Experimental Demonstration of DDoS Mitigation over a Quantum Key Distribution (QKD) Network Using Software Defined Networking (SDN)
We experimentally demonstrate, for the first time, DDoS mitigation of QKD-based networks utilizing a software defined network application. Successful quantum-secured link allocation is achieved after a DDoS attack based on real-time monitoring of quantum parameters
💡 Research Summary
This paper presents the first experimental demonstration of Distributed Denial‑of‑Service (DDoS) mitigation in a Quantum Key Distribution (QKD) network by leveraging a Software‑Defined Networking (SDN) application. The authors recognize that while QKD provides information‑theoretic security against eavesdropping, it remains vulnerable to physical‑layer attacks that increase loss or noise on the quantum channel, causing key‑generation sessions to abort. To address this vulnerability, they integrate an SDN control plane with the optical transport layer, enabling real‑time monitoring of quantum performance metrics and automatic re‑routing of the quantum channel when degradation is detected.
The testbed consists of two QKD devices (ID Quantique Clavis 2) acting as Alice and Bob, connected through a Polatis optical switch that supports OpenFlow 1.0. Three distinct link scenarios are examined: (1) a standard single‑mode fiber (SSMF) link equipped with a 3 dB coupler and a variable attenuator to inject Raman noise, (2) a 1 km, 7‑core multicore fiber (MCF) where crosstalk is introduced in an adjacent core to emulate an intra‑data‑center attack, and (3) a 520 m SSMF link forming a two‑hop mesh with two intermediate nodes. All three paths are pre‑configured to have approximately 9 dB total loss, reflecting realistic deployment conditions.
A custom Quantum Parameters Monitor (QPM) application continuously retrieves the secret‑key rate (SKR) and quantum bit error rate (QBER) from the QKD units via a REST API. When either SKR drops to zero or QBER exceeds a predefined threshold (≈3 %), the QPM flags a link failure and sends an HTTP POST request to the OpenDaylight SDN controller. The controller then issues OpenFlow messages to the optical switch, simultaneously establishing the cross‑connections for an alternative pre‑computed path and tearing down the compromised one. This “all‑at‑once” re‑configuration minimizes switching latency.
Experimental results show a clear relationship between injected attack power and QKD performance. In the SSMF scenario, SKR remains between 700–800 b/s and QBER between 2.5–3 % up to an injected power of –68 dBm; beyond this point, SKR collapses and QBER rises sharply, halting key generation. In the MCF scenario, crosstalk begins to degrade performance at –17 dBm, with complete failure occurring around –9 dBm, illustrating that the number of active cores influences the tolerable power level.
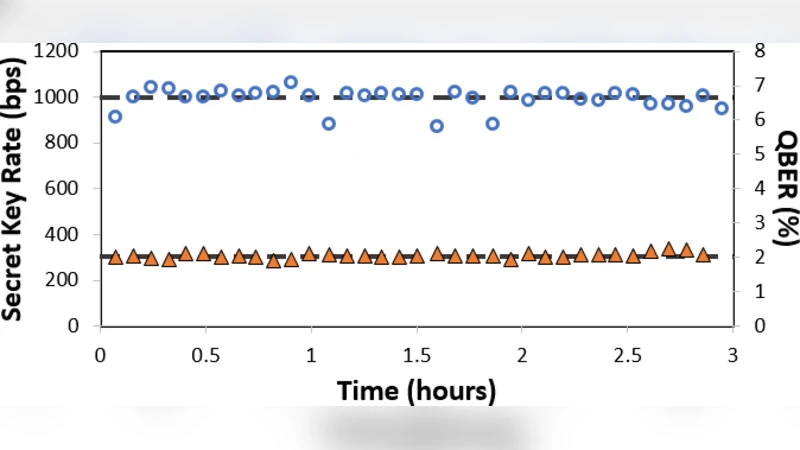
Crucially, the SDN‑driven path switch occurs within a few hundred milliseconds—orders of magnitude faster than the QKD initialization time (several seconds). After re‑routing, a three‑hour monitoring period records an average SKR of ≈950 b/s and QBER of ≈2 % on the new path, essentially identical to the baseline performance without any attack. This demonstrates that the SDN mitigation introduces negligible overhead and does not degrade the quantum channel’s security or throughput.
The authors acknowledge that their laboratory setup benefits from pre‑selected alternative routes with comparable loss and noise characteristics. In real‑world deployments, alternative paths may exhibit significantly higher attenuation or background noise, potentially leading to temporary performance penalties after a switch. Moreover, the detection thresholds are static; adaptive or machine‑learning‑based anomaly detection could reduce false positives and improve responsiveness in dynamic environments.
In conclusion, the work validates that integrating SDN with QKD provides a practical and effective defense against physical‑layer DDoS attacks. By continuously monitoring SKR and QBER and automatically re‑provisioning optical resources, the network maintains continuous key generation with minimal interruption. This approach paves the way for resilient quantum‑secure communications in future heterogeneous networks, where programmable control planes can orchestrate both classical and quantum resources to meet stringent security and availability requirements.
Comments & Academic Discussion
Loading comments...
Leave a Comment