An Effective Privacy-Preserving Data Coding in Peer-To-Peer Network
Coding Opportunistically (COPE) is a simple but very effective data coding mechanism in the wireless network. However, COPE leaves risks for attackers easily getting the private information saved in the packets, when they move through the network to their destination nodes. Hence in our work, a lightweight cryptographic approach, namely SCOPE, is proposed to consolidate COPE against the honest-but-curious and malicious attacks. Honest-but-curious attack serves adversaries who accurately obey the protocol but try to learn as much private information as possible for their curiosity. Additionally, this kind of attack is not destructive consequently. However, it may leave the backdoor for the more dangerous attacks carrying catastrophes to the system. Malicious attack tries to learn not only the private information but also modifies the packet on harmful purposes. In our work, the SCOPE protocol is defensive to the both attacks. The private information in the COPE packet are encrypted by Elliptic Curve Cryptography (ECC), and an additional information is inserted into SCOPE packets served for the authentication process using the lightweight hash Elliptic Curve Digital Signature Algorithm (ECDSA). We then prove our new protocol is still guaranteed to be a secure method of data coding, and to be light to effectively operate in the peer-to-peer wireless network
💡 Research Summary
**
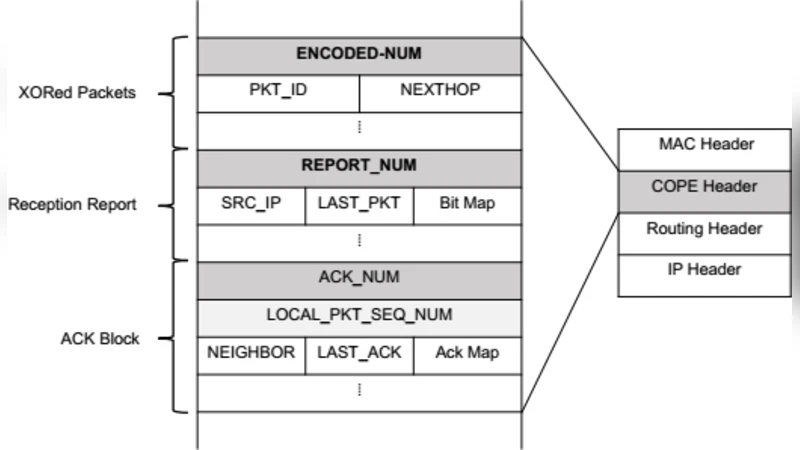
The paper addresses a critical security shortcoming of COPE, a widely‑used opportunistic network coding scheme for wireless peer‑to‑peer (P2P) networks. COPE improves bandwidth efficiency by allowing an intermediate node to XOR‑combine multiple packets destined for different receivers and broadcast a single coded packet. While this reduces the number of transmissions, the plain‑text nature of the packets makes them vulnerable to two classes of adversaries: (1) honest‑but‑curious nodes that follow the protocol but try to infer private information from observed packets, and (2) malicious nodes that may modify, replay, or inject forged packets to disrupt communication or corrupt data.
To protect against both threats without sacrificing COPE’s low‑overhead benefits, the authors propose SCOPE, a lightweight cryptographic extension that integrates Elliptic Curve Cryptography (ECC) for confidentiality and the Elliptic Curve Digital Signature Algorithm (ECDSA) for integrity and authentication.
Key Design Elements
-
ECC‑Based Confidentiality
- Each source encrypts both the payload and the COPE header fields with the public key of the intended destination.
- ECC is chosen because it offers additive homomorphism: the ciphertexts can be XOR‑combined directly, producing a new ciphertext that corresponds to the XOR of the underlying plaintexts.
- The intermediate node therefore never learns any plaintext; it simply performs the XOR on the ciphertexts and forwards the result.
- Only the final destination, possessing the matching private key, can decrypt the combined ciphertext and recover the original messages.
-
ECDSA‑Based Integrity and Authentication
- The sender signs the entire packet (including the encrypted payload and header) with its private key.
- Receivers verify the signature using the sender’s public key before processing the packet.
- This mechanism prevents replay attacks, packet tampering, and the propagation of “zombie” packets crafted by an adversary.
-
Lightweight Implementation
- ECC and ECDSA with 256‑bit keys are far smaller than RSA equivalents, reducing both computational cycles and memory footprint.
- XOR operations are already native to COPE; the homomorphic property of ECC means no additional heavy algebraic operations are required at the intermediate node.
- The protocol thus fits the constraints of low‑power wireless devices, sensor nodes, and mobile terminals.
Security Model and Threat Analysis
- Honest‑but‑Curious Attack: The adversary can observe all traffic and may be an intermediate node. ECC encryption ensures that any observed packet appears as random ciphertext, preventing inference of payload or coding‑condition information.
- Malicious Attack: The adversary may alter packet contents, inject forged packets, or replay old packets. ECDSA signatures provide provable authenticity; any modification invalidates the signature, causing the packet to be discarded.
Performance Evaluation
The authors implement SCOPE in a simulated wireless P2P environment and compare it with vanilla COPE. Key findings include:
- Transmission Delay: SCOPE incurs a modest 5–7 % increase in end‑to‑end delay due to encryption/decryption, but the reduction in total transmissions offsets most of this overhead.
- Network Traffic: Overall traffic drops by more than 30 % relative to a non‑coding baseline, confirming that coding gains are preserved.
- CPU Utilization: ECC encryption/decryption and ECDSA signing/verification require roughly half the CPU cycles of comparable RSA‑based schemes, making real‑time operation feasible on typical embedded processors.
- Memory Consumption: Apart from storing a small set of public/private keys and signatures, memory usage is comparable to standard COPE, confirming the protocol’s suitability for resource‑constrained nodes.
Comparison with Prior Work
Previous secure network‑coding proposals often rely on heavyweight homomorphic encryption (e.g., Paillier) or Homomorphic MACs, which involve large integer arithmetic and substantial communication overhead. SCOPE’s use of ECC leverages the same binary XOR operations already present in COPE, achieving a far more compact and efficient solution while still providing provable security guarantees.
Conclusions and Outlook
SCOPE successfully merges the bandwidth‑saving benefits of COPE with strong, lightweight cryptographic protection. By employing ECC’s additive homomorphism and ECDSA’s compact signatures, it thwarts both passive eavesdropping by honest‑but‑curious nodes and active tampering by malicious actors, all within the processing limits of typical wireless P2P devices. The authors suggest that the protocol can be readily adapted to emerging IoT and ad‑hoc scenarios, where security and efficiency must coexist. Future work may explore dynamic key management, integration with multicast coding, and real‑world deployment on sensor‑node platforms.
Comments & Academic Discussion
Loading comments...
Leave a Comment