Low-Complexity Linear Precoding for Secure Spatial Modulation
In this work, we investigate linear precoding for secure spatial modulation. With secure spatial modulation, the achievable secrecy rate does not have an easy-to-compute mathematical expression, and hence, has to be evaluated numerically, which leads…
Authors: F. Shu, Z. Wang, S. Yan
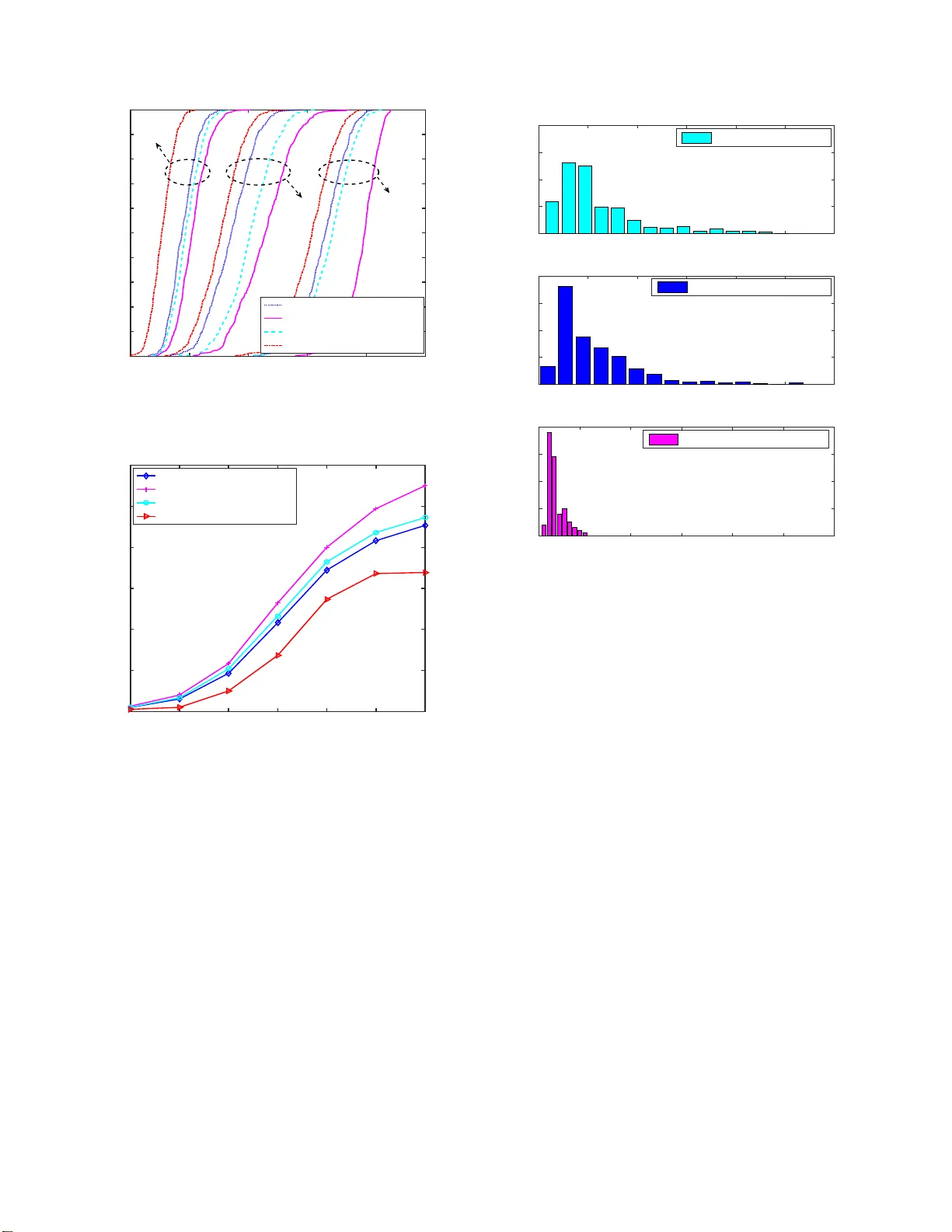
1 Lo w-Comple xity Linear Precoding for Secure Spatial Modulation Feng Shu, Member , IEEE , Z hengwang W ang, Shihao Y an, Member , IEEE , Xiaobo Z h ou, Jun Li, Senior Member , IEEE , Xiangyu n Zhou, Senior Memb er , IEEE Abstract —In this w ork, we inv estigate lin ear pr ecodin g for secure spatial modulation. With secure spatial modulation, the achiev abl e secrecy rate does not hav e an easy-to -compute math- ematical expression, and hence, has to be eva luated numerically , which leads to high complexity in th e opt i mal precoder design. T o address this issu e, an accurate and analytical approximation of the secrecy rate i s d eriv ed in this work. Using this approximation as the objective fun ction, two low-complexity l inear precoding methods based on gradient descend (GD) and successive con vex approximation (S CA) are proposed. T h e GD-based method has much lower complexity but usually con verges to a local optimum. On the other hand, the S CA-based method uses semi-definite relaxa tion to deal with th e n on-con vexity in the precoder opti- mization problem and achieves near -opti mal solution. Compared with the existin g GD-based precoder design in the li terature that directly u ses the exact and numerically evaluated secrecy capacity as the objective function, the two proposed designs hav e significantl y lower complexity . Our SCA- b ased design ev en achiev es a h igher secrec y rate than the existing GD-based design. Index T erms —MIMO, secure spatial modulation, l i near pre- coding, gradient d escend, successive con vex approxima tion. I . I N T R O D U C T I O N S P A T IAL MODULA TION (SM), propo sed by Raed Y . Mesleh in [1], constitutes a pr o mising multiple-input- multiple-ou tput (MIMO) co mmunicatio n technology for futur e wireless commun ication systems. The b asic idea of SM is to use b oth th e indices of tr ansmit anten nas and constellation signals to carry a block of in formatio n bits [ 2]–[4]. Compared to single-inpu t-single-ou tput (SISO) systems, SM systems improve the overall spectral efficiency (SE) b y the lo garithm with base 2 of the num b er of tran smit an tennas [1]. Due to one antenna bein g active at any time instant in SM system s, the impacts of in ter-channel inter ference (I CI) a n d inter-antenna synchro n ization (IAS) can be mitigated [5], an d thus the practical im p lementation co mplexity at the tran smitter and This work was in part supported by the National Natura l Science Founda- tion of China (Grant Nos. 61771244 , 6147219 0, 61702258, 61501238, and 61602245), the China Postdoctoral Scienc e Foun dation (2016M591852), the Postdoctor al research funding program of Jiangsu Province(1 601257C), the Natural Science Foundation of J iangsu Province (Grants No. BK20150791) , and the open resea rch fund of National Mobile Communicatio ns Research Laboratory , Southeast Uni versity , China (No. 2013D02). F . Shu, Z. W ang, X. Zhou, and J. Li are with School of Elect ronic and Optical Enginee ring, Nanjing Univ ersity of Science and T echnol ogy , Nanjing, 210094, China. F . Shu is also with the College of Computer and Information Science s, Fujian Agriculture and Forestry Uni versity , Fuzhou 350002, China. S. Y an is with the School of Engineering, Macquari e Uni versity , Sydney , NSW 2109, Australia (e-mail : shihao.yan@mq.edu.au .) X. Z hou is with Researc h School of Engineeri ng, T he Australia n Nationa l Uni versity , A CT 2601, Australi a (e-mail: xiangyu n.zhou@anu.e du.au.) receiver is significantly reduce d [6]. Compar ed to space-time block cod ing (STBC) and bell labora tories layered space-time (BLAST) arch itectures, th e SM techn ique strikes an attractive tradeoff b etween the SE and energy efficiency (EE), thu s it is app licable to som e futur e energy-efficient scenarios such as internet o f thin g s, 5G and beyond mobile n etworks. Howev er, it is very likely that the con fidential messages ar e intercepted by un in tended receivers, due to the br oadcast nature and openn e ss of wir eless chann el. Therefore, it is very important and necessary to addr ess security issues for such SM systems. Recently , physical layer security on co n ventio nal MIMO systems has be en widely investigated in [7]– [ 11], which exploits th e u niquen e ss and tim e - varying cha r acteristics of wireless ch annel to obtain secur e transmissions against eaves- dropp ers. Particularly , the autho rs in [ 12], [13] exploited the direction mo dulation (DM) technique and random frequ e ncy div erse arrays to ob tain secure and pr ecise transmissions, where only desired users with prede fined specific directio ns and d istances ca n receiv e confid ential messages. Ho wever , some works on physical layer security of co n ven tio nal MIMO systems assum e d that the inp ut signa ls follow Gau ssian dis- tribution [14], wh ic h is not practical in SM systems d ue to the numb e r of transmit antennas being finite. In fact, fin ite alphabet inp uts should b e con sidered in SM systems. In [15]– [26], the au thors inv e stig a te d secure tra nsmissions for SM systems from different aspects. The authors in [15] derived the secr ecy mutual info rmation with finite alph a b et input for a SM m ultiple-inp ut-single- output (MISO) system, and propo sed a pr ecoding sch eme to degrad e the dete c tion perfo rmance at an eavesdropper by decr easing the Euclidean distance at the eavesdropper . Howe ver, the precod ing scheme is n ot applicable fo r SM- MIMO systems. Both [16] and [ 17] add ressed the security of SM systems with the aid of artificial no ise (AN), which was proje c ted into the null space of legitimate ch annels. In [16], the ran d om AN signals were ra diated at the tran sm itter and th e secr e cy rate ( SR) was analyzed . In [17], a f ull-dup lex receiver with self-interferen ce c ancelation ca p ability was em- ployed to transmit AN signals. Mean while, the preco ding- aided spatial modulation (PSM) was generalized to provide secure tran smissions f or o n e legitimate u ser in [1 8], [ 19] o r multiple legitimate users in [20]. The secur ity of PSM was enhanced by con structing time-varying precod er [1 8], [2 0] or op timizing the pr e c oder throug h join tly minimizing th e receive power at eavesdropper and maximizing the receive power at desired user [19]. Unlike traditional SM systems, the PSM uses the index of receiv e an tenna to carry informatio n 2 bits an d activ ates a ll tran smit anten nas, which red u ces the complexity at receiver but r esults in the issues of I AS and ICI at th e transmitter . In [22], [ 23], the au thors explored the schemes of transmit antenna selec tio n to enhance the security of SM-MIMO systems. A n ew idea of redefinin g the mapping rules between the informatio n bits and the indice s of transmit antennas was pro posed to achieve secu re transmission s in [24], and th e n the au thors in [25], [26] further improved the security by exploiting th e knowledge of the legitimate channel state inform ation (CSI) to ro ta te bo th the indices of the tra nsmit antennas and th e constellation symb ols. In [24]–[26], the legitimate CSI actually ca n b e regarded as an encryp tion key to en crypt the confidential messages. In other words, the scheme of rotating bo th the in dices of the transmit anten n as an d the constellation symb ols actu ally does not destroy the receive signals at eav e sd ropper s. Ther e fore, when the legitimate channel is slo w fading chan nel, th e key is in variant dur ing a long cohe r ence in terval, an d thus the eav esdropp e r s may decod e th e key by using th e cryptanalysis or m achine learning meth ods. On the other hand, linear p recodin g for SM sy stem s has received some r esearchers’ attentio n in [27]–[3 2 ] . The au- thors in [ 2 7] pro posed two design schemes of g eneralized precod e r, maximu m m inimum distance (MM D) and gu aran- teed Euclidean distance (GED), and a n iterative algorithm to acquire effecti ve so lutions. Then a low-complexity method with sm a ller n umber s of iterations was pro posed to solve the MMD and GED prob le m s in [31]. Meanwhile, the a u - thors in [28], [29] con stru cted a similar MMD problem for space shift keying (SSK) systems, where the optim ization problem was efficiently solved using semi-defin ite r elaxation (SDR) techniques. In [30], the authors intro d uced two design criterions, maximizin g the min imum Euclidean distance and minimizing the bit erro r r ate (BER), to op timize the diag onal linear preco ding m atrix. In [32], a new precoding scheme was propo sed to improve the mutua l infor mation for gen eralized spatial m odulation (GSM) systems by conv erting the GSM systems into a vir tual MI MO system and emp loying the extended ellipsoid algorith m. Howe ver, all the aforementio ned works optimized the lin ear preco ding vector to improve th e BER per forman ce regardless o f security . In [21], the auth o rs in vestigated the design of linear preco d ing to maximize the actual SR (Max-SR) f or secure SSK systems and the M ax- SR based on gr adient d escend (GD) method (Max -SR-GD) was also proposed to solve the correspo n ding optimizatio n problem , but the comp utational co mplexity is extremely high due to the require m ent of a high computatio nal amount to ev aluate the actual SR. Compared to [21], we will focus on the d esign of linear precod in g with lower com plexity or highe r perfor mance in this work. Our main contributions are summ arized as fo llows: 1) D u e to th e absence of a closed- form expression for SR in secure SM systems with finite alphab et input, it is har d to design a practica l feasible linear p recoder of Max- SR with lower-complexity . T o red uce the compu tational complexity of Max-SR pre coder, an approx imated SR (ASR) is deriv e d and presen ted, which is used as an optimization o bjective function . Numerical Mon te-Carlo simulations show that the obtained ASR is very close to the actual SR fo r different n umber s of transmit anten nas and dif f erent typ es of modulation . 2) By m aking use of the closed-fo r m expression of ASR, the op timization pro blem of maximizin g ASR (Max- ASR) is casted and pro posed. T o solve the optimiz a tion problem , a low-complexity precoder, called Max -ASR- GD, is propo sed to iterativ e ly solve the pr oblem by GD algorithm. It is well-known that the GD m ethod can usually co n verge to a locally optimal solution. Our simulation results also show that the pr oposed Max - ASR-GD ac h iev es a slightly lo wer SR than th e Max- SR-GD pro p osed in [21] but with a sign ificantly lower complexity . 3) T o furth er improve the SR perfor mance in the o pti- mization prob lem of Max- ASR, whic h is a typical non- conv ex quadratically constrained quadr atic programm ing (QCQP) problem a nd NP-h ard in general, its o bjective function is first relaxed an d repr esented as the d if- ference betwe en two convex functions by using SDR technique s. T hen, the succ e ssi ve conv ex approxim ation (SCA) method is e m ployed to iteratively solve the con- vex su b prob lems a n d obtain an approxim ately op timal solution. Finally , the prop osed Max-ASR-SCA is proved to be convergent. From simu lation results, it f ollows that the prop osed Max -ASR-SCA outperf orms the Max -SR- GD method an d M a x-ASR-GD in terms of achieving a higher SR. Mor e importan tly , the numb er of itera tio ns of the prop osed Max -ASR-SCA is smaller than those of Max-SR-GD and Max- ASR-GD. The remain d er of this paper is organ ized as follows. In Section I I , the system model of the co nsidered secur e SM- MIMO is presented, an d the optimiz a tion problem o f Max- ASR is fo rmulated in Section I II. In Section IV , two p r ecoding methods, Max -ASR-GD and Ma x-ASR-SCA, are pro posed to solve the optimiz a tion pr oblem, and their co mputatio n al complexities are analyzed. Numerical r esults are presented in Section V . Finally , we make ou r conclu sions in Section VI. Notation: Matrices, vectors, a nd scalars ar e deno te d b y letters of bold upper case, bold lower case, and lower case, respectively . Signs ( · ) − 1 and ( · ) H denote in verse and con- jugate tra nspose, r espectively . Notation E {·} stand s fo r the expectation oper ation. I N denotes the N × N iden tity matrix , and tr( · ) deno tes matrix trace. I I . S Y S T E M M O D E L A. Secure S patial Mod ulation A typical secure SM-MIMO system model is shown in Fig. 1. In th is system, there are a transmitter (Alice) with N t transmit antenn a s, a legitimate receiv er (Bob) with N b receive antennas, and an eavesdropper (Eve) with N e receive antennas. Alice activates one of her N t transmit antennas to emit M -ary amplitude phase mod ulation (APM) sy mbol, and the index of activ ated antenna is also used to carry inform ation. As a result, the SE is log 2 M N t bits per chan n el use (bpcu). T o enhance th e security of such a SM system, a linear precod e r and AN pr ojection at tr ansmitter is adopted to 3 RF Ă 1 N t Eve Ă N e 1 Bob Ă 1 N b A N projection Bit stream blocking Bit stream Mo dul a t e d b i t s Spa tial b i t s Symbol m a pping Linea r precoding G H A ct i vate one antenna to c ar ry m e ss age Ă Fig. 1. System model of linea r precoding schemes for secure SM system guaran tee the secure transmission against Eve’ s eav esdroppin g. Similar to [16], the transm itted baseband signal at Alice may be co nstructed as follows x = p P 1 Vs n,m + p P 2 T AN n , (1) where V ∈ C N t × N t denotes the linear precodin g matrix, and T AN ∈ C N t × N t is the AN pro jec ting matrix. P 1 and P 2 are the power of confiden tial signal and AN, respectively , with power con straint P 1 + P 2 ≤ P t holding , wh ere P t is the total transmit power . n ∈ C N t × 1 is the ran d om AN vector following standard com plex G a ussian distribution C N (0 , I N t ) . s n,m = e n s m , n ∈ [1 , N t ] , m ∈ [1 , M ] , is the input symbo l vector . s m is the norm alized inp ut sy mbol, with E ( | s m | 2 ) = 1 , which is drawn equipro bably from discrete M -ary constellation, an d e n is th e n th column of iden tity matrix I N t . It is worth n oting that the linear precodin g for SM-MIMO systems is d ifferent fro m conventional MIMO systems. In SM-MIMO system s, only o ne an tenna is activated to tran smit modulated symb ol, so the linear precod ing matrix is a d iag- onal m a trix, i.e. , V = diag ( v ) , where v ∈ C N t × 1 stands for th e linear preco ding vector . Moreover , the eleme n ts of linear p recodin g vector v canno t be a c ti ve simultaneo usly . I n other words, on ly the elem ent corresp onding to the ac tivated transmit an tenna is active during each symbo l interval [27]. Let H ∈ C N b × N t and G ∈ C N e × N t denote the comp lex channel m atrices cor respond ing to the legitimate channe l and eav esdropp in g chann el, respectiv ely . This paper assumes th a t Alice has the perfect CSIs of both ch annels, which may b e tru e for active Eve [ 2 1]. Meanwh ile, Bob and Eve attain their own CSIs thro ugh pilot-assisted channel estimation , respectively . It is assumed that chan nel matrices H a nd G both are flat Rayleig h fading with e ach elem e n t being the stand a r d complex-Gau ssian distribution C N (0 , 1) and keep constant during each co herence time. Accordin gly , th e receive signals at Bob and Eve are respectively stated as fo llows y b = Hx + n b = p P 1 HVs n,m + p P 2 HT AN n + n b , (2) y e = Gx + n e = p P 1 GVs n,m + p P 2 GT AN n + n e , (3) where n b and n e are the ad ditive white Gau ssian noise (A WGN) vectors at Bob and E ve with obeying C N (0 , σ 2 b I N b ) and C N (0 , σ 2 e I N e ) , respecti vely . Consequently , with the kn owledge of H and V , Bob can employ the maximu m likelihood detector (MLD) as follows [ ˆ n, ˆ m ] = arg min n ∈ [1 ,N t ] ,m ∈ [1 ,M ] y b − p P 1 HVs n,m 2 . (4) Here, we consider the worst case when Eve knows the lin e ar precod in g matrix V , and th us Eve may also carr y ou t MLD as f ollows [ ˆ n, ˆ m ] = arg min n ∈ [1 ,N t ] ,m ∈ [1 ,M ] y e − p P 1 GVs n,m 2 . (5) Howe ver, the terms of √ P 2 HT AN n an d √ P 2 GT AN n in (2) and (3) is time-varying interference, which will seriou sly degrade their detecting perf ormanc e. I n what follows, we will derive an expression of SR with respect to T AN and V , then we pro ject the AN signals into the null spa ce of legitimate channel b y designin g the P AN . Finally , o ur main aim of this paper is to design a linear p r ecoding matrix to imp rove SR perfor mance. B. Secr ecy Ra te for Secure S patial mod ulation Similar to [21], we c h aracterize the security b y evaluating av e r age SR defined a s ¯ R s = E H , G ( R s ) , (6) where R s is the instantaneo us SR. Accord in g to [7], the SR for secure SM system is defined as follows R s = [ I ( s ; y b ) − I ( s ; y e )] + , (7) where [ a ] + = max { a, 0 } . I ( s ; y b ) and I ( s ; y e ) denote the mutua l info rmation over legitimate and eaves dropp ing channels, respectively . Howe ver , du e to the interf erence plus noise not being Gaussian distributed in (2) and ( 3), it is no t straightfor ward to derive the expression of SR. Similar to [1 6], the interferen ce plus n oise at Bob is de noted as w b = p P 2 HT AN n + n b , (8) 4 then we u tilize a linear whitening tr ansforma tio n matrix Q b to con vert w b into a white noise vecto r n ′ b = Q − 1 / 2 b w b , (9) where Q b is th e covariance m atrix of w b giv en by Q b = P 2 HT AN T H AN H H + σ 2 b I N b . (10) Substituting (10) into (9) and considerin g that n and n b are indepen d ent, we have E ( n ′ b ) = 0 and E ( n ′ b n ′ H b ) = I N b , thus n ′ b ∼ C N (0 , I N b ) ca n be c onsidered as an A WGN vector . By pre-mu ltiplying the linear m atrix Q b , th e receiver signal in ( 2) can b e simplified as y ′ b = p P 1 Q − 1 / 2 b HVs n,m + n ′ b , (11) which yields, fo r a specifical H , the conditio n al p robab ility density function (PDF) of p ( y ′ b | s n,m ) p ( y ′ b | s n,m ) = 1 π N b exp − y ′ b − p P 1 Q − 1 / 2 b HVs n,m 2 . (12) W e assume that each a n tenna is activ ated eq uiprob ably to transmit co nfidential message an d each symbo l s m is uni- formly selected fr om M -ary constellation . Thus, the complex receive signal vecto r y b at Bob obeys the distribution as follows p ( y ′ b ) = 1 M N t N t X n =1 M X m =1 p ( y ′ b | s n,m ) . (13) As per (12) and (13), following the method given in [33], the mutual information I ( s ; y ′ b ) is written as I ( s ; y ′ b ) = log M N t 2 − 1 M N t N t X n =1 M X m =1 E n ′ b " log 2 N t X n ′ =1 M X m ′ =1 exp k n ′ b k 2 − α n ′ ,m ′ n,m + n ′ b 2 !# , (14) where α n ′ ,m ′ n,m = p P 1 Q − 1 / 2 b HV ( s n,m − s n ′ ,m ′ ) . (15) It shou ld be noted th at the I ( s ; y ′ b ) is equivalent to I ( s ; y b ) , since the tran sf o rmation is lin ear [16]. Similar to (14), w e can derive the mutual in formatio n I ( s ; y e ) as fo llows I ( s ; y e ) = log M N t 2 − 1 M N t N t X n =1 M X m =1 E n ′ e " log 2 N t X n ′ =1 M X m ′ =1 exp k n ′ e k 2 − δ n ′ ,m ′ n,m + n ′ e 2 !# , (16) with δ n ′ ,m ′ n,m = p P 1 Q − 1 / 2 e GV ( s n,m − s n ′ ,m ′ ) , (17) n ′ e = Q − 1 / 2 e ( p P 2 GT AN n + n e ) , (18) where Q e = P 2 GT AN T H AN G H + σ 2 e I N e is the linear whiten- ing tr ansforma tio n matrix a t Eve. C. Design the AN Pr ojecting Matrix In this paper , we consid e r the scenarios with N t ≥ N b , thus the AN signals can be p rojected into the null sp ace of legitimate ch a nnel. Here, we present a closed-fo r m expression of AN projection matrix , which is different from th e singular value d ecompo sition (SVD) method in [16]. Accordingly , the T AN can b e directly calcu lated as follows [ 34] T AN = 1 µ h I N t − H H HH H − 1 H i , (19) where µ = k I N t − H H HH H − 1 H k F is the normalized factor f or satisfying tr( T AN T H AN ) = 1 with the k A k F representin g Frob enius nor m of a matrix A . It can be seen from (19) that T AN is the projecto r of the null space o f legitimate chan nel, thus we have the following e quality HT AN = 0 , Q b = σ 2 b I N b . (20) I I I . O P T I M I Z A T I O N P RO B L E M O N T H E L I N E A R P R E C O D I N G M AT R I X In this sectio n , we first p resent a o ptimization p roblem of Max-SR to o ptimize the lin ear precod ing matrix . T hen, a simple expression of ASR is developed to be the co n ven ie n ce of dealing with the original optimization problem o f Max- SR. Further more, due to the linear preco ding matrix V being diagona l, we turn to optimize the lin ear precod in g vector v = Diag ( V ) for sake o f convenience. A. Maximizing the Secrecy Rate After designing the AN projecting matrix , we turn to optimize th e lin ear precodin g matrix by solvin g the following problem of Max- SR maximize V R s ( V ) (21a) sub ject to : P 1 tr( VV H ) N t ≤ P t − P 2 . (21b) It is worth no tin g that the ab ove optimiz a tion pro blem of d e- signing the linear preco der matrix is intrac table in g e n eral, and we need m a ny ev alu ations for calcu la tin g the actual SR du e to the absence of the closed- f orm expression of SR. Actu ally , the above optimizatio n prob lem can be so lved by using GD method as illustrated in [2 1], but it has a high com putation a l complexity . As we will see later , to reduce the c o mputatio n al complexity , we present a closed -form appro x imated e x pression of SR, which can be used as an effective metr ic to optimize the linea r pr ecoding matr ix . B. Appr ox imated Expression fo r S ecr ecy Rate In this subsection, we pr esent the tight lower b o unds on mutual in formatio n over legitimate and eavesdropping chan- nels, respectively , and p rovide an a c curate approx imation to SR. Similar to [33] and [35], by using Jensen ’ s inequality and 5 the integrals of exponential function , we have the tight lower bound of I ( s ; y b ) I ( s ; y b ) LB = log M N t 2 − 1 M N t N t X n =1 M X m =1 log 2 N t X n ′ =1 M X m ′ =1 exp − α n ′ ,m ′ n,m 2 2 . (22) Similarly , the mutual inf ormation of eavesdropping c hannel can b e lo wer boun ded by I ( s ; y e ) LB = log M N t 2 − 1 M N t N t X n =1 M X m =1 log 2 N t X n ′ =1 M X m ′ =1 exp − δ n ′ ,m ′ n,m 2 2 . (23) Then an accur a te app roximatio n of SR can be given by R ′ s = [ I ( s ; y b ) LB − I ( s ; y e ) LB ] + . (24) T o further make the optimization variable clear, the term α n ′ ,m ′ n,m 2 in (22) can be represented as [31] α n ′ ,m ′ n,m 2 = P 1 · Q − 1 / 2 b HV ( s n,m − s n ′ ,m ′ ) 2 (25a) = P 1 · tr Q − H b HV∆ n ′ ,m ′ n,m V H H H (25b) = P 1 · v H H H Q − H b H ⊙ ∆ n ′ ,m ′ n,m v (25c) = P 1 · v H B n ′ ,m ′ n,m v , (25d) where ∆ n ′ ,m ′ n,m = ( s n,m − s n ′ ,m ′ )( s n,m − s n ′ ,m ′ ) H , (26) B n ′ ,m ′ n,m = h ( H H Q − H b H ) ⊙ ∆ n ′ ,m ′ n,m i . (27) Similarly , the term δ n ′ ,m ′ n,m 2 in (23) can be represented as δ n ′ ,m ′ n,m 2 = P 1 · v H h G H Q − H e G ⊙ ∆ n ′ ,m ′ n,m i v (28a) = P 1 · v H E n ′ ,m ′ n,m v , (28b) with E n ′ ,m ′ n,m = h G H Q − H e G ⊙ ∆ n ′ ,m ′ n,m i , (29) where ⊙ denotes th e Hadam ard product of two matrices. W e note that (25) and (28) are achieved by utilizing the trace proper ty , i.e . , tr( AB ) = tr ( BA ) for m a tr ices A and B . C. Maximizing the App r oximated S R Making use of the above accu rate approxima tion o f SR, the Max-SR op timization problem in (21) can be converted into the following simplified pro b lem maximize v R ′ s ( v ) (30a) sub ject to : tr( vv H ) ≤ N t , (30b) where R ′ s ( v ) is given in (31) a t the top of n ext page, and the (30b) is obtained with P 1 + P 2 ≤ P t . The above Max- ASR can significantly reduce the co m plexity compared to Max-SR in (21) as sho wn in what f ollows. Howe ver , it can be seen from (31) that the ab ove optimization problem is a non -conve x QCQP pro blem, thus it is NP-hard in gen eral. In what follows, we present a lower-complexity GD method and propo se the SCA me th od to addre ss the ab ove op tim ization pro blem. I V . P R O P O S E L O W - C O M P L E X I T Y L I N E A R P R E C O D I N G S C H E M E S O F M A X I M I Z I N G A S R T o provide a rapid solution to the optimization problem in (30), two low-comp lexity m ethods, Max-ASR-GD and Max- ASR-SCA, are presented in this section . For the fo rmer, simi- lar to [2 1], using a gradie n t vector of the clo sed-form ASR, th e iterativ e GD algo rithm can be employed to yield an extremely low-complexity solu tion to the optimization prob lem as given in (30), which converges to a locally optimal solu tion. For the latter , the original pr oblem is first relaxed to a difference of conv ex (DC) pr o gramm in g b y using the SDR method, and the first-order T a ylor approximatio n expansion and SCA way are combined to achieve a n app roximate ly optimal solution. A. Pr oposed Max-ASR-GD Metho d Due to th e nonco n vexity of th e problem (30), it is in tractable to ob ta in a glob ally optimal solution in gen eral. Howe ver, it is possible to employ the GD method , wh ich iteratively searches for a locally op tim al solu tion. The Max-ASR-GD method firstly needs to calculate th e gradien t of R ′ s ( v ) with respect to v . This grad ient is directly shown in (32) at the top of th e next p age. In (32), κ b and κ e are d efined as follows κ b = N t X n ′ =1 M X m ′ =1 exp − P 1 · v H B n ′ ,m ′ n,m v 2 ! , (33) κ e = N t X n ′ =1 M X m ′ =1 exp − P 1 · v H E n ′ ,m ′ n,m v 2 ! . ( 34) Based on the grad ient of R ′ s ( v ) over v in (3 2) , we upda te the linea r pr ecoding vector in the following way v k +1 = v k + µ ∇ v R ′ s ( v k ) , (35) where µ and k are the step size and iterative index, respec- ti vely . It should be noted that the upd ated linea r precoding vector should satisfy the po wer constraint, the po wer normal- ization p rocedu re is written as v = q N t / tr( vv H ) v . (36) The de ta iled p rocedu re of th e pro posed Max-ASR-GD method is illustrated in Algo rithm 1 . The algorith m iterati vely searches for an optimal p . It is guara n teed that this algo rithm conv e rges to a locally optimal solution. It should be noted that the a u thors in [21] prop osed a Max-SR-GD method to solve an optim ization p r oblem similar to (2 1). Howev er , the me th od Max -SR-GD in [ 2 1] is to optimize the linear p recodin g vector in secu re SSK sy stem s, 6 R ′ s ( v ) = 1 M N t N t X n =1 M X m =1 " log 2 N t X n ′ =1 M X m ′ =1 exp − P 1 tr( v H E n ′ ,m ′ n,m v ) 2 !! − log 2 N t X n ′ =1 M X m ′ =1 exp − P 1 tr( v H B n ′ ,m ′ n,m v ) 2 !!# (31) ∇ v R ′ s ( v ) = P 1 M N t N t X n =1 M X m =1 N t P n ′ =1 M P m ′ =1 exp − P 1 · v H B n ′ ,m ′ n,m v 2 B n ′ ,m ′ n,m v 2 κ b · ln2 − N t P n ′ =1 M P m ′ =1 exp − P 1 · v H E n ′ ,m ′ n,m v 2 E n ′ ,m ′ n,m v 2 κ e · ln2 (32) Algorithm 1 The prop osed Max-ASR-GD method for solving problem (30) 1: Initialize v 0 with satisfying tr( v 0 v H 0 ) ≤ N t , set th e step size µ , the minimum tolerance µ min and k = 0 2: Calculate R ′ s ( v k ) b y u sing (3 1) 3: Calculate ∇ v R ′ s ( v k ) b y u sing (3 2) 4: If µ ≥ µ min , goto step 5, otherwise stop and r eturn v k 5: Calculate v k +1 by using (35) and no rmalize v k +1 by using (36) 6: Calculate R ′ s ( v k +1 ) b y u sing (3 1) 7: If R ′ s ( v k +1 ) ≥ R ′ s ( v k ) , th e n goto step 8, otherwise, let µ = µ/ 2 and g oto step 4 8: Do k = k + 1 goto step 3 9: Output the v k , then calculate the SR R s ( v k ) by using (14) and (16) and it can be steadily extended to secu re SM systems. There exists two serio u s prob lems of facing Max-SR-GD: no closed- form expression for SR and h ig h-com p lexity . No closed -form expression me a n s th a t it req uires com plex comp utation to ev aluate the actual value of SR and its g radient per iteratio n . B. Pr oposed Max-ASR -SCA Method The optimization pro blem (30) is a n on-co n vex QCQP problem , wh ich motiv ates us to explore the SDR method . T he SDR is a powerful and computation ally ef ficient app roxima- tion technique , wh ich is particularly ap p licable to non -conve x QCQP prob lems. Many pra ctical expe r iences have indicated that SDR is capable of providing near optimal appro ximation s [36]. Let us introduc e a new matrix variable W = vv H , then we obtain the equivalence o f (3 0) as follows maximize W R ′ s ( W ) (37a) sub ject to : tr( W ) ≤ N t (37b) W 0 (37c) rank( W ) = 1 , (37d) where W 0 deno tes that W is a semi- d efinite ma tr ix. Howe ver, the above o ptimization pro blem still is intr a ctable due to the existence of the non-conve x r ank-o ne constraint. Actually , af te r removin g the non-co n vex rank-one co nstraint in the above optimizatio n pro b lem, (37) is relaxed a s maximize W R ′ s ( W ) (38a) sub ject to : tr( W ) ≤ N t (38b) W 0 . (38c) By d roppin g the ran k-one constrain t, the above SDR achieves a upper bou nd on the optimal solution to the primal p roblem (38). If the o ptimal solution W ∗ to (38) is rank- o ne, the optimal V ∗ is the eig e n vector c orrespon ding to the largest eigenv alue of W ∗ . Oth erwise, the ra ndomiza tio n technique may b e used to ob tain ap proxim a ti ve optimu m. In what follows, we f ocus o n solvin g the optimization p roblem in ( 3 8). In (38), the two constraints are conv ex sets. But its objectiv e function is in form of subtraction of two conve x fun ctions [37]. In general, th is difference is non-co ncave. Obviously , the objectiv e function in (3 8) is also non- concave. It is well- known that SCA is an efficient way to solve this no n-conve x DC p rogra m ming pro blem. T h e algor ithm begins with an initial feasible point, the non-c o n vex objective function is approx imated b y a strictly conve x arou nd this point. The resulting conv ex pr o blem is solved to obtain the feasible p oint for next iteration. The iteration is repeated until the stopp ing criterion is satisfied [38]. For convenience of presen tation, we r ewrite the objective function as R ′ s ( W ) = 1 M N t N t X n =1 M X m =1 [ f 1 ( W ) − f 2 ( W )] , (39) where f 1 ( W ) and f 2 ( W ) are defined as f 1 ( W ) = lo g 2 N t X n ′ =1 M X m ′ =1 exp − tr( WE n ′ ,m ′ n,m ) 2 ! , (40) f 2 ( W ) = lo g 2 N t X n ′ =1 M X m ′ =1 exp − tr( WB n ′ ,m ′ n,m ) 2 ! . (4 1 ) In (39), f 1 ( W ) and f 2 ( W ) are log-su m-exp fun ctions, wh ich are proved to be conv ex [3 7], as a result, R ′ s ( W ) is non- concave. It is well-known that a linear fun ction is bo th conve x and concave. I n the following, we em ploy the first-order T ay lo r 7 series expan sion around a feasible po int W 0 on f 1 ( W ) to transform f 1 ( W ) into a linear fu n ction. Due to f 1 ( W ) being conv ex and differentiable, th e fir st-o rder T aylo r app r oximation actually is a glob al underestima to r of the fu n ction [37], i.e. , the following ineq uality h olds f 1 ( W ) ≥ f 1 ( W 0 ) + tr [ ∇ f 1 ( W 0 ) ( W − W 0 )] , (42) where ∇ f 1 ( W 0 ) is defined as the g radient of the functio n f 1 ( W ) at th e point W 0 , which is derived as ∇ f 1 ( W 0 ) = − N t P n ′ =1 M P m ′ =1 exp − tr W 0 E n ′ ,m ′ n,m 2 E n ′ ,m ′ n,m H 2ln 2 N t P n ′ =1 M P m ′ =1 exp − tr W 0 E n ′ ,m ′ n,m 2 . (43) Then, given a fixed W k − 1 , th e p roblem (38) can be iterati vely computed by solvin g the following conve x subp roblem maximize W k 1 M N t N t X n =1 M X m =1 f ( W k , W k − 1 ) (44a) sub ject to : tr( W k ) ≤ N t (44b) W k 0 , (44c) with f ( W k , W k − 1 ) (45) = f 1 ( W k − 1 ) + tr [ ∇ f 1 ( W k − 1 ) ( W k − W k − 1 )] − f 2 ( W k ) where f ( W k , W k − 1 ) is in f o rm of d ifference o f line ar func- tion an d conve x functio n, thus it is a co ncave fu nction with respect to W k . Ther e fore, the pr oblem (44) is a c o n vex semi- definite p rogram ming (SDP) prob le m , which can be h andled conv e n iently and e fficiently b y using the con vex optimizatio n toolbox CVX or interior-point metho d. Finally , the detailed proced u res of the proposed Max-ASR-SCA method ar e pre- sented in Algo r ithm 2. Algorithm 2 The proposed Max -ASR-SCA metho d for solv- ing p roblem (38) 1: Initialization: find a f e asible po int v 0 , W 0 = v 0 v 0 H , with satisfying the constraints in pro blem (38), set the tolerance ǫ , and k = 0 2: Rep eat 3: Solve the prob le m (44) with W k , and ob tain W ∗ k 4: Set k ← k + 1 5: Update W k = W ∗ k 6: Calculate R ′ s ( W k ) by u sin g (3 9) 7: Un til | R ′ s ( W k ) − R ′ s ( W k − 1 ) |≤ ǫ is met 8: Output the optim a l W ∗ = W k − 1 It is worth no ting th at as long as the each app roxima tio n of objective function satisfies the tightness and differentiation condition s, the proposed Max- ASR-SCA method is guaranteed to conv e rge to a p oint th at satisfies the Kar ush-Kuhn- Tucker (KKT) optim ality cond itio ns of problem (3 8) [38]. Mea nwhile, we present a simple pr oof for the conver gence of the Max- ASR-SCA method in Appendix A . By using the p r oposed Max -ASR-SCA me th od, we actually obtain a SDR solu tion W ∗ to problem (3 7). It is worth while noting that the solu tion is an a pprox imately optima l solu - tion. I f the solution W ∗ is ran k-one , th e optimal v ∗ is the eigenv e ctor corre sponding to the largest eigen value of W ∗ . In fact, the solu tio n may not be rank on e, we may emp loy the ran d omization metho d to search an approx imated solution. Such a rando mization method has be em pirically found to provide efficient approximatio ns fo r a variety of applicatio ns [36]. Until now , we complete our d esign of th e propo sed two methods. C. Complexity Analysis and Comp arison In this subsectio n , we condu ct the complexity analysis o n our pro posed two linear preco ding methods and c o mpare them with the complexity of th e GD me th od in [21]. Here, consider that a matrix -vector multiplication y = Ax , where A ∈ C m × n costs 2 mn floatin g-poin t opera tions (FLOPs), and a m atrix- matrix product C = AB , where A ∈ C m × n and B ∈ C n × p , costs 2 mnp FLOPs (See Appendix C in [37] f o r d etails). For the pr oposed GD method in subsection A, its co m puta- tional co mplexity dep ends m ainly o n the following three parts: (a) comp ute the app roximatio n o f SR, (b) compu te the gradie n t of ASR, an d (c) the num ber of iteration s. After the complexity of expo nential and logar ithm oper a tio ns in (2 2) and ( 2 3) a r e omitted, we have the computation al co mplexity of p art (a ) C a = 2 M 2 N 2 t (4 N 2 t + N b + N e ) . (46) In (32), co mputing the terms E n ′ ,m ′ n,m and B n ′ ,m ′ n,m both req uire about 3 N 2 t FLOPs, where we ignore the complexity of c om- puting the H H Q − H b H and G H Q − H e G , which are in variant matrices fo r a specifical channel. I n fact, ∆ n ′ ,m ′ n,m is a sparse matrix, which h as at most fo ur non-z e r o eleme n ts. Therefo re, the co mplexity of part (b ) ma y be a pprox imately given by C b = 2 M 2 N 2 t (3 N 2 t + 2 N 2 t + 2 N t + 2 N 2 t ) . ( 4 7) Let D 1 denotes the numb er of iterations in Algo rithm 1, then the final computational co m plexity of the Max-ASR-GD method is as follows C Alg . 1 = 2 D 1 M 2 N 2 t (11 N 2 t + 2 N t + N b + N e ) . (48) For the Ma x -SR-GD me thod in [21], its comp lexity analysis is similar to (48). Let N samp denote the nu mber of realization s of no ise f o r accu rately ev alu a ting the actual SR, then the computatio nal complexity of ev aluating SR is about C e = 4 M 2 N t 2 N samp 2 N t 2 + N b + N e . (49 ) It is worthwhile notin g that the actual SR in (14) r equires av e r aging over at least N samp = 50 0 realizations of n oise for accurately ev alua tin g SR. Similar ly , the com putationa l complexity of e valuating th e curr ent grad ient vector is C g = 2 M 2 N 2 t N samp (3 N 2 t + 2 N 2 t + 2 N t + 2 N 2 t ) . (50) Let D 2 denote the numb er of iterations for Algo rithm.1 in [21], th en its complexity is written as C = 2 D 2 M 2 N 2 t N samp (11 N 2 t + 2 N t + 2 N b + 2 N e ) . (51) 8 Finally , fo r the pro p osed Max- ASR-SCA m e th od, its c o m- putational complexity also dep ends on the following three aspects: (a) compu te the (39), (b ) solve the conve x op- timization pr oblem in (44), and (c) th e nu mber of iter a- tions. The computationa l co mplexity of aspect (a) is abo ut 2 M 2 N t 2 2 N 3 t + 3 N t 2 FLOPs. It is noted that the exact com- plexity of aspec t (b) depen ds heavily on the specific con vex solver . Here, it is assumed that the interior point method [39] is used. The o bjective f unction o f problem (44) co nsists of M N t conv ex fu nctions, one lin ear inequality co nstraint, and one line ar matrix inequ ality constraint. Acc o rding to [ 3 6], [39], this p r oblem in (44) may be solved with a worst-case complexity C sdp = O ( N 4 . 5 t log(1 /ς )) + 2 M 2 N 2 t (3 N 3 t + 4 N 2 t ) , ( 5 2) where ς is a given solutio n accuracy , and the secon d term is the comp lexity of constru cting the objective fun ction. Let D 3 denotes the numb er of iter ations in Algor ithm 2. T herefor e, the com plexity of the propo sed Max-ASR-SCA meth od in Algorithm. 2 is approximated as C Alg . 2 = D 3 C sdp + 2 D 3 M 2 N t 2 2 N 3 t + 3 N 2 t . (53) In su m mary , from th e above complexity analysis, it can b e seen that the th ree method s all have a poly n omial complexity . The pr oposed Max-ASR-GD in Algorith m. 1 ha s the lowest complexity a mong the three schemes, an d the propo sed Max- ASR-SCA metho d is in b etween Max -ASR-GD and Max- SR- GD in [21] in terms of complexity du e to N samp ≫ N t . This means that Max-SR-GD is o f th e highest comp lexity among the three m ethods. From (48) and (53), it fo llows that the complexities of Max-ASR-GD an d Max -ASR-SCA have the orders O ( N 4 t ) and O ( N 5 t ) provided that o ther parameter s are fixed, r espectively . Th erefore, w h en the number of transmit antennas tends to large-scale, the p roposed Max -ASR-GD method ha s resulted in a dramatic redu ction on co m putation a l complexity compa r ed to Max-ASR-SCA an d Max -SR-GD. V . N U M E R I C A L R E S U LT S A N D D I S C U S S I O N S In this section, we pr esent o ur n umerical simulation results to ev aluate the p roposed two linear precod in g method s. I n the fo llowing simulation s, the noise power o f Bob and Eve is assumed to be equal, i.e. , σ 2 b = σ 2 e , an d the achievable SR is evaluated by usin g (6) and calcu lated by averaging over 50 realizations of channels. M e anwhile, some n ecessary parameters are set as f ollows: N b = N e = 2 ; µ = 0 . 5 , and µ min = 0 . 01 fo r Algorith m 1; ǫ = 0 . 001 for Algor ithm 2. First, in or d er to verify th e v a lid iness of using ASR as the design m etric. Fig. 2 plots the cu r ves of the a p prox im ated and simu lated actu al SRs versus signal-to- noise ratio (SNR), where Sim-SR stand s for the simulated actual SR for the sake of simplicity . It is no ted that the approxim ated and actual SR are calculated by ( 24) and (7), respectively . It can be seen that all ASR cur ves ar e very close to these of simulated actual SR for almost all SNR regions. In other words, the rate difference between ASR and simulated actua l SR is tri vial. Therefor e, it is reasonab le to employ the closed -form expression of ASR in (24) as the design metric. -15 -10 -5 0 5 10 15 SNR(dB) 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 5 SR (bps/Hz) ASR N t =8 M=4 Sim-SR N t =8 M=4 ASR N t =8 M=2 Sim-SR N t =8 M=2 ASR N t =4 M=2 Sim-SR N t =4 M=2 Fig. 2. Approximated and simulated SR -15 -10 -5 0 5 10 15 SNR (dB) 0 1 2 3 4 5 SR (bps/Hz) Proposed Max-ASR-GD Proposed Max-ASR-SCA Max-SR-GD in [21] No linear precoding Fig. 3. SR performa nce with N t = 8 and M = 4 . Fig. 3 demonstrates the cu rves of SR per forman ce versus SNR for three linear preco ding methods Max-ASR-GD, Max- ASR-SCA, and Max-SR-GD with no linear prec oding schem e as a per forman ce ben chmark . It c an be seen that the three methods can achieve different SR p erform ance gains over the no preco ding case. The SR perfor mance of p roposed Max- ASR-GD metho d is worse than Max -ASR-SCA but tend s to conv e n tional Max-SR-GD in [21]. It has a h igh pro bability that the two based-GD method s, Max -ASR-GD and M a x-SR-GD, conv e rge to their locally op timal solution s while th e p roposed Max-ASR-SCA meth od can o btain the appro ximately optimal solution. The refore, th e pro posed Max-ASR-SCA achieves the best SR perfo rmance amon g the three pr ecoding scheme s. Fig. 4 shows the cumu lativ e distribution func tio n (CDF) curves of SR fo r the thr ee linear p recoding meth ods with different ty pical values of SNRs: -5 dB, 0d B, and 5dB. Th e curves are gener ated by calcu lating SR over 500 rea lizations of all chann els. F o r all thr e e methods, as SNR increases, the CDF curves of SR moves towards the right-han d side. This 9 0 1 2 3 4 5 SR (bps/Hz) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 CDF Proposed Max-ASR-GD Proposed Max-ASR-SCA Max-SR-GD in [21] No linear precoding SNR=0dB SNR=-5dB SNR=5dB Fig. 4. CDF of SR with N t = 8 and M = 4 . -15 -10 -5 0 5 10 15 SNR (dB) 0 0.5 1 1.5 2 2.5 3 SR (bps/Hz) Proposed Max-ASR-GD Proposed Max-ASR-SCA Max-SR-GD in [21] No linear precoding Fig. 5. SR performa nce with N t = 4 and M = 2 . means that the value o f SR b ecomes large as SNR incr eases. Additionally , for all three given values of SNR, the fou r methods have a decreasing order in ter ms of SR perform a nce as follows: Max-ASR-SCA, Max- SR-GD in [2 1], Max-ASR- GD, and witho ut linear precod ing. In ord er to examine the im pact of N t and M on SR perfor mance, Fig. 5 p resents the curves o f SR per forman ce versus SNR for the three metho ds with N t = 4 , an d M = 2 . It can be seen th a t th e the SR p erform ance trend in Fig. 5 is similar to that in Fig. 3. Compared to no linear pr ecoding , the prop osed M ax-ASR-SCA and Max- ASR-GD, an d the Max-SR-GD method in [21] a c hieve 1 b ps/Hz, 0 . 7 bps/Hz, and 0.6 bps/Hz SR improvement at SNR=15 dB, respectiv e ly . Compared to conventional Max-SR-GD, the SR impr ovemen t gain ach iev able by the propo sed Max -ASR-SCA is abou t 13% at SNR=15dB, which is a nice result. Fig. 6 illustrates the h isto g ram of pr obability mass fun ction (PMF) of num ber of iterations for the prop osed Max-ASR- SCA, and Max -ASR GD with conventional Max - SR-GD in 0 10 20 30 40 50 60 0 0.1 0.2 0.3 0.4 PMF Max-SR-GD in [21] 0 10 20 30 40 50 60 0 0.1 0.2 0.3 0.4 PMF Proposed Max-ASR-GD 10 20 30 40 50 60 Number of iterations 0 0.1 0.2 0.3 0.4 PMF Proposed Max-ASR-SCA Fig. 6. PMF of numbers of iteration s with N t = 4 , M = 2 , and SNR = 5 dB. [21] as a performan ce referen ce. I t is noted that 500 channe l trials are condu c ted to show the distribution of number of iterations. It can be seen that nea r 90 perc e nt trials converge within 30, 25 and 8 iter a tio ns for c o n ventional Max-SR- GD in [21], the pr oposed Max -ASR-GD, and Max-ASR-SCA methods, respec ti vely . In oth er words, the prop osed Max - ASR-GD con verges slightly faster th an con ventio nal Max -SR- GD but slower th an pr o posed Max-ASR-SCA. Althou g h the propo sed Max-ASR-SCA meth od co n verges within a fewer number of iterations, its co mplexity of ea ch iteration is hig her than that of the p r oposed Max-ASR-GD method. Fig. 7 presents th e curves of the average number o f itera- tions versus SNR for the above thr e e linear pr e coding schemes. It is o bserved th at the average number of iter ations of f o r the two based-GD methods decrea se as SNR increases. Howe ver, for the Max-ASR-SCA sch eme, the a verag e nu mber of itera- tions slightly increases wh en SNR increases. When SNR tends to be larger tha n 15dB, the average nu mber of iterations nearly keep constant for thr ee linear preco d ing schemes. From Fig. 7, it also c a n be seen that the three sch emes hav e an increasing order in ter ms o f con vergence p erform ances as f ollows: Max- SR-GD, Max-ASR-GD, and Max-ASR-SCA. T o make a detailed comp lexity compar ison amon g the three lin ear precoding schemes, Fig. 8 shows the curves of their co m plexities versus N t . I n acco r dance with Fig. 6, th e number s of iterations are set as D 1 = 25 , D 2 = 30 , D 3 = 8 for in suring 90 % trials conv e rge. It can be seen that the Max- 10 -15 -10 -5 0 5 10 15 20 25 SNR (dB) 0 5 10 15 20 25 30 35 40 45 Average number of iterations Proposed Max-ASR-GD Proposed Max-ASR-SCA Max-SR-GD in [21] Fig. 7. A vera ge number of iteratio ns versu SNR with N t = 4 and M = 2 . 10 20 30 40 50 60 N t 10 6 10 7 10 8 10 9 10 10 10 11 10 12 10 13 10 14 FLOPs Proposed Max-ASR-GD Max-SR-GD in [21] Proposed Max-ASR-SCA Fig. 8. Numbers of FLOPs versu N t with M = 4 . SR-GD method in [21] has an extremely high comp lexity compare d to the two p roposed metho ds. The complexities of the p roposed Max-ASR-GD a n d Max -ASR-SCA are two- order-of-mag nitude, and one-o rder-of-mag n itude lower than that of conv entional Max- SR-GD as th e value of N t is larger than 30, resp ectiv e ly . T hus, the pro p osed two metho ds leads to a significan t complexity reduction over M a x -SR-GD. This makes them app licable to the fu ture secure spatial modulation networks. Furthermo re, compar ed to Max-SR-GD and Max- ASR-SCA, the main a d vantage of the proposed Max-ASR-GD is its extreme ly-low-complexity . Esp ecially , as the value o f N t tends to medium -scale and large-scale, its compu tational complexity is far lower tha n tho se o f Max-SR-GD and Max- ASR-SCA. V I . C O N C L U S I O N In this pap er , we designed two linear precoding schemes for secure SM system s. In order to simplify the or ig inal optimization p roblem of Max- SR-GD an d reduce its com- putational complexity , a simple an d analytical expression of ASR fo r SR was der iv ed as a d esign or optimization metric. Subsequen tly , two low-complexity linear prec o ding schemes, namely Max-ASR-GD and Max- ASR-SCA, were developed based on convex optimization techniqu es. Ou r examination first demo nstrated that the p r oposed Max-ASR-SCA ou tper- forms the con ventio nal Max-SR-GD in terms of achieving a higher SR with a o ne-ord er-of-magnitude lower complexity . In add ition, th e pro posed Max- A SR-GD achieves a two-order- of-mag nitude lower com plexity tha n Max-SR-GD at the cost of a negligib le SR p erform ance loss, wh ich shows tha t the propo sed Max- ASR-GD strikes a g ood balance between the complexity and SR perf o rmance. The pro posed two low- complexity linear precoder s are attractive for fu ture MIMO networks with secure sp a tial m odulation . A P P E N D I X A P R O O F O F T H E C O N V E R G E N C E F O R T H E M A X - A S R - S C A First, conside r that W k is a feasible solution of problem (38) an d f 1 ( W ) is a conve x fu n ction with respe c t to W , so we ha ve the following ineq uality f 1 ( W k +1 ) ≥ f 1 ( W k ) + tr( ∇ f 1 ( W k ) ( W k +1 − W k )) , (54) where W k +1 is a updated solu tion o f problem ( 38) by solving the p roblem (4 4) with a given feasible p oint W k . Then, accordin g to th e objec tive function in ( 4 4a), we have the following inequality N t X n =1 M X m =1 f ( W k +1 , W k ) ≥ N t X n =1 M X m =1 f ( W k , W k ) . (55) Based on the de fin ition of f ( W , W 0 ) in (45), f ( W k +1 , W k ) and f ( W k , W k ) is given by f ( W k +1 , W k ) (56) = f 1 ( W k ) + tr [ ∇ f 1 ( W k ) ( W k +1 − W k )] − f 2 ( W k +1 ) , f ( W k , W k ) = f 1 ( W k ) − f 2 ( W k ) . (57) Finally , by substituting (56) and (57) into ( 55) and using the inequality in (54), we ha ve th e following ineq uality N t X n =1 M X m =1 [ f 1 ( W k +1 ) − f 2 ( W k +1 )] ≥ N t X n =1 M X m =1 [ f 1 ( W k ) − f 2 ( W k )] . (58) It is o bserved the achieved ob jectiv e fu n ction value in (38) is mo notone n on-d e creasing a n d b o unded as the number of iterations increases, thus we may conclud e the SCA algorithm conv e rges. Until now , we com plete the p roof of the co n ver- gence fo r the Max-A SR-SCA. 11 R E F E R E N C E S [1] R. Y . Mesleh, H. Haas, S. Sinanovic, W . A. Chang, and S. Y un, “Spatial modulati on, ” IE EE T rans. V eh. T echnol . , vol . 57, no. 4, pp. 2228–2241, Jul. 2008. [2] M. D. Renzo, H. Haas, and P . M. G rant, “Spatial modulation for multiple -antenna wireless systems: a surv ey , ” IEE E Commun. Mag . , vol. 49, no. 12, pp. 182–191, Dec. 2012. [3] J. Jegana than, A. Ghrayeb, and L . Szczecinski , “Spatial modulation: optimal detecti on and performanc e anal ysis, ” IEEE Commun. Lett. , vol. 12, no. 8, pp. 545–547, Aug. 2008. [4] M. Di Renzo, H. Haas, A. Ghrayeb, S. Sugiura, and L. Hanzo, “Spatia l modulati on for generali zed mimo: challenges, opportunitie s, and imple- mentati on, ” P r oceedings of the IE EE , vol. 102, no. 1, pp. 56–103 , D ec. 2014. [5] P . Y ang, M. Di Renzo, Y . Xiao, S. Li, and L. Hanzo, “Design guideli nes for spatia l modula tion, ” IE EE Communications Surve ys & T utorials , vol. 17, no. 1, pp. 6–26, May . 2014. [6] N. Serafimovski, A. Y ounis, R. Mesleh, P . Chambers, M. Di Renzo, C.-X. W ang, P . M. Grant , M. A. Beach , and H. Haas, “Practi cal im- plementa tion of spatial modulation, ” IEEE T rans. V eh. T echnol , vol. 62, no. 9, pp. 4511–4523, Jun. 2013. [7] A. D. W yner , “The wire-tap channel, ” B ell System T ech. J . , vol. 54, no. 8, pp. 1355–1387, Oct. 1975. [8] Y . S. Shiu, S. Y . Chang, H. C. Wu , C. H. Huang, and H. H. Chen, “Physica l layer security in w ireless networks: a tutorial, ” IEE E W irele s s Commun. , vol. 18, no. 2, pp. 66–74, Apr . 2011. [9] H. M. W ang, Q. Y in, and X. G. Xia, “Distrib uted beamforming for physical -layer security of two-w ay relay networks, ” IEE E T rans. Signal Pr ocess. , vol. 60, no. 7, pp. 3532–35 45, Mar . 2012. [10] N. Zhao, F . R. Y u, M. Li, Q. Y an, and V . C. M. Leung, “Physical layer security issues in interferenc e-alig nment-based wireless networks, ” IEEE Commun. Ma g. , vol. 54, no. 8, pp. 162–168, Aug. 2016. [11] F . Shu, X. W u, J. L i, R. Chen, and B. V ucetic, “Robust synthesis scheme for secure multi -beam direct ional modulation in broadcasting systems, ” IEEE A ccess , vol. 4, no. 99, pp. 6614–6623, Oct. 2016. [12] J. Hu, S. Y an, F . Shu, J. W ang, J. Li, and Y . Zhang, “ Artificial-no ise- aided secure transmission with directional modulation based on random frequenc y di verse arrays, ” IEE E Access , vol. 5, no. x, pp. 1658–1667, Jan. 2017. [13] F . Shu, X. Wu, J. Hu, J. Li, R. Chen, and J. W ang, “Secure and precise wireless transmission for random-subca rrier-selec tion-based directiona l modulati on transmit antenna array , ” IEE E J. Sel. Area s Commun. , vol. PP , no. 99, pp. 1–1, Apr . 2018. [14] Y . Wu, J. B. W ang, J. W ang, R. Schober , and C. Xiao, “Secure transmission with large numbers of antenn as and finite alphabet inputs, ” IEEE T rans. Commun. , vol. 65, no. 8, pp. 3614–36 28, May . 2017. [15] X. Guan, Y . Cai, and W . Y ang, “On the secrec y mutual information of spatial m odulati on with finite alphabet, ” Internati onal Confere nce on W ir eless Communic ations & Signal Pro cessing , pp. 1–4, Jun. 2013. [16] L. W ang, S. Bashar , Y . W ei, and R. Li, “Secrecy enhancement analy sis against unkno wn eav esdropping in spatia l modulat ion, ” IEEE Commun. Lett. , vol. 19, no. 8, pp. 1351–1354, Jun. 2015. [17] C. Liu, L. L. Y ang, and W . W ang, “Secure spatial modulation with a full-dupl ex recei ver , ” IEEE W ire less Commun. Lett. , vol. 6, no. 6, pp. 838–841, Sep. 2017. [18] F . Wu, L. L. Y ang, W . W ang, and Z. Kong, “Secre t preco ding-aid ed spatial modulation, ” IEEE Commun. Lett. , vol. 19, no. 9, pp. 1544–1547, Jul. 2015. [19] F . W u, R. Zhang, L . L. Y ang, and W . W ang, “Tra nsmitter precodin g- aided spatial modulati on for secrecy communications, ” IE EE T rans. V eh. T echnol . , vol. 65, no. 1, pp. 467–471, Jan. 2016. [20] Y . Chen, L . W ang, Z. Zhao, M. Ma, and B. Jiao, “Secure multiuser mimo downli nk transmission via precodi ng-aide d spatial modulati on, ” IEEE Commun. Lett. , vol. 20, no. 6, pp. 1116–1119, Mar . 2016. [21] S. R. Aghdam and T . M. Duman, “Physical layer security for space shift keyin g transmission with precoding, ” IEEE W irel ess Commun. Lett . , vol. 5, no. 2, pp. 180–183, Jan. 2016. [22] F . Shu, Z. W ang, R. Chen, Y . Wu, and J. W ang, “T wo high-performance schemes of transmit antenna select ion for secure spatia l modulation, ” arXiv preprint arX iv:1801.0477 5 , 2018. [23] G. Xia, F . Shu, Y . Zhang, J. W ang, S. ten Brink, and J. Speidel, “ A ntenna select ion m ethod of m aximizi ng secrecy rate for green secure spatial modulati on, ” Under Rev iew , 2018. [24] X. W ang, X. W ang, and L. Sun, “Spatia l modulation aided physical layer security enhanceme nt for fadi ng wiretap channels, ” in Proc. Inter- national Confere nce on W ireless Communications & Signal Pr ocessing , pp. 1–5, Nov . 2016. [25] X. Q. Jiang, M. W en, H. Hai, J. Li, and S. Y . Kim, “Secre cy enhancing scheme for spatial m odulati on, ” IEE E Commun. Lett. , vol. 22, no. 3, pp. 550–553, Dec. 2017. [26] Y . Y ang and M. Guizani, “Mapping-v aried spatial modulation for physical layer security: transmission strat egy and secrec y rate, ” IEE E J . Sel. Areas Commun. , pp. 1–1, Apr . 2018. [27] M. C. Lee, W . H. Chung, and T . S. Lee, “General ized precoder design formulati on and iterat ive algorith m for spatial modulation in mimo systems with csit, ” IEE E T rans. Commun. , vol. 63, no. 4, pp. 1230– 1244, Jan. 2015. [28] A. Strekalo vsky and I. Tse vendorj, “Pre-scaling optimizatio n for space shift keying based on semidefinite relaxation, ” IEEE T rans. Commun. , vol. 63, no. 11, pp. 4231–4243, Aug. 2015. [29] A. Garcia-R odriguez , C. Masouros, and L. Hanzo, “Po wer-ef ficient space shift ke ying transmission via semidefinite programming, ” in IEEE Internati onal Conf. on Commun. , Jul. 2016, pp. 1–6. [30] P . Y ang, Y . L. Guan, Y . Xiao, M. D. Renzo, S. Li, and L. Hanzo, “Trans- mit precoded spat ial modulation: Maximiz ing the m inimum euclide an distanc e versus minimizing the bit error ratio, ” IEEE T rans. W ire less Commun. , vol. 15, no. 3, pp. 2054–2068, Nov . 2016. [31] P . Cheng, Z. Chen, J. A. Z hang, Y . Li, and B. V ucetic, “Low-comple xity precodi ng for spatial modulation, ” in V eh. T echno l. Conf. , Feb. 2018, pp. 1–5. [32] S. R. Jin, W . C. Choi, J. H. Park, and D. J. Pa rk, “Line ar precoding design for mutual information maximizatio n in general ized spatial modulati on with finite alphabet inputs, ” IE EE Commun. Lett. , vol . 19, no. 8, pp. 1323–1326, Jun. 2015. [33] X. Guan, Y . Cai, and W . Y ang, “On the mutual information and precodi ng for spatia l modulation with finite alphabet, ” IEEE W irele s s Commun. Lett . , vol . 2, no. 4, pp. 383–386, May . 2013. [34] J. Hu, F . Shu, and J. L i, “Rob ust synthesis method for secure direc- tional modulation with imperfect direction angle, ” IEE E Commun. Lett. , vol. 20, no. 6, pp. 1084–1087, Apr . 2016. [35] W . Zeng, C. Xiao, M. W ang, and J . Lu, “Linear precod ing for finite- alphabe t inputs ove r m imo fading channels with statistic al csi, ” IEEE T rans. Signal Pr ocess. , vol. 60, no. 6, pp. 3134–3148, Feb . 2012. [36] Z. Q. Luo, W . K. Ma, M. C. S o, Y . Y e, and S . Zhang, “Semidefini te relaxa tion of quadrat ic optimization problems, ” IEEE Signal Proc ess. Mag , vol. 27, no. 3, pp. 20–34, Apr . 2010. [37] S. Boyd and V . L, Con vex optimization . Cambridge : Cambrid ge Uni v . Press, 2004. [38] O. Mehann a, K. Huang, B. Gopal akrishnan, and A. Ko nar , “Feasible point pursuit and successi ve approximation of non-con vex qcqps, ” IEEE Signal P r ocess. Lett , vol. 22, no. 7, pp. 804–808, Nov . 2014. [39] C. Helmberg , F . Rendl, R. J. V anderbei, and H. W olkowi cz, “ An interior - point method for semidefinite programming, ” SIAM J. Optim. , v ol. 6, no. 2, pp. 342–361, May . 1996.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment