A Survey of Machine and Deep Learning Methods for Internet of Things (IoT) Security
The Internet of Things (IoT) integrates billions of smart devices that can communicate with one another with minimal human intervention. It is one of the fastest developing fields in the history of computing, with an estimated 50 billion devices by the end of 2020. On the one hand, IoT play a crucial role in enhancing several real-life smart applications that can improve life quality. On the other hand, the crosscutting nature of IoT systems and the multidisciplinary components involved in the deployment of such systems introduced new security challenges. Implementing security measures, such as encryption, authentication, access control, network security and application security, for IoT devices and their inherent vulnerabilities is ineffective. Therefore, existing security methods should be enhanced to secure the IoT system effectively. Machine learning and deep learning (ML/DL) have advanced considerably over the last few years, and machine intelligence has transitioned from laboratory curiosity to practical machinery in several important applications. Consequently, ML/DL methods are important in transforming the security of IoT systems from merely facilitating secure communication between devices to security-based intelligence systems. The goal of this work is to provide a comprehensive survey of ML /DL methods that can be used to develop enhanced security methods for IoT systems. IoT security threats that are related to inherent or newly introduced threats are presented, and various potential IoT system attack surfaces and the possible threats related to each surface are discussed. We then thoroughly review ML/DL methods for IoT security and present the opportunities, advantages and shortcomings of each method. We discuss the opportunities and challenges involved in applying ML/DL to IoT security. These opportunities and challenges can serve as potential future research directions.
💡 Research Summary
The surveyed paper provides a comprehensive overview of how machine learning (ML) and deep learning (DL) techniques can be employed to enhance security in the rapidly expanding Internet of Things (IoT) ecosystem. Beginning with an introduction that highlights the massive scale of IoT—projected to reach tens of billions of devices—and its integration into smart homes, cities, and industrial automation, the authors point out that traditional security mechanisms such as encryption, authentication, and access control are insufficient due to the heterogeneous, resource‑constrained, and highly interconnected nature of IoT devices.
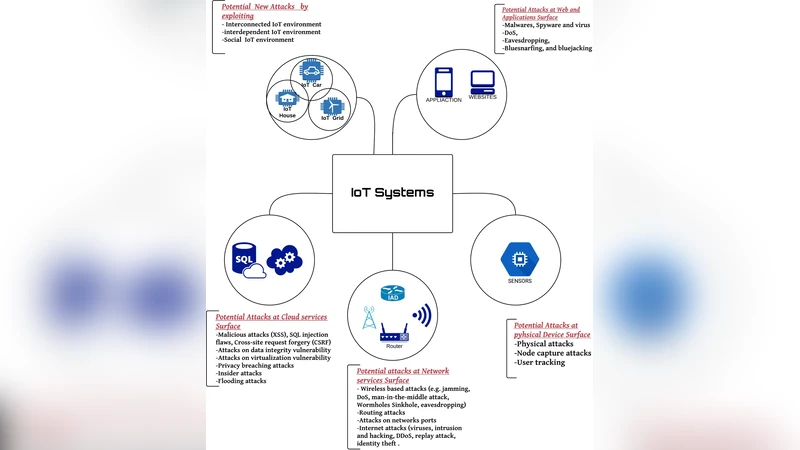
The authors then present a systematic taxonomy of IoT attack surfaces, dividing the architecture into four primary layers: physical, network, service, and cloud. For each layer they enumerate representative threats: hardware tampering, firmware injection, and side‑channel attacks at the physical level; packet sniffing, man‑in‑the‑middle, and distributed denial‑of‑service attacks on the network; vulnerable APIs, malicious applications, and data manipulation in the service tier; and data exfiltration, privilege escalation, and multi‑tenant breaches in the cloud. This layered view underscores that attacks often span multiple layers, creating complex, multi‑vector scenarios.
The core of the survey is a detailed classification of ML/DL‑based security solutions. Supervised learning methods—support vector machines, random forests, gradient‑boosted trees, and similar classifiers—are described as effective when ample labeled data exist, delivering high detection accuracy with relatively low inference latency. Unsupervised approaches, including clustering (K‑means, DBSCAN), isolation forests, and autoencoders, are highlighted for anomaly detection in environments where labeling is expensive or impossible. Reinforcement learning is discussed as a means to develop adaptive defense policies that react to evolving attacker behavior, modeled as Markov decision processes.
Deep learning architectures receive particular attention. Convolutional neural networks (CNNs) are applied to transformed packet sequences or traffic “images” to capture spatial patterns, while recurrent networks (RNNs, LSTMs) and Transformers model temporal dependencies in traffic logs. Graph neural networks (GNNs) are introduced for representing the IoT topology as a graph, enabling detection of sophisticated lateral movement and multi‑hop attacks. Generative adversarial networks (GANs) are used both to synthesize realistic attack traffic for training and to evaluate model robustness against adversarial examples.
Given the severe computational, memory, and power constraints of many IoT nodes, the paper surveys model‑compression techniques—pruning, quantization, knowledge distillation—and hardware acceleration strategies (FPGA, ASIC) that enable on‑device inference. A hybrid edge‑cloud deployment model is advocated: lightweight detection runs on edge gateways for real‑time response, while deeper analytics and model updates are performed in the cloud.
Data challenges are also examined. The authors note the prevalence of class imbalance (few attack samples versus abundant benign traffic) and the high cost of manual labeling. They discuss data‑augmentation, semi‑supervised learning, transfer learning, and synthetic data generation as ways to mitigate these issues. Public datasets such as N‑BaIoT, IoT‑23, and UNSW‑NB15 are reviewed, with a critique that they often fail to capture the diversity and noise of real‑world deployments.
The survey further addresses two critical research gaps: explainability and adversarial robustness. Explainable AI (XAI) techniques are deemed essential for operators to trust and act upon model decisions, while adversarial training, defensive distillation, and robust architecture design are recommended to protect against crafted inputs that could fool detection systems.
Finally, the authors outline future research directions: (1) designing unified frameworks that jointly optimize model lightweightness, privacy preservation (e.g., federated learning), and detection performance; (2) developing multimodal models that fuse network traffic, sensor readings, and system logs; (3) implementing continual learning mechanisms that adapt to evolving threats without catastrophic forgetting; and (4) establishing standardized benchmarks, metrics, and evaluation protocols to enable fair comparison across studies.
In summary, the paper serves as a valuable roadmap for researchers and practitioners seeking to integrate ML/DL into IoT security, offering a balanced view of current capabilities, practical constraints, and open challenges that must be addressed to achieve resilient, intelligent protection for the next generation of connected devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment