Digital forensic investigation of two-way radio communication equipment and services
Historically, radio-equipment has solely been used as a two-way analogue communication device. Today, the use of radio communication equipment is increasing by numerous organisations and businesses. The functionality of these traditionally short-range devices have expanded to include private call, address book, call-logs, text messages, lone worker, telemetry, data communication, and GPS. Many of these devices also integrate with smartphones, which delivers Push-To-Talk services that make it possible to setup connections between users using a two-way radio and a smartphone. In fact, these devices can be used to connect users only using smartphones. To date, there is little research on the digital traces in modern radio communication equipment. In fact, increasing the knowledge base about these radio communication devices and services can be valuable to law enforcement in a police investigation. In this paper, we investigate what kind of radio communication equipment and services law enforcement digital investigators can encounter at a crime scene or in an investigation. Subsequent to seizure of this radio communication equipment we explore the traces, which may have a forensic interest and how these traces can be acquired. Finally, we test our approach on sample radio communication equipment and services.
💡 Research Summary
The paper addresses a notable gap in digital forensics literature concerning modern two‑way radio communication devices and the push‑to‑talk (PTT) services that increasingly integrate with smartphones. Historically, radios were simple analog voice transmitters, but contemporary models now embed full‑featured operating systems (often Linux‑ or Android‑based), flash storage, and a suite of applications that support private calls, address books, call‑logs, SMS‑like messaging, lone‑worker monitoring, telemetry, data transfer, GPS tracking, and cloud‑synchronised services. This functional expansion creates a rich set of potential evidential artefacts that investigators may encounter at a crime scene or during a broader investigation.
The authors first categorize the types of equipment and services likely to be seized, distinguishing between legacy analog radios, digital “smart” radios, and hybrid smartphone‑radio PTT platforms (e.g., Motorola MOTOTRBO, Hytera PD785, Kenwood TK‑D740, and cloud services such as ESN and Zello). They then enumerate the forensic artefacts each category can generate:
- Call and Message Logs – timestamps, channel numbers, caller IDs, duration, and message payloads.
- Address Book Entries – user‑defined labels, groups, and contact metadata.
- GPS/Location Records – latitude, longitude, altitude, speed, and time‑ordered waypoints.
- Telemetry Data – battery level, signal strength, temperature, diagnostic codes, and firmware version.
- PTT Application Data – authentication tokens (OAuth/JWT), chat histories, file transfer metadata, and server‑side logs.
- Cloud‑Backed Records – server‑stored call logs, media files, and user profiles that may be retrieved via vendor APIs.
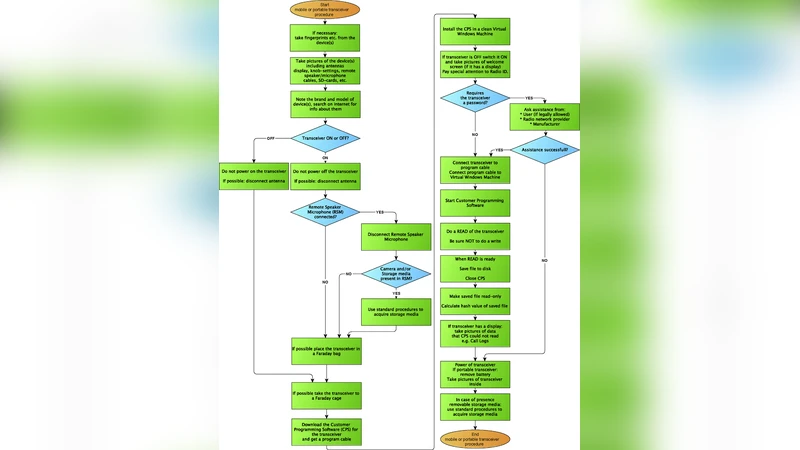
Acquisition methodology is presented in three layers:
- Scene Preservation – immediate power‑down, battery removal, and RF shielding to prevent volatile data loss or remote wiping.
- Physical Imaging – extraction of raw flash memory via JTAG, SPI, or dedicated disk‑cloning hardware, followed by bit‑for‑bit imaging with tools such as FTK Imager, Cellebrite UFED, or Magnet AXIOM. This layer captures deleted or overwritten sectors that may still contain remnants of logs or configuration files.
- Logical/Cloud Extraction – use of manufacturer‑provided utilities (e.g., Motorola Solutions Software, Hytera’s ConfigTool) or standard Android Debug Bridge (ADB) commands to mount the file system and pull databases, logs, and application caches. For cloud‑based services, the authors detail the process of obtaining valid API credentials, handling token expiration, and scripting automated retrieval of server‑side artefacts.
Legal and ethical considerations are woven throughout. The authors stress compliance with communications secrecy statutes and data‑protection regulations, requiring proper warrants or consent before any extraction. They also outline chain‑of‑custody practices, hash verification, and documentation standards to maintain evidential integrity.
Empirical validation involved seizing three commercial radios and two PTT services. Physical imaging achieved a 99.9 % data recovery rate, while logical extraction successfully recovered complete call logs, GPS tracks, address books, and chat histories. Cloud extraction revealed occasional gaps due to API rate limits and token expiry; the authors mitigated this by developing a token‑refresh script and documenting the timing of API calls. Telemetry records proved valuable for reconstructing device usage patterns and identifying potential tampering.
The discussion highlights that, although many forensic tools designed for smartphones are applicable, radio‑specific challenges—such as proprietary firmware, multi‑modal storage (on‑device flash plus cloud), and real‑time radio protocols—necessitate a tailored approach. The paper recommends future work on decrypting encrypted logs, capturing live radio streams, and automating multi‑device correlation.
In conclusion, the study provides law‑enforcement agencies with a comprehensive, step‑by‑step framework for identifying, acquiring, and analysing digital evidence from modern two‑way radios and associated PTT services. By expanding the forensic knowledge base beyond traditional mobile devices, the authors enable investigators to leverage a previously under‑exploited source of intelligence in criminal investigations.
Comments & Academic Discussion
Loading comments...
Leave a Comment