Preserving the Location Privacy of Secondary Users in Cooperative Spectrum Sensing
Cooperative spectrum sensing, despite its effectiveness in enabling dynamic spectrum access, suffers from location privacy threats, merely because secondary users (SUs)’ sensing reports that need to be shared with a fusion center to make spectrum availability decisions are highly correlated to the users’ locations. It is therefore important that cooperative spectrum sensing schemes be empowered with privacy preserving capabilities so as to provide SUs with incentives for participating in the sensing task. In this paper, we propose privacy preserving protocols that make use of various cryptographic mechanisms to preserve the location privacy of SUs while performing reliable and efficient spectrum sensing. We also present cost-performance tradeoffs. The first consists on using an additional architectural entity at the benefit of incurring lower computation overhead by relying only on symmetric cryptography. The second consists on using an additional secure comparison protocol at the benefit of incurring lesser architectural cost by not requiring extra entities. Our schemes can also adapt to the case of a malicious fusion center as we discuss in this paper. We also show that not only are our proposed schemes secure and more efficient than existing alternatives, but also achieve fault tolerance and are robust against sporadic network topological changes.
💡 Research Summary
Cooperative spectrum sensing (CSS) is a cornerstone of cognitive radio networks, enabling secondary users (SUs) to collectively detect the presence of primary users and opportunistically access idle spectrum. However, the RSS (received signal strength) values reported by SUs are strongly correlated with their physical locations, making it possible for a malicious fusion center (FC) or an eavesdropper to infer fine‑grained location information—a threat known as single‑report location privacy (SRLP) and differential location privacy (DLP) attacks. This paper addresses the privacy problem by proposing two cryptographic protocols that protect SU location while preserving the reliability and efficiency of CSS.
The first protocol, LP‑3PSS (Three‑Party Private Spectrum Sensing), introduces a semi‑trusted gateway (GW) alongside the FC. SUs encrypt their RSS values with an order‑preserving encryption (OPE) scheme and send the ciphertexts to GW. GW forwards the OPE ciphertexts to the FC, which can compare them directly because OPE preserves order. A dynamic group key is established among all parties using a Tree‑based Group Elliptic Curve Diffie‑Hellman (TGECDH) protocol, allowing the system to handle joins and leaves without re‑keying all participants. Since only symmetric‑key operations are used, LP‑3PSS achieves low computational overhead (≈30 ms per sensing round) and minimal communication (≈1 KB). The gateway never learns the plaintext RSS or the detection threshold τ, and the FC never learns individual RSS values, only the ordering needed for the half‑voting decision rule.
The second protocol, LP‑2PSS (Two‑Party Private Spectrum Sensing), eliminates the extra entity and relies on Yao’s Millionaires (YM) protocol for secure comparison. Each SU holds its RSS value, while the FC holds the detection threshold τ. Through YM, the two parties jointly compute the Boolean predicate “RSS > τ?” without revealing the underlying numbers. This approach guarantees that τ remains secret from SUs and RSS remains secret from the FC, even if the FC attempts to manipulate τ to extract information. The trade‑off is higher computational cost because YM requires public‑key operations; the measured latency is 80–120 ms per round, but no additional hardware or trusted third party is needed.
Both schemes adopt the half‑voting rule, which is provably optimal for minimizing the sum of false‑alarm and missed‑detection probabilities in a voting‑based fusion. The rule declares the channel occupied (H1) if at least λ = ⌈n/2⌉ SUs vote “busy”. To further improve robustness, the authors integrate a Beta reputation mechanism. After each sensing period, the FC updates each SU’s positive and negative rating coefficients based on agreement with the global decision, computes a credibility score, and adjusts the voting weight accordingly. This mitigates the impact of malicious or faulty SUs and provides fault tolerance against missing reports.
The security model assumes that (i) the FC may vary τ to infer RSS, (ii) the GW follows the protocol honestly but is curious, (iii) no collusion occurs between FC, GW, and SUs. Under these assumptions, the paper proves that LP‑3PSS achieves information‑theoretic privacy: the three non‑colluding entities learn nothing beyond the final voting outcome. LP‑2PSS inherits the security guarantees of YM, ensuring that neither party learns the other’s private input.
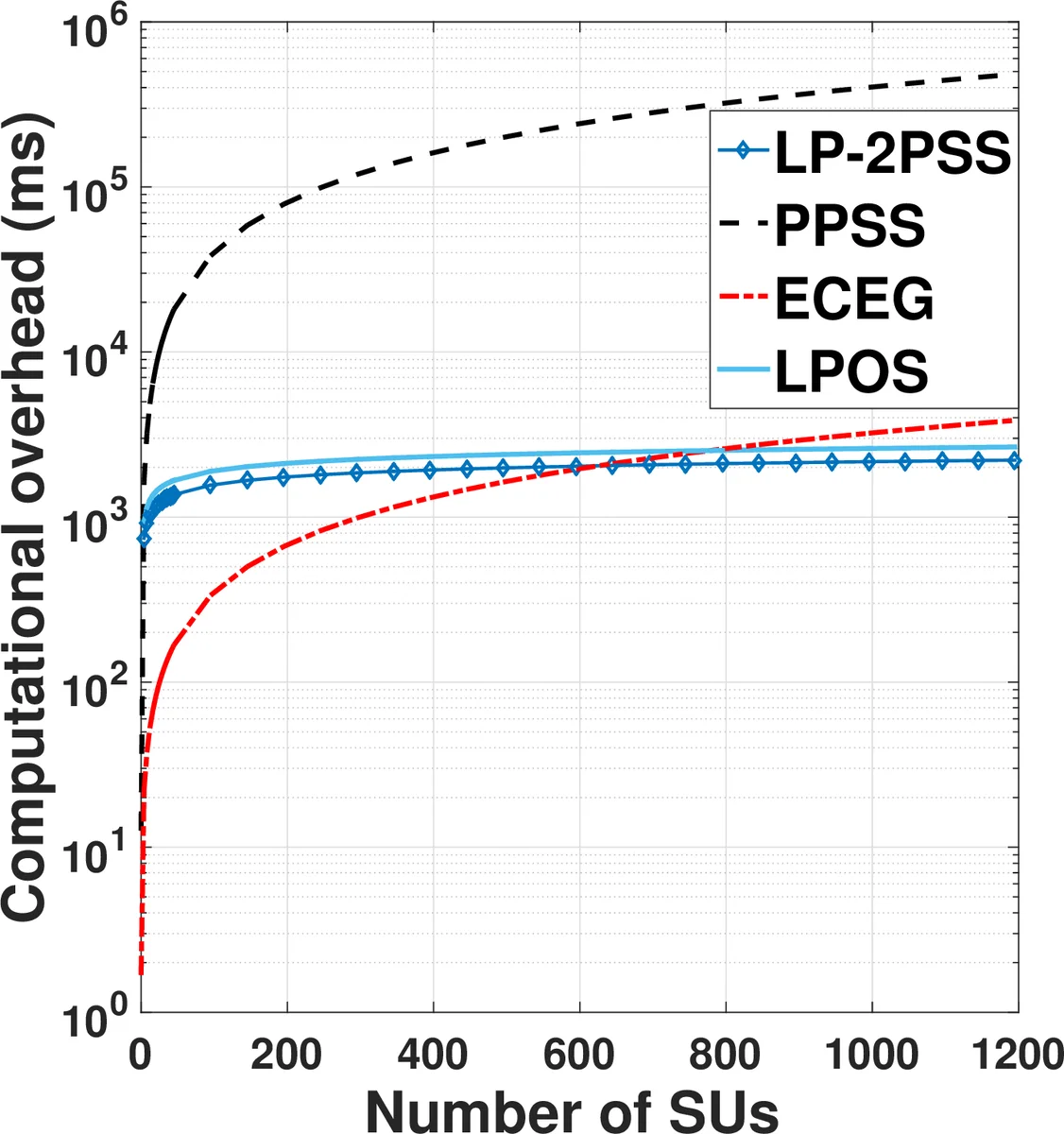
Performance evaluation compares the proposed protocols with prior work such as PPSS and PDAFT. LP‑3PSS outperforms both in computation (≈30 ms vs. >200 ms) and communication (≈1 KB vs. several KB), while offering stronger privacy because the RSS values are never exposed to the FC. LP‑2PSS, although slower, eliminates the need for a gateway and still achieves lower overhead than PPSS, which relies on discrete logarithm‑based encryption and pairwise secret sharing. Both schemes remain robust under dynamic network conditions: the TGECDH group key can be updated efficiently when multiple SUs join or leave, and the reputation system quickly isolates misbehaving nodes.
In summary, the paper delivers two practical, privacy‑preserving CSS solutions with clear trade‑offs: LP‑3PSS provides low computational cost and higher privacy at the expense of deploying an extra semi‑trusted gateway, while LP‑2PSS offers a gateway‑free design with modestly higher computational load. Both achieve location privacy, fault tolerance, and accurate spectrum detection, making them suitable for a wide range of cognitive radio deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment