Double-Spending Risk Quantification in Private, Consortium and Public Ethereum Blockchains
Recently, several works conjectured the vulnerabilities of mainstream blockchains under several network attacks. All these attacks translate into showing that the assumptions of these blockchains can be violated in theory or under simulation at best. Unfortunately, previous results typically omit both the nature of the network under which the blockchain code runs and whether blockchains are private, consortium or public. In this paper, we study the public Ethereum blockchain as well as a consortium and private blockchains and quantify the feasibility of man-in-the-middle and double spending attacks against them. To this end, we list important properties of the Ethereum public blockchain topology, we deploy VMs with constrained CPU quantum to mimic the top-10 mining pools of Ethereum and we develop full-fledged attacks, that first partition the network through BGP hijacking or ARP spoofing before issuing a Balance Attack to steal coins. Our results demonstrate that attacking Ethereum is remarkably devastating in a consortium or private context as the adversary can multiply her digital assets by 200, 000x in 10 hours through BGP hijacking whereas it would be almost impossible in a public context.
💡 Research Summary
The paper “Double‑Spending Risk Quantification in Private, Consortium and Public Ethereum Blockchains” presents a comprehensive empirical study of how network‑level attacks can be combined with a double‑spending strategy to steal Ether in different deployment contexts. The authors begin by reviewing past incidents—most notably a 2014 BGP hijack that stole $83 k of Bitcoin and a recent DNS‑based hijack of an Ethereum wallet—to illustrate that man‑in‑the‑middle (MITM) attacks are a realistic threat to cryptocurrency systems. While prior research has largely focused on theoretical analyses or simulations of network delays, this work integrates real‑world network topology, mining‑power distribution, and actual routing attacks to assess the feasibility of stealing assets in practice.
Methodology
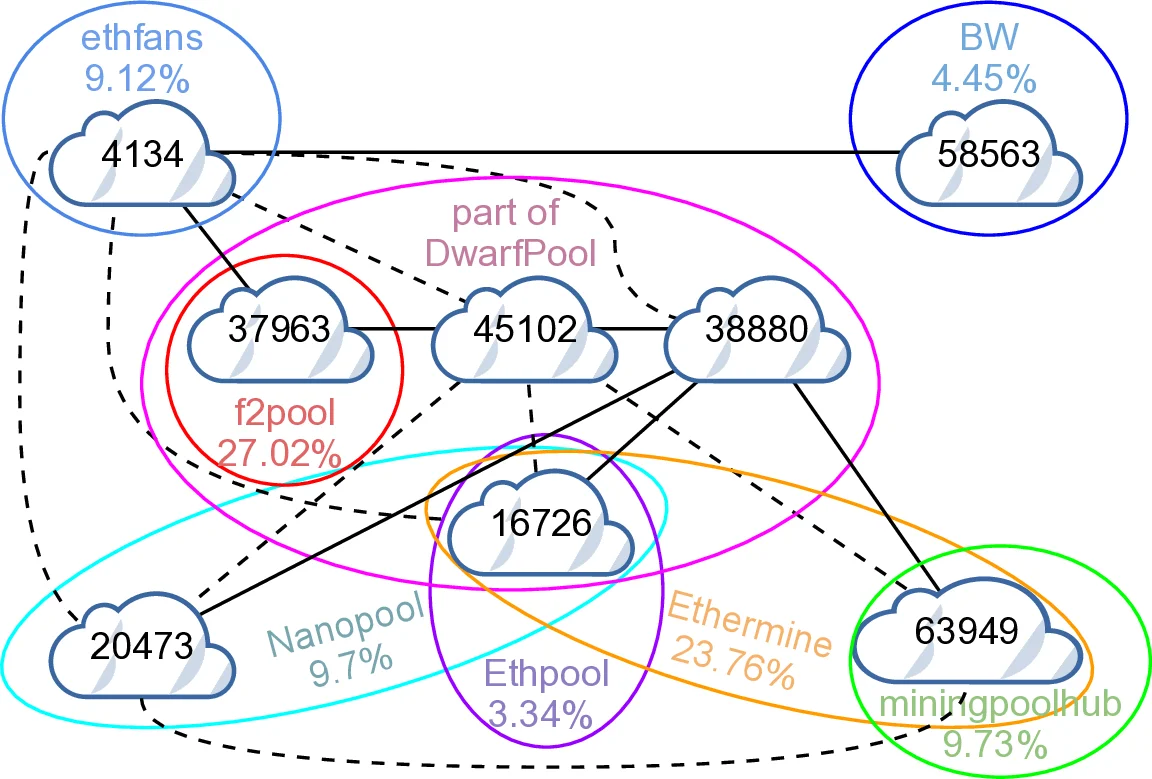
- Mining‑power recreation – The authors collected data on the top‑10 Ethereum mining pools (as of August 2017) from etherscan.io, including each pool’s hash‑rate share, stratum server locations, and autonomous system (AS) numbers. Using Linux cgroups, they constrained the CPU quota of ten virtual machines (VMs) in an OpenStack testbed so that each VM’s mining power matched the real‑world pool percentages to within one decimal place. This approach faithfully reproduces the decentralized yet pool‑centric nature of Ethereum’s proof‑of‑work (PoW) ecosystem.
- Network topology – Five BGP routers were instantiated to interconnect the VMs, reproducing the AS‑level relationships observed in the public Ethereum network. The testbed could be re‑configured to emulate three deployment models: (a) a public blockchain where each VM resides in a distinct AS with multiple peering links, (b) a consortium blockchain where a handful of organizations share a few ASes, and (c) a fully private blockchain confined to a single LAN.
- Attack vectors – Two MITM techniques were employed: (i) BGP hijacking, where the attacker announces false IP prefixes to divert traffic between selected ASes, and (ii) ARP spoofing, which manipulates MAC‑address tables inside a LAN to block local traffic. Both techniques aim to partition the network for a limited period (typically 7 minutes).
- Balance Attack – After partitioning, the attacker launches the Balance Attack (as defined in prior work). The attacker issues a transaction in one sub‑group (e.g., paying a merchant) while simultaneously mining in the other sub‑group with a modest amount of hash power. Because Ethereum selects the canonical chain based on cumulative difficulty, the attacker’s mined blocks can cause the branch containing the “honest” transaction to be discarded once the partitions heal, thereby achieving double‑spending.
Experimental Findings
- Public Ethereum: The highly meshed AS topology and abundant alternative routes make a single BGP hijack insufficient to sustain a full partition. Even when a temporary split is induced, other mining pools quickly relay blocks across the remaining paths, preventing the attacker from balancing the sub‑groups’ hash power. Consequently, the double‑spending success rate in the public setting was effectively zero.
- Consortium Ethereum: With only a few ASes and simpler routing policies, the same BGP hijack successfully isolated two groups of miners for the full 7‑minute window. During this interval the attacker’s modest hash contribution (≈10 % of total power) was enough to tip the cumulative difficulty in favor of the attacker’s branch. Repeating the attack over a 10‑hour period yielded a gain of roughly 200 000 × the initial capital, demonstrating a dramatic amplification effect.
- Private Ethereum: ARP spoofing within a LAN achieved instantaneous partitioning. Because the private network lacks any redundant paths, the attacker could control the entire communication flow. The Balance Attack succeeded with even lower hash power, confirming that private deployments are extremely vulnerable to internal MITM attacks.
Key Insights
- Network topology is a first‑order security factor – The same protocol (Ethereum’s PoW with difficulty‑based chain selection) behaves securely in a globally distributed public network but collapses under a modestly sized consortium or private topology.
- Realistic mining‑power modeling matters – By reproducing the exact hash‑rate distribution of the top pools, the authors show that an attacker does not need a majority of the network’s total hash power; a well‑balanced partition plus a small extra contribution suffices.
- BGP security gaps translate directly into financial loss – The study quantifies how a classic routing vulnerability (lack of origin validation) can be weaponized to generate massive monetary gains in a blockchain context.
- Mitigation must be multi‑layered – The authors recommend deploying RPKI/BGPsec to harden routing, adding peer‑diversity checks in Ethereum clients to detect abnormal propagation delays, and designing consortium/private networks with redundant paths and geographically dispersed nodes.
Conclusion
The paper convincingly demonstrates that double‑spending attacks are not merely theoretical constructs; they become practical when an adversary can partition the network and exploit Ethereum’s difficulty‑based fork resolution. Public Ethereum’s extensive peering makes such attacks prohibitively difficult, whereas consortium and private deployments—common in enterprise and financial consortia—are highly susceptible. The work underscores the necessity of integrating network‑level defenses (secure routing, diversified connectivity) with blockchain protocol hardening to protect against financially catastrophic attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment