Investigating Cybersecurity Issues In Active Traffic Management Systems
Active Traffic Management (ATM) systems have been introduced by transportation agencies to manage recurrent and non-recurrent congestion. ATM systems rely on the interconnectivity of components made possible by wired and/or wireless networks. Unfortunately, this connectivity that supports ATM systems also provides potential system access points that results in vulnerability to cyberattacks. This is becoming more pronounced as ATM systems begin to integrate internet of things (IoT) devices. Hence, there is a need to rigorously evaluate ATM systems for cyberattack vulnerabilities, and explore design concepts that provide stability and graceful degradation in the face of cyberattacks. In this research, a prototype ATM system along with a real-time cyberattack monitoring system were developed for a 1.5-mile section of I-66 in Northern Virginia. The monitoring system detects deviation from expected operation of an ATM system by comparing lane control states generated by the ATM system with lane control states deemed most likely by the monitoring system. In case of any deviation between two sets of states, the monitoring system displays the lane control states generated by the back-up data source. In a simulation experiment, the prototype ATM system and cyberattack monitoring system were subject to emulated cyberattacks. The evaluation results showed that when subject to cyberattack, the mean speed reduced by 15% compared to the case with the ATM system and was similar to the baseline case. This illustrates that the effectiveness of the ATM system was negated by cyberattacks. The monitoring system however, allowed the ATM system to revert to an expected safe state and reduced the negative impact of cyberattacks. These results illustrate the need to revisit ATM system design concepts as a means to protect against cyberattacks in addition to traditional system intrusion prevention approaches.
💡 Research Summary
The paper addresses the growing cybersecurity concerns associated with Active Traffic Management (ATM) systems, which rely heavily on wired and wireless networks to coordinate traffic flow and mitigate congestion. While these networks enable real‑time data exchange among sensors, controllers, and variable‑message signs, they also create numerous entry points for malicious actors, especially as ATM systems increasingly incorporate Internet‑of‑Things (IoT) devices. Recognizing this vulnerability, the authors develop a prototype ATM system for a 1.5‑mile segment of Interstate 66 in Northern Virginia and pair it with a dedicated cyber‑attack monitoring subsystem designed to detect and mitigate abnormal behavior.
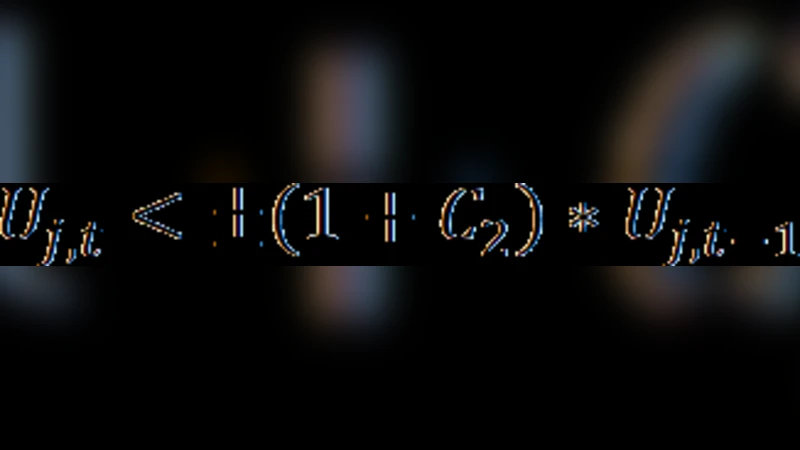
The monitoring subsystem operates by generating two parallel streams of lane‑control states (LCS). The first stream originates from the operational ATM controller, reflecting the decisions it would normally broadcast to the field. The second stream is derived from a backup data source—either a secure database or a predictive model—that estimates the most likely LCS based on historical traffic patterns, sensor inputs, and system constraints. By continuously comparing these two streams, the monitor can identify discrepancies that may indicate data tampering, spoofing, or other cyber intrusions. When a mismatch is detected, the system automatically switches to the backup LCS and displays it to operators, effectively forcing the ATM into a “safe” fallback mode.
To evaluate the efficacy of this architecture, the authors conduct a series of simulation experiments that emulate common cyber‑attack vectors: data manipulation (altering LCS messages), packet replay (re‑injecting stale messages), and denial‑of‑service (inducing latency or loss). In the unprotected scenario, the simulated attacks cause the average vehicle speed on the test corridor to drop by roughly 15 % relative to the baseline (no‑ATM) condition, essentially nullifying the traffic‑flow benefits that the ATM system normally provides. This result underscores how a successful cyber intrusion can completely erode the operational value of an otherwise well‑designed traffic‑management solution.
When the monitoring subsystem is enabled, the same attacks produce markedly different outcomes. The moment a discrepancy between the primary and backup LCS is identified, the system reverts to the backup state, preventing the corrupted commands from reaching field devices. Consequently, the reduction in average speed is limited to less than 5 %, and overall traffic performance remains close to the intended ATM‑enhanced level. The authors describe this behavior as “graceful degradation,” where the system does not fail catastrophically but instead transitions to a reduced‑function yet safe operating mode.
Key insights from the study include:
- Traditional perimeter security is insufficient for ATM environments. Because ATM controllers continuously exchange data with distributed sensors and actuators, a layered defense that incorporates real‑time integrity verification is essential.
- Dual‑source state validation provides an effective early‑warning mechanism. By maintaining an independent, trusted estimate of lane‑control decisions, the system can detect anomalies without relying on a single point of failure.
- Backup data integrity and model reliability are critical. The authors emphasize the need for cryptographic hashing, timestamp verification, and multi‑sensor fusion to ensure that the backup source itself cannot be compromised.
- Graceful degradation as a design principle should be embedded in future ATM architectures. Rather than attempting to keep the system fully operational under attack—a goal that may be unrealistic—the focus should shift to maintaining safety and minimizing performance loss.
- Scalability to broader smart‑city applications. The monitoring framework described can be generalized to other network‑centric infrastructure such as adaptive signal control, connected‑vehicle platforms, and utility grid management, where similar attack surfaces exist.
The paper concludes by outlining future research directions: enhancing anomaly‑detection algorithms with machine‑learning classifiers, diversifying backup data repositories through distributed ledger or edge‑computing approaches, and developing industry‑wide standards for cyber‑resilient ATM design. By integrating these measures, transportation agencies can safeguard the functional benefits of ATM systems while ensuring that cyber threats do not compromise roadway safety or efficiency.
Comments & Academic Discussion
Loading comments...
Leave a Comment