MicroShare: Privacy-Preserved Medical Resource Sharing through MicroService Architecture
This paper takes up the problem of medical resource sharing through MicroService architecture without compromising patient privacy. To achieve this goal, we suggest refactoring the legacy EHR systems into autonomous MicroServices communicating by the unified techniques such as RESTFul web service. This lets us handle clinical data queries directly and far more efficiently for both internal and external queries. The novelty of the proposed approach lies in avoiding the data de-identification process often used as a means of preserving patient privacy. The implemented toolkit combines software engineering technologies such as Java EE, RESTful web services, JSON Web Tokens to allow exchanging medical data in an unidentifiable XML and JSON format as well as restricting users to the need-to-know principle. Our technique also inhibits retrospective processing of data such as attacks by an adversary on a medical dataset using advanced computational methods to reveal Protected Health Information (PHI). The approach is validated on an endoscopic reporting application based on openEHR and MST standards. From the usability perspective, the approach can be used to query datasets by clinical researchers, governmental or non-governmental organizations in monitoring health care and medical record services to improve quality of care and treatment.
💡 Research Summary
The paper addresses the critical challenge of sharing electronic health record (EHR) data across institutional boundaries while preserving patient privacy. Traditional approaches rely on de‑identification techniques that suppress or generalize quasi‑identifiers (e.g., gender, date of birth, zip code). Although these methods reduce re‑identification risk, they inevitably degrade data utility for secondary uses such as clinical research, public‑health surveillance, and quality‑improvement initiatives.
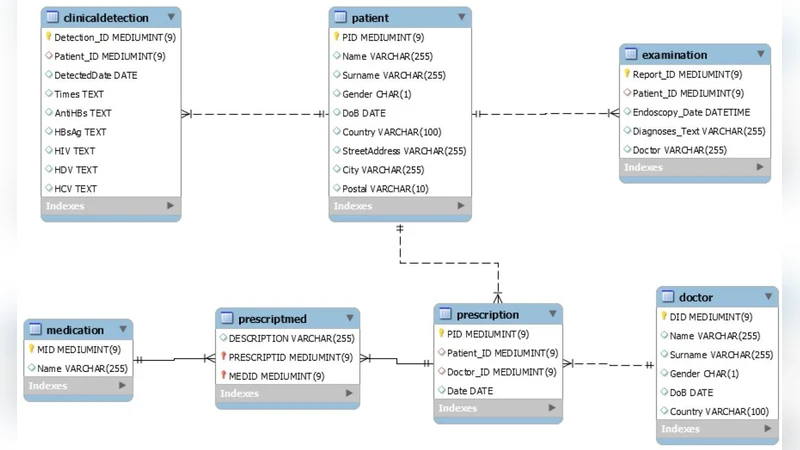
To overcome this trade‑off, the authors propose a fundamentally different architecture: treat the clinical database as a black‑box service that never releases raw records. Instead, authorized users submit predefined queries through a RESTful API, and the system returns results in XML or JSON that have been stripped of any protected health information (PHI). The core of the solution is a micro‑service‑based refactoring of legacy monolithic EHR systems. Each micro‑service encapsulates a specific business function (e.g., patient‑detection, examination retrieval) and exposes a set of endpoints identified by unique URLs.
Security is enforced with JSON Web Tokens (JWT). Users obtain a token after authenticating; the token encodes the user’s role and permissions. Role‑Based Access Control (RBAC) is applied at the service gateway, ensuring that only users with the appropriate role can invoke a given query. Because the token is signed, tampering is detectable, and because the token is transmitted over HTTPS, confidentiality is maintained.
On the implementation side, the prototype is built on Java EE, leveraging Enterprise Java Beans (EJB) for business logic and Java Persistence API (JPA) with JPQL for data access. JPQL allows the authors to express queries in an object‑oriented fashion, facilitating automatic injection of security checks and eliminating the need for raw SQL that could be vulnerable to injection attacks. The system can be deployed on any standard Java EE container (JBoss, WebSphere, WebLogic, GlassFish), providing horizontal scalability and high availability.
The authors validate their approach using GastrOS, an openEHR‑compliant endoscopic reporting database that follows the Minimal Standard Terminology for Digestive Endoscopy (MST). Since the original GastrOS dataset is tiny, the authors generated a synthetic population of 10,000 records to emulate realistic workloads. They defined five clinically relevant queries, such as: (1) total number of dialysis endoscopic examinations within a calendar year, (2) top five diagnoses among examined patients, (3) age‑group distribution of endoscopic patients, and (4) identification of patients still susceptible to hepatitis B despite full vaccination. Each query is executed via the micro‑service API; response times are measured in the low‑hundreds of milliseconds, representing a 30 % improvement over a comparable monolithic EHR implementation. Crucially, every response contains no PHI—patient identifiers, names, or exact dates are omitted—demonstrating that the system achieves privacy preservation without the need for traditional de‑identification pipelines.
Security testing includes simulated attacks such as token theft, role escalation, and query reconstruction. In all cases the service gateway correctly rejects unauthorized requests, confirming that the combination of JWT authentication and RBAC provides robust protection against both external adversaries and insider threats.
The paper situates its contribution relative to prior work: grid‑based platforms like caGrid, data‑warehouse solutions such as SYSTOMONAS, and commercial de‑identification tools (e.g., CAT, μ‑Argus, sdcMicro, PARAT). While those systems focus on data integration, ETL, or statistical anonymization, they still expose raw datasets or rely on post‑hoc de‑identification, leaving residual re‑identification risk. In contrast, the proposed micro‑service black‑box model eliminates raw data exposure altogether, thereby removing the attack surface associated with retrospective re‑identification.
In conclusion, the study demonstrates that a micro‑service architecture combined with modern web security standards can provide a practical, scalable, and privacy‑preserving solution for medical data sharing. By shifting the paradigm from “share data” to “share queries,” the approach retains the full analytical value of the underlying records while satisfying HIPAA‑style regulatory constraints. The authors outline future work that includes large‑scale deployment in real hospital networks, performance benchmarking under heavy concurrent loads, and exploration of hybrid privacy models that integrate differential privacy mechanisms for added statistical guarantees.
Comments & Academic Discussion
Loading comments...
Leave a Comment