An Image Encryption Algorithm Based on Chaotic Maps and Discrete Linear Chirp Transform
In this paper, a novel image encryption algorithm, which involves a chaotic block image scrambling followed by a two-dimensional (2-D) discrete linear chirp transform, is proposed. The definition of the 2-D discrete linear chirp transform is introduc…
Authors: Osama A. S. Alkishriwo
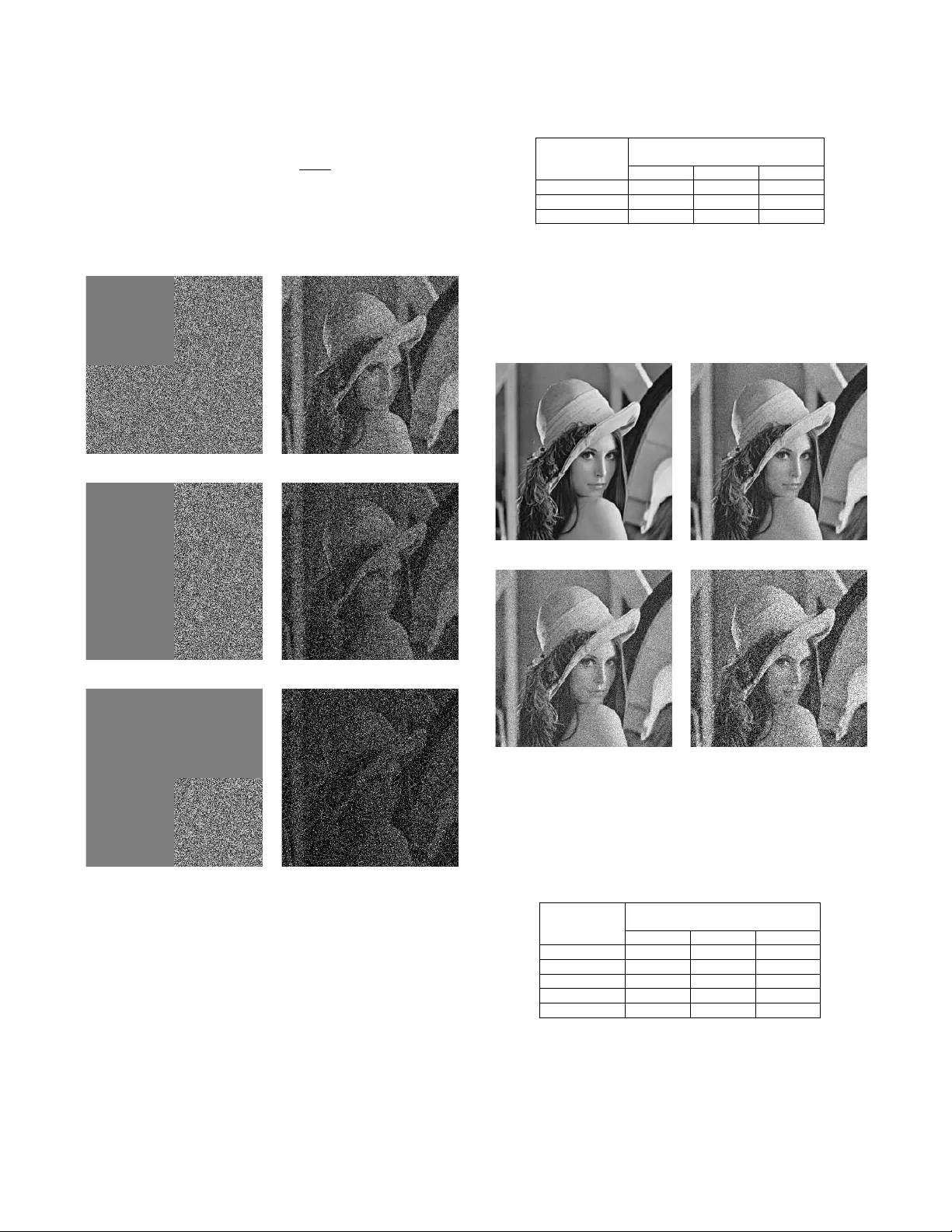
ALMAD AR JOURNAL FOR COMMUNICA TIONS, INFORMA TION TECHNOLOGY , AND APPLICA TIONS 1 An Image Encryption Algorithm Based on Chaotic Maps and Discrete Linear Chirp T ransform Osama A S Alkishriwo 1 Abstract —In this paper , a novel image encryption algorithm, which in volv es a chaotic block image scrambling follo wed by a two–dimensional (2D) discrete linear chirp transform, is pro- posed. The definition of the 2D discrete linear chirp transform is introduced and then it is used to construct the basis of the novel encryption algorithm. Finally , security analysis are performed to show the quality of the encryption pr ocess using differ ent metrics. Index T erms —Image encryption, Chaotic logistic map, Discrete linear chirp transform. I . I N T RO D U C T I O N W ith the rapid development of digital technologies and Internet, information security including image encryp- tion has become more and more important. The traditional encryption algorithms such as data encryption standard (DES), advanced encryption standard (AES), and public ke y encryp- tion algorithm (RSA) are not suitable for image encryption because the digital image has intrinsic properties such as bulk data capacities, high redundancy , and strong correlation between the adjacent pixels [1], [2]. Therefore, many en- cryption methods relying on dif ferent approaches hav e been introduced in literature to fulfil the security requirements of digital images. Among these approaches, encryption algo- rithms based on spatial domain [3], [4], frequency domain [6], [7], and fractional domain [8] hav e been proposed for encryption algorithm design. In spatial domain methods, the encryption algorithm works on the pix els of plain image directly , while the frequency domain schemes act on the coefficients of the transformed image which can be attained using transformation tools such as fast Fourier transform (FFT), discrete cosine transform (DCT), and discrete wav elet transform (DWT). On the other hand, the fractional domain approaches can giv e greater complexity to the system by gi ving an extra parameter of the transform order , which enlarges the key space resulting in a better and secure data protection as compared to the spatial and frequency domain methods. The most widely in vestig ated fractional transform is the fractional Fourier transform, which has a well established continuous–time version and also se veral definitions in the discrete–time frame work. In recent years, many different fractional Fourier trans- form encryption schemes hav e been proposed. In [9], Zhu et al. proposed an optical image encryption method based on multi–fractional Fourier transforms (MFRFT). Pei and Hsue Osama A S Alkishriwo is a lecturer with the Department of Electri- cal and Electronic Engineering, University of Tripoli, Libya, Email: alk- ishriew o@yahoo.com presented an image encryption method based on multiple– parameter discrete fractional Fourier transform (MPDFRFT) [10]. In [11], Liu et al. introduced a random fractional Fourier transform (RFRFT) by using random phase modulations. The results in [12] have shown that these image encryption schemes had deficiencies. Therefore, many encryption algo- rithms based on the FrFT were suggested to enhance security [13]–[16], [18], [19]. In this paper , the definition of the 2D discrete linear chirp transform (2D-DLCT) is proposed and an image encryption scheme based on such transform is introduced. The 2D-DLCT is an extension to the 1D discrete linear chirp transform giv en in [20], which has an excellent property in a sense that the chirp rate parameter ideally can have infinity support such that −∞ < β < + ∞ compared to the support of the fractional order of the fractional Fourier transform 0 ≤ α ≤ π/ 2 . In the proposed encryption scheme, the plain image is scrambled using chaotic logistic map which has three secret keys. The scrambled image is 2D-DLCT transformed using β x and β y chirp rates. These chirp rates serves as a secret keys as well. Then the transformed image is scrambled using different logistic map with another set of secret keys. Numerical results show the proposed scheme can be infeasible to the brute–force attack, more secure, and can resist noise and occlusion attacks. The remainder of this paper is organized as follows. In sec- tion II, the definition of the 2D discrete Linear chirp transform is introduced. Section III presents the details of the proposed image encryption scheme. Section IV gives the numerical simulations and results to demonstrate the performance and verify the v alidity of the proposed scheme. The conclusion is drawn and stated in section V . I I . 2 D D I S C R E T E L I N E A R C H I R P T R A N S F O R M ( 2 D - D L C T ) Let x ( n, m ) be a two–dimensional discrete signal, where n = 0 , 1 , · · · , N − 1 and m = 0 , 1 , · · · , M − 1 . The two–dimensional discrete linear chirp transform of the signal x ( n, m ) with chirp rates β x for the x–axis and β y for the y–axis is defined as X ( k , ` ) = N − 1 X n =0 M − 1 X m =0 x ( n, m ) K β x ,β y ( n, m, k , ` ) (1) with the kernel K β x ,β y ( n, m, k , ` ) = K β x ( n, k ) K β y ( m, ` ) (2) 2 ALMAD AR JOURNAL FOR COMMUNICA TIONS, INFORMA TION TECHNOLOGY , AND APPLICA TIONS where, K β x ( n, k ) = exp − 2 π N ( k n + β x n 2 ) (3) and K β y ( m, ` ) = exp − 2 π M ( ` m + β y m 2 ) (4) The chirp rates β x and β y are real numbers which can take any v alue from their support −∞ < β x , β y < ∞ . The 2D- DLCT can be e xpressed as a tensor product of two one– dimensional transforms. The in verse 2D-DLCT is obtained using the follo wing mathematical expression x ( n, m ) = N − 1 X k =0 M − 1 X ` =0 X ( k , ` ) K ∗ β x ,β y ( n, m, k , ` ) (5) where 0 ≤ k ≤ N − 1 , 0 ≤ ` ≤ M − 1 , and ( ∗ ) denotes the conjugate. I I I . T H E P R O P O S E D E N C RY P T I O N A N D D E C RY P T I O N A L G O R I T H M The proposed image encryption scheme is illustrated in Fig. 1(a). It employs the 2D-DLCT de vel oped in Section II and additional strategies such as pixel rearrangement in the spatial and chirp rate domains using the well known chaotic logistic maps. The logistic map is a one–dimensional nonlinear chaos function and is defined as [3] x i +1 = µx i (1 − x i ) (6) where µ is the system parameter sometimes known as bifur- cation parameter and x i (0 , 1) is the sequence value. When 3 . 5699456 ≤ µ ≤ 4 , slight variations in the initial value yield dramatically dif ferent results over time. That is to say , logistic map will operate in chaotic state. W ith x 0 being the initial value, a non–periodic sequence { x i ; i = 0 , 1 , 2 , 3 , · · · } sensitiv e to the initial value is generated. Ke y 1 0 , 1 , 1 P lain I m a g e C h ao tic Scr a m b li n g 2D - D L C T Ke y 3 0 , 2 , 2 Ke y 2 , C h ao tic Scr a m b li n g E n cr y p ted I m a g e ( a) Ke y 3 0 , 2 , 2 E n cr y p ted I m a g e C h ao tic Scr a m b li n g 2D - I DL C T Ke y 1 0 , 1 , 1 Ke y 2 , C h ao tic Scr a m b li n g P lain I m a g e ( b ) Fig. 1: Schematic diagram of the proposed algorithm: (a) Encryption process, (b) Decryption process. W ithout loss of generality , the size of the plain image I is an N × M and the encryption procedure is described as follows: • Setting the initial v alues of the chaotic system by means of the plain image I to increase the relationship between the encryption scheme and the plain image. • Given the initial parameter x 0 and µ 1 , generate a random sequence x = { x 1 , x 2 , · · · , x L } , where L > N × M , and discard the first p 1 values. A new sequence v = { v 1+ p 1 , v 2+ p 2 , · · · , v N M + p 1 } is obtained. The parame- ters x 0 , µ 1 , and p 1 serve as a first priv ate ke y (ke y 1 ). • Sort the sequence v in ascending order or descending order to form a ne w sequence. Thus, the positions of the elements are varied and the positions are recorded as I X . • Reshape the plain image I N × M into a vector S N M × 1 , and then use the scrambling index I X to reorder the items of the vector S . The scrambled image in the spatial domain can be obtained by recon verting S into an N × M matrix E . • Choose two real numbers for β x and β y , which serve as a second priv ate key (ke y 2 ), and employ them to transform the image E using 2D-DLCT . • Scramble the attained matrix as explained in the pre vious steps using different set of initial values, that is y 0 , µ 2 , and p 2 which represent the third pri v ate key (key 3 ). • Finally , the encrypted image is obtained by conv erting the scrambled vector into an N × M matrix Y . The decryption algorithm is the in verse operation of the encryption as sho wn in Fig. 1(b). I V . S I M U L AT I O N R E S U L T S A N D S E C U R I T Y A N A L Y S I S In the simulations, a standard Lena test image of size 256 × 256 [21] that has allocation of 8 bits/pixel of gray–scale is used. The parameters of the chaotic logistic map and the chirp rates of the 2D-DLCT which employed in the simulation experiments are listed in T able I. T ABLE I: Simulation parameters. Parameter V alue x 0 0 . 31 µ 1 3 . 8 p 1 mod ( P i,j I ij , 9999) y 0 0 . 25 µ 2 3 . 7 p 2 mod ( P i,j I ij , 9990) β x 1 . 5 β y − 3 . 5 Figures 2(a), (b), and (c) show the plain image, encrypted image, and decrypted image, respectiv ely . In the following subsections, the security analysis of the proposed encryption scheme is performed to check its resistance to v arious attacks. A. K e y Space Analysis Ke y space size is the total number of different keys that can be used in an encryption algorithm. In a cryptographic system, the key space should be sufficiently large to make brute–force attack infeasible. The proposed encryption algorithm have the following secret keys: key 1 = { x 0 , µ 1 , p 1 } , key 2 = { β x , β y } , and key 3 = { y 0 , µ 2 , p 2 } and their corresponding spaces are ALMAD AR JOURNAL FOR COMMUNICA TIONS, INFORMA TION TECHNOLOGY , AND APPLICA TIONS 3 (a) (b) (c) Fig. 2: Encryption and decryption results. (a) Plain image. (b) Encrypted image. (c) Decrypted image. s 1 , s 2 , s 3 , s 4 , s 5 , s 6 , s 7 , and s 8 , respecti vely . These keys are independent from each other . Thus the total ke y space of the encryption scheme can be computed as s > Y i s i (7) If we assume the computation precision of the computer is 10 − 14 , then the ke y space is about 10 74 ≈ 2 245 . Such a large key space can ensure a high security against brute–force attacks [22]. B. K e y Sensitivity Analysis A good encryption scheme should be sensitive to each secret ke y . In other words, a small change on the key must be able to cause a great change on the encrypted image. In order to ev aluate the ke y sensitivity of the proposed algorithm, the mean square error (MSE) between the plain image and decrypted image is calculated as follo ws MSE = 1 N × M N X i =1 M X j =1 | I ( i, j ) − D ( i, j ) | 2 (8) where I ( i, j ) is the plain image and D ( i, j ) denotes the corresponding decrypted image. T o determine the sensitivity of the key parameters, the decryption procedure is processed by v arying one parameter while the others held constant. Figures 3(a), (b), (c), and (d) show the MSE versus devi- ation of the k ey encryption parameters β x , x 0 , µ 1 , and p 1 , respectiv ely . Since the MSE increases sharply when the the key parameters depart from its correct value and it is equal to zero when the image is decrypted with correct decryption parameters, a small change to the keys can lead to different decrypted image ha ving no connection with the original image. It should be noted that we omit the sensiti vity analysis of the remaining key parameters y 0 , µ 2 , and p 2 because they give similar results to those shown with the key parameters x 0 , µ 1 , and p 1 . −8 −6 −4 −2 0 2 4 6 8 x 10 −3 0 20 40 60 80 100 120 140 160 180 200 Deviation from the key β x ( δ x ) Mean Square Error (MSE) (a) −8 −6 −4 −2 0 2 4 6 8 x 10 −15 0 20 40 60 80 100 120 Deviation from initial value x 0 ( δ x 0 ) Mean Square Error (MSE) (b) −8 −6 −4 −2 0 2 4 6 8 x 10 −15 0 20 40 60 80 100 120 Deviation from the key µ 1 ( δ µ 1 ) Mean Square Error (MSE) (c) −10 −5 0 5 10 0 20 40 60 80 100 120 Deviation from the key p 1 ( δ p 1 ) Mean Square Error (MSE) (d) Fig. 3: MSE for deviation of the correct keys. (a) Chirp rate β x . (b) Initial value x 0 . (c) Logistic map function parameter µ 1 . (d) T runcated position p 1 . 0 100 200 300 400 500 600 700 800 Distribution Gray Scale 0 50 100 150 200 250 (a) 0 100 200 300 400 500 600 700 800 900 Distribution Gray Scale 0 50 100 150 200 250 (b) 0 100 200 300 400 500 600 700 800 Grag Scale Distribution Gray Scale 0 50 100 150 200 250 (c) 0 100 200 300 400 500 600 700 800 900 1000 Distribution Gray Scale 0 50 100 150 200 250 (d) Fig. 4: Examples of histograms. (a) Lena image. (b) Encrypted image of Lena. (c) Baboon image. (d) Encrypted image of Baboon. 4 ALMAD AR JOURNAL FOR COMMUNICA TIONS, INFORMA TION TECHNOLOGY , AND APPLICA TIONS C. Histogr am Analysis T o resist statistical attacks, the encrypted images should hav e histograms that are consistent in distrib ution and are different from the histograms of their plain images. Figure 4(a) and (c) show the histograms of Lena and Baboon plain images respectiv ely , while Fig. 4(b) and (d) present the histograms of their encrypted images. It is clear that the histograms of the plain images are dif ferent from each other and their corre- sponding encrypted images hav e similar statistical properties. Moreov er , the values of the encrypted image are subject to normal distribution. Hence, the encrypted image histogram data does not provide any useful information for the attackers to perform any statistical analysis attack on the encrypted image. D. Corr elation Analysis T o e valuate the correlation of adjacent pixels, 6000 pairs of adjacent pixels are randomly selected from both the plain and encrypted images. A good encrypted image must have lo w correlation for the three directions-– horizontal, v ertical and diagonal. The distribution of two adjacent pixels to the plain and encrypted images for the three directions is shown in Fig. 5(a)–(f). Thus, correlation plots of plain images exhibit clear patterns while those of their encrypted counterparts show no clear pattern, the points being rather randomly distrib uted. In order to test the correlations of adjacent pixels for the plain and encrypted images, the correlation coefficients r xy of each pair are calculated using the follo wing equations r xy = P L i =1 ( x i − ¯ x )( y i − ¯ y ) r h P L i =1 ( x i − ¯ x ) 2 i h P L i =1 ( y i − ¯ y ) 2 i (9) where ¯ x = 1 /L P L i =1 x i , ¯ y = 1 /L P L i =1 y i , x i is the value of the i-th selected pixel, y i is the value of the correspondent adjacent pixel, and L is the total number of pixels selected from the image. The correlation coefficients of the plain image and encrypted image are summarized in T able II. T ABLE II: Correlation coefficients of two adjacent pixels in the plain and encrypted images. Image and scheme Horizontal V ertical Diagonal Plain Lena 0 . 9481 0 . 9737 0 . 9244 Encrypted Lena − 0 . 0014 0 . 0025 0 . 0051 Plain Baboon 0 . 8701 0 . 8411 0 . 7889 Encrypted Baboon 0 . 0077 − 0 . 002 − 0 . 0039 Plain Cameraman 0 . 9556 0 . 9738 0 . 934 Encrypted Cameraman − 5 . 84 × 10 − 4 − 0 . 0077 0 . 0015 Plain Pirate 0 . 9434 0 . 9564 0 . 9134 Encrypted Pirate − 0 . 002 5 . 25 × 10 − 4 − 0 . 0048 The importance of this work is also emphasised through the values of the correlation coefficient in T able III. It is clear that the correlation coefficient of the proposed algorithm is smaller than that of other methods proposed in Refs. [16], [17], [23]– [26]. 0 50 100 150 200 250 0 50 100 150 200 250 Pixel gray value on location (x,y) Pixel gray value on location (x,y+1) (a) 0 50 100 150 200 250 0 50 100 150 200 250 Pixel gray value on location (x,y) Pixel gray value on location (x,y+1) (b) 0 50 100 150 200 250 0 50 100 150 200 250 Pixel gray value on location (x,y) Pixel gray value on location (x+1,y) (c) 0 50 100 150 200 250 0 50 100 150 200 250 Pixel gray value on location (x,y) Pixel gray value on location (x+1,y) (d) 0 50 100 150 200 250 0 50 100 150 200 250 Pixel gray value on location (x,y) Pixel gray value on location (x+1,y+1) (e) 0 50 100 150 200 250 0 50 100 150 200 250 Pixel gray value on location (x,y) Pixel gray value on location (x+1,y+1) (f) Fig. 5: Correlation coefficients of plain and encrypted Lena images, from top to bottom: in horizontal, vertical, and diag- onal direction, respecti vely . T ABLE III: Correlation coef ficient of the proposed algorithm compared to others using plain Lena image. Algorithm Horizontal V ertical Diagonal Proposed algorithm − 0 . 0014 0 . 0025 0 . 0051 Ref. [17] 0 . 002 0 . 0062 0 . 0066 Ref. [16] − 0 . 0069 − 0 . 0188 − 0 . 0482 Ref. [23] − 0 . 0274 0 . 0046 − 0 . 0038 Ref. [24] 0 . 319 0 . 3314 0 . 0149 Ref. [25] − 0 . 0016 − 0 . 0033 0 . 0130 Ref. [26] − 0 . 0226 0 . 0041 0 . 0368 E. Occlusion Attack Analysis T o test the robustness of the proposed encryption algorithm against loss of data, we occlude 25% , 50% , and 75% of the encrypted image pixels. The decryption process is performed on the occluded encrypted image of “Lena" with all correct priv ate keys. The encrypted images with 25% , 50% , and 75% data losses are shown in Fig. 6(a), (c), and (e) while the corresponding reco vered images are illustrated in Fig. 6(b), (d), and (f), respectively . The decrypted images is recognisable ev en when the encrypted image is occluded up to 75% , though the quality of recov ered images drops with the increase in occluded area. W e employ the peak signal–to–noise ratio ALMAD AR JOURNAL FOR COMMUNICA TIONS, INFORMA TION TECHNOLOGY , AND APPLICA TIONS 5 (PSNR) to compute the quality of the recov ered image after attack. For a grayscale image, the PSNR may be computed using the follo wing mathematical expression, PSNR = 10 log 10 255 2 MSE (10) where MSE is defined in Eq. (8). The results of resisting occlusion attack of the proposed algorithm compared to others are presented in T able IV. (a) (b) (c) (d) (e) (f) Fig. 6: Occlusion attack analysis. (a) Encrypted image with 25% occlusion. (b) Decrypted image from (a). (c) Encrypted image with 50% occlusion. (d) Decrypted image from (c). (e) Encrypted image with 75% occlusion. (f) Decrypted image from (e). F . Noise Attack Analysis The robustness of the proposed encryption algorithm is also tested against noise attack. The encrypted Lena image is added to a zero mean Gaussian noise with different intensities. Fig. 7(a)–(d) show decrypted images with noise intensity 0 . 01 , 0 . 05 , 0 . 1 , and 0 . 2 , respecti vely . The PSNR values of the proposed scheme and the schemes in [28] and [29] are T ABLE IV: Comparison between the PSNR of the recon- structed images with dif ferent block size data loss. PSNR (dB) Occlusion (%) Proposed Ref. [14] Ref. [27] 25 25 . 70 13 . 88 15 . 42 50 24 . 82 11 . 27 11 . 26 75 24 . 33 9 . 60 7 . 05 compared in T able V, which shows that the proposed scheme has better performance at high levels of Gaussian noise. Thus, the results demonstrate that the proposed scheme can resist the noise attack. (a) (b) (c) (d) Fig. 7: Decrypted images with different le vels of Gaussian noise. (a) σ = 0 . 01 . (b) σ = 0 . 05 . (c) σ = 0 . 1 . (d) σ = 0 . 2 . T ABLE V: The PSNR of decrypted images under dif ferent noise le vels. PSNR (dB) Intensity (%) Proposed Ref. [28] Ref. [29] 0 . 01 43 . 97 30 . 59 38 . 93 0 . 05 32 . 36 28 . 55 33 . 64 0 . 1 29 . 42 25 . 33 29 . 57 0 . 2 27 . 95 20 . 58 26 . 95 0 . 25 27 . 52 18 . 91 23 . 88 V . C O N C L U S I O N In summary , an image encryption scheme has been proposed based on logistic maps and 2D discrete Linear chirp trans- form. It is demonstrated that the proposed scheme ensures, feasibility , security , and robustness by performing simulations 6 ALMAD AR JOURNAL FOR COMMUNICA TIONS, INFORMA TION TECHNOLOGY , AND APPLICA TIONS for grayscale images. The results show that the scheme is infeasible to the brute–force attack and offers a great degree of security as seen from its statistical analysis and sensiti vity to the encryption parameters. Finally , it has been illustrated that the proposed method is robust against noise and occlusion attacks. R E F E R E N C E S [1] N. K. Pareek, V . Patidar , and K. K. Sud, “Image encryption using chaotic logistic map," Image and V ision Computing , V ol. 24, no. 9, pp. 926 − 934, Sep. 2006. [2] H. Y ang, K-W W ong, X. Liao, W . Zhang, and P . W ei, “ A fast image encryption and au- thentication scheme based on chaotic maps," Com- munications in Nonlinear Science and Numerical Simulation , V ol. 15, no. 11, pp. 3507 − 3517, Nov . 2010. [3] R. Matthews, “ On the deri vation of a chaotic encryption algorithm," Cryptologia , V ol. 13, no. 1, pp. 29 − 42, Jan. 1989. [4] Z-I Zhu, W . Zhang, K-W W ong, and H. Y u, “ A chaos–based symmetric image encryption scheme using a bit–level permutation," Information Sciences, V ol. 181, no. 6, pp. 1171 − 1186, Mar . 2011. [5] Z. Liu, L. Xu, T . Liu, H. Chen, P . Li, C. Lin, and S. Liu, “Color image encryption by using Arnold transform and color–blend operation in discrete cosine transform domains," Optics Communication , V ol. 284, no. 1, pp. 123 − 128, Jan. 2011. [6] P . Refregier , “ Optical image encryption based on input plane and F ourier plane random encoding," Optics Letters , V ol. 20, no. 7, pp. 767 − 769, Apr . 1995. [7] Y . Luo, M. Du, and J. Liu, “ A symmetrical image encryption scheme in wa velet and time domain," Communications in Nonlinear Science Numerical Simulation , V ol. 20, no. 2, pp. 447 − 460, May 2015. [8] G. Unnikrishnan, J. Joseph, and K. Singh, “Optical encryption by double–random phase encoding in the fractional F ourier domain," Optics Letters , V ol. 25, no. 12, pp. 887 − 889, Jun. 2000. [9] B.H. Zhu, S.T . Liu, and Q.W . Ran, “Optical image encryption based on multifractional Fourier transforms," Optics Letters , V ol. 25, no. 16, pp. 1159 − 1161, Aug. 2000. [10] S.C. Pei and W .L. Hsue, “The multiple–parameter discrete fractional Fourier transform," IEEE Signal Pr ocessing Letters , V ol. 13, no. 6, pp. 329 − 332, Jun. 2006. [11] Z. Liu and S. Liu, “Random fractional Fourier transform," Optics Letters , V ol. 32, no. 15, pp. 2088 − 2090, Aug. 2007. [12] Q. Ran, H. Zhang, J. Zhang, L. T an, and J. Ma, “Deficiencies of the cryptography based on multiple–parameter fractional Fourier transform," Optics Letters , V ol. 34, no. 11, pp. 1729 − 1731, Jun. 2009. [13] N. Zhou, Y . W ang, L. Gong, H. He, and J. Wu, “Novel single–channel color image encryption algorithm based on chaos and fractional Fourier transform," Optics Communications , V ol. 284, no. 12, pp. 2789 − 2796, Jun. 2011. [14] J. Lang, “Image encryption based on the reality–preserving multiple- parameter fractional Fourier transform and chaos permutation," Optics and Lasers in Engineering , V ol. 50, no. 7, pp. 929 − 937, Jul. 2012. [15] A. Elshamy , A. Rashed, A. Mohamed, O. Faragallah, Y . Mu, S. Alshe- beili, and F . Abd El-samie, “Optical image encryption based on chaotic baker map and double random phase encoding," Journal of Lightwave T echnolo gy , V ol. 31, no. 15, pp. 2533 − 2539, Aug. 2013. [16] L. Sui, H. Lu, Z. W ang, and Q. Sun, “Double–image encryption using discrete fractional random transform and logistic maps," Optics and Lasers in Engineering , V ol. 56, pp. 1 − 12, May 2014. [17] J. Lima and L. Novaes, “Image encryption based on the fractional Fourier transform over finite fields," Signal Processing , V ol. 94, no. , pp. 521 − 530, 2014. [18] Y . Li, F . Zhang, Y . Li, and R. T ao, “ Asymmetric multiple–image encryption based on the cascaded fractional Fourier transform," Optics and Lasers in Engineering , V ol. 72, pp. 18 − 25, Apr . 2015. [19] T . Zhao, Q. Ran, L. Y uan, Y . Chi, and J. Ma, “Security of image en- cryption scheme based on multi–parameter fractional Fourier transform," Optics Communications , V ol. 376, pp. 47 − 51, May 2016. [20] O. A. Alkishriwo, A. Akan, and L. F . Chaparro, “Intrinsic mode chirp decomposition of non–stationry signals", IET Signal Pr ocessing , vol. 8, no. 3, pp. 267 − 276, May . May 2014. [21] Image Database /http://www .imageprocessingplace.com/index.htm [22] G. Alv arez and S. Li, “Some basic cryptographic requirements for chaos- based cryptosystems," International Journal Bifurcation and Chaos , V ol. 16, no. 8, pp. 2129 − 2151, 2006. [23] B. Nini and C. Lemmouchi, “Security analysis of a three–dimensional rotation–based image encryption," IET Image Pr ocessing , V ol. 9, no. 8, pp. 680 − 689, Aug. 2015. [24] M. H. Annaby , M. A. Rushdi, and E. A. Nehary , “Image encryption via discrete fractional Fourier –type transforms generated by random matri- ces," Signal Pr ocessing: Image Communication , V ol. 49, pp. 25 − 46, Nov . 2016. [25] X. Chai, Z. Gan, K. Y ang, Y . Chen, and X. Liu, “ An image encryp- tion algorithm based on the memristive hyperchaotic system, cellular automata, and DNA sequence operations," Signal Pr ocessing: Image Communication , V ol. 52, pp. 6 − 19, Mar. 2017. [26] L. Xu, X. Gou, Z. Li, and J. Li,“ A nov el chaotic image encryption algorithm using block scrambling and dynamix index based diffusion," Optics and Lasers in Engineering , V ol. 79, pp. 41 − 52, Apr . 2017. [27] N. Rawat, B. Kim, and Rajesh Kumar , “Fast digital image encryption based on compressive sensing using structurally random matrices and Arnold transform technique," Optik–International Journal of Light and Electr on Optics , V ol. 127, no. 4, pp. 2282 − 2286, Feb. 2016. [28] N. Zhou, S. Pan, S. Cheng, Z. Zhou, “Image compression—encryption scheme based on hyper –chaotic system and 2D compressiv e sensing," Optics and Laser T echnology , V ol. 82, pp. 121 − 133, Aug. 2016. [29] D. Xiao, L. W ang, T . Xiang, and Y . W ang, “Multi–focus image fusion and robust encryption algorithm based on compressive sensing," Optics and Laser T echnology , V ol. 91, pp. 212 − 225, Jun. 2017.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment