Requirements for Secure Clock Synchronization
This paper establishes a fundamental theory of secure clock synchronization. Accurate clock synchronization is the backbone of systems managing power distribution, financial transactions, telecommunication operations, database services, etc. Some clo…
Authors: Lakshay Narula, Todd Humphreys
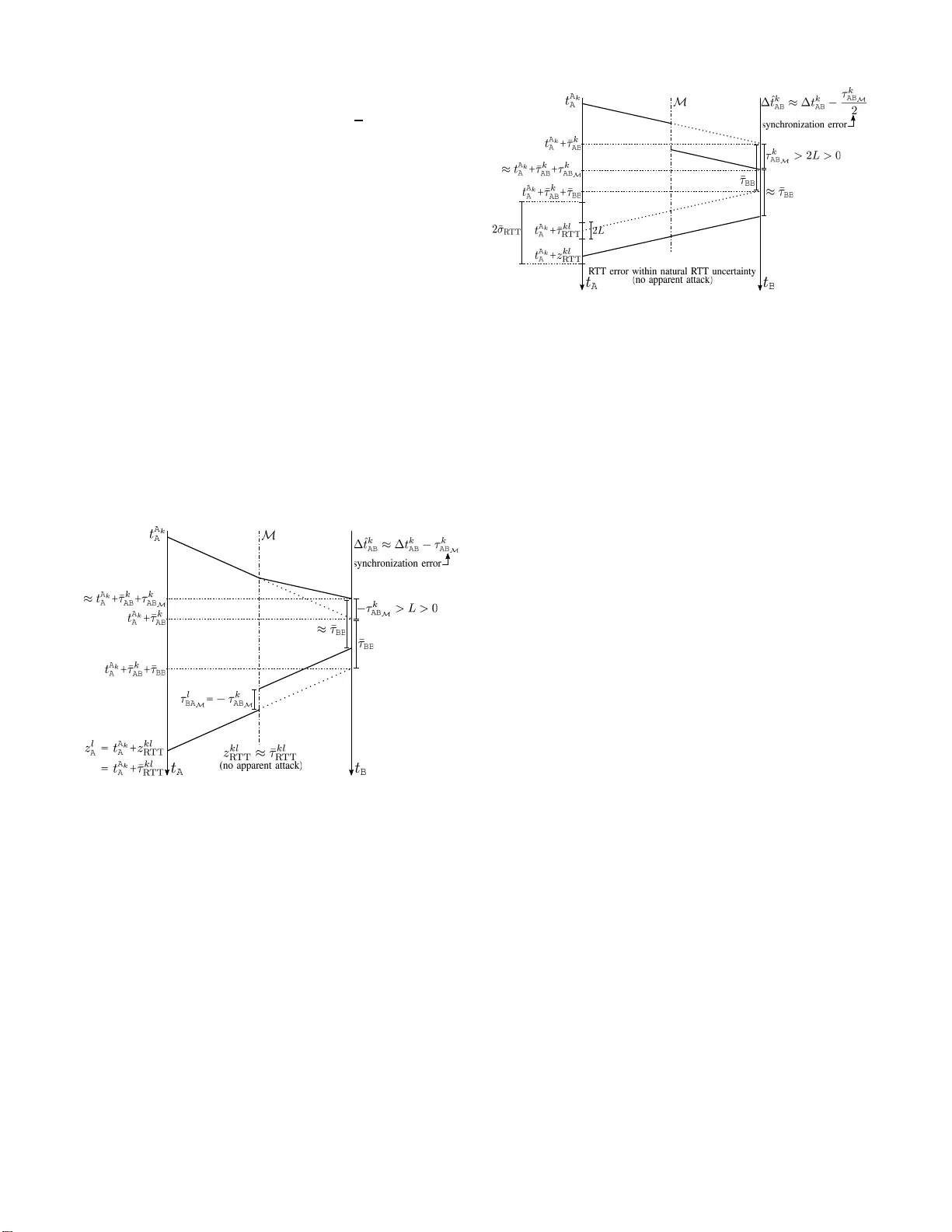
Requirements for Secure Clock S y nchronization Laksha y Narula, Student Member , IEEE, a n d T odd E. Humphreys, Mem b er , IEEE Abstract —This paper establishes a fundamental t h eory of secure clock synchronization. Accurate clock syn ch ronization is the backbone of systems managing power distribution, financial transactions, telecommunication operations, database services, etc. Some clock synchronization (time transfer) systems, such as the Global Na vigation S atellite Systems (GNSS), are based on one-way communication from a master to a sl ave clock. Others, such as the Network T ransport Pr otocol (NTP), a nd the IEEE 1588 Precision Time Protocol (PTP), inv olve two-way communication between the master and sla ve. This paper shows that all one-way time transfer protoco ls are vulnerable to replay attacks that can potentially compromise timing information. A set of conditions for secure two-way clock synchronization is proposed a nd p ro ved to be necessary and sufficient. It i s shown that IEEE 1588 PTP , although a two-way synchronization protocol, is not compliant with these cond itions, and is theref ore insecure. Requirements for secure IEEE 1588 PTP are proposed, and a second example protocol is offered to ill ustrate the range of compliant systems. Index T erms —time transfer; clock synchronization; security . I . I N T R O D U C T I O N Secure clock syn chroniza tio n is critical to a host o f tech- nologies and inf rastructure to day . The phasor measuremen t units (PMUs) that enab le mon itoring and control in po wer grids need timin g information to synchro nize measurements across a wide geograp hical area [ 1]. W ireless commu nication networks synchro nize t heir ba se stations to enable call h andoff [2]. Financial networks transfer time across the globe to ensure a common time for pricing and transaction time-stamping [3]. Cloud da tab ase services such as Google’ s Clou d Spanner similarly require precise s yn chronizatio n between the data centers to maintain consistency [4]. These clock synch r oniza- tion ap plications have sub-millisecon d a c curacy and stringent security requirem ents. Clock sy nchron ization is per formed either by over -the - wire packet-based communication (NTP , PT P , etc.), or by over-the- air radio signals (GNSS [2], cellular sig n als, LORAN [5], DCF77 [6], e tc. ); bo th wired and wireless clock sync hroniza- tion ar e used extensively . Synchronizatio n by GNSS is the method of choice in systems with the most stringent accur acy requirem ents. Equipped with atomic clo cks sync hronized to the most accurate time standards a vailable, GNSS satellites can syn chronize a ny n umber of stations on Ea rth to within a few ten s of nanoseco nds [7]. NTP is usually on ly accurate to a fe w milliseconds, b ut essentially comes f or free whene ver the host d evice is co n nected to a network. L. Narula is with the Department of E lectr ical and Computer Engineering, Cockrel l School of Engineeri ng, The Univ ersity of T exas at Austin, Austin, TX 78712 USA (email: lakshay .narula@ute xas.edu). T . E. Humphreys is with the Department of Aerospace E ngineering and Engineeri ng Mechanics, Cockrell School of E ngineering, The Uni versity of T exas at Austin, Austin, TX 78712 USA. One-way clock synchro n ization proto cols are based on unidirectio nal commun ication from the time master station, A , to the slave station , B . In such p rotocols, A acts as a bro a dcast station and may send out ti ming signals either continu o usly or periodically . The principal d r awback of one-way wireless clock synch ronization p rotocols is th eir vulner ability to delay attacks in which a man-in-the-m iddle (MITM) adversary nefar - iously delay s or r e p eats a valid tran smission from one station to an other . Cryptog raphic and other measures ca n impr ove the security of one- way p rotocols aga in st d e lay and oth e r signal- and data-level spoofing attacks [8]– [10], b ut, as will b e shown, such pr o tocols remain fun damentally insecure bec a use of th eir inability to measure ro und trip time. They can be secured against unsophisticated attacks, but rem ain v ulnerab le to mo re powerful adversaries. T wo-way clock synchron ization protoco ls inv o lve bi- directional comm unication between statio n s A an d B . Such protoco ls en able measuremen t of th e roun d trip time of th e timing signa l, which is shown to be necessary for d etecting MITM delay attacks. This measur e ment, howe ver , is no t by itself su fficient f or p r ovable security against suc h attacks. This p aper establishes a fu ndamen tal theory o f secure clock synchro n ization. I n contra st to the curren t literatu re on tim ing security [11]–[ 1 7], the problem is f ormalized with d efinitions, explicit assumptions, and proo fs. The major contributions of this work are as follows: 1) One-way sync h ronization proto cols are shown to b e in- secure against a MITM delay attack. Adversarial delay is shown to be ind istinguishable from clock bias, and hence is u n observable with out f u rther assump tions. 2) A set o f n e cessary cond itions for secu re two-way clock synchronizatio n is presented a nd p roved. Similar protoco l-specific conditions have been p r eviously pro- posed [11], [13], [18], but hav e n ot been genera lize d to apply to a u niv ersal clock sync h ronization model. 3) The p roposed necessary condition s, with stricter u pper bound s, are shown to be sufficient for secu re syn chroniza- tion in presence of a probab ilistic poly n omial time (PPT) adversary . Provable security for clo ck synchr onization h as not p reviously been explor e d in th e liter ature. 4) The two-way synchro n ization scheme of IEEE 1 588 PTP is shown to violate a necessary conditio n fo r security . This is a known vuln erability of PTP f o r which a fix has been pr o posed [1 1]. Having established a theo ry fo r security , this paper is able to show that the proposed fix is sufficient but is no t the minima l n ecessary modificatio n. A m ore p arsimoniou s security req uirement for PTP is presented that is b oth necessary and sufficient for secu re synchro n ization. 5) A generic co nstruction of a secur e two-way c lock syn- chroniza tio n protocol is p resented to illustrate the gen eral applicability of the p roposed necessary and sufficient condition s to a r ange of und erlying proto cols. This paper is a significant extension of [19], by the same authors: (1 ) th e necessary cond itions for security have be en rev amped to incorpo rate both continuous and packet-based clock synch ronization systems, (2) a su fficiency p roof for th e security con d itions has been f o rmulated, and ( 3) proto col- specific co untermeasu res presented in the literature have b een unified with the p roposed con ditions. W ired clock syn chroniz a tion is inhe r ently more secure than its wir e le ss co unterpar t becau se physical acc e ss to cables is easier controlled than access to ra d io cha nnels. This paper primarily fo cuses on the more ch allenging task o f clock synchro n ization over a wireless chan n el; no netheless, the attacks and security proto cols d iscussed herein also a pply to wireline clo ck synchronization protoco ls in th e ca se where the ad versary gets acce ss to the c h annel. For examp le, if an adversary is able to h ijack a bo undary clock in a wir eline PTP network, then th e resulting vu lnerabilities are equi valent to that of wireless synchr o nization wher e the ad versar y has op en access to th e rad io channel. In fact, an adversarial boun dary clock is even more p o tent than a wireless adversary since it can co mpletely blo ck the authe n tic signal from reach ing B . The rest of this paper is organized as follows. Previous works on secure clock synch ronization , and their relation to this pape r, are summ a rized in Sec tion II. Section I II presents a generic model for clock synch ronization and sho ws that all possible on e -way synchro n ization pr otocols are insecur e. Section IV p resents the set of security c o nditions fo r a wireless clock synchro nization pro to col, pr ovin g these to be necessary by contr adiction. Section V presents a pro of of sufficiency for the same set o f cond itions with stricter upper bo unds. A construction of an examp le secure p rotocol is presented in Section VI , a lo ng with the security requirements for IEEE 1588 PTP . Sectio n VII presents a simulation study of a secure clock syn chronizatio n mo del op erating over a simplistic channel model. Concluding rem arks ar e ma d e in Section VIII. I I . R E L A T E D W O R K GNSS, NTP , and PTP are the most widely used proto cols for clock synch ronization . A nu mber of r esearch e fforts have been mad e to assess and imp r ove the security o f these proto - cols. T h is section reviews some of th e notable efforts in the literature. The GNSS jamming and spoofing threat h as been recog- nized in the literature for more than a decade. A sur vey of th e current state-of- the-art in spoo fing and an ti-spoofing technique s is presente d in [8]. Recent work s on G N SS an ti- spoofing techn iques have specifically focused on the case o f timing security . Collaborative multi-receiver [ 16] and direct time estimatio n [17] techniqu e s ha ve been propo sed for robust GNSS clo ck syn chronizatio n. The growing popularity of IEE E 1588 PTP for syn chro- nization in critical infr astructure has brou g ht abo ut conce r ns regarding its security [11]–[15]. The threats to I EEE 15 88 PTP can br oadly be categorized into data-level attac k s (su c h as modification of time messages) and phy sical layer at- tacks (such as replay and d elay attacks). While cr yptogr a phic protoco ls are able to foil data-level attack s ag ainst realistic adversaries, som e signal-le vel attack s, suc h as the delay attack, remain open v ulnerabilities. Unfortun ately , their execution is relativ ely simple. Signal-level attacks, such as the man- in -the- middle attack, have been studied in the recent past. Howe ver , these studies on ly includ e a b rief discussion on coun termea- sure technique s, an d no proo f or theoretical guaran tee of the efficac y of the cou ntermeasur e s has been provid ed. Ullman et al. [11] p ropose me asuring the prop agation delays during in itialization o f clock synchr o nization and monitorin g the propag ation delay s du ring the normal operation of the time synchro n ization p rotocol. Howe ver , [1 1] d oes n ot prove that such a defense would be suf ficient to prevent the de lay attacks. In [13], it is rema r ked that the clock offset com p uted between mu ltiple master clocks over a symm etric chann e l must be zero, and thu s, if multiple master clocks are av ailable, they can d etect any malicious de lay intr o duced by an ad versary . Howe ver , th is defen se does not co nsider the p ossibility th at the ad versary may only delay the packets sen t to the slave nodes. The work presented in [18] is per haps in closest relation to the current paper . An nessi et al. upper bou nd the clock drift betwe en subsequ ent synchron ization sign a ls using a dr ift model, and perfo rm two-way exchange of timestamps such that the master clock is ab le to verify th e time at the slave. Furthermo re, given the maximum clo c k drift rate and the maximum and minimum prop agation delay of the timing signal, they der i ve an u p per bo und on the adversar ial delay that can go un noticed. H owever , with conservati ve bo unds on the maximum clock drif t rate and the variation in path delay s, the accur acy g u arantees derived in [18] may b e insufficient for certain application s. Mo reover , as will be shown in th is paper, they fail to take account of on e the nec e ssary co nditions for secure sy nchron ization. This p a p er abstracts the clock synchr o nization m odel and assesses its security in a generic setting. I t is shown that specialization of the gener ic security con d itions to th e par- ticular p rotocols assessed in the aforemen tioned efforts leads to solutions similar o r identical to th ose previously advanced. Thus, e stablishing th e f undamen tal theory of secur e clock synchro n ization also serves to u nify the prior work in the literature. I I I . S Y S T E M M O D E L A ge n eral system mod el for clock syn chronizatio n is shown in Fig. 1. The time seeker station, B , wishe s to synchr o nize its clock to that of th e time ma ster station, A . For wireless synchro n ization applications, station s A and B are assumed to have known locatio ns, x A and x B , respectively . Due to clock imperfectio ns, the tim e at station B , t B , con tinuously d rifts with respect to t A , the time at station A . Station B seeks to track the relativ e drift o f its clock by an exchan g e of signals between A and B . W ithout lo ss of gener ality , th is paper a ssum es t A is equiv alent to tru e time (relative to som e ref e r ence epo ch), a close pr oxy fo r which is GPS system time. It is assumed that A and B are able to exchange cry pto- graphic keys securely , if req uired. This exchange may occur T ABLE I N O TA T I O N U S E D I N T H I S PA P E R A Time master station B Time seek er station t m i m Tra nsmit time, according to m , of its i th signal feature t m i n Recei pt time, acc ording to n , of the i th signal feature trans- mitted by m τ i mn Delay , in true time, experie nced by the i th featur e in propa- gating from m to n τ i mn M Component of τ i mn introduc ed by the man-in-the-middl e ad- versa ry τ i mn N Component of τ i mn due to natu ral factors, includin g process- ing, transmission, and propagation delay ¯ τ i mn Modeled or a priori estimate of τ i mn N ˜ τ i mn N τ i mn N − ¯ τ i mn τ BB Delay , in true time, betwee n the receipt of sync and transmis- sion of re sponse at B ¯ τ BB Delay , a ccording to B , betwe en the receip t of sync and transmission of r esponse at B ˜ τ BB τ BB − ¯ τ BB ∆ t i AB Clock off set between A and B at the time of receipt of the i th feature at B ∆ ˆ t i AB B ’ s best estimate of ∆ t i AB w i mn Measurement noise associated with the m easured time-of- arri va l of the i th signal featu re from m at n τ ij R TT Round trip time, in true time, in volving the i th and j th signa l feature s of A and B , respect iv ely ¯ τ ij R TT Modeled or a priori estimate of τ ij R TT z ij R TT A noisy measurement of τ ij R TT over a public channel via a p rotocol suc h as the Dif fie-Hellman key exchan ge [20] or v ia quantu m key exchange tech niques [21], [ 22]. Alternatively , symm etric keys for neighb o ring sta- tions may be lo aded at the time o f installation . Fig. 1. Abstract model of a clock s ynchroni zation system with a time m aster station A and a time seeker station B . T he antenna outputs are driv en by the clock through the recei ver and transmitt er blocks. Station A sends out a sync signal, s A , ha ving d istinct featu res which can be disamb iguated fro m one ano ther by ob serving a window of th e signal c o ntaining the feature. The tran sition in s A marking the beginning of a data packet is an example of such a sign al feature . Fur thermor e , the sy stem at A is designed such that th e k th feature is tr a nsmitted at time t A k A . B e ith er knows t A k A by pr ior arrangem ent, or a d igital repr e sentation of t A k A is encoded in s A (e.g., a timestamp). In any case, B knows when the k th featu re was sent, acco rding to A ’ s clock . This sets up a bijectio n S k A ⇋ k ⇋ t A k A (1) where S k A represents a window of s A containing the k th featu re. Station B ’ s received sync sign al, denoted r B , is a de layed and n oisy re p lica of s A . Let τ k AB denote the delay ( in true time) experienced by the k th featur e of s A as it travels fr om A to B . For line-of -sight (L OS) wireless commu n ication, τ k AB is the sum of the fr ee-space pr opagation d elay over th e distance k x B − x A k and additional delays due to interaction of the timing signal with th e intervenin g ch annel. A. One-W ay Clock Syn chr onizatio n Mod el In one- way clock syn chronizatio n, th e exchang e of signals between A an d B terminate s with reception of the sync signal at B . Let t A k B denote the time according to B at which the k th featur e of s A is received at B . The window cap tured b y B con ta in ing the k th feature o f s A , denoted R k B , enab les B to measure t A k B to within a small error caused by m easurement noise. This erro r , w k AB , is mode led as zero-mea n with variance σ 2 ǫ . The m easurement itself, d enoted z k B , is m o deled as z k B = t A k B + w k AB = t A k A + τ k AB − ∆ t k AB + w k AB (2) where ∆ t k AB ≡ t A k A + τ k AB − t A k B (3) is the u nknown time offset B wishes to estimate. As the bijection in (1) is k n own to B , B can o b tain t A k A for the k th detected fea tu re. I f a p r ior estimate ¯ τ k AB of the d e lay τ k AB is av ailable to B , then the desired time offset can be estimated as ∆ ˆ t k AB = t A k A + ¯ τ k AB − z k B (4) As a concrete examp le, co n sider the case of clock synchr o- nization via GNSS in wh ich B is a GNSS r eceiv er in a known fixed location x B , and A is a GNSS satellite whose locatio n is known to vary with time as x A ( t A ) . On detection of the k th feature in a window of captu red data, B determines t A k A using (1) and also makes the measurem e nt z k B = t A k A + τ k AB − ∆ t k AB + w k AB = t A k A + " k x B − x A ( t A k A ) k + D k ρ c # − ∆ t k AB + w k AB where D k ρ is the sum of excess ionospher ic and neutral- atmospher ic delay s (in distance units) and c is the speed of light. The known r eceiv er and satellite po sitions c a n be inv o ked to mo del the sign al’ s p r opagation de lay as ¯ τ k AB = k x B − x A ( t A k A ) k + ¯ D k ρ c where ¯ D k ρ is a mo del of the excess delay D k ρ at the time o f receipt o f the k th feature at B . The modeled excess delay is ba sed on atmosp heric models p ossibly refined by dual- frequen cy measuremen ts [23]. An estimate of the time offset, ∆ ˆ t k AB , can th en be m ade u sing t A k A , z k B , and ¯ τ k AB in (4 ). It must be n oted that, fo r o n e-way clo c k syn chronizatio n, any err ors in the estimate of the distance between A and B , and in th e estimate of the excess cha n nel d elay , will ap pear as an error in th e estimate of the time offset. B. T wo-W ay Clock Syn chr onizatio n Model As discussed above, if an estimate of ¯ τ k AB is av ailable, then clock synchronizatio n is complete after B r eceiv es the sync signal r B . The r espon se signal from B in a two-way p rotocol is typically used to either determine, or refin e, the estimate of ¯ τ k AB with a m easurement of the ro und tr ip time (R TT) . Th e ab ility to measure R TT obviates the requ ir ement th at k x B − x A k be known a priori . I n IEEE 15 8 8 PTP , f or example, R TT is measured to initially obtain , and perio d ically refine, the value of ¯ τ k AB used in d eriving ∆ ˆ t k AB from (4). In the system model co nsidered in th is paper , station B transmits a r esp o nse s B that is d esigned such that (1) th e re is a one-to- one mappin g l ( k ) between th e l th feature in s B and the k th feature in s A , and (2) the l th feature’ s index can be inferred by ob servation o f a window containing it. Symb o lically , if S l B is a window of s B containing the l th feature of the r espon se signal, th en S l B ⇋ l ( k ) ⇋ k (5) On receipt of th e k th fea ture in s A , at time t A k B by B ’ s clock, but at z k B as measured by B , B transmits the l th f eature in s B after a sh o rt delay , τ BB (in true time) , hereon r eferred to as the layover time . The layover time is in troduced as a p ractical c o nsideration . On receipt of A ’ s k th feature, B is physically una ble to transmit its own l th feature with zero delay . Thu s, B is allo wed to specify a shor t layover time, ¯ τ BB , after which it intends to launch its l th f eature. It is impor tant to no te that th e actua l layover time, τ BB , will not be the same as the intended lay over time due to (1) non -zero m e a surement noise w k AB and (2) non- zero freque ncy offset of the clock at B with respe c t to true time. Howe ver, if the layover time is sufficiently shor t and the measurement n o ise is ben ign, the difference ¯ τ BB − τ BB can be made negligible co mpared to th e time syn chron iza tion requirem ent, with th e actual value dep ending on the quality of B ’ s clock. Station A receives the r espo nse signa l as a delay ed and noisy replica of s B , den oted r A . Th e delay experienced by th e l th feature as it tr av els fr om B to A , in true time , is deno te d τ l BA . Station A captures a window R l A of r A that en a b les A to id entify the l th f eature in s B accordin g to (5), an d to in fer th at the received f eature is in r esponse to th e k th fe a ture transmitted by A . Fu r thermor e , A makes a noise-co rrupted mea su rement z l A of th e time-of-ar riv al of the l th f eature in s B , acco r ding to A ’ s clock. T he noise, de n oted w l BA , is again m odeled as zero- mean with variance σ 2 ǫ . The full measur e m ent mod el is g iv en by z l A = t B l A + w l BA = t A k A + τ k AB + τ BB + τ l BA + w l BA Since t A k A is exactly kn own at A , a d irect no isy m easurement of th e r ound trip time τ k AB + τ BB + τ l BA can b e m ade as z kl R TT ≡ z l A − t A k A (6) Note that the noise w l BA and w k AB in z kl R TT is embe dded within z l A and τ BB , r espectively . Un der the a ssum ption of sym metric delays, i.e., τ k AB = τ l BA , and with knowledge of ¯ τ BB , the measured R TT in (6) can be exploited to imp rove the modeled propag ation delay fo r futu re exchanges b etween A and B : ¯ τ m AB = ¯ τ n BA = z kl R TT − ¯ τ BB 2 where m > k and n > l . The two-way exchang e of sync an d r espon se messages is summarized visually in Fig. 2. Fig. 2. T wo-w ay exc hange of sync and response messages betwee n A and B in the absence of a man-in-t he-middle adversary . Since R TT will play a c entral ro le in the discussion on secure syn chron iza tion later o n, various definitio ns and as- sumptions co ncerning R TT ar e stated her e for clarity: • R TT f or the k th feature in s A and th e corr esponding l th feature in s B is d e fined as τ kl R TT ≡ τ k AB + τ BB + τ l BA • Measured R TT inclu des, in addition to R TT , measurement noise at A ; it is m o deled as z kl R TT = τ k AB + τ BB + τ l BA + w l BA • Modeled R TT , also called the prior estimate o f R TT , is defined as ¯ τ kl R TT ≡ ¯ τ k AB + ¯ τ BB + ¯ τ l BA (7) For example, in the case of wireless clock synchro niza- tion with LOS electro magnetic signals, a p rior estimate of R TT is based o n the distance betwee n A an d B and on models of ch annel delays in excess of free-space propag ation betwe e n these. • The mo deled R TT , ¯ τ kl R TT , can be refin ed with measu re- ments of R TT in a two-way proto col. Alter nativ ely , as will be discussed later , if an accu rate mode le d R TT is av ailable, it and the measu r ed R TT can b e used to d etect delay attacks. • Unambig uous measu r ement of R TT req uires that there exist a one- to-one mapp ing between the sign a l f eatures in s A and s B , as mathematica lly rep resented in (5). On detection o f the l th feature in s B , A must be able to deduce that this feature was transmitted appro ximately ¯ τ BB after B received the k th featur e in s A . This requir e m ent is approp riately a part of the R TT definition since it en ables A to un ambiguo usly measur e R TT . C. Attac k Mo del The attack mod el in this p aper con siders a MITM a dver- sary M . The av ailable compu tational resou rces allow M to execute p r obabilistic po ly nomial time ( PPT) algo rithms. M can recei ve, detect, and rep lay signals from A and B with arbitrarily precise dire c tio nal antenn as. Additiona lly , M h a s precise kn owledge of x A and x B , an d can take up any position around or betwee n the two stations. I t has unr estricted access to the signals that A a n d B exchange over the air , and ha s complete knowledge of their synch r onization protocol sav e for the crypto graphic keys. Let L denote th e alert limit, d efined as the er ror in time synchro n ization no t to be exceed ed with out issuing an aler t. Definition III.1. C lock syn chr onization is defined to be com- pr o mised if | ∆ t AB − ∆ ˆ t AB | ≥ L . Note th at, in the absence o f an adversary , clock synch r o- nization is n ot co m promised so long as | τ k AB − ¯ τ k AB + w k AB | < L Howe ver , in the presen ce of a MITM adversary , the sync sign a l is d e layed o r advanced such tha t τ k AB = τ k AB N + τ k AB M (8) where τ k AB N > 0 is the natural or p hysical d elay (equal to τ k AB in the absence of an adversary) and τ k AB M ≥ 0 is the a dversarial delay . I n this case, if | τ k AB − ¯ τ k AB + w k AB | = | τ k AB N − ¯ τ k AB + τ k AB M + w k AB | ≥ L (9) then c lock syn chroniza tion is co m promised. D. V ulnerability of One- W ay Clock Sy nchr oniza tio n One-way clock synchron ization is fundamenta lly vulnerab le to a delay attack b e cause it p rovides no mechan ism to mea- sure R TT . The adversary M can com promise any one-way wireless clo ck synchro nization p r otocol by retran smitting the authentic sync signal from A such that the retran smitted signal, s M , overpowers or oth erwise supersedes the au thentic signal s A . In the absence of additional assumptio ns beyond tho se underp inning the one-way protoco l described earlier, M can introdu c e an arbitrary delay τ k AB M in its retransmission, ther eby compro mising the syn c hronizatio n pr ocess. Note that wh ereas counterfeit signal attacks can be pre- vented by authen tication and cry ptograp hic methods [24], these techn iques do not prev ent dela y attacks because th e delayed or repeated signal has the same cryptog raphic char ac- teristics as that of th e g e nuine signal, the on ly difference being that it is received with a (possibly sma ll) a dditional de lay . The delay introduce d by M is added to the natural delay , τ k AB N , of th e signal between A a n d B . As a result, an error of ≈ τ k AB M is intr oduced in the e stima ted time offset a t B . From (4), it follows th at ∆ ˆ t k AB = t A k A + ¯ τ k AB − z k B = t A k A + ¯ τ k AB − ( t A k A + τ k AB − ∆ t k AB + w k AB ) = ( ¯ τ k AB − τ k AB N ) − τ k AB M + ∆ t k AB − w k AB ≈ ∆ t k AB − τ k AB M (10) where it is assumed that the err o r due to inaccurately m odeled delay is n egligib le and that σ ǫ ≪ τ k AB M . In the absence of an R TT me a surement, and witho ut furthe r assump tions on the nature of the protoco l or the clock drift model consider ed, the adversarial delay τ AB M is indisting uishable from a clock offset of th e sam e magn itude. T o be sure, measure s can be taken to make a MITM delay attack hard er to execute withou t detection. But, im p ortantly , these m easures cann o t guarantee that the syn chronizatio n will remain uncompromised . V ariou s measures proposed in the literature, an d their sh o rtcoming s, are discussed below . a) Received Signal Strength Monito ring: The adversary M might attemp t to overpower the a uthentic signal in or der to spoof the s ync m essage, leading to a n incr ease in the total signal power received at B . Station B co u ld monitor the received sign al streng th (RSS) to d etect such an attack [2 5]. Howe ver , a potent ad versar y could transmit, in addition to its delayed sign al, an amplitu de-matched , p hase-inv erted nulling signal that an nihilates the authentic syn c signal s A as received at B , thu s preventing an un usual increase in received power a t B . If M is po sitioned along the straight-line path between A and B , nulling of s A can b e effected w ith out prio r knowledge of s A . A labo ratory demon stration of su c h nu lling is reported in [2 6]. b) Selective Rejection o f F a lse Signal: If B recei ves both the authen tic and false ( delayed) sync signals, it may be able to ap ply an gle-of- arriv al o r signal pr ocessing te c h niques to selecti vely reject the delayed signal [8], [ 9], [27], [2 8]. Howe ver , d iscr imination based o n ang le-of-ar riv al fails if M is p o sitioned alon g the lin e f rom A to B , and, a s co nceded in [9], signal-pr o cessing-based techniqu e s for selective reje c tio n of false signals can be thwarted b y an adversary transmittin g an ad ditional nu llin g signa l, as described above. c) Collaborative V erification: Multiple time seekers may attempt to synchr o nize to the same time m aster . In this scenario, the tim e seekers can po tentially detect maliciou s activity b y cro ss-checking the recei ved signals [16]. In the simplest imp lementation, all time seekers can collabor ate to verify that they are sy n chroniz e d amongst each other . In case of an unco ordinated attack against a su bset of time seekers, this verification would expose the attack since the time offset computed at the attacked su bset wou ld be different from th at computed at the other stations. In principle, howe ver , it is possible for an adversar y to execute a coordinated attack against all the time seekers, thus concealin g its presence. I V . N E C E S S A RY C O N D I T I O N S F O R S E C U R E S Y N C H RO N I Z A T I O N This section presents a set o f conditions for secure two- way clock sync hronizatio n and proves these to be nec e ssary by con tradiction. I n other word s, it is shown that if a two- way cloc k synchron ization p rotocol does n o t satisfy any on e of these p r oposed condition s, there exists an attack that can compro mise clock sync h ronization witho ut detec tion. It is impor tant to note that the ability to measur e R TT in a two-way protoco l is necessary , but not su fficient, fo r provably secure syn chroniza tion. As an example , IEEE 1588 PTP is a two-way pr otocol that has b een prop o sed as an alternative to GNSS for sub-micr osecond c lo ck sy nchron ization in critical infrastructu re such as the PMU network. But, despite the b i- directional exchan ge between stations, and hence the ability to measure R TT , recent work h as sho wn that PTP is vulnerable to delay attacks in whic h a MITM in tr oduces asymm etric de la y between A and B . Asymmetric delay br eaks the assump tion that τ k AB = τ k BA and leads to an erro neous pr ior for ¯ τ AB and ¯ τ BA for future exchang e s. This vulnerability is documented in both the literature [11], [ 13], [18] and the IEEE 15 88- 2008 standard. Thus, a secure two-way clock sync hronizatio n protoco l must satisfy a dditional security requ irements beyon d the ability to mea su re R TT . The condition s in troduced b e low are not tied to any spe- cific proto c o l, unlike some measures prop osed in the curr ent literature [11]–[17]. They a re generally applicable to any two- way proto col (e.g., PT P) for which the fo regoing two-way synchro n ization mo del ap plies. Assuming the tim e master A in itiates the two-way c o mmu- nication, the necessary co nditions f o r secu r e clock synchro- nization are a s fo llows: 1) Both A and B must tran smit u npredic tab le wa veforms to prevent th e ad versary M from generatin g coun terfeit signals that p ass auth entication. In practice, this implies the u se of a cry ptograp hic con struct such as a message authenticatio n code (M AC) or a digital signature. 2) The pro p agation tim e of the signal m u st b e irre d ucible to within the alert limit L along b o th sign al paths. For wireless clo ck syn c hronizatio n , this condition implies synchro n ization via LOS electromagnetic signals as L → 0 . 3) The R TT between A and B must be kno wn to A and measurable b y A to within the aler t limit L . Th e R TT mu st include the d elays internal to b oth A and B , in ad dition to the propag ation delay . Station A mu st know of any intentional delay introduc e d by B , such as the layover time τ BB introdu c ed ea r lier . A. Pr oof o f Necessity o f Cond itio ns 1) Stations A an d B mu st transmit u npr edictab le signals: T o p rove this con d ition is n ecessary , two scenarios ar e con- sidered: a) station A transmits a signal wav efor m s A that is predictable , and , b ) station B tra nsmits a sign al waveform s B that is p redictable. a) s A is predictable: M can compr omise syn chroniza - tion with out d etection as follows: i) M takes up a position between A and B along the lin e joining th e anten nas at the two station s. ii) M initially transmits a replica of s A such that B r eceiv es identical signals from both A and M . Subsequ e ntly , M increases its signal power or o th erwise supersedes s A (e.g., v ia sig nal nulling, as discussed earlier) such th at B tracks s M , the signal transmitted b y M . ( Hereafter, whenever sign als fro m M compete with tho se fro m A or B , it will b e assumed that tho se from M exert contro l.) iii) Exploiting the predictab ility of s A , M a dvances its replica s M with respect to s A by | τ k AB M | , where τ k AB M < 0 . B tracks th e advanced sign al, resulting in an erro r of τ k AB M in the co mputed ∆ ˆ t k AB as shown in (10). iv) B tran sm its the unp r edictable response s B compliant with the prearran ged layover time ¯ τ BB . M intercepts this signal from B , and replays it to A w ith a delay of τ l BA M = − τ k AB M > 0 , causing A to track the delayed sign a l. As a result, th e R TT is τ k AB + τ BB + τ l BA as A expe c ts. I n summary: τ k AB = τ k AB N + τ k AB M τ l BA = τ l BA N + τ l BA M = τ l BA N − τ k AB M ⇒ τ k AB + τ l BA = τ k AB N + τ l BA N Thus, M u ndoes the effect of its sync advance, preventing A from d e tecting the attack. b) s B is predictable: M can compr omise syn chroniza - tion with out d etection by replicatin g B ’ s b ehavior: i) M takes up a position between A and B along the lin e joining th e anten nas at the two station s. ii) M recei ves the sync signal and g enerates a v alid r espon se with a delay ¯ τ BB + k x M − x B k k x A − x B k ¯ τ k AB + ¯ τ l BA (11) such th at the R TT is ¯ τ k AB + ¯ τ BB + ¯ τ l BA , as A expe cts. iii) M recor d s the u npredic ta b le signal from A and replays it to B with an arb itr ary delay τ k AB M > 0 . This re sults in an e rror o f ap p roximately τ k AB M in the computed ∆ ˆ t k AB at B , as shown in (1 0). 2) Pr opagation time must be irr ed ucible to within L : If there exists a ch annel that reduc es th e pro pagation time from A to B or from B to A by m o re th an L as compa r ed to the channel used by A and B , th en M can c omprom ise synchro- nization without d etection. The fo llowing attack assumes the propag ation time from A to B is redu cible by more th an L ; a similar attack exploits the situation in which th e p ropaga tio n time fr o m B to A is red ucible by more than L . i) M record s the sync signal s A going f rom A to B . ii) M makes the recorded signa l reach B advanced b y | τ k AB M | compare d to s A , where τ k AB M < − L . An er r or of τ k AB M is in troduced in the time offset value com puted at B as shown in ( 10). iii) M records the response signa l s B , which has the expected prearran ged layover time τ BB ≈ ¯ τ BB . M replays this signal to A with a d elay of τ l BA M = − τ k AB M such tha t the R TT is co nsistent with what A expects. 3) RTT kn o wn to and mea surable by A to within L : Synchro nization can be comp romised without de te c tion if | z kl R TT − ¯ τ kl R TT | > L with no n -negligible prob ability even in the absence o f an adversary . T his co ndition can be met if a) the prior estimates ¯ τ k AB , ¯ τ l BA , or ¯ τ BB are not accurate to the correspo n ding tr ue values to within L , or b) the magn itude of the measuremen t error sum | w k AB + w l BA | is larger than L . Note that the condition | w k AB | > L co mpromises synchron iza tion ev en absent an adversary . An adversary M can exploit the condition | z kl R TT − ¯ τ kl R TT | > L as fo llows: i) M initially tr ansmits a re p lica o f s A such that B r eceiv es identical signals fro m both A and M . Sub sequently , M introdu c es a delay τ k AB M > 0 in the replayed sign al s M . As assum ed earlier, s M exerts control an d intro duces an error of ap proximate ly τ k AB M in the comp uted ∆ ˆ t k AB at B , as shown in (1 0). ii) S tation B transmits the r espo n se sig n al with the prea r- ranged layover time τ BB ≈ ¯ τ BB with respect to the d elayed signal. iii) In the receiv ed sign al r A , A iden tifies the expe c ted featur e l ( k ) . The R TT , if m easurable, includ es th e delay τ k AB M introdu c ed b y M . iv) Howe ver , A is unable to definitively declare an attack , since the erro rs in th e modeled R TT an d/or the measur e - ment o f R TT are po ssibly larger than L . In oth er words, it is n o t possible to claim that | z kl R TT − ¯ τ kl R TT | > L only in the p resence of ad versarial delay . V . P R O O F O F S U FFI C I E N C Y This section p resents a sufficiency p roof f or the set of secu- rity condition s pro posed in the previous section. A su fficienc y proof guaran tees secure synch ronization u nder the consid e r ed system and attack m o dels. Th is p a p er d r aws inspiratio n fro m the literature on modern cry p tograph y and fo rmalizes th e pro b- lem of secu re clock synchro nization with explicit de finitions, assumptions, an d pr oofs. A. Assumptions This pr o of assumes th at the system under con sideration strictly comp lies with th e set of necessary security condition s. Specifically , 1) Both A and B use an authenticated en cryption scheme to g enerate unpr edictable and verifiably auth entic signals in the p resence of a pro babilistic p olynom ial time (PPT) adversary . 2) The difference between the R TT along th e commu nica- tion chan nel betwe e n A and B and the shortest po ssible R TT is negligible as co mpared to L . 3) The difference b etween th e modele d delay s ¯ τ k AB and ¯ τ l BA and the true delays τ k AB and τ l BA , re spectiv ely , is negligible as co mpared to L . | ¯ τ k AB − τ k AB N | ≪ L (12) and | ¯ τ l BA − τ l BA N | ≪ L (13) Furthermo re, A and B ag ree upo n a fixed layover time ¯ τ BB , and the difference b etween this and the true layover time is n egligible: | τ BB − ¯ τ BB | ≪ L . 4) The standard deviation of th e n oise corr upting the mea- surements t A k B and t B l A is negligible c o mpared to th e alert limit: σ ǫ ≪ L (14) Notice that the ab ove assumptions ar e the same as the neces- sary co n ditions in Section IV, but with stricter up per b ounds on th e con ditions. If symmetric keys ar e exchan ged prio r to synchr onization, then priv ate-key cry p tograph ic schemes such as Encry pt-then- MA C [29] can be used for au thenticated en cryption. Alterna- ti vely , if th e keys m ust be exchan ged over a pu blic channel, then digital signatures [30] can be used to authe n ticate the encryp ted messages. Cryptogr a phic authentication schemes like MA C and digital signatures generate a tag associated with a message. Qualitati vely , a MA C or dig ital signature scheme is secure if a PPT adversary , even whe n given access to multiple valid message-tag pairs o f its own cho ice (as many as possible in poly n omial time), can not gen erate a valid tag for a new message with n on-negligib le probab ility . I rrespective of the cryp tograph ic scheme u sed, th is pro o f assumes tha t the probab ility of M generatin g a new v alid s ync o r r espon se signal is a n egligible fu nction of the key len gth n : P [ Valid ] < negl ( n ) (15) T o detect an attack before the synchr onization erro r exceeds L , A must select a threshold lower than L beyo nd which an attack is d eclared. Con sider the m o deled R TT , ¯ τ kl R TT , as d e fin ed in (7), an d the measurem ent z kl R TT as defin ed in (6). A threshold less th an L , say L − δ with 0 < δ < L , is set by station A such that if | z kl R TT − ¯ τ kl R TT | > L − δ , then an attack is declared . B. Definitions Definition V .1. A PPT adversary M succeeds if clock syn- chr onizatio n is c o mpr o mised (Defi nition III . 1) and | z kl R TT − ¯ τ kl R TT | ≤ L − δ Definition V .2. F a ster -than -light ( superluminal) pr opaga tion is d e fined to b e h ar d if M cannot pr opaga te a signal at a speed higher tha n th e speed of lig ht with no n-negligible pr o bability . Under h ar dness o f superlumin al pr opaga tion P [ Sup erluminal ] ≈ 0 Definition V .3. A clock synchr onization pr otocol is defin ed to be secu re if, u nder th e h ar dness of superlumina l p r op agation assumption, P [ Success ] < negl ( n ) wher e Success for M is d efined in Defi nition V .1. C. Pr oof In the presen c e of an adversary M , th e measurem ent z kl R TT is mo deled as z kl R TT = τ k AB N + τ k AB M + τ l BA N + τ l BA M + τ BB + w l BA (16) Let ˜ τ k AB N and ˜ τ l BA N denote the erro r in th e modeled signal delay due to natural/p hysical phenome n on. Also, let ˜ τ B be the difference between the inten ded layover time ¯ τ BB and the actual lay over time τ BB . N o te that these might be po siti ve or negativ e. ˜ τ k AB N = τ k AB N − ¯ τ k AB (17) ˜ τ l BA N = τ l BA N − ¯ τ l BA (18) ˜ τ BB = τ BB − ¯ τ BB (19) From (7), (16), (17), ( 18), and (1 9) it fo llows that z kl R TT = ¯ τ kl R TT + ˜ τ k AB N + τ k AB M + ˜ τ l BA N + τ l BA M + ˜ τ BB + w l BA Follo wing the assumptio ns in (12) and (13), the residual d elays are n egligib le in compar ison to L : | ˜ τ k AB N | ≪ L (20) | ˜ τ l BA N | ≪ L (21) This assumption is reasonab le sinc e o therwise the system could not con fidently m eet the accuracy r equiremen ts ev en in the absence of an adversary . Also, if ¯ τ BB is a short time interval and the m easurement no ise σ ǫ is benig n, it is reasona b le to assume that | ˜ τ BB | ≪ L (22) Note tha t M ca n advance the signal b y ( a ) forging a v alid mes- sage/tag pair, or ( b ) pr opagating th e signal faster-than-light. The assumption s of secure MA C and hardn e ss of sup e rluminal propag ation enf orce that P [ τ k AB M < 0 ] < P [ V alid ] + P [ Supe rluminal ] ≈ n egl ( n ) In o rder to stay u n detected, the adversary mu st en su re L − δ ≥ | z kl R TT − ¯ τ kl R TT | = | ˜ τ k AB N + τ k AB M + ˜ τ l BA N + τ l BA M + ˜ τ BB + w l BA | (23) At the same time, in o rder to comp romise time transfer, from (9), M mu st en sure L ≤ | ˜ τ k AB N + τ k AB M + w k AB | ≤ | ˜ τ k AB N + w k AB | + | τ k AB M | ⇒ | τ k AB M | ≥ L − | ˜ τ k AB N + w k AB | (24) The p robability of suc c ess fo r M is ev aluated as P [ Success ] = P [( Success ) ∩ ( τ k AB M < 0)]+ P [( Success ) ∩ ( τ k AB M ≥ 0 )] = P [( Success ) | ( τ k AB M < 0)] P [ τ k AB M < 0 ]+ P [( Success ) ∩ ( τ k AB M ≥ 0 )] ≤ P [ τ k AB M < 0 ] + P [( Success ) ∩ ( τ k AB M ≥ 0)] < n egl ( n ) + P [( Success ) ∩ ( τ k AB M ≥ 0)] (25) In th e c a se where τ AB M ≥ 0 , (2 4) simplifies to τ k AB M ≥ L − | ˜ τ k AB N + w k AB | Substituting the least po ssible value of τ k AB M into (2 3), it follows that | ˜ τ k AB N + L − | ˜ τ k AB N + w k AB | + ˜ τ l BA N + τ l BA M + ˜ τ BB + w l BA | ≤ L − δ Notice that from the assumptions m ade in ( 14), ( 20), (21), and (22), all ter m s except L and τ l BA M on the left-h and side of the inequality ar e negligible c ompared to L ; th u s, | L + τ l BA M | ≤ L − δ Since bo th L an d L − δ are defined to be po siti ve, the above inequality simp lifies to τ l BA M ≤ − δ where δ > 0 . Thus, for M to succeed in the case wh ere τ k AB M ≥ 0 , we mu st have that τ l BA M < 0 . As a result P [( Success ) ∩ ( τ k AB M ≥ 0 )] < negl ( n ) Thus, from (2 5) P [ Success ] < negl ( n ) Qualitativ ely , th e pr o of presented her e argues that for the adversary to succeed, it needs to either advance the sync sign a l ( τ AB M < 0 ), or advance the res po n se signal ( τ BA M < 0 ). W ith the use of a secu re MA C (or d igital signatu re) an d the hardness of superlum in al pro pagation, the adversary c a n only succeed with a negligib le probab ility . V I . S E C U R E C O N S T RU C T I O N S This section specializes the necessary and sufficient co n - ditions for secure clo ck syn chronizatio n to IEE E 1588 PTP . In addition, it presents an alternative to PTP for wireless synchro n ization—a complian t sync h ronization system w ith GNSS-like signals. A. Secur e IEEE 158 8 PTP The nece ssary an d sufficient condition s for secu r e synchr o- nization, as ada pted to IEEE 158 8 PTP , ar e as fo llows: 1) Stations A an d B m ust use an auth enticated enc r yption scheme to prevent M f rom g e n erating valid message/tag pairs. 2) The difference b etween the path delay s between A and B and th e shortest possible path d elays mu st be negligible as compared to L . F or wireless PTP [31], [32], this implies co mmunica tin g over th e LOS chann e l as L → 0 . For tra ditional wireline PT P , A and B must attem pt to commun icate over the (n early) shor test possible path. 3) The p ath delay , which is usually estimated from the R TT measuremen ts, must be acc u rately k nown a priori f or secure synch ronization . The R TT measur ements m ust be verified against the expected R TT . This imp lies that the layover time ¯ τ BB must also be k nown to A . Note that in the usual PTP formulation, the path delay is measured and used by the time seeker B . T o this end, in the usual form ulation A sen ds the tr ansmit time of the sync message an d the receip t time of the d e la y r eq message (in PTP parlance) . Similar conventions may be acc o mmodate d in the system model presented in this paper , wherein A sends the values o f t A k A , z l A , and ¯ τ kl R TT to B , and the following calcu lations may be perform e d and used at B . However , this would only be a co sm e tic change and does n ot affect the argumen ts in th is paper . The first secu rity co ndition has alread y b een pro p osed in the IEEE 1 5 88-20 08 standar d. The second con dition, howe ver , has not been con sidered in any of the earlier work s in the literature. Following the d epiction of sync a n d response signal exchang e in Fig. 2 and the attack strategy outlined in Section IV -A2, Fig. 3 illustrate s a n example attack against a PTP implemen tation th at does not satisfy the second necessary condition . Notice that th e existence of a shorter time path enables M to advance the sync signal relative to the authen tic message from A . Subsequently , M is able to undo the effect of the a d vance o n the R TT by de la y ing the r esponse sign a l fro m B to A . Station A does not measure any abn ormality in th e R TT , and thu s ca n not raise an alarm . Meanwhile, syn c h ronization has been compr o mised at B . Fig. 3. Illustra tion of an example attack against a PTP implementat ion that violat es the second necessary condition. The third co ndition is similar to the proposal in [1 1] of measuring the path delays du ring initializatio n and monitoring the delays during n o rmal o peration. Ho wever , [ 11] requires that B r espond to A with zero d elay d uring initialization to enable mea su rement of the refer ence d elays. This condition is suf ficient, but n ot necessary for secur e synchronizatio n. The system is in fact secure even if B is a llowed a fixed layover time. Fig. 4 illustrates an example attack against a PTP implementatio n in v iolation of the thir d necessary conditio n. Note that th e uncertainty of the a priori estimate of the R TT ( ¯ σ R TT ) is larger than th e alert limit, violating the thir d necessary condition which req uires that the expected R TT be known to within the alert limit (and with much hig her accur acy for pr ov able sufficiency). Even though th e measured R TT in this case is in c onsistent with the expected R TT , it canno t b e definitively flagged as an a ttac k since ben ign variations in the R TT may also have led to the obser ved R TT . Fig. 4. Illustra tion of an example atta ck against a PT P implementatio n that violat es the third necessary condition. Interestingly , at first sight, the third security condition in this paper does n ot resemble the pr o posed d efense in [18] that enforce s an u pper boun d o n the synchro nization erro r accu - mulated b etween sync messages and recommen ds that B send its tim estamps to A periodically for verificatio n. As explained next, this co ndition is in fact eq uiv alent to the con dition of known and measurab le R TT , when adapted accord ing to the system model co nsidered in [18]. Note that the requirem e nt of a zero delay in [1 1], or a shor t layover tim e in this paper, enables A to measure the R T T since the transmit tim e of the l th f e ature in s B , tha t is t B l B , can be approx imately traced b a c k to A ’ s clo ck to within the alert limit as t A k A + ¯ τ k AB + ¯ τ BB . Enf orcing the synchron ization erro r to within L and tran smitting B ’ s timestamp to A achiev es the same objective for the defense in [ 1 8], since the transmit time f rom B can be traced back to A ’ s clock with th e assumed appr oximate synchro n ization. The r efore, the pro posed counter measures in [11] and [1 8] are two different in carnations of the third security condition pro posed in this p aper . Of co urse, th e failure of b oth [11] and [18] to addr e ss the second n ecessary cond ition makes their proposed defenses vulnera b le to an ad versar y that can commun icate along a shorter tim e path between A a n d B . B. Alternative Compliant S ystem This section describes an alternati ve wireless c lock synchro- nization protoco l th a t satisfies the set of necessary a n d suffi- cient co nditions p resented in Section IV. The pr o posed p ro- tocol in volves bi-d irectional exchange o f GNSS-like pseudo - random codes for con tinuous clock syn chroniz a tion, in con- trast to discrete p acket-based synchron ization techniques such as NTP and PTP . It is o ffered h ere to illustrate th e gen eral applicability of the pro posed necessary and sufficient c o n- ditions to a range of und erlying pro tocols. Su ch a proto col can p otentially be app lied in two-way satellite time transfer and terrestrial wireless clock synchronization systems for continuo us clock syn chroniza tio n, in contrast to the packet- based d iscrete sync hronizatio n in NTP/PTP . The time master A an d the time seeker B comm unicate wirelessly over the LOS channel b etween the node s. T o simplify the analysis, it is assumed that A and B secur ely share long sequ ences of p seudo-ran dom bits prior to sync h roniza- tion. These sequences o f b its will later enable g eneration of unpred ictable signals. The pseu do-ran d om sequ ence for A has the form b A = b k A N k =0 , b k A ∈ { 0 , 1 } The p seudo-ra n dom co de C A ( t A ) for A is then g enerated as C A ( t A ) = 2 b k A − 1 for t A ∈ [ t A k A , t A k +1 A ) , k ∈ { 0 , 1 , 2 , . . . } where t A k A denotes the time accordin g to A at which the start of the k th b it in A ’ s signal is transmitted. The pseud o-rand om nature of b A ensures that C A ( t A ) has good cro ss-correlation proper ties, which enables an accurate measurement of the time-of-ar riv al of A ’ s signal at B , that is, σ ǫ ≪ L . Station A mo dulates a carrier with the code C A and tran smits a sign al s A ( t A ) whose complex baseb and representatio n is g iv en as s A ( t A ) = C A ( t A ) exp ( j θ A ( t A )) This signal is received at B as r B ( t A , τ AB ) = s A ( t A − τ AB ) + w AB ( t A ) = C A ( t A − τ AB ) exp ( j θ A ( t A − τ AB )) + w AB ( t A ) where all symbols have their usual meanings as detailed in Section III. Station B captu res a window R k B of r B and correlates it with a local replica of C A . The result of th e correlation enables B to detect the start of the k th bit of C A in the win dow , a nd p rovides a measurem ent z k B = t A k B + w k AB of the time-of-arriv al of the k th bit at B . Fur thermor e , the relationship betwe e n the start of th e k th bit a n d t A k A enables B to infer the latter . If a p rior estimate ¯ τ k AB of τ k AB is available, the n B estimates the clock offset ∆ t k AB as in (4) . Similar to the pseu do-ran dom sequence and code constru c- tion for A , B gen erates its u npredictab le code C B ( t B ) . A and B agree on a one-to -one mapp ing between C A and C B such that B respond s with th e l th bit of C B on r eception o f the start of the k th bit o f C A . Fur thermore , A and B agree that the start of th e l th bit of C B will have a co d e-phase o ffset o f ¯ τ BB with respect to th e start of the k th bit o f C A . Station B transmits the r esponse signal a s s B ( t B ) = C B ( t B ) exp ( j θ B ( t B )) such th at t B l B = z k B + ¯ τ BB accordin g to the time at B . In true time, the epoch t B l B correspo n ds to t B l B ⇋ t A k A + τ k AB + w k AB + τ BB Station A r e c ei ves the r espon se as r A = s B ( t B − τ BA ) + w BA ( t A ) and capture s a window o f the sign al R l A . A cor relates R l A with a local rep lica of C B to d etect th e start o f the l th bit of C B . This enables A to mea sure the time-o f -arriv al z l A = t B l A + w l BA Moreover , the detection of the l th b it indicates that it was transmitted in respo nse to the r eceipt o f th e start of the k th bit of C A . Since A knows the start time of th e k th bit as t A k A , it m easures the R T T as d escribed in (6). Note that th e exch ange of o ne-time pad sequen ces e nables the prop osed system to satisfy the first security condition. W ireless LOS comm unication satisfies the seco nd secu rity condition , and the knowledge of the cod e-phase la y over offset enables A to make an accurate pr io r estimate of th e R TT within the alert limit, th ereby satisfying the third secu r ity condition . Thus, th e p roposed system comp lies with all th ree nece ssary and sufficient condition s f or secu re clock sync h ronization . V I I . S Y S T E M S I M U L A T I O N This section presen ts a simulatio n study of a secure clock synchro n ization model operating ov er a simplistic chan nel model. Unlike th e abstract tr e atment of delays in the security deriv ations presented earlier, th e simulation is ca r ried out with mo d els of delays experien ced by the synch r onization messages over a real channel. This study also expoun ds the inte r play between sla ve clock stability , secu r ity requir e - ments, attack models, an d attack detection thresholds that must be d etermined in a practical synchro nization system. The channel and attack mo dels developed in this simulatio n are n ot compr ehensive. Rather, relatively simple m odels a r e considered to clearly d emonstrate th e un d erlying prin ciples. More sophisticated c h annel an d attack models can similarly be an alyzed by following the ou tline of this simulation . A. Channel Model The simu lated system resembles a tradition a l lo cal ar ea network, and is schema tica lly depicted in Fig. 5. As bef ore, A and B are the time master and seeker stations, resp e cti vely . T h e messages b etween th ese stations p ass th r ough a series o f N routers. Each ro uter is un der network traffic loadin g gene rated by the nodes labeled T . The routers perf orm simple packet for- warding, i.e. , no cr yptogr a phic operatio ns or comp lex payload modification s are perf ormed. Each rou ter transmits the queu ed packets at a service rate o f 1 Gbp s. Each network packet is assumed to h ave a size of 1542 bytes. The MI TM adversary M maliciously inserts itself alo ng the commu n ication path between A and B . Fig. 5. Schematic diagram of the network topology considered in this section. The sync and response packets from A and B experience processing and q ueueing delay at each router, and pro p- agation/link delay between routers. Queueing delay is the duration for which the p a cket is buf fered in the router before it can be tran smitted. Processing de lay is the time taken by the router to proc ess the packet header, for example, to determine the packet’ s destination. Since the ro uters in this simulation perfo rm simple packet forwarding , the processing delay is n egligible as compared to th e queueing delay [3 3]. T he propag ation/link delay is also insignifican t for lo cal networks because the propa g ation speed is a comp arable fraction o f the speed o f light. Thus, only the queueing delay significantly contributes to the overall channel d elay variations. Let the network idle probab ility for a p articular router , denoted b y ρ , be d efined as the p r obability of the ro uter qu eue being empty at a randomly chosen time instant. Since the synchro n ization p a c kets are delay-sen siti ve, th e ro uters in this simulation implement non-p reemptive prio rity sched uling for synchro n ization pac kets when the queue is not empty . Th is means that on arrival of a sync or r espon se p acket, the rou ter is allowed to comp lete the transmission o f the data packet currently being serviced, if any , but is required to service the de lay -sensitiv e packet befor e th e othe r netw ork data in the q ueue. Since the time per iod between consecutive sync - r esponse pair s is quite large as compared to the R TT for a giv en pair, it is assumed tha t a ro uter nev er h as more th an o ne delay-sensitive packet in its queue. Under such sched uling, the delay experien ced by th e timing messages is best mo deled as follows: with prob ability ρ , the total router delay is zero , an d with probability ( 1 − ρ ) the total router delay is uniformly distributed b etween zero and the maximum time to service a packet of length 15 42 bytes ( 1 542 × 8 × 2 − 30 ≈ 11 . 49 microsecon ds for a Gigab it route r ). Giv en the above chan nel specifications an d values for N and ρ , it is possible to perf orm a Monte Carlo simulation to obtain the a n ticipated R TT ¯ τ R TT , which is taken to be the empirical m e an of th e R TT measureme n ts in the sim u lation, and th e associated standard deviation ¯ σ R TT . As shown in Fig. 6, in case of a single sync - r esp onse pair m easurement, the R T T has an empirical mean of 80 . 34 microseco nds an d an em pirical standar d deviation of 17 . 0 9 micr oseconds with N = 1 0 and ρ = 0 . 3 . Observe th at ev en for a relatively small N , the empirical distribution appro aches the G a u ssian shape, but has slightly he avier tail on the high er end of the de la y . The distribution for mean of batches of 10 observations has a smaller empirical stan d ard deviation of 5 . 41 micro seco nds. 20 40 60 80 100 120 140 RTT ( s) Observations = 1 Observations = 10 Fig. 6. Empirical distributio n of the R TT of sync - r esponse pairs through a network of N = 10 routers with network idle probabili ty of ρ = 0 . 3 . The light-shaded histog ram shows the empirical distrib ution of the R TT of a single sync - respon se pair . The dark-shaded histogram shows the corresponding distrib ution for the mean of batches of 10 observ ations of the R TT . B. System and Security Requirements The clock at the time seeker B drifts with respect to the true time clock at A unless corrected by a sync message from A . As before, let L d e note th e ale r t limit for the system. Let T deno te a time du ration over wh ich a perf ectly sync hronized clock at B at the beginning of the d uration, absent a n adversary , drifts more than L N for some L N < L with a prob ability smaller than a n accep tably small bou nd P ǫ . In th e system under simula tio n, the clock offset fo r B is estimated and co rrected f o r e very T seconds. By defin ition of T , it holds that if the clocks at A and B are perfectly synchro n ized after e very T seconds, then the n atural drift en velope of B ’ s clock do e s not exceed L with an unacceptably high pr obability . Defin e L M , L − L N Observe that if an adversary is a ble to intro duce a synch r o- nization error larger than L M , then th e system is comprom ised since the n atural drif t o f the clock at B could poten tially lead to a c lo ck offset gre ater than L befo re the next synchronization interval, with a prob ability gre a ter than P ǫ . Thus, A must flag any adversar ia l delay greater than L − L N with prob ability higher th an a desired detec tio n prob ability , denoted by P D . It is worth noting that this pra ctical complicatio n of the magnitude of L N was abstracted in the sufficiency proo f , where the threshold was set to L − δ for δ > 0 . In general, A ma kes multiple measurements of th e R TT between A and B over the time period T . As shown in Fig. 6, the mean of multip le ob servations over T has a distribution with a smaller standard de viation as compared to th at of a sin g le observ ation. In the simulated system, if n o attack is de te c te d , A updates ¯ τ k AB ev ery T seconds b ased on the empirical mean of th e R TT measurements made over th at period. Note that e ven tho ugh ¯ τ k AB is updated based on the measuremen ts, no upda tes are applied to ¯ τ R TT and ¯ σ R TT , which are pre determined by simulation or measurem e nts u nder a secure c a lib ration camp aign. The empirical mean of the measur ed R T T is taken as the test statistic to detect an attack . For the attack model detailed next, it can be shown that this test statistic becom e s optimal for large values of N [34]. C. Atta ck Model The synch ronization system co nsidered in this simulation complies with the necessary secu rity co n ditions presen ted in this paper . Conseq uently , the adversary M is unable to advance the sync or response m essages, and can only increase the R T T measured by A relative to the auth entic R TT . This simulation considers a simple adversary model that introduces a fixed delay in the measured R TT . In order to conce a l its presence while co mprom ising synchro nization with ap precia- ble prob ability , M intro duces a de lay o f L M + ξ second s for some small ξ > 0 . Let H 0 denote the null hyp o thesis (no attack) , and H 1 denote the alterna tive hypo thesis. Under H 0 , the me a sured R TT at A is drawn from the distribution that was used to calibrate/simulate the cha nnel delay distribution, while under H 1 , the measured R TT is drawn f r om a distribution that is shifted from the calibratio n distribution b y L M + ξ . This is visually d epicted in Fig. 7 . Given a detection thresho ld λ , the dark-shad e d region in Fig. 7 denotes th e probability o f false alarm, P F , while the light-shaded region denotes the probab ility of missed detection ( 1 − P D ). In observing Fig. 7 , it might be argued , and holds true, that a rea sonable attacker may introdu c e noise in the introdu ced delay to inflate the width of the distribution unde r H 1 and thereby d ecrease the probability of detection o f an attack . Howev er, in that case, the empir ical mean test statis tic is n o longer optimal. In stead, A would incorpo rate the observed variance of the R TT in its test statistic in additio n to the em pirical mean. In short, the attack model in this simulation is not compr ehensive, as explained p reviously . For a m ore soph isticated treatment o f sensor deception and protection techniqu es, the rea d er ma y ref er to [35]. Fig. 7. Repre sentation of the distribution s under H 0 and H 1 along with the detec tion threshol d and the associ ated P F and P D . D. Simulation The system and attack described above have been simulated with N = 1 0 an d ρ = 0 . 3 fo r all ro uters. The adversarial delay L M + ξ is set to 10 microsecon ds, and the required probab ility of detection P D is set to 0 . 999 . The number of R TT obser vations made in tim e T ar e varied b etween 1 and 200 . Given the number of observations, and a r equired P D , the system is simulated u n der H 1 for 10 6 detection ep ochs and the ma x imum po ssible detection threshold λ th a t satisfies th e detection pr obability is obtaine d. Subsequ e ntly , the system is simulated under H 0 and the number of test statistics exceeding the thresho ld λ are re c orded. The frequ ency of such epochs is reported as th e pro bability of false alarm P F . Fig. 8 shows the above p r ocedur e for 80 R TT measuremen ts made per test statistic. I n this case, λ is o b tained to be 84.53 microsecon ds an d the correspondin g P F is 1 . 59% . Fig. 9 shows a log-log plot o f P F as a fu nction of the numb er of observations made per test statistic. Whe n the numb e r of observations is g reater th an 1 6 0 , no false alarms were ob served with 10 6 trials. For the g i ven chann el delay variation statistics, the p robability of false alarm is very high fo r small num ber of observations p er decision ep o ch since the thresho ld λ that must be set to d e tect an attack with the required P D is large in comp a rison to the min imal de la y th a t th e adversary m ust introdu c e to compr o mise synchron ization ( L M ). For a mor e stable channel, suc h as a wireless or PTP-aw are channel, fewer measuremen ts p er de cision epo ch would suffice. 75 80 85 90 95 RTT ( s) Fig. 8. Distribut ion of the test statistic under H 0 and H 1 for 80 R TT measurement s per decision epoch. ( N = 10 , ρ = 0 . 3 , L M + ξ = 10 µ s, P D = 0 . 999 ) 10 0 10 1 10 2 10 3 Number of Observations over T 10 -5 10 0 Probability of False Alarm Fig. 9. Probability of false alarm as a function of number of observat ions per decision epoch. ( N = 10 , ρ = 0 . 3 , L M + ξ = 10 µ s, P D = 0 . 999 ) E. Pr actical Implicatio ns Section V -A makes fairly remarkab le assum ptions about the syn c h ronization system to show provably secure time transfer . For instance, it requires that erro rs in the a priori estimate of the R TT of the timing messages b e negligible compare d to th e alert limit. Nonetheless, as shown in this section, for a given channel with bou nded delay variations and a given slave clock , som e level of security gu arantee can be made for a sync h ronization system that satisfies the ne cessary and sufficient co n ditions pr e sented h erein. For concrete n ess, consider a system that req uires an ale r t limit of L = 100 microsecon ds and a slave clock that d r ifts no mo re than L N = 50 microsecond s over a period of T = 1 second with acceptably high p robability ( 1 − P ǫ ). Then , f or N = 10 and ρ = 0 . 3 , if A m akes 10 R TT measurements over 1 seco nd, the empirical mean test statistic is d istributed as the da rk- shaded distrib ution in Fig. 6 with a standard de viation of ≈ 5 . 4 microsecon ds. For L M = L − L N = 50 micro seconds, a threshold of ≈ ¯ τ R TT + 30 micro seconds will yield a missed detection rate of a pprox im ately 1 in 150 0 0 , and a false alarm rate of approximately 3 . 5 in 1 millio n . W ith a more stable sla ve clock or mo r e measu rements per secon d, th e se p robabilities can b e m ade more fav orable. Another impo rtant co ncern that h as not been ad dressed in the simulation is that of the incorporatio n of cryptograp hic constructs in the synch ronization p rotocol. The en cryption and decr yption alg orithms are ofte n complex and take non- negligible processing time to execute. Howe ver , note that at A , the sync message is timestamped after the en cryption process, and thus the time taken for encr y ption is in c onsequen tial. At B , it is impor tant to co n cede th at the decryptio n of the sync message and the encryption o f the r espon se message canno t b e assumed to h a ppen instantan eously . This has b e en acco u nted for by a llowing the layover time ¯ τ BB for the cry ptograp hic processes to e xecute. Once again, the rec e ipt timestamp of the r espo nse messag e at A is applied befor e th e decryp tion process, and hen ce the decryptio n time at A is inco nsequential. Thus, com pliance with the first security con dition must n ot pose sign ificant pr actical challen ges. V I I I . C O N C L U S I O N S A f undame n tal theo ry of secure clock synchr o nization was developed for a generic system model. The p roblem of secur e clock sync h ronization was fo rmalized with explicit assump- tions, models, and definitions. It was shown tha t all p o ssible one-way clock synch ronization protoco ls are vulnerab le to re- play attack s. A set o f necessary conditions f or secure two-way clock synch ronization was pro posed and proved. Compliance with these necessary cond itions with strict upper bou nds was shown to be sufficient for secure clock synchr onization, which is a significan t result for provable security in critica l infrastruc- ture. The gene r al applicab ility of the set of security co nditions was demon strated by specializin g these cond itions to design a secure PT P protoco l and an alternative secur e two-way cloc k synchro n ization pr o tocol with GNSS-like sig n als. Results from a simula tio n with mo dels of c h annel delays we re presented to expound the interplay between slave cloc k stability , secu rity requirem ents, attack models, and attack d etection thresh o lds. A C K N O W L E D G M E N T S This project h as b een sup ported b y the National Science Foundation under Grant No. 1 45447 4 (CAREER), by the Data-suppo rted Transportation Op erations and Planning Cen- ter (DSTOP), a Tier 1 USDO T University T ra nsportation Center , and by the U.S. Departm e nt of Energy und er the T ASQC prog ram led by Oak Ridg e Nation a l Labo ratory . R E F E R E N C E S [1] A. Phadke, B. Pick ett, M. Adamiak, M. Bego vic, G. Benmouyal, R. Burnett Jr, T . Cease, J. Goossens, D. Hansen, M. Ke zunovic et al. , “Synchroni zed sampling and phasor measurements for relaying and control , ” IE EE T ransactions on P ower Delivery , vol. 9, no. 1, pp. 442– 452, 1994. [2] J. G. McNeff, “The global positioni ng system, ” IE EE T ransacti ons on Micr owave Theory and T echniqu es , vol. 50, no. 3, pp. 645–652, 2002. [3] J. J. Angel, “When finance meets physics: The impact of the speed of light on financial market s and their regul ation, ” F inancial Revie w , v ol. 2, no. 49, pp. 271–281 , 2014. [4] J. C. Corbett, J. Dean, M. Epstein, A. Fikes, C. Frost, J. J. Furman, S. Ghemawat , A. Gubare v , C. Heiser , P . Hochschild et al. , “Spanner: Googles globally distri buted dat abase, ” ACM T ransactions on Computer Systems (TOC S) , vol . 31, no. 3, p. 8, 2013. [5] L. D. Shapiro, “Time synchroni zation from Loran-C, ” IEEE Spectrum , vol. 8, no. 5, pp. 46–55, 1968. [6] A. Bauch, P . Hetz el, and D. Piester , “T ime and frequency dissemination with DCF77: From 1959 to 2009 and beyond, ” PTB-Mitteilung en , vol. 119, no. 3, pp. 3–26, 2009. [7] D. W . Allan and M. A. W eiss, Accurate time and fre quency transfer dur- ing common-vie w of a GPS satellite . E lectronic Industries Association, 1980. [8] M. L . Psiaki and T . E. Humphre ys, “GNSS spoofing and detection, ” Pr oceedings of the IEEE , vol. 104, no. 6, pp. 1258–12 70, 2016. [9] K. D. W esson, J. N. Gross, T . E. Humphreys, a nd B. L. Evans, “GNSS signal authen tication via po wer and distortion monitoring, ” IEEE T ransactions on Aer ospace and Electr onic Systems , 2018, to be publishe d; preprint av ailable at https://arxi v .org/abs/ 1702.06554 . [10] D. Chou, L. Heng, and G. Gao, “Robust GPS-based timing for phasor measurement units: A position-i nformation-aided ap proach, ” in Pr oceed- ings of the ION GNSS+ Meeti ng , 2014. [11] M. Ullmann and M. V ¨ ogeler , “Delay attacks — Implication on NTP and PTP time synchroniza tion, ” in Preci sion Cloc k Sync hr onization for Measur ement, Contr ol an d Communicati on, 2009. ISPCS 2009. Internati onal Symposium on . IE E E, 2009, pp. 1–6. [12] T . Mizrahi, “ A game theoret ic analysis of delay attacks against time synchroniz ation protoc ols, ” in P re cision Cloc k Synchr onization for Mea- sure ment Contr ol and Communicat ion (ISPCS), 2012 International IEEE Symposium on . IE EE, 2012, pp. 1–6. [13] B . Moussa, M. Debbabi, and C. Assi, “ A detecti on and mitigat ion model for PT P delay attack in an IEC 61850 substation, ” IEEE T ransactions on Smart Grid , 2016. [14] Q. Y ang, D. An, and W . Y u, “On time desynchroniz ation attack against IEEE 1588 protocol in po wer grid systems, ” in Ener gytec h, 2013 IEEE . IEEE, 2013, pp. 1–5. [15] J.-C. T ournier and O. Goerlitz, “Strate gies to secure the IEEE 1588 protocol in digital substation automat ion, ” in Critical Infrast ructure s, 2009. CRIS 2009. F ourth International Confer ence on . IEEE, 2009, pp. 1–8. [16] S. Bhamidip ati, Y . Ng, and G. X. Gao, “Multi- recei ver GPS-based direct time estimation for PMUs, ” in Proc eedings of the 29th Internati onal T echnical Meeti ng of The Satellit e Division of the Institute of Navigatio n (ION GNSS+ 2016), P ortland, OR , 2016. [17] Y . Ng and G. X. Gao, “Robust GPS-based direct time estimation for PMUs, ” in P osition, Location and Nav igation Symposium (PLANS), 2016 IEE E/ION . IEEE, 2016, pp. 472–476. [18] R . Annessi, J. Fabi ni, and T . Zseby , “SecureT ime: Secure multica st time synchroniz ation, ” arXiv pr eprint arXiv:1705.10669 , 2017. [19] L. Narula and T . E. Hum phre ys, “Requi rements for secure wire less time transfer , ” in Procee dings of the IEEE/ION PLANS Meeting , Sava nnah, GA, 2016. [20] R . C. Merkle, “Secure communications ov er insecure channels, ” Com- municati ons of the ACM , vol. 21, no. 4, pp. 294–299, 1978. [21] C . H. Bennett and G. Brassard, “Quantum cryptography: Public key distrib ution and coin tossing, ” 1984. [22] A. K. Ekert, “Quantum cryptography based on Bel l’ s theore m, ” Physical re vie w letter s , vol . 67, no. 6, p. 661, 1991. [23] P . Misra and P . Enge, Global P ositioning System: Signals, Measure ments, and P erformance , re vised secon d ed. Lincoln, Massachusetts: Ganga- Jumana Press, 2012. [24] K. D. W esson, M. P . Rothlisber ger , and T . E. Humphreys, “ A proposed navi gation message authentica tion implementat ion for civil GPS anti- spoofing, ” in P r oceeding s of the ION GNSS Meeting . Portland, Oregon: Institut e of Navigat ion, 2011. [25] D. M. Akos, “Who’ s afraid of the spoofe r? GPS/GNSS spoofing detec tion via automati c gain control (AGC), ” Navigation, Journal of the Institute of Navigation , vol. 59, no. 4, pp. 281–29 0, 2012. [26] T . E. Hum phreys, Springer Handbook of Global Navigation Satellit e Systems . Springer , 2017, ch. Interference, pp. 469–504 . [27] M. Meurer , A. Kono va ltse v , M. Cuntz, and C. H ¨ attich, “Rob ust joint multi-an tenna spoofing dete ction and attitude estimation using direct ion assisted multiple hypothese s RAIM, ” in Procee dings of the 25th Meeti ng of the Satellite Division of the Institut e of Navigati on (ION GNSS+ 2012) . ION, 2012. [28] D. Borio, “P ANO V A tests and their application to GNSS spoofing detec tion, ” IEEE T ransacti ons on A erospac e and Electr onic Systems , vol. 49, no. 1, pp. 381–394, Jan. 2013. [29] M. Bellare and C. Namprempre, “ Authentic ated encryption : Relations among notions and analysis of the generic compositi on paradigm, ” Advances in Cryptolo gy–ASIACR YPT 2000 , pp. 531–545 , 2000. [30] S. Goldwasser , S. Micali, and R. L. Ri vest, “ A digital signature scheme secure against adapti ve chosen -message at tacks, ” SIAM Journal on Computing , vol. 17, no. 2, pp. 281–308, 1988. [31] A. Mahmood, G. Gaderer , H . Trsek, S. Schwal owsk y , and N. Ke r ¨ o, “T ow ards high accurac y in IEEE 802.11 based clock synchroniz ation using PTP , ” in Preci sion Cloc k Synch ron ization for Measur ement Con- tr ol and Communic ation (ISPCS), 2011 Internation al IE EE Symposium on . IEEE, 2011, pp. 13–18. [32] T . Cookle v , J. C. Eidson, and A. Pakdaman, “ An implementation of IE E E 1588 ov er IEE E 802.11b for synchroniza tion of wireless local area net- work nodes, ” IE EE T ransactions on Instrumen tation and Measur ement , vol. 56, no. 5, pp. 1632–1639, Oct. 2007. [33] R . Ra maswamy , N. W eng, and T . W olf, “ Characteri zing netw ork processing delay , ” in Global T elecommun ications Confere nce, 2004. GLOBECOM’04. IEE E , vol. 3. IEE E, 2004, pp. 1629–1634. [34] H. L. V an Tr ees, Detect ion, estimation, and modulation theory , part I: detec tion, estimatio n, and linear modulation theory . John Wil ey & Sons, 2004. [35] J. Bhatti and T . Humphrey s, “Hostile control of ships via false GPS sig- nals: Demonstrati on and detect ion, ” Navigation, Jou rnal of the Insti tute of Navigation , vol. 64, no. 1, 2017. Lakshay Narula rec eiv ed the B.T ech. degree in elect ronics engin eering fr om IIT -BHU, India , in 2014, and the M.S. degree in elect rical and computer enginee ring from The Uni versity of T exas at Austin, Austin, T X , USA, in 2016. He is currently a Ph.D. student with the Depart- ment of E lectr ical a nd Computer Engineering at The Univ ersity of T exas at Austin, and a Graduate Researc h Assistant at the UT Radiona vigati on Lab . His research inte rests includ e GNSS signal process- ing, secure perception in autonomous systems, and detec tion and estimation. Lakshay has previousl y been a visiting student at the PLAN G roup at Uni versity of Calgary , Calgary , AB, Canada, and a systems enginee r at Accord Softwa re & Systems, Bangalore , India. He was a recipient of the 2017 Qualcomm Innov ation Fello wship. T odd E. Humphreys recei ved the B.S . and M.S. degre es in elec trical and computer engine ering from Utah State Univ ersity , Logan, UT , USA, in 2000 and 2003, respecti vely , and the Ph.D. degre e in aerospac e enginee ring from Cornell Univ ersity , Itha ca, NY , USA, in 2008. He is an Associate Professor with the Depart ment of Aerospace Engineering and Engineering Mechan- ics, The Univ ersity of T exas (UT) at Austi n, Austin, TX, USA, and Director of the UT Radionavig ation Laboratory . He speci alizes in the applicati on of op- timal detecti on and estimation techniques to problems in satelli te navigat ion, autonomous systems, and signal processing. His recent focus has been on secure percepti on for autonomous systems, includi ng navigati on, timing, and colli sion avoi dance, and on centimet er-accu rate location for the m ass market. Dr . Hum phreys recei ved the Univ ersity of T exas Regents’ Outstanding T eaching A ward in 2012, the Nation al Science Foundati on CAREER A ward in 2015, and the Institute of Navigati on Thurlow A ward in 2015.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment