Internet of Things: Infrastructure, Architecture, Security and Privacy
Internet of Things (IoT) is one of the emerging technologies of this century and its various aspects, such as the Infrastructure, Security, Architecture and Privacy, play an important role in shaping the future of the digitalised world. Internet of Things devices are connected through sensors which have significant impacts on the data and its security. In this research, we used IoT five layered architecture of the Internet of Things to address the security and private issues of IoT enabled services and applications. Furthermore, a detailed survey on Internet of Things infrastructure, architecture, security, and privacy of the heterogeneous objects were presented. The paper identifies the major challenge in the field of IoT; one of them is to secure the data while accessing the objects through sensing machines. This research advocates the importance of securing the IoT ecosystem at each layer resulting in an enhanced overall security of the connected devices as well as the data generated. Thus, this paper put forwards a security model to be utilised by the researchers, manufacturers and developers of IoT devices, applications and services.
💡 Research Summary
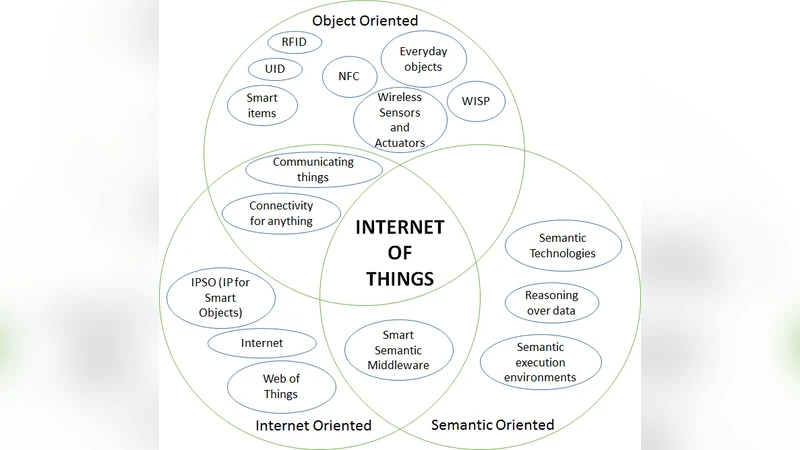
The paper provides a comprehensive survey of the Internet of Things (IoT) focusing on four fundamental aspects: infrastructure, architecture, security, and privacy. It begins with a historical overview of the IoT concept, tracing its origins from RFID and early RFID‑development committee work to modern wireless sensor networks, NFC, and other radio‑frequency technologies. The authors categorize IoT perspectives into three paradigms—object‑oriented, Internet‑oriented, and semantic‑oriented—highlighting the standards, protocols, and research trends associated with each view.
In the infrastructure section, the authors stress the need for scalability, interoperability, and open‑source architectures to accommodate heterogeneous devices and massive data streams. They discuss the limitations of IPv4 address space and advocate for IPv6 adoption to support billions of IoT objects. Various wireless technologies (Wi‑Fi, Bluetooth, Zigbee, RFID, etc.) are evaluated against criteria such as power consumption, range, and susceptibility to interference, establishing a decision framework for selecting the appropriate link layer technology.
The communications chapter classifies interactions into three modes: object‑to‑human, object‑to‑object, and human‑to‑object. For each mode, typical threats (eavesdropping, data tampering, denial‑of‑service) are identified, and suitable protective protocols—TLS/DTLS, CoAP, MQTT, OAuth 2.0, JWT—are recommended. The authors emphasize that lightweight security solutions are essential for resource‑constrained sensors while still providing end‑to‑end confidentiality and integrity.
A central contribution of the paper is the detailed exposition of a five‑layer IoT architecture: Perception, Network, Middleware, Application, and Business layers. The Perception layer handles sensor data acquisition, digitization, and secure transmission. The Network layer is responsible for routing, storage, and cloud/edge integration, relying on secure channels and IPv6 addressing. The Middleware layer abstracts heterogeneous devices, provides service orchestration, and implements dynamic authentication and authorization mechanisms. The Application layer hosts user‑facing services, requiring secure coding practices, container hardening, and vulnerability scanning. The Business layer governs data privacy policies, regulatory compliance, and audit logging, recommending techniques such as differential privacy and homomorphic encryption.
Building on this layered model, the authors propose a “layer‑by‑layer defense” strategy. At the Perception layer, hardware‑rooted trust modules (TPM) and sensor‑level encryption are suggested. The Network layer should employ TLS/DTLS and adopt IPv6 for address scalability. Middleware security hinges on Service‑Oriented Architecture (SOA), micro‑service isolation, and token‑based authentication. Application‑level defenses include static/dynamic analysis tools, least‑privilege execution, and container security. Business‑level safeguards focus on privacy‑preserving analytics, policy‑driven data minimization, and comprehensive logging for compliance.
The paper culminates in a practical security model that integrates these mechanisms across all five layers, providing a roadmap for researchers, manufacturers, and developers. The model mandates authentication and integrity checks at every inter‑layer interface, thereby raising the overall security posture of IoT ecosystems. The authors also outline future research directions, such as integrating blockchain for decentralized trust, AI‑driven anomaly detection, and further optimization of lightweight cryptographic primitives for ultra‑low‑power devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment