On Security Research Towards Future Mobile Network Generations
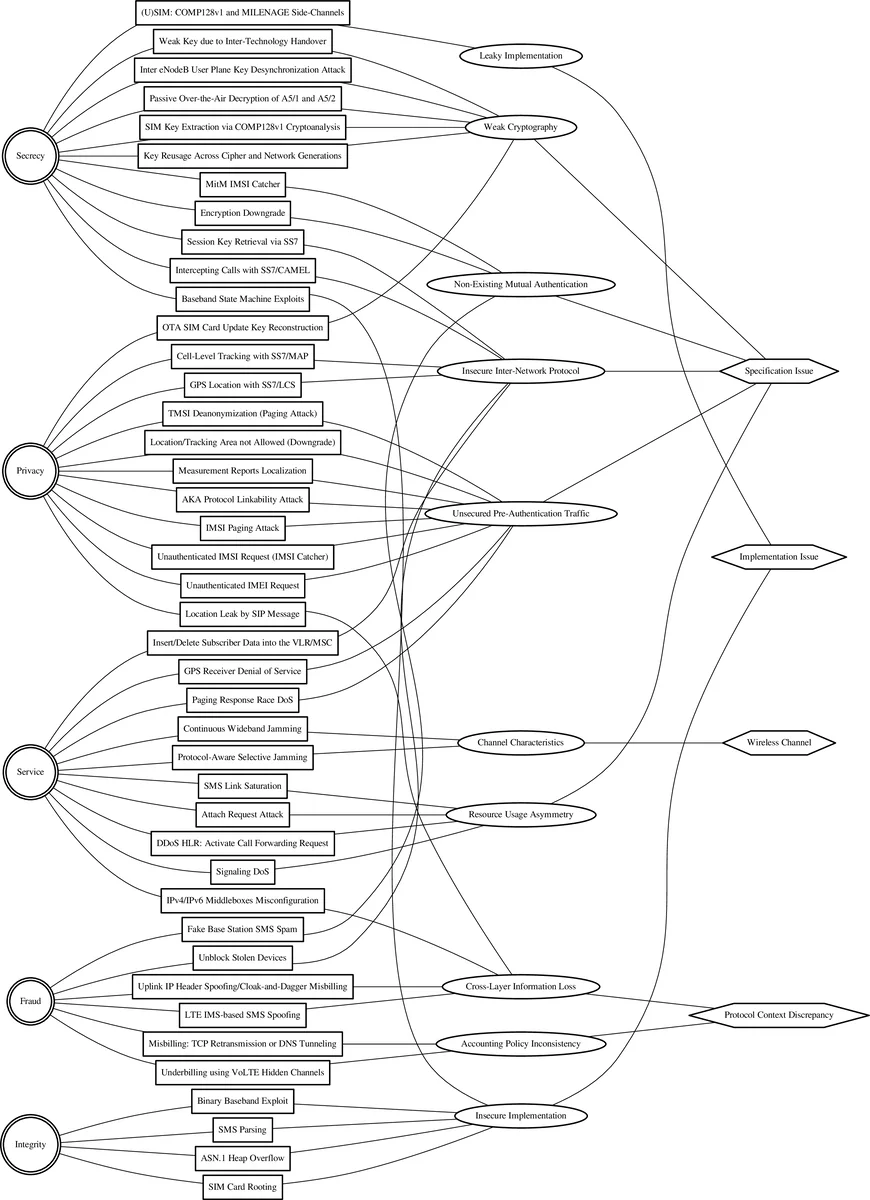
Over the last decades, numerous security and privacy issues in all three active mobile network generations have been revealed that threaten users as well as network providers. In view of the newest generation (5G) currently under development, we now have the unique opportunity to identify research directions for the next generation based on existing security and privacy issues as well as already proposed defenses. This paper aims to unify security knowledge on mobile phone networks into a comprehensive overview and to derive pressing open research questions. To achieve this systematically, we develop a methodology that categorizes known attacks by their aim, proposed defenses, underlying causes, and root causes. Further, we assess the impact and the efficacy of each attack and defense. We then apply this methodology to existing literature on attacks and defenses in all three network generations. By doing so, we identify ten causes and four root causes of attacks. Mapping the attacks to proposed defenses and suggestions for the 5G specification enables us to uncover open research questions and challenges for the development of next-generation mobile networks. The problems of unsecured pre-authentication traffic and jamming attacks exist across all three mobile generations. They should be addressed in the future, in particular, to wipe out the class of downgrade attacks and, thereby, strengthen the users’ privacy. Further advances are needed in the areas of inter-operator protocols as well as secure baseband implementations. Additionally, mitigations against denial-of-service attacks by smart protocol design represent an open research question.
💡 Research Summary
The paper “On Security Research Towards Future Mobile Network Generations” presents a systematic survey of security and privacy vulnerabilities that have been discovered across the three active mobile network generations—GSM (2G), UMTS (3G), and LTE (4G)—and uses this knowledge to outline research directions for upcoming generations, especially 5G and beyond. The authors first motivate the need for a comprehensive view by noting that mobile communications now serve billions of users and critical infrastructures, making security failures a societal risk. They observe that prior work has largely treated attacks and counter‑measures in isolation, preventing the identification of systemic problems that span multiple generations.
To address this gap, the authors develop a six‑step systematization methodology: (1) define security requirements (confidentiality, integrity, authentication, privacy, availability); (2) classify attacks by their aims (e.g., privacy breach, service disruption, revenue theft); (3) characterize attacks in terms of attacker capabilities, required resources, and required network state; (4) map existing defenses to attack vectors and assess their deployment status; (5) group related attacks under “causes” that reflect common design flaws; and (6) aggregate causes into four high‑level “root causes.” This structured approach enables a quantitative comparison of impact and efficacy across the literature.
Applying the methodology, the authors identify ten distinct causes of vulnerabilities and four overarching root causes: (i) insecure pre‑authentication traffic, (ii) susceptibility to radio‑level jamming, (iii) reliance on legacy inter‑operator signaling protocols (SS7, Diameter) with weak authentication, and (iv) insecure baseband firmware implementations. The first two causes are present in all three generations, while the latter two are amplified by the increasing complexity of inter‑operator roaming and the growing functionality of the baseband processor.
The paper then surveys the defenses that have been proposed for each cause. For pre‑authentication traffic, proposals include encrypting initial messages (e.g., 5G‑AKA), authenticating radio measurement requests, and employing mutual authentication even before session establishment. For jamming, suggestions range from adaptive power control and beamforming to collaborative detection among neighboring base stations. For SS7/Diameter, the authors discuss adding IPsec/TLS, mandatory authentication, and redesigning the protocols to follow a least‑privilege model. For baseband security, they review secure boot, signed firmware updates, and runtime integrity monitoring. In each case, the authors find that many defenses remain optional, are not uniformly deployed, or impose compatibility constraints that hinder adoption.
From this analysis, the authors formulate a set of open research questions that must be addressed to harden future mobile networks: 1) How can strong authentication and confidentiality be introduced in the pre‑authentication phase without breaking legacy device support? 2) What real‑time jamming detection and mitigation mechanisms can be integrated into radio resource management, especially for emerging mmWave and beamforming technologies? 3) How should inter‑operator signaling be redesigned to eliminate the inherent trust assumptions of SS7 and Diameter while preserving global roaming? 4) What standardized processes can guarantee the integrity of baseband firmware throughout its lifecycle, including OTA updates? 5) How can downgrade attacks be prevented through protocol design so that older, insecure features cannot be forced upon newer devices?
The authors conclude that addressing these root causes during the standardization of 5G—and later 6G—will require close collaboration between academia, industry, and standards bodies. They advocate for a “security‑by‑design” mindset that treats privacy and resilience as primary design goals rather than afterthoughts. By embedding robust pre‑authentication mechanisms, resilient radio designs, secure inter‑operator protocols, and trustworthy baseband implementations into the core specifications, future mobile networks can avoid the legacy vulnerabilities that have plagued earlier generations and provide a safer foundation for the increasingly critical services that depend on mobile connectivity.
Comments & Academic Discussion
Loading comments...
Leave a Comment