COZMO-A New Lightweight Stream Cipher
This paper deals with the merger of the two lightweight stream ciphers: A5by1 and Trivium. The idea is to make the key stream generation more secure and to remove the attacks of the individual algorithms. The bits generated by the Trivium cipher will act as the input of the A5by1 cipher. The registers used in the A5by1 cipher will be filled by the output bits of the Trivium cipher. The three registers will then be connected to generate an output which will be our required key stream.
💡 Research Summary
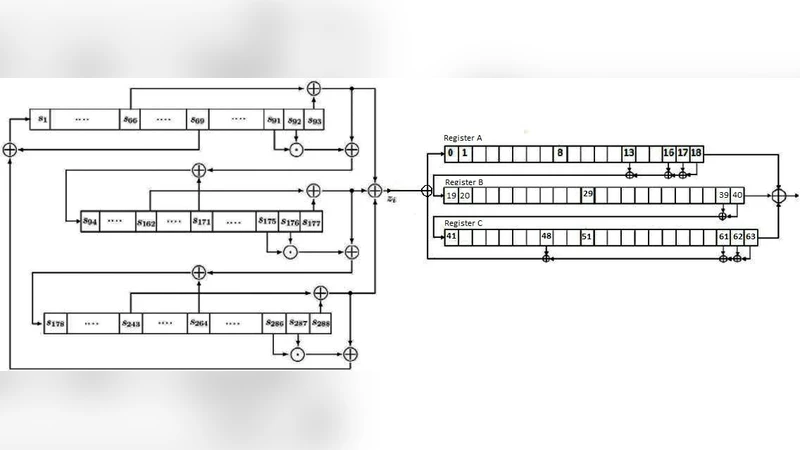
The paper introduces COZMO, a novel lightweight stream cipher that combines two well‑known lightweight ciphers, Trivium and A5/1, with the aim of improving security and resistance to attacks that affect each algorithm individually. The authors first describe the internal workings of Trivium, which consists of three non‑linear feedback shift registers (NFSRs) of lengths 93, 84, and 111 bits. Trivium is initialized with an 80‑bit secret key and an 80‑bit IV, undergoes 1152 warm‑up cycles, and then generates a keystream by repeatedly applying specific AND and XOR feedback functions. A mathematical model using a state‑transition matrix A and a nonlinear vector b(t) is provided to formalize the state evolution.
Next, the paper reviews A5/1, a GSM‑derived stream cipher that uses three linear shift registers of 19, 22, and 23 bits. A majority‑vote function on three “clocking bits” determines which registers are shifted each cycle; the selected registers are updated by XOR‑ing designated tap bits, while the output keystream bit is the XOR of the three registers’ last bits.
COZMO’s construction proceeds as follows: Trivium is run for 1152 + 64 cycles, producing a 64‑bit output sequence z_i. These bits are fed as external input to the three A5/1 registers, which are initially cleared to zero. For each iteration, the algorithm computes three intermediate XOR values: p1 = r13 ⊕ r16 ⊕ r17 ⊕ r18 (register A), p2 = r20 ⊕ r21 (register B), and p3 = r7 ⊕ r20 ⊕ r21 ⊕ r22 (register C). The majority function is evaluated on three designated bits (L, M, N) taken from the registers. Registers that belong to the majority are right‑shifted by one position; their new first bit is replaced by the corresponding p‑value or, in the case of register A, by p3 XORed with the current Trivium output bit z_i. Registers not in the majority remain unchanged. The final keystream bit t_i for the i‑th round is obtained by XOR‑ing the last bits of the three registers (r18, r40, r63). The process repeats indefinitely, producing a continuous keystream.
To assess randomness, the authors applied the NIST SP 800‑22 statistical test suite, including Frequency, Cumulative Sum (both forward and reverse), Approximate Entropy, Linear Complexity, Serial (both m and m+1), Longest Run of Ones, and Runs tests. All p‑values for COZMO exceeded the 0.01 significance threshold, indicating that the generated sequence passes each test at the 1 % level. Comparative tables show that COZMO’s p‑values are generally higher than those obtained for the standalone A5/1 and Trivium implementations, suggesting an improvement in statistical quality.
The paper concludes that COZMO offers a stronger keystream in terms of randomness while retaining the low‑resource characteristics desirable for lightweight applications such as IoT devices and embedded systems. The authors acknowledge that further work is needed to evaluate resistance against specific cryptanalytic attacks (e.g., correlation, time‑memory trade‑off, and majority‑vote attacks) and to optimize hardware implementation, but they argue that the hybrid design provides a promising direction for future lightweight cipher research.
Comments & Academic Discussion
Loading comments...
Leave a Comment