Efficient and Secure Group Key Management in IoT using Multistage Interconnected PUF
Secure group-oriented communication is crucial to a wide range of applications in Internet of Things (IoT). Security problems related to group-oriented communications in IoT-based applications placed in a privacy-sensitive environment have become a major concern along with the development of the technology. Unfortunately, many IoT devices are designed to be portable and light-weight; thus, their functionalities, including security modules, are heavily constrained by the limited energy resources (e.g., battery capacity). To address these problems, we propose a group key management scheme based on a novel physically unclonable function (PUF) design: multistage interconnected PUF (MIPUF) to secure group communications in an energy-constrained environment. Our design is capable of performing key management tasks such as key distribution, key storage and rekeying securely and efficiently. We show that our design is secure against multiple attack methods and our experimental results show that our design saves 47.33% of energy globally comparing to state-of-the-art Elliptic-curve cryptography (ECC)-based key management scheme on average.
💡 Research Summary
The paper addresses the pressing need for secure and energy‑efficient group communication in the Internet of Things (IoT), where devices are typically constrained by limited battery capacity and modest computational resources. Traditional group key management solutions that rely on public‑key cryptography, such as elliptic‑curve cryptography (ECC), impose heavy computational loads and consequently high energy consumption, making them unsuitable for many low‑power IoT nodes. To overcome these limitations, the authors propose a novel physically unclonable function (PUF) architecture called the Multistage Interconnected PUF (MIPUF) and integrate it into a complete group key management protocol that covers key distribution, key storage, and rekeying.
MIPUF Architecture
MIPUF is built from two fundamental components: Processing Elements (PEs) and Switching Elements (SEs).
- Processing Elements (PEs) act as the core PUF blocks. Each PE consists of multiple strong PUF instances (the authors use arbiter PUFs for proof‑of‑concept) that accept an n‑bit challenge and produce an m‑bit response. By arranging several PUFs in parallel, a PE can generate a larger response space while preserving the inherent unclonability of the underlying PUFs.
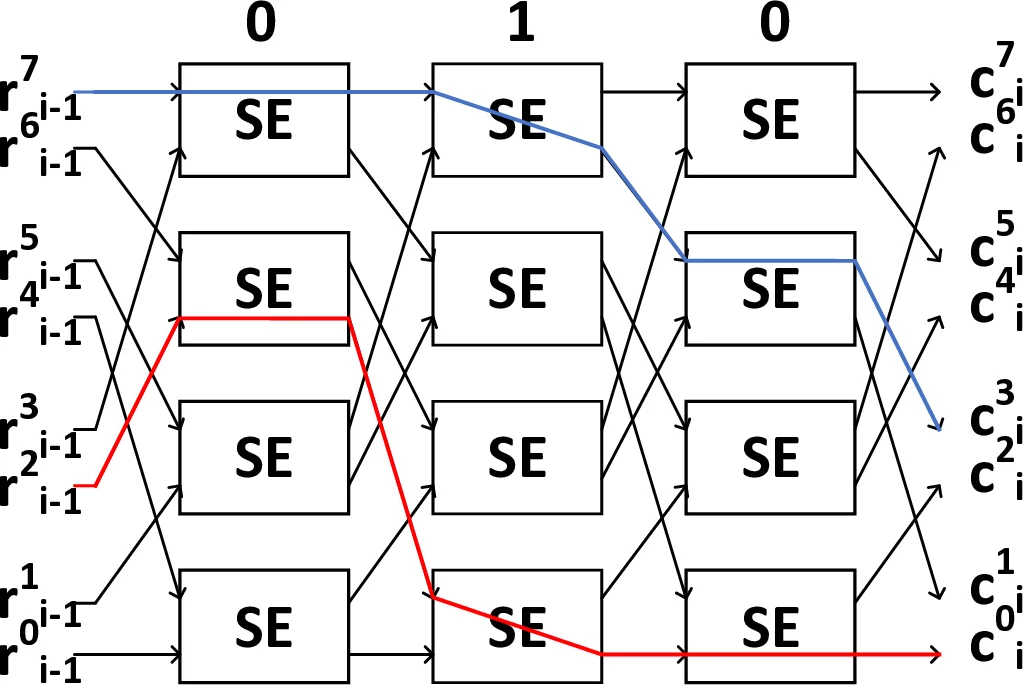
- Switching Elements (SEs) are implemented as 2×2 multiplexers arranged in a blocking Omega‑network style. SEs route the response of one PE to become the challenge of the next PE, according to a configuration vector. This vector is itself encrypted using earlier PUF nodes, ensuring that the true interconnection pattern remains hidden from an adversary. The blocking network provides O(N log N) wiring complexity for an N × N interconnection, offering a good trade‑off between configurability and hardware cost.
The multistage interconnection introduces non‑linearity and high system complexity, which dramatically hampers modeling attacks that attempt to predict PUF responses from observed challenge‑response pairs (CRPs). Moreover, the configuration vector can be changed frequently at negligible cost, allowing the system to “re‑program” its challenge‑response mapping on the fly.
Security Evaluation
Two key metrics are examined:
- Inter‑configuration variation (uniqueness) – measured as the Hamming distance between outputs generated under different interconnection configurations. Experiments on a Xilinx Spartan‑6 FPGA show an average variation of 47.9 %, close to the ideal 50 % and slightly better than conventional arbiter PUFs (≈47 %).
- Intra‑configuration variation (reliability) – measured as the Hamming distance when the same configuration and challenge are applied repeatedly. Without error correction, the variation is 35.37 %; after inserting a lightweight fuzzy extractor between each PE, the variation drops to 2.67 %, demonstrating that the system can reliably reproduce the same key despite temperature and voltage fluctuations (20 °C–65 °C, 0.95 V–1.2 V).
Modeling resistance is quantified using logistic regression, evolutionary strategies, and deep learning attacks, each trained on 100 k CRPs. For a 4‑node MIPUF, the best single‑bit prediction accuracy hovers around 50.6 %, essentially random, whereas comparable architectures (e.g., 1024‑bit arbiter PUF) achieve 96 %+ accuracy. The authors attribute this robustness to the broken linearity and the frequent re‑configuration capability.
Group Key Management Protocol
The protocol assumes a relatively powerful control unit and many lightweight IoT nodes, each equipped with an MIPUF, a hardware hash function, and a compact AES engine. It proceeds in three phases:
-
Key Distribution – The control unit sends two messages per node. The node’s MIPUF, seeded with a device‑specific challenge and a secret interconnection configuration, generates the group key on the fly. The key is never stored in clear memory; instead, a “key hint” (π_i) and encrypted configuration data (c_γi, f_i) are stored securely.
-
Key Storage – When a node needs to encrypt or decrypt group traffic, it reconstructs the group key by feeding the stored hint and configuration back into its MIPUF. Because the key never resides persistently, an attacker who compromises the node’s non‑volatile memory still cannot obtain the actual group key without also compromising the PUF hardware.
-
Rekeying – Upon membership changes (join/leave) or periodic renewal, the control unit issues a new configuration vector and/or challenge, causing each node’s MIPUF to produce a fresh group key. The old key instantly becomes obsolete, providing forward secrecy (leaving members cannot decrypt future messages) and backward secrecy (new members cannot decrypt past messages). Rekeying incurs only the cost of transmitting the new configuration, which is lightweight compared to re‑executing heavy ECC operations.
Energy Efficiency
Simulation results compare the proposed MIPUF‑based scheme against a state‑of‑the‑art ECC‑based group key management solution. Across the full lifecycle (distribution, storage, rekeying), the MIPUF approach consumes on average 47.33 % less energy. The savings stem from eliminating expensive elliptic‑curve point multiplications, relying instead on hardware‑native PUF evaluations, a lightweight fuzzy extractor, and a minimal AES block cipher.
Conclusions and Future Work
The authors demonstrate that a carefully designed multistage PUF can serve as a versatile, low‑power cryptographic primitive capable of handling the entire group key management process in constrained IoT environments. The architecture offers strong resistance to modeling attacks, high uniqueness, and acceptable reliability after modest error correction. Energy measurements indicate a substantial reduction compared with conventional public‑key schemes. Future research directions include: (i) integrating stronger strong‑PUF designs such as LRR‑DPUF to further improve modeling resistance; (ii) fabricating a full hardware prototype to validate the reported energy savings under real‑world workloads; and (iii) extending the protocol to support large‑scale dynamic groups with hierarchical key structures.
Comments & Academic Discussion
Loading comments...
Leave a Comment