RF-PUF: Enhancing IoT Security through Authentication of Wireless Nodes using In-situ Machine Learning
Traditional authentication in radio-frequency (RF) systems enable secure data communication within a network through techniques such as digital signatures and hash-based message authentication codes (HMAC), which suffer from key recovery attacks. State-of-the-art IoT networks such as Nest also use Open Authentication (OAuth 2.0) protocols that are vulnerable to cross-site-recovery forgery (CSRF), which shows that these techniques may not prevent an adversary from copying or modeling the secret IDs or encryption keys using invasive, side channel, learning or software attacks. Physical unclonable functions (PUF), on the other hand, can exploit manufacturing process variations to uniquely identify silicon chips which makes a PUF-based system extremely robust and secure at low cost, as it is practically impossible to replicate the same silicon characteristics across dies. Taking inspiration from human communication, which utilizes inherent variations in the voice signatures to identify a certain speaker, we present RF- PUF: a deep neural network-based framework that allows real-time authentication of wireless nodes, using the effects of inherent process variation on RF properties of the wireless transmitters (Tx), detected through in-situ machine learning at the receiver (Rx) end. The proposed method utilizes the already-existing asymmetric RF communication framework and does not require any additional circuitry for PUF generation or feature extraction. Simulation results involving the process variations in a standard 65 nm technology node, and features such as LO offset and I-Q imbalance detected with a neural network having 50 neurons in the hidden layer indicate that the framework can distinguish up to 4800 transmitters with an accuracy of 99.9% (~ 99% for 10,000 transmitters) under varying channel conditions, and without the need for traditional preambles.
💡 Research Summary
The paper addresses the growing security challenges in the Internet‑of‑Things (IoT) where billions of low‑power devices operate in untrusted environments. Traditional authentication mechanisms—digital signatures, HMAC, and OAuth 2.0—rely on secret keys stored in non‑volatile memory and are vulnerable to key‑recovery, invasive side‑channel, and cross‑site request forgery attacks. Physical Unclonable Functions (PUFs) exploit unavoidable manufacturing variations to generate device‑specific secrets that are extremely difficult to clone, offering a promising hardware‑based alternative.
Inspired by human voice recognition, where each speaker’s unique vocal signature enables identification independent of spoken content, the authors propose RF‑PUF: a framework that treats the inherent analog/RF non‑idealities of each wireless transmitter (Tx) as a “voice” that can be recognized by a machine‑learning engine residing in the receiver (Rx). The key insight is that process‑induced variations such as local‑oscillator (LO) frequency offset, in‑phase/quadrature (I‑Q) amplitude and phase imbalance, and power‑amplifier back‑off are already present in every transmitted signal. By extracting these features at the Rx—using existing blocks such as carrier synchronizers, automatic gain control (AGC), and root‑raised‑cosine filters—no extra circuitry is required on the resource‑constrained Tx side.
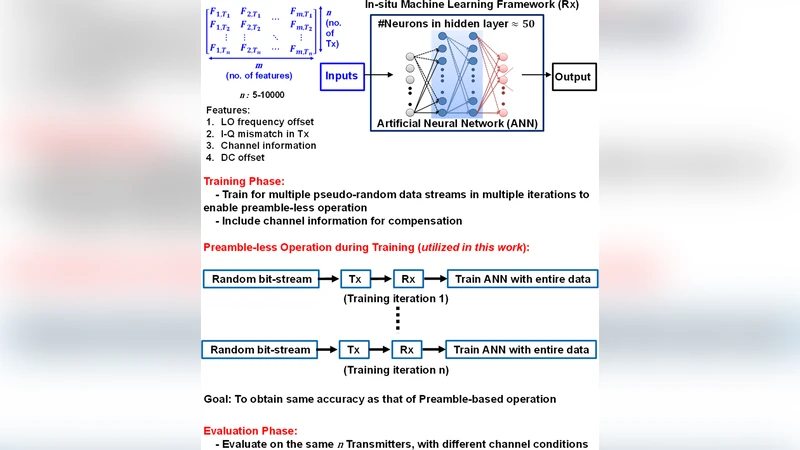
The extracted feature vector (frequency offset, I‑Q amplitude error, I‑Q phase error, and optionally channel‑compensation parameters) is fed into a shallow artificial neural network (ANN) with three layers: an input layer, a hidden layer of 50 neurons, and an output layer that performs multi‑class classification of the transmitter identity. The network is trained in a supervised manner on a large dataset comprising multiple random bit‑streams per device and a variety of channel conditions (AWGN, Rayleigh fading, Doppler shifts). Because the classification problem is highly nonlinear and multidimensional, the ANN can capture subtle correlations among the features, effectively turning the RF signature into a strong PUF with a large number of challenge‑response pairs (CRPs).
Simulation experiments are performed using a 65 nm CMOS process model to emulate realistic process spread. Frequency offsets follow a normal distribution with σ≈20 kHz (≈25 ppm at 2.4 GHz), while I‑Q imbalances are drawn from measured silicon data. The authors simulate 4 800 distinct transmitters and achieve 99.9 % identification accuracy; scaling up to 10 000 transmitters still yields ≈99 % accuracy. These results are obtained without the high oversampling rates (hundreds of MS/s) required by conventional RF fingerprinting or RF‑DNA techniques, demonstrating that a modest sampling rate and standard receiver front‑end suffice.
Security analysis highlights several strengths: (1) the uniqueness stems from uncontrollable manufacturing variations, making physical cloning practically impossible; (2) the “secret” never resides in memory, eliminating key‑extraction attacks; (3) the receiver’s own non‑idealities are compensated within the learning loop, preventing an adversary from exploiting Rx imperfections. The authors acknowledge that model‑inversion attacks (e.g., using a surrogate neural network to approximate the classifier) could be attempted, and they propose augmenting RF‑PUF with error‑correction codes or hash‑based multi‑factor authentication to further harden the system.
Compared with prior work, RF‑PUF differs in four major ways: it is preamble‑less, avoids high‑rate transient capture, leverages a higher‑dimensional feature space to achieve strong‑PUF properties, and includes explicit compensation for receiver imperfections. Consequently, the approach is well‑suited for asymmetric IoT networks where many low‑cost transmitters communicate with a single, more capable gateway.
In conclusion, RF‑PUF offers a low‑cost, low‑power, and scalable physical‑layer authentication mechanism that can operate as a standalone security primitive or be combined with existing cryptographic protocols for multi‑factor authentication. Future work suggested includes silicon prototype fabrication, on‑chip implementation of the lightweight ANN, exploration of online learning for device enrollment/revocation, and extensive field trials to validate robustness against real‑world interference and adversarial machine‑learning attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment