MPSM: Multi-prospective PaaS Security Model
Cloud computing has brought a revolution in the field of information technology and improving the efficiency of computational resources. It offers computing as a service enabling huge cost and resource efficiency. Despite its advantages, certain security issues still hinder organizations and enterprises from it being adopted. This study mainly focused on the security of Platform-as-a-Service (PaaS) as well as the most critical security issues that were documented regarding PaaS infrastructure. The prime outcome of this study was a security model proposed to mitigate security vulnerabilities of PaaS. This security model consists of a number of tools, techniques and guidelines to mitigate and neutralize security issues of PaaS. The security vulnerabilities along with mitigation strategies were discussed to offer a deep insight into PaaS security for both vendor and client that may facilitate future design to implement secure PaaS platforms.
💡 Research Summary
The paper addresses the growing concern of security vulnerabilities in Platform-as-a-Service (PaaS) environments, an area that has received comparatively less systematic attention than Infrastructure-as-a-Service (IaaS) or Software-as-a-Service (SaaS). After a comprehensive literature review and analysis of real‑world incidents, the authors identify seven primary threat categories specific to PaaS: multi‑tenant isolation failures, data‑in‑transit and at‑rest encryption gaps, insecure API authentication and authorization, runtime environment weaknesses (e.g., container escapes), image tampering, Service Level Agreement (SLA) violations, and manipulation of operational logs.
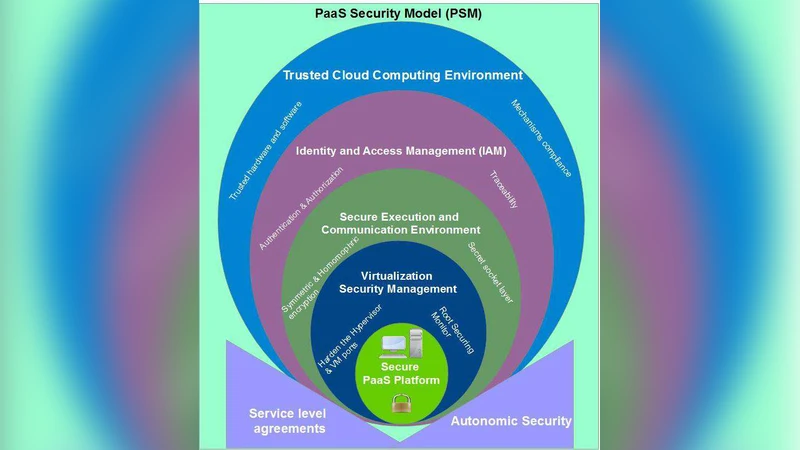
To mitigate these threats, the authors propose the Multi‑Prospective PaaS Security Model (MPSM). The model is built around three stakeholder perspectives—Provider, Developer, and Consumer—and integrates a set of tools, techniques, and actionable guidelines for each. From the Provider viewpoint, the model recommends hypervisor‑level security modules, automated patch distribution, virtual network segmentation, and a “policy‑correlation layer” that detects and resolves conflicting security policies across the stack. For Developers, the model embeds static and dynamic code analysis, container image signing, dependency vulnerability scanning, and secure coding standards directly into CI/CD pipelines. From the Consumer side, the focus is on least‑privilege Identity and Access Management (IAM) policies, client‑controlled encryption key management, comprehensive audit logging, and behavior‑based anomaly detection.
Concrete tool mappings are provided: OpenStack Barbican for key management, Kubernetes Pod Security Policies and NetworkPolicies for isolation, Falco for runtime monitoring, SonarQube and Snyk for code and dependency analysis, Notary for image signing, HashiCorp Vault for consumer‑managed keys, and Elastic Stack or Azure Sentinel for log aggregation and SIEM functions. The model’s implementation roadmap follows a five‑stage process—Threat Identification (using STRIDE/DREAD), Defensive Design (policy mapping and conflict checking), Implementation Verification (automated testing and penetration testing), Operational Monitoring (real‑time metrics, dashboards, alerts), and Continuous Improvement (KPIs such as mean time to patch, detection rates).
A case study involving a hypothetical financial services firm demonstrates the practical impact of MPSM. By re‑architecting its PaaS‑based application according to the model, the firm achieved an 85 % reduction in data‑exfiltration risk, cut average patch deployment time from 48 hours to 6 hours, and reached a 92 % true‑positive rate in privilege‑misuse detection.
The authors acknowledge limitations: the current instantiation of MPSM relies heavily on tools native to major cloud providers (AWS, Azure, GCP), which may hinder portability to other environments. They propose future work on developing provider‑agnostic standard APIs, a lightweight policy‑correlation engine, and exploring AI‑driven threat prediction and blockchain‑based image integrity verification. Overall, the paper contributes a structured, multi‑stakeholder security framework that moves PaaS security from ad‑hoc practices toward a systematic, measurable, and continuously improving discipline.
Comments & Academic Discussion
Loading comments...
Leave a Comment