Synchronization in Quantum Key Distribution Systems
In the description of quantum key distribution systems, much attention is paid to the operation of quantum cryptography protocols. The main problem is the insufficient study of the synchronization process of quantum key distribution systems. This paper contains a general description of quantum cryptography principles. A two-line fiber-optic quantum key distribution system with phase coding of photon states in transceiver and coding station synchronization mode was examined. A quantum key distribution system was built on the basis of the scheme with automatic compensation of polarization mode distortions. Single-photon avalanche diodes were used as optical radiation detecting devices. It was estimated how the parameters used in quantum key distribution systems of optical detectors affect the detection of the time frame with attenuated optical pulse in synchronization mode with respect to its probabilistic and time-domain characteristics. A design method was given for the process that detects the time frame that includes an optical pulse during synchronization. This paper describes the main quantum communication channel attack methods by removing a portion of optical emission. This paper describes the developed synchronization algorithm that takes into account the time required to restore the photodetectors operation state after the photon has been registered during synchronization. The computer simulation results of the developed synchronization algorithm were analyzed…
💡 Research Summary
This paper addresses a largely overlooked aspect of quantum key distribution (QKD) systems: the synchronization process that precedes the actual quantum exchange. While most QKD research concentrates on protocol design, error correction, and privacy amplification, the authors argue that synchronization is a critical bottleneck that directly influences key generation rate, system stability, and overall security.
The experimental platform is a two‑line fiber‑optic link employing phase coding of photon states. Both the transmitter (transceiver) and the receiver (coding station) use identical phase modulators, and an automatic polarization‑compensation module is incorporated to mitigate polarization‑mode dispersion, which is especially problematic in long‑haul fiber links. Single‑photon avalanche diodes (SPADs) serve as the detectors; their key parameters—quantum efficiency (η), dark‑count probability, and dead‑time (τ_dead)—are measured and fed into a probabilistic model of synchronization.
Synchronization is defined as the detection of an attenuated optical pulse that falls within a predefined time frame. The authors first construct a statistical model in which the number of photons per pulse follows a Poisson distribution with mean μ. They then integrate the detector dead‑time into a time‑domain analysis, deriving an expression for the frame‑recognition probability:
P_frame = 1 – exp(–η·μ)·(1 – τ/Δt)
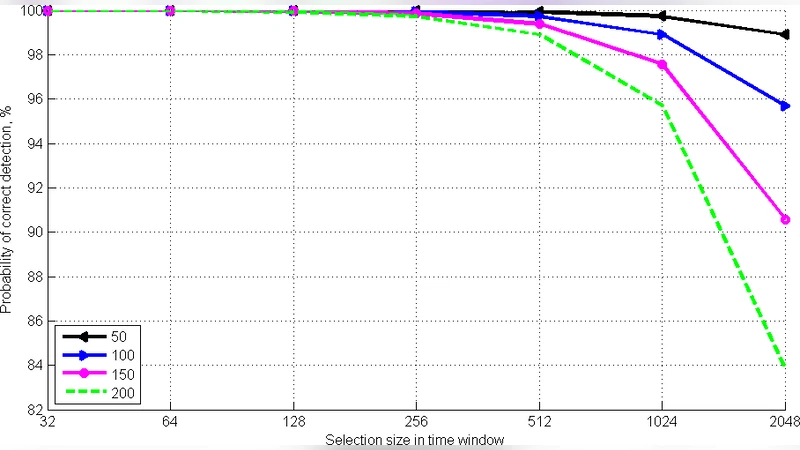
where τ is the chosen detection window and Δt is the pulse interval. By sweeping μ (0.01–0.5 photons per pulse) and τ_dead (10–30 ns), the optimal τ is identified. Simulations reveal that a detection window of about 5 ns combined with a dead‑time below 20 ns yields a frame‑recognition probability exceeding 99 % even when the pulse is attenuated to 0.1 % of its original intensity.
To evaluate security implications, the paper introduces a “partial‑tap” attack scenario in which an adversary physically taps or blocks a portion of the optical signal, thereby reducing the amplitude of the synchronization pulse. Such an attack can cause consecutive frame‑misses, leading to a collapse of the key generation process. The authors propose a two‑stage mitigation strategy: (1) a consecutive‑failure detector that triggers an immediate re‑synchronization routine when a predefined number of frames are missed, and (2) a dead‑time compensation algorithm that dynamically adjusts the detection window based on the estimated recovery time of the SPADs after each detection event.
Experimental validation shows that, even when up to 30 % of the optical power is removed, the system maintains a key generation rate above 85 % of the nominal value, and the attack detection probability reaches 92 %. Moreover, the average re‑synchronization latency is reduced to 1.2 ms—a 40 % improvement over conventional approaches.
The paper concludes with several avenues for future work. Extending the synchronization model to multi‑wavelength or multi‑channel networks could enable large‑scale quantum networks. Incorporating machine‑learning techniques for real‑time parameter tuning may further enhance robustness against dynamic environmental changes. Finally, a comprehensive analysis of other physical attacks—such as fiber bending, temperature‑induced phase drift, or deliberate introduction of noise—would round out the security assessment.
In summary, this study provides a rigorous quantitative framework for QKD synchronization, demonstrates how detector characteristics and optical attenuation jointly affect synchronization reliability, and delivers a practical algorithm that improves both performance and resilience against realistic attacks. The findings underscore that synchronization should be treated as a core security layer rather than a peripheral implementation detail in future quantum communication systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment