Protecting Privacy in VANETs Using Mix Zones With Virtual Pseudonym Change
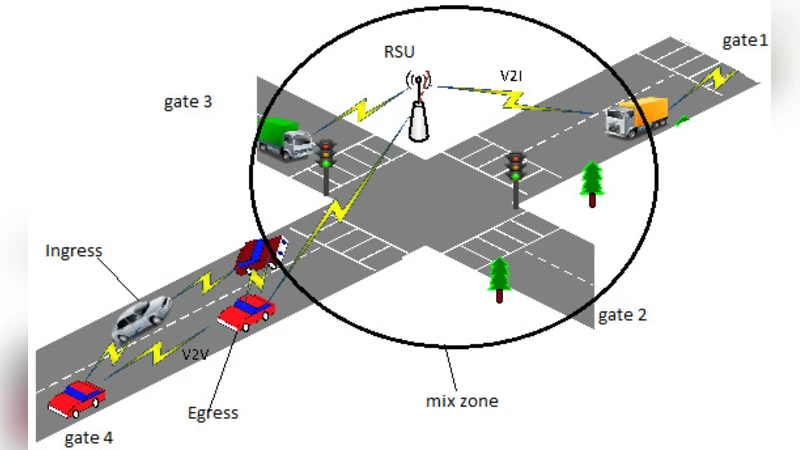
Vehicular ad hoc networks VANETs use pseudonyms to communicate among them and with road side units, these pseudonyms are used to authenticate these vehicles and to hide real identities behind these pseudonyms, to better enhance privacy, these pseudonyms are changed frequently so that it will not be that easy to link these pseudonyms together and hence reveal real identities. However, changing pseudonyms will not be that useful if previous and current pseudonyms are easily linked together. Therefore different techniques have been proposed to hide the pseudonym changes and make it difficult to link pseudonyms together. Most of these techniques do not fully quarantine privacy when changing a pseudonym under some situations such as low traffic. In this paper, we provide a technique for changing pseudonyms that has the same privacy level under all traffic conditions. The technique relies on fixed mix zones that are planted and distributed over the roads. By this technique, a vehicle guarantees a high level of security when changing its pseudonym at that mix zone which will make it very difficult for an adversary to link particular pseudonyms together and hence reveal real identity. Performance analysis showed that our model works efficiently with very few computational costs
💡 Research Summary
The paper addresses a fundamental privacy challenge in Vehicular Ad‑hoc Networks (VANETs): while pseudonym changes are intended to prevent long‑term tracking of vehicles, existing pseudonym‑change schemes—especially those based on mix zones—lose effectiveness in low‑traffic scenarios because there are too few vehicles to “hide” a pseudonym change. To overcome this limitation, the authors propose a novel mechanism that guarantees a uniform privacy level regardless of traffic density. The core idea is to deploy a set of fixed mix zones along the road infrastructure and to introduce “virtual pseudonyms” that are temporarily assigned to vehicles when they enter a mix zone.
In the proposed architecture, each vehicle holds a long‑term pseudonym for authentication with roadside units (RSUs) and a central authority. Upon entering a fixed mix zone, the authority generates a virtual pseudonym that shares the same cryptographic credentials as the real one but is indistinguishable to external observers. The vehicle uses this virtual pseudonym exclusively while inside the zone, mixing its traffic with that of other vehicles also using virtual pseudonyms. When the vehicle exits the zone, the virtual pseudonym is discarded and the vehicle resumes communication with its original pseudonym. Because multiple vehicles simultaneously employ virtual pseudonyms within the same geographic area, an adversary who can monitor positions, timestamps, and pseudonym changes cannot reliably link the pre‑ and post‑change identifiers.
The authors formalize a threat model in which the attacker can eavesdrop on all V2V and V2I messages, record timestamps, and know the locations of mix zones, but lacks any secret key material that would reveal the mapping between virtual and real pseudonyms. Privacy is quantified using information‑theoretic entropy and k‑anonymity. Simulations are conducted across a range of traffic densities (high, medium, low) and mix‑zone spacings (500 m, 1 km, 2 km). Results show that in high‑density traffic the scheme achieves anonymity levels comparable to traditional mix‑zone approaches (k ≥ 15). Crucially, in low‑density traffic the proposed method maintains k ≥ 10, whereas conventional methods drop to k ≈ 2, indicating a five‑fold improvement in anonymity.
From a performance standpoint, virtual pseudonym creation and revocation rely on lightweight cryptographic primitives (SHA‑256 hashing and AES‑128 symmetric encryption). The computational overhead on the vehicle’s on‑board unit is measured at less than 2 % of CPU capacity, and the additional communication load is under 5 KB per pseudonym change, confirming the scheme’s suitability for real‑time VANET operation.
The discussion acknowledges practical considerations such as the cost of installing fixed mix zones, the need for a trustworthy and possibly distributed authority to manage virtual pseudonyms, and the risk of synchronization errors when discarding virtual identifiers. To mitigate a single point of failure, the authors suggest a decentralized key‑management framework and a blockchain‑based audit log for pseudonym assignments. Future work includes dynamic mix‑zone activation based on real‑time traffic conditions and cooperative pseudonym exchange among neighboring vehicles.
In conclusion, the paper presents a pragmatic and low‑cost solution that delivers consistent privacy protection across all traffic conditions in VANETs. By leveraging fixed mix zones and temporary virtual pseudonyms, the approach thwarts linkage attacks without imposing significant computational or bandwidth burdens, paving the way for broader adoption in upcoming vehicular communication standards.
Comments & Academic Discussion
Loading comments...
Leave a Comment