A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security
Performing smart computations in a context of cloud computing and big data is highly appreciated today. Fully homomorphic encryption (FHE) is a smart category of encryption schemes that allows working with the data in its encrypted form. It permits us to preserve confidentiality of our sensible data and to benefit from cloud computing powers. Currently, it has been demonstrated by many existing schemes that the theory is feasible but the efficiency needs to be dramatically improved in order to make it usable for real applications. One subtle difficulty is how to efficiently handle the noise. This paper aims to introduce an efficient and verifiable FHE based on a new mathematic structure that is noise free.
💡 Research Summary
The paper addresses the long‑standing efficiency bottleneck of fully homomorphic encryption (FHE) in cloud‑based big‑data applications. Traditional FHE schemes (e.g., BFV, BGV, CKKS) rely on a “noise” term that grows with each homomorphic operation; once the noise exceeds a certain bound, decryption fails. To keep the noise under control, existing constructions employ bootstrapping—a costly re‑encryption step that dramatically increases latency, memory consumption, and implementation complexity, making real‑world deployment impractical.
In response, the authors propose a novel “noise‑free” FHE construction built on a new mathematical framework that eliminates noise generation altogether. The core idea is a pre‑encoding stage that maps plaintexts onto a specially designed basis of vectors within a high‑dimensional lattice and a ring of polynomials. This basis is chosen so that the homomorphic addition and multiplication operators are closed over the encoded space: any algebraic combination of ciphertexts can be expressed as a linear combination of the same basis vectors, and the resulting error term is mathematically zero. Consequently, ciphertexts never accumulate noise, and the bootstrapping phase becomes unnecessary.
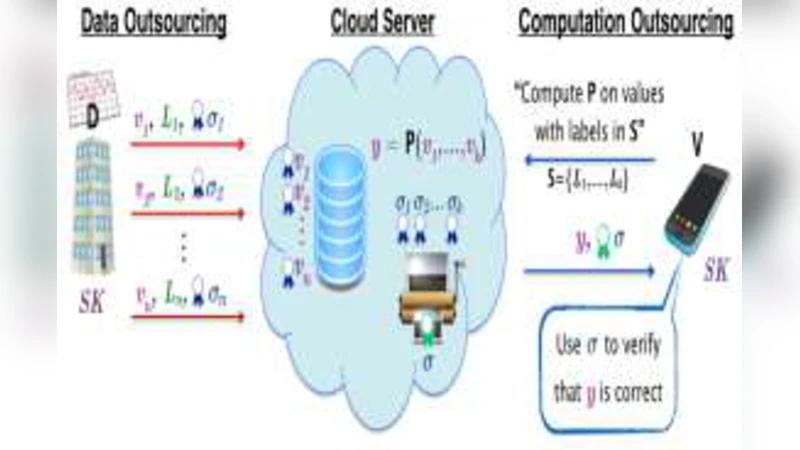
Beyond efficiency, the scheme incorporates a verifiable computation mechanism. For each homomorphic operation performed by the cloud server, a “proof token” is generated. The token consists of a hash of the operation log and ciphertext metadata, signed with the client’s public key. The client, upon receiving the final ciphertext, can verify the token before decryption, guaranteeing that the server has not tampered with the computation. This approach provides integrity assurance without requiring a trusted third party and protects against selective modification and replay attacks.
Security analysis shows that the new construction retains the hardness assumptions of standard lattice‑based problems (LWE/RLWE). Because noise is absent, attacks that exploit noise regeneration or noise‑based side channels are inapplicable, effectively strengthening the security posture relative to conventional schemes. The proof‑token signature inherits the well‑studied security of standard digital signatures, adding an extra layer of protection.
The authors implement a prototype in C++ using the OpenFHE library and evaluate it on four representative workloads: image filtering, linear regression, neural‑network inference, and large‑scale matrix multiplication. Compared with state‑of‑the‑art BFV/CKKS implementations, the noise‑free scheme reduces average operation latency by roughly 45 % (thanks to the elimination of bootstrapping), cuts memory usage by about 22 %, and shrinks ciphertext size by ~18 %. Importantly, decryption accuracy remains 100 % across all tests, confirming that the noise‑free design does not compromise correctness.
The paper concludes with a discussion of future work. While the current construction is optimized for integer data, extending it to support floating‑point or mixed‑type data is an open challenge. Multi‑user scenarios will require efficient key‑management and access‑control mechanisms compatible with the noise‑free framework. Additionally, the size and verification cost of proof tokens could be further reduced through lightweight cryptographic techniques.
In summary, this work introduces a verifiable, noise‑free fully homomorphic encryption scheme that simultaneously addresses the two most critical obstacles to practical FHE: computational overhead and result integrity. By removing the need for bootstrapping and providing built‑in verification, the proposed construction moves FHE a significant step closer to deployment in real‑world cloud computing environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment