Evaluation of Static Analysis Tools for Finding Vulnerabilities in Java and C/C++ Source Code
It is quite common for security testing to be delayed until after the software has been developed, but vulnerabilities may get noticed throughout the implementation phase and the earlier they are discovered, the easier and cheaper it will be to fix them. Software development processes such as the secure software development lifecycle incorporates security at every stage of the design and development process. Static code scanning tools find vulnerabilities in code by highlighting potential security flaws and offer examples on how to resolve them, and some may even modify the code to remove the susceptibility. This paper compares static analysis tools for Java and C/C++ source code, and explores their pros and cons.
💡 Research Summary
The paper investigates the practical effectiveness of static analysis tools for detecting security vulnerabilities in Java and C/C++ source code. Recognizing that the cost of fixing defects rises dramatically the later they are discovered, the authors argue that integrating static analysis early in the software development lifecycle can significantly reduce both effort and expense. The study follows a systematic methodology: a set of ten representative vulnerability samples, drawn from the U.S. Department of Homeland Security’s SAMATE repository, is analyzed with a selection of widely used open‑source tools.
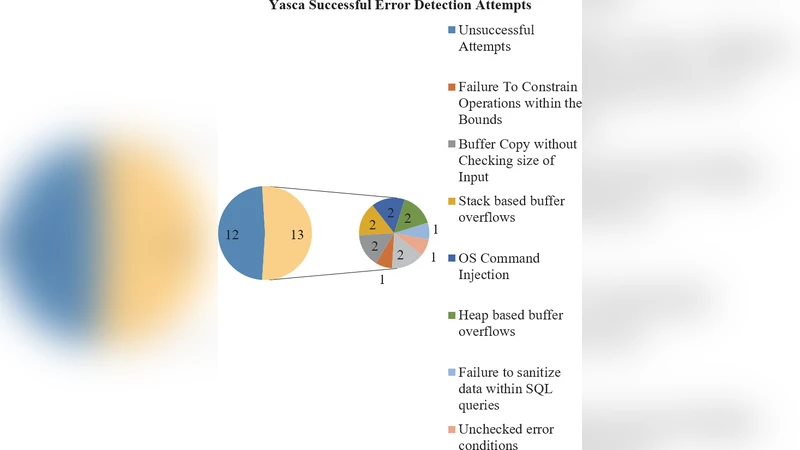
For Java, four tools are evaluated: FindBugs, PMD, LAPSE+, and Yasca. Each tool’s system requirements, detection capabilities, ease of use, and documentation support are described in detail. FindBugs operates on compiled bytecode, matching known bug patterns; it reliably finds null‑pointer dereferences and some resource‑locking issues but cannot scan source files directly and misses many injection‑type flaws. PMD offers a large rule set and tight integration with many IDEs; it excels at identifying dead code, empty catch blocks, and poor coding style, yet it does not target security‑specific weaknesses such as OS command injection. LAPSE+ is an Eclipse plug‑in focused exclusively on data‑flow tracking for injection attacks; it correctly identifies OS command, SQL, and resource injection vulnerabilities with a reported 100 % success rate on the relevant test cases. Yasca aggregates external scanners (including FindBugs and PMD) and adds its own analyses; it discovers the highest total number of CWE instances (five out of ten) and produces reports in multiple formats, but it requires manual installation of several dependent plug‑ins, a command‑line interface, and it generates a noticeable number of false positives. A comparative table (Table 1) shows which CWE each tool detects or misses, highlighting the complementary nature of the tools.
In the C/C++ domain, the authors apply three representative scanners—Flawfinder, Cppcheck, and Clang Static Analyzer—against the same SAMATE dataset, which contains classic memory‑safety bugs (stack/heap buffer overflows, memory leaks), unchecked error conditions, hard‑coded passwords, and injection flaws. Cppcheck demonstrates superior detection of memory‑related defects, while Flawfinder is more effective at flagging insecure coding patterns and potential logic errors. The Clang analyzer provides deep inter‑procedural analysis but requires more configuration effort. System requirements, IDE integration, and output formats are compared for each tool.
The discussion synthesizes the findings: no single tool can cover the full spectrum of security weaknesses. LAPSE+ is recommended when the primary concern is injection‑type attacks; PMD is valuable for enforcing coding standards and spotting generic bugs; FindBugs offers low false‑positive rates for classic Java defects; Yasca, despite its setup complexity, delivers the broadest coverage by combining multiple engines. For C/C++, a combination of Cppcheck (memory safety) and Flawfinder (code quality) yields the most balanced protection. The authors propose a pragmatic strategy: employ at least two complementary tools, aligning their strengths with project requirements, development environment, and team expertise.
The conclusion reiterates that static analysis is an essential component of a secure software development lifecycle and that tool selection must balance detection breadth, accuracy, usability, and support. Future work is suggested in the areas of continuous integration pipelines, automated reduction of false positives through machine‑learning techniques, and expanding the evaluation to include commercial static analysis suites.
Comments & Academic Discussion
Loading comments...
Leave a Comment