MAGNETO: Covert Channel between Air-Gapped Systems and Nearby Smartphones via CPU-Generated Magnetic Fields
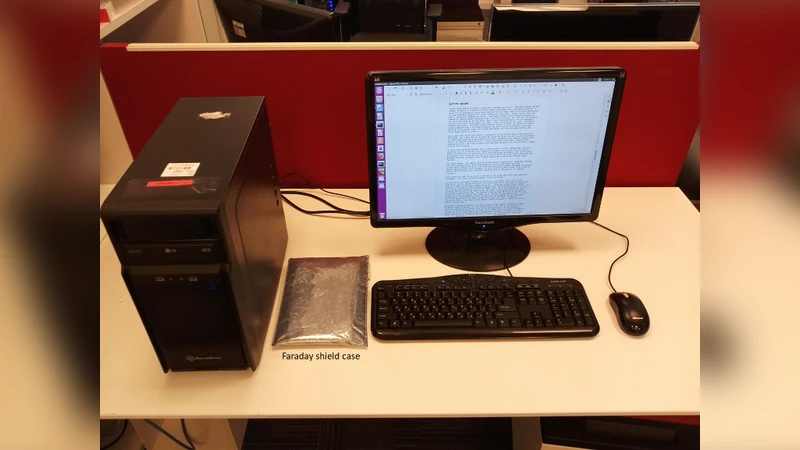
In this paper, we show that attackers can leak data from isolated, air-gapped computers to nearby smartphones via covert magnetic signals. The proposed covert channel works even if a smartphone is kept inside a Faraday shielding case, which aims to block any type of inbound and outbound wireless communication (Wi-Fi, cellular, Bluetooth, etc.). The channel also works if the smartphone is set in airplane mode in order to block any communication with the device. We implement a malware that controls the magnetic fields emanating from the computer by regulating workloads on the CPU cores. Sensitive data such as encryption keys, passwords, or keylogging data is encoded and transmitted over the magnetic signals. A smartphone located near the computer receives the covert signals with its magnetic sensor. We present technical background, and discuss signal generation, data encoding, and signal reception. We show that the proposed covert channel works from a user-level process, without requiring special privileges, and can successfully operate from within an isolated virtual machine (VM).
💡 Research Summary
The paper introduces “MAGNETO,” a covert channel that enables data exfiltration from air‑gapped computers to nearby smartphones by exploiting low‑frequency magnetic fields generated through controlled CPU workload. Unlike previously studied electromagnetic, acoustic, optical, or thermal side‑channels, this method leverages the fact that varying the power consumption of CPU cores induces measurable magnetic field fluctuations in the power delivery circuitry. By deliberately toggling CPU load at specific frequencies, the malware creates a carrier wave that can be modulated using either On‑Off Keying (OOK) or Binary Frequency‑Shift Keying (B‑FSK).
The attack model consists of three stages: (1) infection of an air‑gapped network via removable media, supply‑chain compromise, or insider threat; (2) infection of the target’s smartphone with a malicious app that reads the built‑in magnetometer; and (3) data transmission from the compromised computer to the phone. The smartphone’s magnetometer, typically a three‑axis Hall‑effect sensor with a resolution of tens of micro‑tesla and a sampling rate of 50‑150 Hz, can detect the magnetic field variations even when the device is in airplane mode or enclosed in a Faraday‑shielded case, because the sensor is not considered a communication interface and operates at low frequencies that can penetrate such shielding.
Implementation details show that the transmitter runs as a user‑level process, requiring no special privileges, and can even operate inside a virtual machine. Worker threads are pinned to individual CPU cores; each thread alternates between a busy‑wait loop (full load) and a sleep period to generate the desired frequency. For OOK, the presence of the carrier represents a binary ‘1’; its absence represents ‘0’. For B‑FSK, two distinct carrier frequencies encode ‘0’ and ‘1’. The authors provide pseudocode (Algorithm 1) describing the core‑binding and timing logic.
Experimental evaluation was performed on desktop PCs and laptops, using several Android smartphones as receivers. The channel achieved bit rates ranging from 0.2 bit/s to 5 bit/s, with a maximum reliable distance of about 12 cm for desktops and up to 12 cm for laptops (the latter limited by lower power consumption). The magnetic field strength follows an inverse‑cube law (∝ 1/r³), which explains the short range. Nevertheless, the authors demonstrate that low‑frequency magnetic emissions can bypass Faraday cages, confirming the feasibility of the attack in highly controlled environments.
Compared to prior work such as ODINI (which also uses CPU‑generated magnetic fields but requires a dedicated magnetic “bug” near the target) and Myhayun’s hard‑disk‑based magnetic channel, MAGNETO’s novelty lies in using only the CPU, making it applicable to virtually any modern computer without additional hardware modifications. The trade‑off is lower bandwidth and limited range, but the ease of deployment and lack of privilege requirements make it a realistic threat.
The paper discusses countermeasures, including: (a) monitoring abnormal CPU load patterns that could indicate malicious modulation; (b) restricting or disabling magnetometer access on smartphones in high‑security zones; (c) augmenting Faraday shielding with high‑permeability materials to attenuate low‑frequency magnetic fields; and (d) employing anomaly‑detection systems that correlate magnetic sensor readings with expected environmental noise. The authors also suggest that future research could explore higher‑frequency modulation, multi‑core synchronization for increased signal strength, and error‑correction schemes to improve reliability.
In conclusion, MAGNETO demonstrates that even when traditional wireless interfaces are disabled, the ubiquitous CPU and smartphone magnetometer can be co‑opted to create a covert magnetic communication path, challenging the assumption that physical air‑gap isolation alone guarantees data confidentiality. The work broadens the taxonomy of air‑gap covert channels and underscores the need for holistic security measures that consider unconventional side‑channels.
Comments & Academic Discussion
Loading comments...
Leave a Comment