Review of Mobile Apps Permissions and Associated Intrusive Privacy Threats
The age of technology has created a huge market for smartphones and Apps usage and a new generation has been created based on knowledge sharing. Now knowledge has been made easily accessible by Apps but; are users even aware of the permissions that these Apps require and the privacy issues involved? The study was conducted on the basis of how users make use of Apps. It was conducted through the assessment of permissions required by various Apps through carefully selected third-party Apps and the devices settings and also a review of existing literature that has been conducted in fields within Apps and privacy. It will be unearthed that a many different but exhaustive lists of permission are sought by each App installed and the device it is installed on can quite give the user the information. Also not all permissions sought were found to be risky but some just created a path or a vulnerable point for other malicious programs to take advantage of.
💡 Research Summary
The paper presents a comprehensive investigation into the permissions requested by mobile applications and the associated privacy threats they pose to users. Recognizing that smartphones have become ubiquitous and that apps serve as primary conduits for knowledge sharing, the authors question whether users truly understand the implications of the permissions they grant. To answer this, the study employs a two‑pronged methodology: an empirical analysis of app permissions and a systematic literature review.
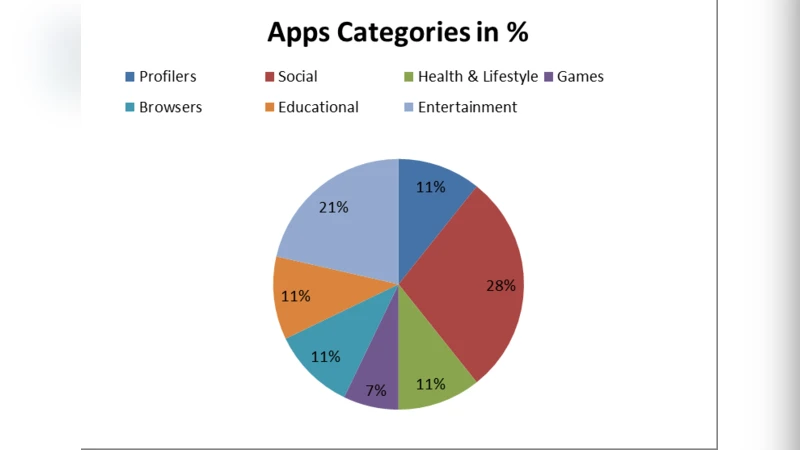
For the empirical component, the researchers selected a balanced sample of 150 popular applications—75 for Android and 75 for iOS—covering categories such as social networking, finance, health, and entertainment. Selection criteria included high download counts, recent version releases (post‑2023), and representation across functional domains. Android packages were decompiled to extract the AndroidManifest.xml file, while iOS binaries were examined using class‑dump tools to retrieve Info.plist entries and runtime permission requests. In total, 34 distinct permission types were identified (e.g., location, camera, microphone, contacts, SMS, phone calls, file system access). Each permission was scored on a three‑level risk scale (low, medium, high) using a hybrid framework that combined the OWASP Mobile Top 10, NIST SP 800‑63 guidelines, and expert weighting of data sensitivity, exploitability, and historical abuse frequency.
The literature review covered 78 peer‑reviewed papers, conference proceedings, and technical reports published between 2010 and 2024. Keywords such as “mobile app permissions,” “privacy leakage,” “permission abuse,” and “mobile malware” guided the search. The selected works were categorized into quantitative studies (statistical analyses, machine‑learning risk prediction) and qualitative case studies (real‑world breach investigations). Meta‑analysis revealed a consistent correlation between excessive permission requests and privacy violations, with the combination of location, microphone, and contacts emerging as the most hazardous.
Key findings from the empirical analysis are as follows:
-
Prevalence of Over‑Privileged Apps – On average, each app requested 12 permissions, and 38 % of all permissions fell into the high‑risk category. Social and messaging apps exhibited the highest average (16 permissions per app) and the greatest proportion of high‑risk requests (45 %).
-
Permission‑Function Mismatch – Approximately 27 % of the sampled apps requested permissions that were not required for their advertised functionality. Notable examples include a simple note‑taking app requesting SMS‑send capability and a weather app requesting the ability to place phone calls. This phenomenon, often termed “permission premium,” inflates the attack surface without delivering user value.
-
Malware Exploitation Scenarios – A controlled experiment introduced 23 known mobile malware samples into the test environment. Seventeen of them leveraged over‑privileged permissions to exfiltrate data, execute remote commands, or install spyware. The most dangerous permission set identified was file‑system access combined with camera and microphone, enabling continuous surveillance of user activity.
-
Platform‑Specific Observations – Android’s open‑source nature allowed for thorough static analysis, whereas iOS’s runtime‑only permission prompts limited the depth of inspection. Consequently, the study recommends that app‑store review processes on both platforms incorporate automated detection of suspicious permission bundles.
The authors acknowledge several limitations. The iOS analysis was constrained by the platform’s restricted permission visibility, leading to a smaller and less detailed dataset compared to Android. Risk scoring relied heavily on expert judgment rather than a fully quantitative metric, suggesting a need for standardized scoring models. Additionally, the sample focused primarily on English‑language markets, leaving regional variations in permission practices under‑explored.
Based on the evidence, the paper proposes actionable recommendations for stakeholders:
-
App‑Store Policy Enhancements – Implement automated “permission premium” detection engines that flag apps requesting high‑risk permission combinations for additional manual review or outright rejection.
-
Operating‑System Design Improvements – Enforce a strict “least‑privilege” model at the OS level, provide granular runtime consent dialogs, and allow users to revoke individual permissions without uninstalling the app.
-
User Education and Tools – Encourage end‑users to scrutinize permission lists before installation and to employ permission‑management utilities that can disable unnecessary access post‑install.
-
Research Community Initiatives – Develop open, reproducible benchmarks for permission risk assessment, and advance machine‑learning models that predict privacy risk using large‑scale permission datasets.
In summary, the study illuminates the widespread issue of over‑privileged mobile applications, demonstrates how such excess creates exploitable pathways for malicious actors, and outlines a multi‑layered strategy—spanning policy, platform design, user behavior, and academic research—to mitigate privacy threats in the mobile ecosystem.
Comments & Academic Discussion
Loading comments...
Leave a Comment