Robust LSB Watermarking Optimized for Local Structural Similarity
Growth of the Internet and networked multimedia systems has emphasized the need for copyright protection of the media. Media can be images, audio clips, videos and etc. Digital watermarking is today extensively used for many applications such as auth…
Authors: Amin Banitalebi, Said Nader-Esfahani, Alireza Nasiri Avanaki
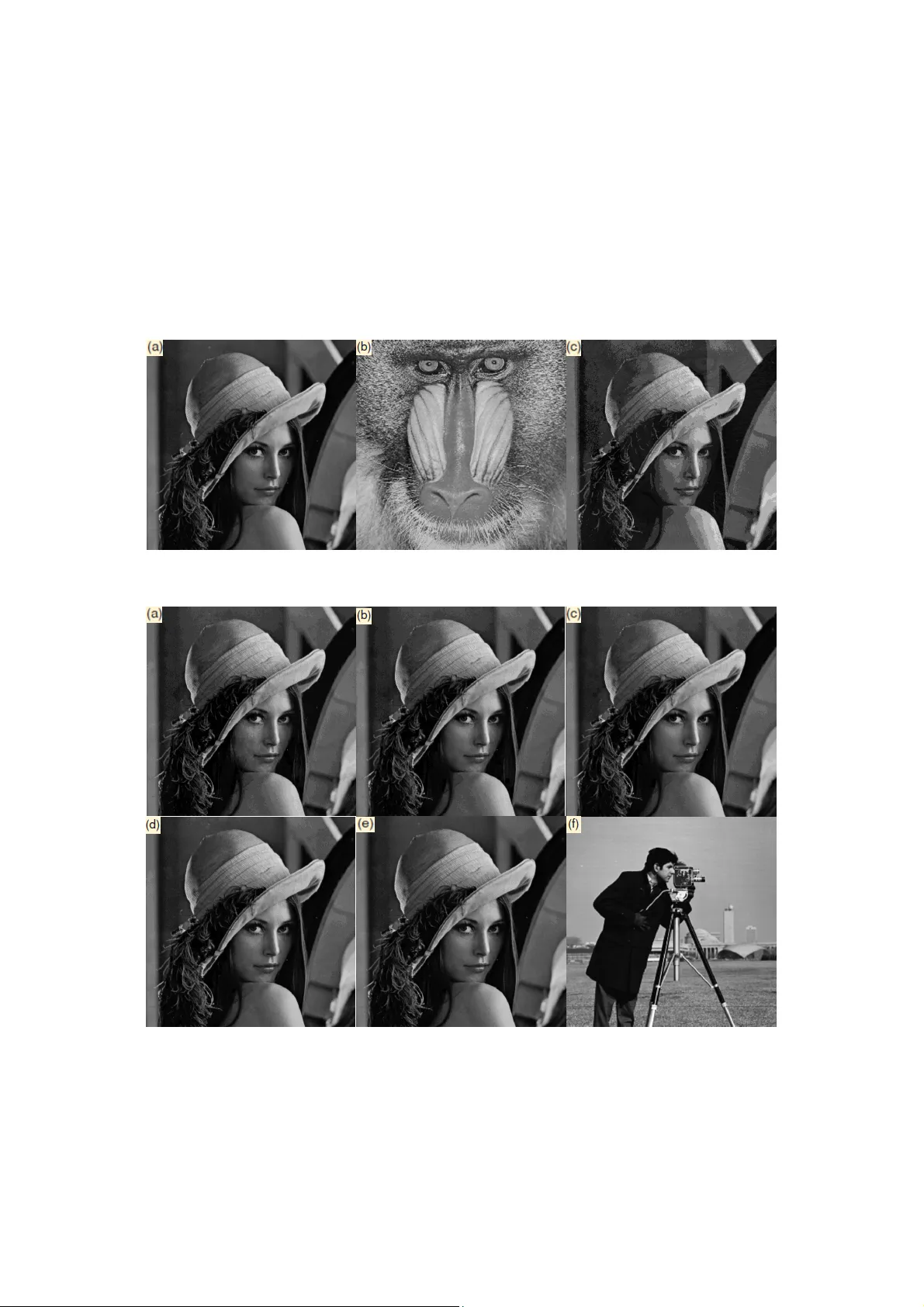
Robust LSB Watermarking Optimized for Local Structural Similarity Amin Banitalebi, Said Nader-Esfahani, Alireza Nasiri Avanaki School of Electrical and Comput er Engineering University of Tehran, Tehran 14395-515, Iran banitalebi@ieee.org Abstract —Growth of the Internet and networked multimedia systems has emphasized the need for copyright protection of the media. Media can be images, audio clip s, videos and etc. Digital watermarking is today extensively used for man y applications such as authentication of ownership or identification of illegal copies. Digital watermark is an invisibl e or maybe visible structure added to the original media (known as a sset). Images are considered as communication channel when they are sub ject to a watermark embedding procedure so in the cas e of embedding a digital wa termar k in an image, the capacity of the channel should be considered. There is a trade-of f between imperceptibilit y, robustness and capacity for embeddi ng a watermark in an asset. In the case of image watermarks, it is reasonable that the watermarking algorithm should depend on the content and structure of the image. Conventionally, mean squared error (MSE) has been used a s a common distort ion measure to assess the quality of the images. Newly developed quality metrics proposed some distortion measu res that are based on human visual s ystem (HVS). These met rics show that MSE is not based on HVS and it has a lack of accu racy when dealing with perceptually important s ignals such as images and videos. SSIM or structural similarit y is a state of the art HVS ba sed image quality crit erion that has recen tly been of mu ch interest. In this paper we propose a robust least significant bit (LSB) watermarking scheme which is optimized for stru ctural similarity. The watermark is embedded i nto a host image through an adaptive algorithm. Va rious attacks examin ed on the embedding approach and simulation results revealed the fact that the watermarked s equence can be extracted with an acceptable accuracy after all attacks. In comp arison to the or iginal algorithm, the proposed method increases the capacity while the imperceptibilit y and robustness remain fix. Keywords-digita l watermarking; structural simila rity; Least significant bit watermarking. I. I NTRODUCTI ON Watermarking is usually defined as the prac tice of imperceptible altering a work to embed a message about that work [6]. W ith the g rowth of the Inte rnet an d mult imedia industry the usage of the watermarking for proof of ownership and copyright protection is an indispensable necessity. There are some considerati ons when embedding a dig ital watermark into a host signal. The main concern of the embedding part of any data hiding syst em is to make the hidden data imperceptible. This task can be achieved either implicitly, by properly choosing the set of host features and embedding rule, or explicitly, by introduc ing a concealment step after embedding [7]. But, there is trade-off between imperceptibility, robustness and capacity o f the watermarking system; a triangular trade-off in which moving toward each corner will take us away from the other corners. Perhaps we can introduce another important parameter, the co mplexity of the embedding algorithm or speed of each embedding action. This parameter is important when e mbedding action should be done rapidly and maybe iteratively for each user. Transaction watermarking is the best example for this i dea [5]. Transaction watermarking is copyright protection for online shops by customer identification watermarking in which a speci fic watermark should be embedded in the media each time a user downloads that media. An ideal water marking scheme should considers these trade-offs into account in the best way. In the case of image signals, watermark can directly be embedded to the spatial domain or in the transfor m domain. It can be visible or invisible. Here, we address the invisible watermarking strategies. As we mentioned above, there are two main requirements o f invisible w atermarks: E mbedded watermark should be perceptually invisible and robust to common signal processing and intentional attacks while the capacity is already taken into account. Focus of early researches on digital water marking was al most on the first objective without considerin g the second one. Recently much works have been done to find the best trade-off between robustness, imperceptibility and capacity [8-14]. In some methods watermarks are i mplied in the pixel domain [15-17]. Embedding in the asset domain could ha ve possible advantages such as low complexity, low cost, low delay as well as this fact that temporal/spatial localization o f the watermark is automatically achieved, thus permittin g a better characterization of the distortion introduced by the watermark and its possible annoying effects. In the transform domain, the wat ermark is inse rted into th e coef ficien ts of a digi tal tra nsform of the host asset. Barni’s main work was on the discrete cosine transf orm (DCT) an d di screte Fouri er tran sfo rm (DFT ) [20] . Embedding in the wavelet domain transfor m is also of much interest [2]. [18] Utilized DCT and [19] util ized contourlet as their transforms. Usually transform domain watermarks exhibit a higher robustness to the attacks. More imperceptibility can be achieved by avoiding the changes into the low frequency components. Complexity of this type of e mbedding can be the trade-off of this system. It has been showed that MSE cannot track the human perception carefully [21-23]. The Applicati ons of HVS based image quality criterions are being s pread recent years. So me works have been done in the field of digital water marking with the human perception concluded in those approaches [2,3,4]. For example, [3] used a noise visibility function (NVF) to set a threshold for embedding rule capacity. In this paper we propose a novel digital watermarking method that utilizes SSIM in the embedding and extraction rules. We have tested our a lgorithm on the LSB watermarking scheme. The original LSB water marking is modified so that the capacity is maximized, while the watermark re mains imperceptible. Insertion of the watermark sequence is an adaptive procedure. The stop condition for water mark insertion in each block of image is specified by an SSIM threshold. In section II SSIM theory will be rev iew. Section III describes our proposed method an d section IV is dedica ted to the simulation results as well as comparison while secti on V concludes the paper. II. S TRUC TURA L S IMILAR ITY B ASICS Natural images are highly structured and this local dependency of the pixels is not c ompletely removed during a digital transform. This fact is the basic idea to the definition of the SSIM. The reference (original) and the distorted images ( x , y respectively) are decomposed to their luminance, contrast and structure components. These components are defined as: ) 1 ( ) ( ) , ( , ) 2 ( ) , ( , ) 2 ( ) , ( 3 3 2 2 2 2 1 2 2 1 C C y x s C C y x c C C y x l y x xy y x y x y x y x And the local SSIM metric is defined as: ) 2 ( ) .( ) 2 .( ) 2 ( ) , ( . ) , ( . ) , ( ) , ( 3 3 2 2 2 2 1 2 2 1 C C C C C C y x s y x c y x l y x S y x xy y x y x y x y x In the above equation, , , are three parameters that are used for the adjustment of the importance of each of the three components. We suppose that t hey have all equal importance. μ x and μ y are (respectively) the local sa mple means of x and y , σ x and σ y are (respectively) the local sample standard deviations of x and y , and σ xy is the sample cross correlation of x and y after removing their means. The item s C 1 , C 2 , and C 3 are small positive constants that stabilize each term, so that near-zero sample means, v ariances, or correlations do not lead to numerical instability. The entire SSIM metric between the original and the reference image i s calculated by averaging the local SSIM all over the image. More details are available at [23]. III. P ROPOS ED M ETHOD A. Original LSB algorithm We will have a short review on original LSB approach. The asset is image A and the watermark image is B . N is a parameter that shows the e mbedding depth. Suppose that we have 8-bit images. The algorithm says that: N left-sided bits o f the image B should be repla ced with the N right-side d bits o f the image A for each pixel (represented in 8-bit for mat). In this way, most significant bits or equally important infor mation of imag e B is watermarked in the place of l east significant bits or details of the image A . Fig. 1 shows the original Lena image ( A ) and wat ermark imag e ( B ) and corresponding watermarked imag e. B. Proposed Algorithm The proposed algorith m finds a good trade-off point between capacity and i mperceptibility and robustness. The embedding process can be done in the follo wing steps: Step1: divide the asset ( A ) and the watermark ( B ) imag es into k×k blocks. We set k=11 for the sake of simulation speed and complexity reduction. Step 2: f or th e i th block of both images, compute the SSIM index between these two blocks. Name this local block similarity as SSIM_i. Step 3: if SSIM_i is greater than a pre-specified threshold ( thr1 ) then do the original L SB embedding algorithm for one bit of only these two blocks, i. e. replace the left sided bit of all pixels of the i th block of B with the right sided bit o f corresponding pixels of the i th block of im age A . Step 4: co mpute SSIM between the i th block of A an d the i th block (the block gener ated in step 3) of the new image (watermarked image or W ). If the si milarity is greater than a second threshold ( thr2 , we chose 0. 75) then repeat step 3 fo r another bit, i . e. embe d anoth er bit of B in W . For example if we have just embedded the j th bit of B in W and the new SSIM is bigger than thr2 then we shou ld embed the (j+1) th bit. Step 5: repeat step 4 until t he new computed SSIM would become less than thr2 . Stop the e mbedding in this block now and go to step 2 for the (i+1) th block. The proposed algorithm leads us to a local optimum of watermark embedding in the case that by adjusting the threshold value one can directly tune the imperceptibility and capacity. Another advantage of this method is that it is robust to most of the attacks. As we will see in t he results section, unlike the crude LSB algorith m, the proposed method can extract the true watermark sequence with an acceptable accuracy after various at tacks or process ing. The extraction procedure would be easy. If we could have the place and location of the embedded bits as a watermark key then we can easily extract the embedded sequence. IV. R ESULTS AND C OM PARISON The proposed algorithm was si mulated in MATLAB and Lena is chosen for asset and Cameraman as the watermark image. Fig. 2 shows the simulation results for thr2=0 .75 and different thr1 values. As it can be seen from the fig. 2, thr1=0.8 is a good point of the trade-o ff between imperceptib ility and robustness and capacity, but, due to the application one can choose arbitrary thresholds. T able 1 sketches the response o f the extraction of the wa termark after proces sing and attacks. Error percentage is the Hamming distance between the extracted watermark and true water mark. As it is seen from the table, the proposed method is robust agains t the attacks w hile the original LSB approach is not. Fig. 4 demonstrates the detectors output to the 100 rando mly generated sequences . As we can see, the detector shows the biggest cor relation in the case of the true watermark sequence. In comparison to the original LSB algorithm, it is notew orthy that the proposed algorithm would require more co mputational complexity but we can achieve a better trade-off bet ween capacity and imperceptibility and also a better rob ustness against the attacks and unavoidable artifacts will be available. The str uctural similarity based method offers an ad aptive embedding procedure that will embed the watermark sequence until a threshold for imperceptibil ity is achieved. It is clear t hat less threshold values will r esults in a bigger capacity but l ess invis ibil ity. Choosi ng thr1 equal t o zero makes the new algorithm just very si milar to the original LS B method. Figure 1: Original LSB algor ithm; (a) Asset (b) Watermark Image (c) Watermarked I mage Figure 2: Watermarked Image resulted from the proposed algorithm; (a) Thr1=0 (b) Thr1=0.2 (c) Thr1 =0.4 (d) Thr1=0.6 (e) Thr1=0. 8 (f) Watermark Im age Table 1: Accuracy of the watermark extraction dur ing various attacks: extraction error percentage Threshol d 1=0 Threshold1=0.2 Threshold1=0.4 Threshold1=0.6 Threshold1=0.8 Original LSB Motion Blur 0.196 0.178 0.152 0.142 0.105 0.288 Jpeg Compression 0.143 0.124 0.108 0.089 0.054 0.225 Low Pass Filtering 0.154 0.142 0.122 0.114 0.073 0.239 Cropping 0.025 0.020 0.015 0.011 0.002 0.025 Gaussian Noise 0.230 0.213 0.178 0.152 0.116 0.268 Salt & Pepper Noise 0.213 0.184 0.155 0.123 0.094 0.296 Figure 3: Watermarked image of prop osed method after various attack type s: (a) motion blur (b) jpeg co mpression (c) low pass fi ltering (d) cropping (e ) Gaussian noise (f) salt & pepper noise Figure 4: Watermark detecto r for 100 randomly gene rated sequences V. C ONCL USION In this paper we first gave a historical review on digital watermarking and its trade-offs and then we state the necessity of the usage of HVS based quality metrics. A short survey on SSIM was reviewed. We proposed a n ew modified LSB watermarking technique based on structural similar ity. Simula tion r esults prove d that the propo sed method can find a better trade-off between capacity and imperceptibility than the original version. Rob ustness of the new algorithm was examined during the attacks. Results revealed this fact that the watermarked sequence can be extracted with an acceptable accuracy after all attacks. VI. R EFERENCES [1] F. Y. Du an and I. King, "A Sh ort Summary of Digital Water marking Techniques for Multimedia Data," in Proc. Proceedings of the 1999 Hong Kong International Computer Conference (HKICC'99) , Hong Kong, 1999. [2] Y. Yusof and O. O. Khalifa, “Imp erceptability and robustness analysis of DWT-based digital watermarking ,” IEEE International Conference on Computer and Communication Engineering, pp. 1325-1330, Kuala Lumpur, Malaysia, 2008. [3] Zh. Fan and Zh. Hongbin , “Capacity and reliability of di gital watermarking,” IEEE International Con ference on the Bussiness of Electronic Product Reliability and Liability, pp. 162-165, 2004. [4] X. Zhang, Y. Xu and F. Zhang, “Structural similarity based information hiding,” IITA International Conference on Control, Automation and system Engineering, pp. 88-91, 2009. [5] M. Steinbach, E. H auer and P. Wolf, “Efficient watermarking strategies,” IEEE Third Interna tional Conference on Automated Production of Cross Media Content for Multi-Channel Di stribution, pp. 65-71, 2009. [6] I. J. Cox, M. L. Miller, J. A. Bloom, J. Fridrich and T. Kalker, Digital Watermarking and Steganography , 2 nd ed. Massachuset s: Morgan Kaufmann, 2008. [7] M. Barni and F. Bartolini, W atermarking Systems Engineering , New York: Marcel Dekker, 2004. [8] E. Salahi, M. S. Moin and A. Salahi, “A Ne w Visualy Imperc eptible and robust image waterm arking scheme in Contourlet domain,” International Conference on Intelligent In formation Hiding and Multimedia Signal Processing, IIHMSP, pp. 457- 460, 2008. [9] K. Ramani, E. V . Prasad, S. Varadaraj an and A. Subrama nyam, “A robust watermarking s cheme for information hiding,” 16 th International Confere nce on Advanced Computing and Communications, ADCOM, 2008. [10] G. Xun, L. Hai-Ming, “Towards fast and robust watermarking scheme for H. 264 video,” 10 th IEEE International Sy mposium on Multimedia, ISM 2008, pp. 649-653, Jan. 2009. [11] I. J. Cox, J. K ilian, T. Leighton and T. Shamoon, “Secure spread spectrum watermarking for multi media,” IEEE Trans. on Image Processing, vol. 6(12), pp.1673-1678, 1997. [12] N. Nikolaidis and I. Pitas, “Copyr ight protection of image using robust digital signatures,” IEEE Internati onal Conference on Acoustics, Speech and Signal Processing, ICASSP 96, vol. 4, pp. 2168-2171, May, 1996. [13] M. D. Swanson, B. Zhu and A. H. Tewf ik, “Transparent robust image watermarking,” International C onference on Image Proces sing, vol. 3, pp. 211-214, Laussane, Switzerland, Sept. 16-19, 1996. [14] V. H. Manker, T . S. Das, S. Saha an d S. K. sa rkar, “Ro bust imag e watermarking under pixel wise masking f ramework,” First International Conference on Emerging Trends in Engineering and Technology, ICETET, J uly, 2008. [15] S. S. Be di and S. Verma, “A de sign of secure wa termarking schem e for images in spatial domain,” 2006 Annual IEEE Indian Conference, Sept. 2006. [16] H. H . Lar ijani and G. R. R ad, “A new spatial domain algorithm for gray scale images wa termarking,” Inter national Conferenc e on Computer and Comm unication Engineering, ICCCE, Kuala Lumpur, 2008. [17] V. Licks, F. Ourique, R. Jordan and F. Perez-Gonz alez, “The ef fect of the random jitter attack on the bit error rate performance o f spatial domain image watermarking,” International Conf erence on image porcessing, ICIP 2003. [18] G. P. Be tancourth, A. Haggag, M. Ghone im, T. Yahagi and L. Lianming, “Robust watermarking in DCT domain using dual detection,” IEEE Internationa l Symposium on Industerial Engineering, Montreal, 2008. [19] M. Jayalakshim, S. N. Merchant and U. B. Desai, “Signif icant pixel watermarking in contourlet domain,” IET International Confer ence on Visual Information Engineering, VIE06, India, 2006. [20] M. Barni, F. Barto lini, A. De Rosa and A. Piv a, “Capacity o f the watermarking channel: how many bits can be hidden within a digital image,” Security and Watermarking of Multimedia Contents, Procedeeings of SPIE, vol. 3654, pp. 437-448, 1999. [21] H. R. Sheikh and A. C. Bovic, "Image information and visual quality," IEEE Transactions on Image Processing , Vol. 15, No. 2, Feb. 2006. [22] Z. Wang and A. C. Bovik , “Mean squared Error: l ove it or leave it?,” IEEE Signal Processing Magazine, Jan. 2009. [23] Z. Wang, A. C. Bovik, H. R. Sheikh, and E. P. Simoncelli, “Image quality assessment: from error vi sibil ity to st ructural similarity ,” IEEE Trans. Image Processing , vol. 13, pp. 600–612, Apr. 2004. [24] A. Banitalebi, S. Na der-Esfahani and A. Nasiri Ava naki, “A pe rceptual based motion compensation technique for video coding,” submitted to 6 th Iranian Conferenc e on Machine Vision and Image Processing, MVIP, Iran, Oct. 2010. [25] A. Banitalebi, R. Parseh, S. Nader-Esfahani and F. La houti, “Exploring the distributed video coding in a quality assessment context,” submitted to 5 th International Sysposium on Telecommunications, IST, Kish Island, Ir an, Dec. 2010.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment