Fundamental Concepts of Cyber Resilience: Introduction and Overview
Given the rapid evolution of threats to cyber systems, new management approaches are needed that address risk across all interdependent domains (i.e., physical, information, cognitive, and social) of cyber systems. Further, the traditional approach of hardening of cyber systems against identified threats has proven to be impossible. Therefore, in the same way that biological systems develop immunity as a way to respond to infections and other attacks, so too must cyber systems adapt to ever-changing threats that continue to attack vital system functions, and to bounce back from the effects of the attacks. Here, we explain the basic concepts of resilience in the context of systems, discuss related properties, and make business case of cyber resilience. We also offer a brief summary of ways to assess cyber resilience of a system, and approaches to improving cyber resilience.
💡 Research Summary
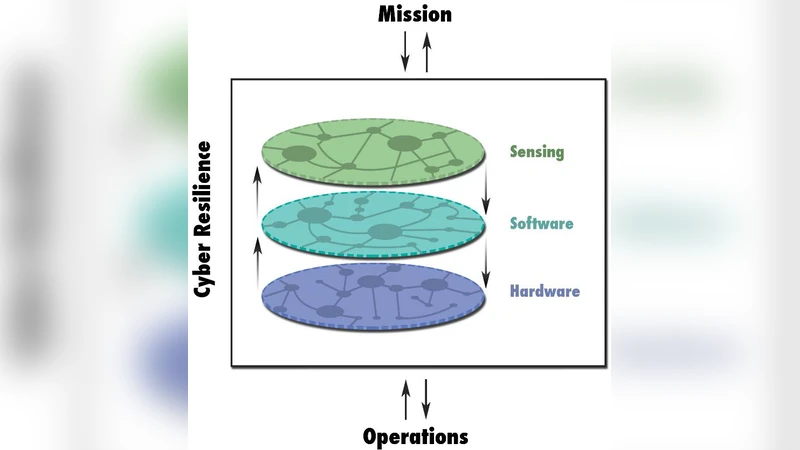
The paper addresses the growing complexity and velocity of cyber threats and argues that traditional “hardening” approaches—where systems are fortified against known vulnerabilities—are no longer sufficient. Instead, it proposes a paradigm shift toward cyber resilience, a management philosophy that treats cyber systems as interconnected across four interdependent domains: physical, informational, cognitive, and social. By viewing these domains as a tightly coupled ecosystem, the authors highlight that a breach in one area can cascade through the others, making isolated defenses ineffective.
Central to the discussion is the analogy to biological immunity. Just as organisms detect, respond to, recover from, and learn from infections, cyber systems should be designed to execute a continuous “detect‑respond‑recover‑learn” cycle. The paper delineates four core attributes of resilience: (1) Robustness – the ability to withstand an initial shock without immediate degradation; (2) Resilience – the capacity to return to a functional state (or a new, acceptable state) after disruption; (3) Recovery – the speed and completeness with which lost services are restored, typically measured by Recovery Time Objective (RTO) and Recovery Point Objective (RPO); and (4) Adaptability – the system’s ability to incorporate lessons learned from incidents and evolve its defenses. Together, these attributes form a holistic resilience framework that goes beyond mere recovery to include proactive learning and adaptation.
From a business perspective, the authors make a compelling case that investing in resilience yields higher return on investment than traditional security spending. Resilience reduces downtime, protects revenue streams, preserves brand reputation, and can lower insurance premiums and regulatory penalties. Moreover, resilient architectures often simplify compliance reporting because they embed continuous monitoring and rapid incident response into operational processes.
The paper outlines a multi‑layered assessment methodology. First, threat‑scenario simulations model a range of attack vectors, including multi‑stage and supply‑chain attacks, to test system behavior under stress. Second, a dependency matrix maps inter‑domain relationships, enabling cascade‑failure analysis that quantifies how a failure in the physical layer might propagate to cognitive or social layers. Third, quantitative metrics such as RTO, RPO, mean time to detect (MTTD), and mean time to remediate (MTTR) are collected through controlled drills. Fourth, learning metrics—such as the proportion of automated patches applied after an incident, frequency of policy updates, and the length of the post‑incident improvement cycle—capture the adaptability dimension. By combining these quantitative and qualitative indicators, organizations can derive a resilience score that reflects both current capability and improvement trajectory.
Improvement strategies are grouped into five pillars. (A) Proactive Design advocates modular, micro‑service architectures, zero‑trust networking, and defense‑in‑depth segmentation to limit blast radius. (B) Real‑time Monitoring and Automated Response leverages AI/ML‑driven anomaly detection, automated quarantine, and orchestration platforms that can execute containment playbooks without human latency. (C) Standardized Recovery Processes emphasizes regularly tested disaster‑recovery plans, immutable backups, and scripted restoration procedures to reduce human error. (D) Organizational Culture and Awareness calls for continuous cyber‑hygiene training, red‑team/blue‑team exercises, and tabletop simulations to embed a resilience mindset across all staff levels. (E) Supply‑Chain Resilience requires continuous vetting of third‑party vendors, shared‑risk assessments, and contractual clauses that enforce security standards throughout the ecosystem.
In conclusion, the authors argue that cyber security must evolve from a static, defense‑centric model to a dynamic, resilience‑centric model. This transition demands integrated technical controls, robust processes, and a culture of continuous learning. By adopting the proposed framework, organizations can better withstand, absorb, and adapt to the ever‑changing threat landscape, ensuring sustained operation of critical functions despite persistent attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment