Resource Allocation for Secure MISO-NOMA Cognitive Radios Relying on SWIPT
Cognitive radio (CR) and non-orthogonal multiple access (NOMA) are two promising technologies in the next generation wireless communication systems. The security of a NOMA CR network (CRN) is important but lacks of study. In this paper, a multiple-input single-output NOMA CRN relying on simultaneous wireless information and power transfer is studied. In order to improve the security of both the primary and secondary network, an artificial noise-aided cooperative jamming scheme is proposed. Different from the most existing works, a power minimization problem is formulated under a practical non-linear energy harvesting model. A suboptimal scheme is proposed to solve this problem based on semidefinite relaxation and successive convex approximation. Simulation results show that the proposed cooperative jamming scheme is efficient to achieve secure communication and NOMA outperforms the conventional orthogonal multiple access in terms of the power consumption.
💡 Research Summary
This paper investigates a downlink multiple‑input single‑output (MISO) cognitive radio (CR) network that simultaneously employs non‑orthogonal multiple access (NOMA) and simultaneous wireless information and power transfer (SWIPT). The authors recognize that such a system is vulnerable to eavesdropping because the same radio‑frequency (RF) signals carry both confidential information and harvested energy. To protect both the primary network (PN) and the secondary network (SN), they propose an artificial‑noise‑aided cooperative jamming scheme: the secondary base station (CBS) generates artificial noise (AN) that is transmitted together with the primary base station’s (PBS) signal, thereby confusing the energy‑harvesting eavesdroppers (EHRs) that belong to the primary network. In exchange, the primary network grants the secondary network access to its licensed spectrum, allowing the CBS to serve secondary users (SUs) and EHRs via NOMA while also delivering power through SWIPT.
A realistic non‑linear energy‑harvesting (EH) model is adopted, based on the logistic‑type circuit model widely used in recent SWIPT literature. This model captures the saturation behavior of practical rectifiers, making the harvested‑power constraints inherently non‑convex. The design objective is to minimize the total transmit power (sum of the PBS and CBS beamforming matrices and the AN covariance matrices) subject to: (i) minimum secrecy‑rate requirements for each primary user (PU) and each SU, (ii) a maximum tolerable interference level at each PU, (iii) minimum harvested‑power requirements for all EHRs, and (iv) rank‑one constraints on the beamforming matrices (to ensure they correspond to actual beamforming vectors).
Because of the logarithmic secrecy‑rate expressions, the non‑linear EH equations, and the rank constraints, the resulting optimization problem (denoted P1) is highly non‑convex. The authors tackle it with a two‑stage sub‑optimal approach:
-
Semidefinite Relaxation (SDR) – The rank‑one constraints are relaxed, allowing the beamforming matrices to be positive semidefinite. After solving the relaxed problem, a Gaussian randomization step can be used to extract feasible rank‑one solutions if necessary.
-
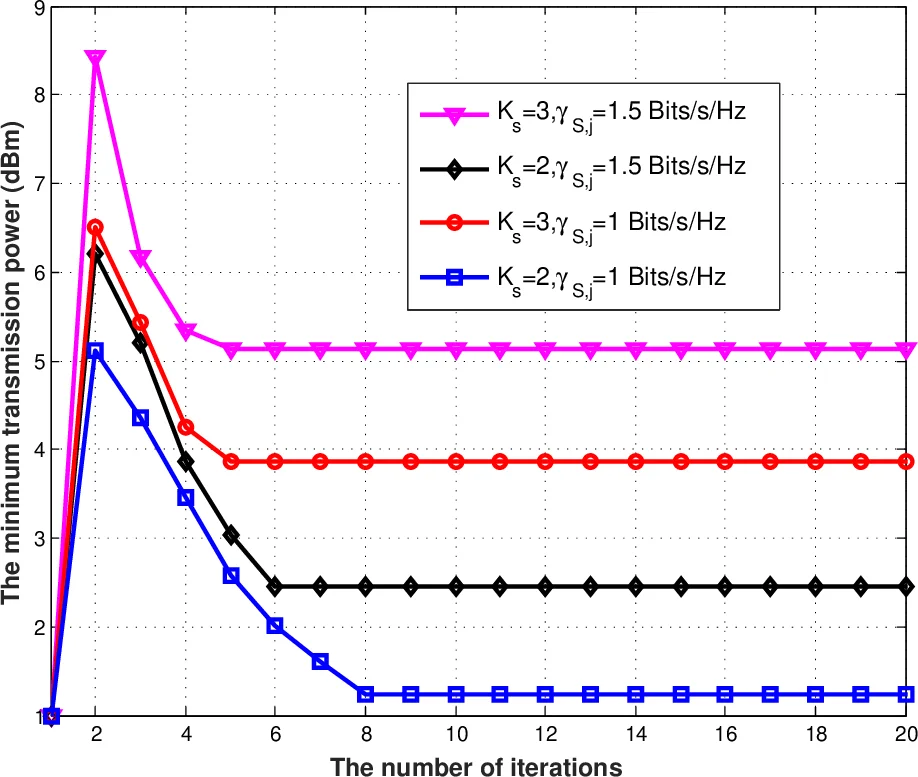
Successive Convex Approximation (SCA) – The non‑convex logarithmic and exponential terms in the secrecy‑rate and EH constraints are linearized around current operating points using first‑order Taylor expansions. Auxiliary variables (e.g., τ, α, β, λ, μ, ρ, δ) are introduced to rewrite the constraints in an exponential form, which can then be approximated by convex inequalities. At each iteration, a convex semidefinite program (SDP) is solved; the solution updates the auxiliary variables, and the process repeats until convergence.
The algorithm converges to a stationary point of the original problem, providing a practical power‑efficient design. Numerical simulations are conducted with multiple PU clusters, several SUs, and EHRs in both networks. Key findings include:
- Security Enhancement: The cooperative AN generated by the CBS significantly reduces the eavesdropping capability of primary‑network EHRs, allowing the secrecy‑rate constraints to be met with lower transmit power.
- Power Savings of NOMA: Compared with an orthogonal multiple‑access (OMA) baseline, the NOMA‑based secondary network achieves the same secrecy‑rate targets while consuming roughly 20–30 % less total power, confirming NOMA’s superior spectral‑efficiency translates into energy savings in this secure SWIPT setting.
- Impact of Non‑Linear EH Model: Incorporating the realistic EH model prevents over‑allocation of power to the EHRs in the saturation region, leading to a more balanced power distribution and further reductions in total transmit power relative to a linear EH assumption.
The paper’s contributions are threefold: (1) it introduces the first physical‑layer security framework for a CR‑NOMA‑SWIPT system, leveraging cooperative jamming to protect both primary and secondary communications; (2) it integrates a practical non‑linear EH model into the power‑minimization problem and provides a tractable SDR‑SCA solution; (3) it empirically demonstrates that NOMA outperforms OMA in terms of power efficiency while satisfying stringent secrecy and energy‑harvesting requirements.
Overall, the work offers valuable design insights for future 5G‑Beyond networks where spectrum sharing, massive connectivity, energy harvesting, and security must be jointly addressed. Future extensions could consider imperfect channel state information, multi‑cell coordination, and low‑complexity real‑time implementations.
Comments & Academic Discussion
Loading comments...
Leave a Comment