the solution suitable for resource‑constrained hardware.
- Trusted Third Party (TTP) – Holds the ABE master key and generates user decryption keys. Each key embeds an access policy expressed as a monotonic Boolean formula (AND/OR tree) over attributes. The policy may also contain a “dummy” attribute that is never updated, preventing the cloud from reconstructing full decryption keys.
- Cloud‑side storage and proxy re‑encryption – Encrypted data are stored in the CSS. When a user’s key must be revoked (unplanned revocation), the system updates a subset of attributes to new versions. The TTP creates re‑encryption keys for those attributes and stores them in a version‑history list on the cloud. The cloud lazily re‑encrypts outdated ciphertext components only when a user requests them, applying the appropriate sequence of re‑encryption keys. This “lazy” approach keeps revocation overhead low.
- Segment‑tree representation of spatial/temporal intervals – To efficiently express policies such as “user may read data from zone 3‑7” the authors employ discrete segment trees. A point (e.g., a specific sensor ID or timestamp) is represented by a small set of tree nodes (O(log ρ)), and an interval is represented by another small set. The intersection test required by ABE is reduced to checking whether the point‑node set intersects the interval‑node set, which is also O(log ρ). This dramatically reduces the size of attribute sets for geographic or temporal policies.
Security analysis covers three adversary models: (i) an honest‑but‑curious cloud, (ii) external eavesdroppers or compromised devices, and (iii) colluding users attempting to combine keys. The paper proves that (i) the cloud never learns plaintext because it only sees ciphertext and re‑encryption keys; (ii) compromised devices cannot derive ABE keys because they never hold master or user keys; (iii) collusion is prevented by the inherent collusion‑resistance of KP‑ABE and by the dummy attribute that forces every user to retain a secret component unknown to the cloud.
Performance evaluation is carried out through simulations that vary the number of attributes, policy depth, and revocation frequency. Results show:
- Encryption at the device is dominated by symmetric operations, yielding latency well below 5 ms even on typical low‑power microcontrollers.
- Decryption time grows linearly with the number of attributes in the policy; for policies with up to 10 attributes, decryption remains under 50 ms on a standard laptop.
- Revocation overhead is logarithmic in the number of attribute versions thanks to the lazy proxy re‑encryption; the cloud performs at most a few modular exponentiations per request.
- Memory footprint of policies using segment trees is reduced by roughly 30 % compared with naïve attribute enumeration, because each interval is encoded with O(log ρ) nodes instead of ρ individual attributes.
The authors conclude that ABE‑Cities successfully balances three competing goals: (a) minimal computational load on constrained IoT devices, (b) expressive and fine‑grained access control, and (c) efficient, scalable key revocation. They suggest future work on hierarchical ABE extensions, multi‑authority TTPs, and real‑world pilot deployments in a city‑wide sensor network.
Comments & Academic Discussion
Loading comments...
Leave a Comment