A new design principle of robust onion-like networks self-organized in growth
Today’s economy, production activity, and our life are sustained by social and technological network infrastructures, while new threats of network attacks by destructing loops have been found recently in network science. We inversely take into account the weakness, and propose a new design principle for incrementally growing robust networks. The networks are self-organized by enhancing interwoven long loops. In particular, we consider the range-limited approximation of linking by intermediations in a few hops, and show the strong robustness in the growth without degrading efficiency of paths. Moreover, we demonstrate that the tolerance of connectivity is reformable even from extremely vulnerable real networks according to our proposed growing process with some investment. These results may indicate a prospective direction to the future growth of our network infrastructures.
💡 Research Summary
The paper addresses a pressing vulnerability of modern networked infrastructures—namely, the susceptibility of scale‑free (SF) topologies to newly identified loop‑destruction attacks such as Collective Influence (CI) and Belief Propagation (BP) attacks. While SF networks provide short paths and efficient routing, their reliance on a few high‑degree hubs makes them fragile under targeted removal. Recent studies have shown that an “onion‑like” architecture—characterized by a densely connected core of older nodes surrounded by younger peripheral layers—exhibits superior robustness, especially when degree‑degree correlations (assortativity) are positive. However, existing incremental generation methods for onion‑like networks either require costly global rewiring or produce weak robustness during early growth stages.
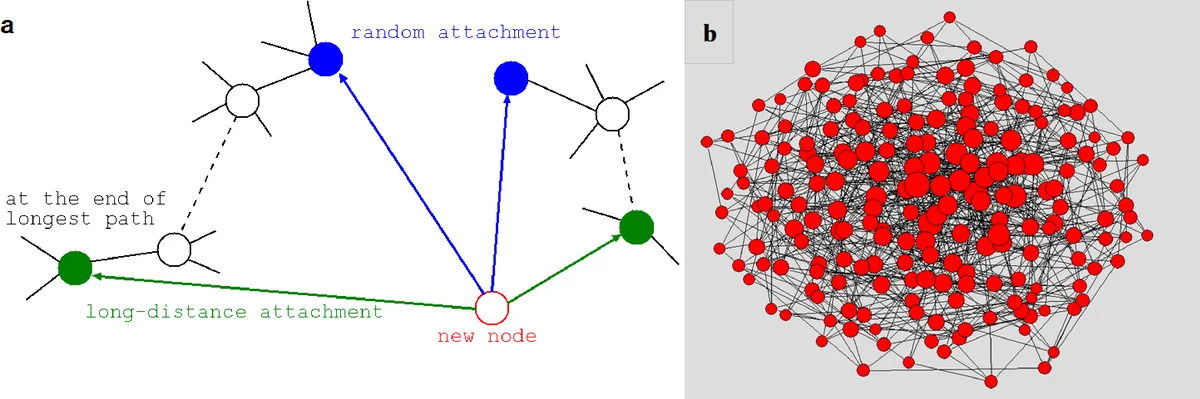
The authors propose a novel, locally implementable growth rule that deliberately creates long loops during network expansion. At each time step a new node is added with m links (m ≥ 4). The links are formed in pairs: one endpoint is chosen either uniformly at random (RLD‑A) or preferentially by degree (PLD‑A), and the second endpoint is the node farthest (in hop count) from the first. This “random‑long‑distance attachment” (RLD‑A) or “preferential‑long‑distance attachment” (PLD‑A) ensures that each new node participates in at least m/2 long loops, dramatically increasing the redundancy of alternative paths. To keep the scheme realistic, a range‑limited approximation (MED) replaces the farthest node with a node located within µ hops (µ = 2–4) from the first endpoint, mimicking low‑cost intermediate connections.
Analytically, the authors show that node degree grows logarithmically with network size (k_i(t) ∼ (1/β)·log t), leading to an exponential degree distribution p(k) ∝ e^{‑βk}. This contrasts with the power‑law tail of classic Barabási‑Albert (BA) networks and prevents the emergence of overly dominant hubs. The model also preserves the small‑world property: the average shortest‑path length scales as O(log N) despite many links being formed randomly.
Robustness is quantified by the area‑under‑curve metric R = (1/N)∑_{q=1/N}^{1} S(q), where S(q) is the fraction of nodes remaining in the giant component after removing a fraction q of nodes. The authors evaluate three attack strategies: High‑Degree Adaptive (HD A), CI with l = 3 layers, and BP attacks. Simulations reveal that networks grown with RLD‑A (m = 4) achieve R ≈ 0.31–0.35 against HD A and R ≈ 0.28–0.34 against BP, far exceeding the BA baseline (R ≈ 0.1). Moreover, the BP‑induced collapse is significantly delayed, indicating that the long‑loop structure provides alternative routes even when many hubs are eliminated. Assortativity r is also markedly higher (r ≈ 0.2) for RLD‑A and MED with µ = 3–4, confirming the emergence of an onion‑like topology. MED with µ = 2 shows weaker improvement, highlighting the importance of sufficient loop length.
To test practical relevance, the authors conduct virtual growth experiments starting from real‑world networks (Facebook, US airline, US power grid). By repeatedly applying the proposed attachment rules, these initially vulnerable, low‑assortativity networks evolve into robust onion‑like structures. With modest parameter choices (m = 4–12), robustness R climbs from ≈0.1 to >0.3 after the network size roughly doubles (N ≈ 10 000). The degree‑degree correlation also rises to r > 0.2, confirming that the method can retrofit existing infrastructures without wholesale rewiring.
In conclusion, the paper introduces a simple, scalable, and cost‑aware growth mechanism that simultaneously enhances robustness, maintains efficient routing, and induces positive degree correlations. By focusing on the creation of long loops through locally available information (random or preferential node selection plus limited‑range intermediaries), the approach offers a realistic pathway for evolving current scale‑free infrastructures into resilient onion‑like networks. Future work should explore detailed cost models, dynamic traffic loads, and real‑time implementation in operational networks, but the presented results already suggest a promising direction for safeguarding critical networked systems against sophisticated targeted attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment