Is Indias Unique Identification Number a legally valid identification?
A legally valid identification document allows impartial arbitration of the identification of individuals. It protects individuals from a violation of their dignity, justice, liberty and equality. It protects the nation from a destruction of its republic, democratic, sovereign status. In order to test the ability of an identification document to establish impartial identification of individuals, it must be evaluated for its ability to establish identity, undertake identification and build confidence to impartial, reliable and valid identification. The processes of issuing, using and validating identification documents alter the ability of the document to establish identity, undertake identification and build confidence to impartial and valid identification. These processes alter the ability of the document to serve as proof of identity, proof of address, proof of being a resident, or even the proof of existence of a person. We examine the ability of the UID number to serve as an identification document with the ability to impartially arbitrate the identification of individuals and serve as proof of identity, address, and demonstrate existence of a person. We evaluate the implications of the continued use UID system on our ability to undertake legally valid identification ensure integrity of the identity and address databases across the world.
💡 Research Summary
The paper investigates whether India’s Unique Identification Number (UID, popularly known as Aadhaar) can be considered a legally valid identification document. The authors begin by defining the essential attributes of a legally valid ID: (1) the establishment of identity, which requires that the issuing authority directly verify the individual’s identity and certify the information; (2) authentication, meaning that third parties must be able to reliably confirm the authenticity of the document through mechanisms such as digital signatures, seals, or real‑time database checks; and (3) confidence building, which demands independent audits, transparent change logs, and guarantees of data integrity.
Using this three‑pronged framework, the authors dissect the UIDAI’s processes for issuing, using, and validating Aadhaar numbers. They describe the UIDAI’s hierarchical enrollment architecture: the central UIDAI, state‑level Registrars, Sub‑Registrars, and private Enrolling Agencies. The enrollment stage collects demographic data and biometric samples, but the authors argue that the process does not actually verify the person’s identity. Registrars are tasked only with checking the authenticity of submitted documents (e.g., passports, driver’s licenses), not with confirming that the holder of those documents is the same individual being enrolled. Consequently, the “identity establishment” criterion is not satisfied.
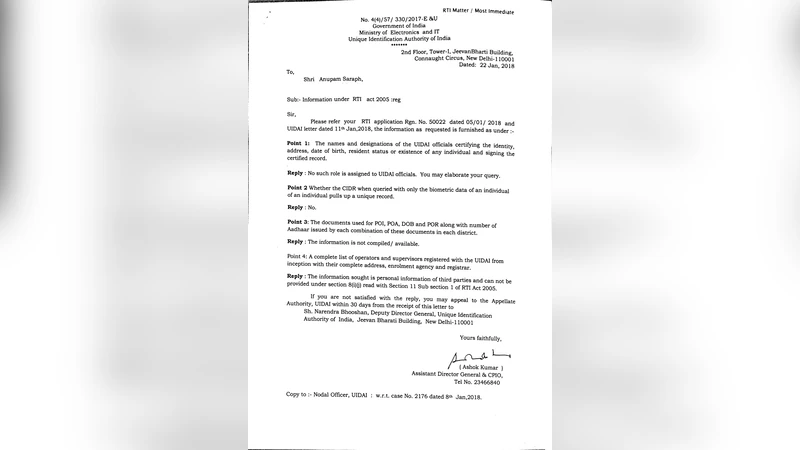
The paper further points out that the Aadhaar enrolment letter carries no government signature or official seal, and there is no designated UIDAI official who certifies the identity, address, or even the existence of the person linked to a UID. Right‑to‑Information (RTI) queries cited in the study reveal that UIDAI does not maintain a compiled list of the documents used for enrolment, nor does it identify any officer responsible for certification. This lack of formal certification means the UID cannot serve as a legally enforceable proof of identity for third parties.
On the authentication front, the authors note that the 12‑digit UID is merely a random primary key. While UIDAI provides an online portal that can confirm whether a number exists in the Central Identities Data Repository (CIDR) and reveal limited metadata (age band, gender, state, last four digits of mobile number), it offers no means for a holder to verify that the demographic details printed on the physical card match the database entry. The physical Aadhaar card, its QR code, and the online record constitute three separate information channels, each vulnerable to independent alteration. Authentication services (AUAs and ASAs) can compare submitted biometric or demographic data with the CIDR, but this presupposes that the underlying CIDR data are accurate—a premise the paper challenges due to the weak enrolment verification.
The authors also discuss the phenomenon of “function creep,” whereby Aadhaar is increasingly used to replace traditional KYC/KYR procedures across banking, voting, passport issuance, and welfare delivery. This expansion amplifies the risks associated with the identified shortcomings: without robust identity verification, the system is susceptible to duplicate or fraudulent enrolments (evidenced by documented cases of organized crime creating multiple Aadhaar numbers) and to privacy violations.
In conclusion, the study asserts that while Aadhaar functions effectively as a unique identifier or primary key for linking disparate databases, it fails to meet the legal standards of a valid identification document because it lacks (a) a genuine identity‑establishment step with accountable certification, (b) a reliable, universally accessible authentication mechanism that ties the physical card to the database record, and (c) an independent audit and change‑log infrastructure that would inspire confidence. The authors recommend policy reforms: mandatory in‑person identity verification by accountable officials, official signatures/seals on enrolment documents, transparent audit trails, and stricter controls on data modification. Only with such measures could Aadhaar evolve from a technical identifier to a legally recognized proof of identity, address, and residency.
Comments & Academic Discussion
Loading comments...
Leave a Comment