Real-Time Rejection and Mitigation of Time Synchronization Attacks on the Global Positioning System
This paper introduces the Time Synchronization Attack Rejection and Mitigation (TSARM) technique for Time Synchronization Attacks (TSAs) over the Global Positioning System (GPS). The technique estimates the clock bias and drift of the GPS receiver al…
Authors: Ali Khalajmehrabadi, Nikolaos Gatsis, David Akopian
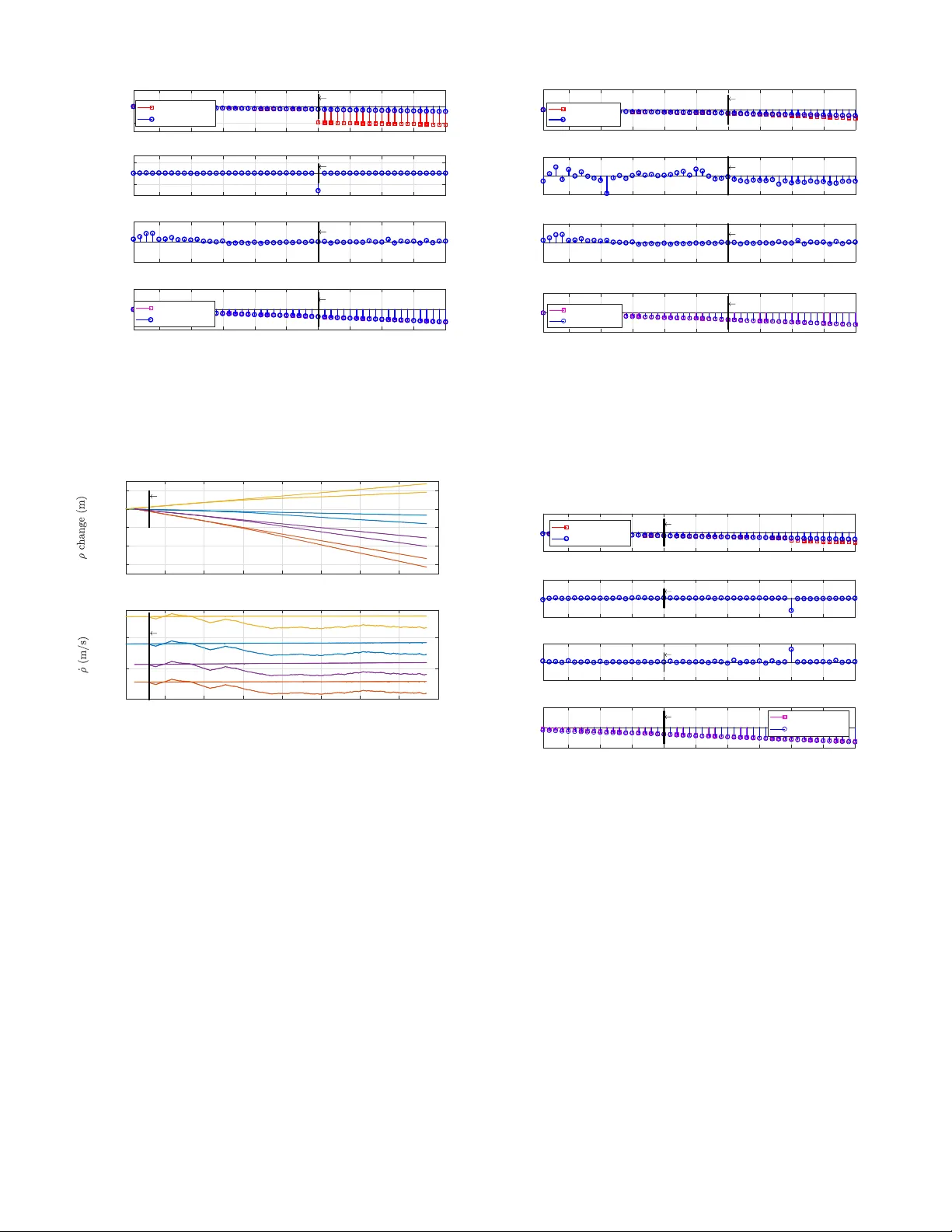
Real-Time Rejection and Mitigation of Time Synchronization Attac ks on the Global P ositioning System Ali Khalajmehrabadi, Student Member , IEEE , Nik olaos Gatsis, Member , IEEE , David Ak opian, Senior Member , IEEE , and Ahmad F . T aha, Member , IEEE Abstract —This paper introduces the Time Sync hroniza- tion Attac k Rejection and Mitigation (TSARM) tec hnique for Time Synchr onization Attacks (TSAs) over the Global P o- sitioning System (GPS). The technique estimates the cloc k bias and drift of the GPS receiver along with the possible attack contrar y to previous approac hes. Having estimated the time instants of the attack, the cloc k bias and drift of the receiver are corrected. The pr oposed technique is com- putationally efficient and can be easily implemented in real time, in a fashion complementary to standard algorithms for position, velocity , and time estimation in off-the-shelf receivers. The perf ormance of this technique is ev aluated on a set of collected data from a real GPS receiver . Our method render s e xcellent time recovery consistent with the application requirements. The numerical results demon- strate that the TSARM technique outperforms competing approac hes in the literature . Index T erms —Global P ositioning System, Time Synchro- nization Attack, Spoofing Detection I . I N T R O D U C T I O N I NFRASTR UCTURES such as road tolling systems, terres- trial digital video broadcasting, cell phone and air traffic control to wers, real-time industrial control systems, and Phasor Measurement Units (PMUs) [1] hea vily rely on synchronized precise timing for consistent and accurate network communi- cations to maintain records and ensure their traceability . The Global Positioning System (GPS) provides time reference of microsecond precision for these systems [2]–[5]. The GPS-based time-synchronization systems use the ci vil- ian GPS channels, which are open to the public [6], [7]. The unencrypted nature of these signals makes them vulnerable to unintentional interference and intentional attacks. Thus, unauthorized manipulation of GPS signals leads to disruption of correct readings of GPS-based time references, and thus, is called Time Synchronization Attack (TSA). T o address the impact of malicious attacks, for instance on PMU data, the Electric Power Research Institute published a technical report that recognizes the vulnerability of PMUs to GPS spoofing under its scenario W AMP A C.12: GPS T ime Signal Compr o- mise [8]. These attacks introduce erroneous time stamps which are ev entually equiv alent to inducing wrong phase angle in Authors are with the Electrical and Computer Engineer ing Depar t- ment, University of T exas at San Antonio, San Antonio, TX, 78249, USA (e-mails: { ali.khalajmehrabadi, nikolaos.gatsis, david.ak opian, ah- mad.taha } @utsa.edu). the PMU measurements [9], [10]. The impact of TSAs on generator trip control, transmission line fault detection, voltage stability monitoring, disturbing e vent locationing, and power system state estimation has been studied and e valuated both experimentally [11] and through simulations [12]–[14]. Intentional unauthorized manipulation of GPS signals is commonly referred to as GPS spoofing , and can be categorized based on the spoofer mechanism as follows: • J amming (blocking) : The spoofer sends high po wer signals to jam the normal operation of the receiver by disrupting the normal operation of the victim recei ver , often referred to as loosing lock . Then, the victim receiver may lock onto the spoofer signal after jamming [9], [15]–[17]. • Data level spoofing : The spoofer manipulates the na vigation data such as orbital parameters (ephemerides) that are used to compute satellite locations [13], [15], [18]. • Signal level spoofing : The spoofer synthesizes GPS-like signals that carry the same navigation data as concurrently broadcasted by the satellites [11]. • Recor d-and-replay attack : The spoofer records the authentic GPS signals and retransmits them with selected delays at higher po wer [9], [19]. T ypically the spoofer starts from low power transmission and increases its power to force the recei ver to lock onto the spoofed (delayed) signal. The spoofer may change the transmitting signal properties such that the victim receiv er miscalculates its estimates. Common off-the-shelf GPS receiv ers lack proper mecha- nisms to detect these attacks. A group of studies hav e been directed towards ev aluating the requirements for successful attacks, theoretically [16] and experimentally [11], [29]–[31]. For instance, the work in [30] has designed a real spoofer as a Software Defined Radio (SDR) that records authentic GPS signals and retransmits fake signals. It pro vides the option of manipulating v arious signal properties for spoofing. A. Spoofing Detection T echniques in the Literature The first lev el of countermeasures to reduce the ef fect of malicious attacks on GPS receiv ers typically relies on the Receiv er Autonomous Integrity Monitoring (RAIM) [4]. Of f- the-shelf GPS recei vers typically apply RAIM consistency checks to detect the anomalies exploiting measurement redun- dancies. For example, RAIM may e valuate the v ariance of GPS solution residuals and consequently generate an alarm if it exceeds a predetermined threshold. Similar v ariance authentication techniques have been proposed in [22], [32] T ABLE I G P S S P O O FI N G D E T E C T I O N T E C H N I Q U E S : D E T E C T I O N D O M A I N A N D I M P L E M E N T ATI O N A S P E C T S Method Attack Detection Domain Attack Implementation Aspects Relevant EKF GPS Na vigation domain Not Estimated Benchmark for most common GPS recei vers Y es CUSUM [20] GPS baseband signal domain Not Estimated Applies hypothesis testing on packets of received signal No Ref. [21] GPS baseband & power grid domains Not Estimated Combines the statistics of carrier-to-noise ratio difference between two GPS antennas No SPREE [22] GPS baseband signal domain Not Estimated Applies auxiliary peak tracking in the correlators of receiv er No Ref. [23], [24] GPS baseband signal domain Not Estimated Applies a position-information-aided vector tracking loop No Ref. [25], [26] GPS na vigation domain Not Estimated Needs collaboration among multiple GPS recei vers No Ref. [27] GPS na vigation domain Not Estimated Applies an anti-spoofing particle filter Y es Ref. [28] GPS na vigation domain Not Estimated Applies hypothesis testing on a GPS clock signature Y es TSARM GPS na vigation domain Estimated Applies a real-time optimization technique - based on hypothesis testing on the Kalman filter innov ations; howe ver , they are vulnerable to smarter attacks that pass RAIM checks or the innov ation hypothesis testing. A plethora of countermeasures hav e been designed to make the recei vers robust against more sophisticated attacks [9], [15], [17]–[19], [21]–[25], [27], [28], [33]–[35]. V ector tracking exploits the signals from all satellites jointly and feedbacks the predicted position, velocity , and time (PVT) to the internal lock loops [23], [24], [33]. If an attack occurs, the lock loops become unstable which is an indication of attack. Cooperativ e GPS receiv ers can perfrom authentication check by analyzing the integrity of measurements through peer -to- peer communications [24], [25], [34], [35]. Also, a quick sanity check for stationary time synchronization de vices is to monitor the estimated location. As the true location can be known a priori , any large shift that exceeds the maximum allow able position estimation error can be an indication of attack [28]. The recei ver carrier-to-noise receiv er can be used as an indicator of spoofing attack [17]. In [21], the difference between the carrier-to-noise ratios of two GPS antennas has been proposed as a metric of PMU trustworthiness. In addi- tion, some approaches compare the recei ver’ s clock behavior against its statistics in normal operation [19], [28], [33]. B. Existing Literature Gaps As discussed abov e, prior research studies addressed a breadth of problems related to GPS spoofing. Ho wever , there are certain gaps that should still be addressed: 1) Most of the works do not pro vide analytical models for different types of spoofing attacks. The possible attacking procedure models are crucial for designing the countermeasures against the spoofing attacks. 2) Although some countermeasures might be ef fectiv e for a certain type of attack, a comprehensive countermeasure dev elopment is still lacking for defending the GPS receiv er . This is practically needed as the recei ver cannot predict the type of attack. 3) The main effort in the literature is in detection of possible spoofing attacks. Howe ver , ev en with the spoofing detection, the GPS receiv er cannot resume its normal operation, especially in PMU applications where the network’ s normal operation cannot be interrupted. So, the spoofing countermeasures should not only detect the attacks but also mitigate their effects so that the network can resume its normal operation. 4) There is a need for simpler solutions which can be integrated with current systems. C . Contrib utions of This Work This work addresses the previously mentioned gaps for stationary time synchronization systems. T o the best of our knowledge, this is the first work that provides the follo wing major contributions: 1) The new method is not a mere spoofing detector; it also estimates the spoofing attack. 2) The spoofed signatures, i.e., clock bias and drift, are corrected using the estimated attack. 3) The ne w method detects the smartest attacks that maintain the consistency in the measurement set. A descriptive comparison between our solution and represen- tativ e works in the literature is provided in T able I. A revie w of the spoofing detection domain shows that most of the prior art operates at the baseband signal processing domain, which necessitates manipulation of the receiver circuitry . Hence, the approach in the present paper is compared only to those works whose detection methodology lies in navigation domain. The proposed TSA detection and mitigation approach in this paper consists of two parts. First, a dynamical model is introduced which analytically models the attacks in the receiv er’ s clock bias and drift. Through a proposed nov el T ime Synchronization Attack Rejection and Mitigation (TSARM) approach, the clock bias and drift are estimated along with the attack. Secondly , the estimated clock bias and drift are modified based on the estimated attacks so that the receiver would be able to continue its normal operation with corrected timing for the application. The proposed method detects and mitigates the effects of the smartest and most consistent reported attacks in which the position of the victim recei ver is not altered and the attacks on the pseudoranges are consistent with the attacks on pseudorange rates. Different from outlier detection approaches in [36], [37], the proposed method detects the anomalous behavior of the spoofer ev en if the measurement integrity is preserved. The spoofing mitigation scheme has the follo wing desirable at- tributes: 1) It solves a small quadratic program, which makes it applicable to commonly used devices. 2) It can be easily in- tegrated into existing systems without changing the receiv er’ s circuitry or necessitating mulitple GPS receiv ers as opposed to [21]–[24], [33], [34]. 3) It can run in parallel with current systems and provide an alert if spoofing has occurred. 4) W ithout halting the normal operation of the system, corrected timing estimates can be computed. The proposed anti-spoofing technique has been ev aluated using a commercial GPS recei ver with open-source measure- ments access [38]. These measurements have been perturbed with spoofing attacks specific to PMU operation. Applying the proposed anti-spoofing technique sho ws that the clock bias of the receiver can be corrected within the maximum allowable error in the PMU IEEE C37.118 standard [39]. P aper Or ganization: A brief description of the GPS is described in Section II. Then, we provide the models for possible spoofing attacks in Section III. Section IV elaborates on the proposed solution to detect and modify the ef fect of these attacks. Our solution is numerically ev aluated in Section V follo wed by the conclusions in Section VI. I I . G P S P V T E S T I M A T I O N In this section, a brief o verview of the GPS Position, V elocity , and T ime (PVT) estimation is presented. The main idea of localization and timing through GPS is trilateration, which relies on the kno wn location of satellites as well as distance measurements between satellites and the GPS receiver . In particular , the GPS signal from satellite n contains a set of navig ation data, comprising the ephemeris and the almanac (typically updated ev ery 2 hours and one week, respectiv ely), together with the signal’ s time of transmission ( t n ). This data is used to compute the satellite’ s position p n = [ x n ( t n ) , y n ( t n ) , z n ( t n )] T in Earth Centered Earth Fixed (ECEF) coordinates, through a function known to the GPS receiv er . Let t R denote the time that the signal arriv es at the GPS receiv er . The distance between the user (GPS receiv er) and satellite n can be found by multiplying the signal propa- gation time t R − t n by the speed of light c . This quantity is called pseudorang e : ρ n = c ( t R − t n ) , n = 1 , . . . , N , where N is the number of visible satellites. The pseudorange is not the exact distance because the receiver and satellite clocks are both biased with respect to the absolute GPS time. Let the receiver and satellite clock biases be denoted by b u and b n , respectiv ely . Therefore, the time of reception t R and t n are related to their absolute values in GPS time as follows: t R = t GPS R + b u ; t n = t GPS n + b n , n = 1 , . . . , N . The b n ’ s are computed from the receiv ed navig ation data and are considered known. Ho wever , the bias b u must be estimated and should be subtracted from the measured t R to yield the receiv er absolute GPS time t GPS R , which can be used as a time reference used for synchronization. Synchronization systems time stamp their readings based on the Coordinated Univ ersal T ime (UTC) which has a known of fset with the GPS time as t UTC R = t GPS R − ∆ t UTC , where ∆ t UTC is a vailable online. 1 Let p u = [ x u , y u , z u ] T be the coordinates of the GPS receiv er , and d n its true range to satellite n . This distance is expressed via the locations p u , p n and the times t GPS R , t GPS n as d n = k p n − p u k 2 = c ( t GPS R − t GPS n ) . Therefore, the measurement equation becomes ρ n = k p n − p u k 2 + c ( b u − b n ) + ρ n (1) where n = 1 , . . . , N , and ρ n represents the noise. The unknowns in (1) are x u , y u , z u , b u and therefore measurements from at least four satellites are needed to estimate them. 1 https://confluence.qps.nl/qinsy/en/utc- to- gps- time- correction- \ 32245263.html (accessed Jan. 16, 2018). Furthermore, the nominal carrier frequency ( f c = 1575 . 42 MHz ) of the transmitted signals from the satellite experiences a Doppler shift at the receiv er due to the relati ve motion between the receiv er and the satellite. Hence, in addition to pseudoranges, pseudorange rates are estimated from the Doppler shift and are related to the relative satellite velocity v n and the user velocity v u via ˙ ρ n = ( v n − v u ) T p n − p u k p n − p u k + ˙ b u + ˙ ρ n (2) where ˙ b u is the clock drift. In most cases, there are more than four visible satellites, resulting in an overdetermined system of equations in (1) and (2). T ypical GPS recei vers use nonlinear W eighted Least Squares (WLS) to solve (1) and (2) and provide an estimate of the location, velocity , clock bias, and clock drift of the recei ver , often referred to as PVT solution. T o additionally e xploit the consecutiv e nature of the estimates, a dynamical model is used. The con ventional dynamical model for stationary receiv ers is a random walk model [3, Chap. 9] x u [ l + 1] y u [ l + 1] z u [ l + 1] b u [ l + 1] ˙ b u [ l + 1] = I 3 × 3 0 3 × 2 0 2 × 3 1 ∆ t 0 1 x u [ l ] y u [ l ] z u [ l ] b u [ l ] ˙ b u [ l ] + w [ l ] (3) where l is the time index, ∆ t is the time resolution (typically 1 sec), and w is the noise. The dynamical system (3) and measurement equations (1) and (2) are the basis for estimating the user PVT using the Extended Kalman Filter (EKF). Previous works have sho wn that simple attacks are able to mislead the solutions of WLS or EKF . Stationary GPS- based time synchronization systems are currently equipped with the position-hold mode option which can potentially detect an attack if the GPS position differs from a known receiv er location by a maximum allowed error [40]. This can be used as the first indication of attack. But, more advanced spoofers, such as the ones de veloped in [30], ha ve the ability to manipulate the clock bias and drift estimates of the stationary receiv er without altering its position and velocity (the latter should be zero). So, even with EKF on the con ventional dynamical models, perturbations on the pseudoranges in (1) and pseudorange rates in (2) can be designed so that they directly result in clock bias and drift perturbations without altering the position and v elocity of the receiver . I I I . M O D E L I N G T I M E S Y N C H R O N I Z A T I O N A T TAC K S This section puts forth a general attack model that encom- passes the attack types discussed in the literature. This model is instrumental for designing the anti-spoofing technique dis- cussed in the next section. While TSAs hav e different physical mechanisms, they man- ifest themselves as attacks on pseudorange and pseudorange rates. These attacks can be modeled as direct perturbations on (1) and (2) as ρ s [ l ] = ρ [ l ] + s ρ [ l ] ˙ ρ s [ l ] = ˙ ρ [ l ] + s ˙ ρ [ l ] (4) 0 50 100 150 200 250 300 (a) -15000 -10000 -5000 0 5000 0 50 100 150 200 250 300 (b) Time (s) -8000 -6000 -4000 -2000 0 Fig. 1. T ype I attack on (a) pseudorange and (b) pseudorange rate versus local observation time . where s ρ and s ˙ ρ are the spoofing perturbations on pseudor- anges and pseudorange rates, respectively; and ρ s and ˙ ρ s are respectiv ely the spoofed pseudorange and pseudorange rates. A typical spoofer follows practical considerations to intro- duce feasible attacks. These considerations can be formulated as follows: 1) An attack is meaningful if it infringes the maximum allowed error defined in the system specification. For instance in PMU applications, the attack should exceed the maximum allowable error tolerance specified by the IEEE C37.118 Standard, which is 1% T otal V ariation Error (TVE), equiv alently expressed as 0 . 573 ◦ phase angle error , 26 . 65 µ s clock bias error, or 7989 m of distance-equiv alent bias error [39]. On the other hand, CDMA cellular networks require timing accuracy of 10 µ s. 2 2) Due to the peculiarities of the GPS recei vers, the internal feedback loops may loose lock on the spoofed signal if the spoofer’ s signal properties change rapidly [11], [29]. 3) The designed spoofers have the ability to manipulate the clock drift (by manipulating the Doppler frequency) and clock bias (by manipulating the code delay) [30]. These perturbations can be applied separately , howe ver , the smartest attacks maintain the consistency of the spoofer’ s transmitted signal. This means that the pertubations on pseudoranges, s ρ , are the integration of perturbations ov er pseudorange rates, s ˙ ρ , in (4). Here, distinguishing between two attack procedures is ad- vantageous as the literature includes very few research reports on the technical intricacies of the spoofer constraints: • T ype I: The spoofer manipulates the authentic signal so that the bias abruptly changes in a very short time [13], [15], [28]. Fig. 1 illustrates this attack. The attack on the pseudoranges suddenly appears at t = 30 s and perturbs the pseudoranges by 8000 m . The equi valent attack on pseudorange rates is a Dirac delta function. • T ype II: The spoofer gradually manipulates the authentic signals and changes the clock bias through time [11], [17], [19], [28], [29], [41]. This attack can be modeled by s ρ [ l ] = s ρ [ l − 1] + s ˙ ρ [ l ]∆ t s ˙ ρ [ l ] = s ˙ ρ [ l − 1] + ˙ s ˙ ρ [ l ]∆ t (5) 2 http://www .endruntechnologies.com/cdma (accessed Sept. 11, 2017). 0 50 100 150 200 250 300 350 400 (a) -50000 0 50000 0 50 100 150 200 250 300 350 400 (b) Time(s) -500 0 500 Fig. 2. T ype II attack on (a) pseudorange and (b) pseudorange rate versus local observation time . where s ˙ ρ and ˙ s ˙ ρ are respectively called distance equiv alent velocity and distance equiv alent acceleration of the attack. T o maintain the victim recei ver lock on the spoofer’ s signals, the attack should not exceed a certain distance equiv alent velocity . T wo such limiting numbers are reported in the liter- ature, namely , | s ˙ ρ | ≤ 400 m / s in [29] and | s ˙ ρ | ≤ 1000 m / s in [11]. The acceleration to reach the maximum spoofing velocity is reported to be | ˙ s ˙ ρ | ≤ 5 m / s 2 . The spoofer accel- eration ˙ s ˙ ρ can be random, which makes T ype II attack quite general. The distance equiv alent velocity can be con verted to the equi valent bias change rate (in s / s ) through dividing the velocity by the speed of light. Fig. 2 illustrates this attack. The attack on the pseudoranges starts at t = 30 s and perturbs the pseudoranges gradually with distance equi valent velocity not exceeding 400 m / s and maximum distance equiv alent random acceleration satisfying | ˙ s ˙ ρ | ≤ 5 m / s 2 . The introduced attack models are quite general and can mathematically capture most attacks on the victim receiver’ s measurements (pseudoranges and pseudorange rates) discussed in Section I. In another words, T ype I and T ype II attacks can be the result of data le vel spoofing, signal le vel spoofing, record-and-replay attack, or a combination of the aformen- tioned attacks. The main difference between T ype I and T ype II attacks is the spoofing speed. The speed of the attack depends on the capabilities of the spoofer with respect to manipulating various features of the GPS signals. Indeed, attacks of different speeds hav e been reported in the literature provided earlier in the present section. This work does not deal with jamming, which disrupts the navigation functionality completely whereas spoofing misleads it. In the next section, a dynamical model for the clock bias and drift is introduced which incorporates these attacks. Based on this dynamical model, an optimization problem to estimate these attacks along with the clock bias and drift is proposed. I V . T S A - A WA R E D Y N A M I C A L M O D E L , T S A R E J E C T I O N A N D M I T I G A T I O N This section introduces a dynamical model to accommodate the spoofing attack and a method to estimate the attack. Afterwards, a procedure for approximately nullifing the ef fects of the attack on the clock bias and drift is introduced. A. Nov el TSA-aware Dynamical Model Modeling of the attack on pseudoranges and pseudorange rates is motiv ated by the attack types discussed in the previous section. These attacks do not alter the position or velocity , but only the clock bias and clock drift. Our model does not follow the con ventional dynamical model for stationary receiv ers which allows the position of the receiver to follow a random walk model (3). Instead, the known position and velocity of the victim recei ver are exploited jointly . The state vector contains the clock bias and clock drift, and the attacks are explicitly modeled on these components, leading to the following dynamical model: cb u [ l + 1] c ˙ b u [ l + 1] | {z } x l +1 = 1 ∆ t 0 1 | {z } F cb u [ l ] c ˙ b u [ l ] | {z } x l + cs b [ l ] cs ˙ b [ l ] | {z } s l + cw b [ l ] cw ˙ b [ l ] | {z } w l (6) where s b and s ˙ b are the attacks on clock bias and clock drift and w b and w ˙ b are colored Gaussian noise samples with cov ariance function defined in [3, Chap. 9]. Here, both sides are multiplied with c , which is a typically adopted conv ention. The state noise covariance matrix, Q l , is particular to the crystal oscillator of the de vice. Similarly , define ρ [ l ] = [ ρ 1 [ l ] , . . . , ρ N [ l ]] T and ˙ ρ [ l ] = [ ˙ ρ 1 [ l ] , . . . , ˙ ρ N [ l ]] T . The measurement equation can be as ρ [ l ] ˙ ρ [ l ] | {z } y l = 1 N × 1 0 N × 1 0 N × 1 1 N × 1 | {z } H cb u [ l ] c ˙ b u [ l ] | {z } x l + k p 1 [ l ] − p u [ l ] k . . . k p N [ l ] − p u [ l ] k ( v 1 [ l ] − v u [ l ]) T . p 1 [ l ] − p u [ l ] k p 1 [ l ] − p u [ l ] k . . . ( v N [ l ] − v u [ l ]) T . p N [ l ] − p u [ l ] k p N [ l ] − p u [ l ] k − cb 1 [ l ] . . . cb N [ l ] c ˙ b 1 [ l ] . . . c ˙ b N [ l ] | {z } c l + ρ 1 [ l ] . . . ρ N [ l ] ˙ ρ 1 [ l ] . . . ˙ ρ N [ l ] | {z } l . (7) Explicit modeling of p u and v u in c l indicates that the dynamical model benefits from using the stationary victim receiv er’ s known position and velocity (the latter is zero). The measurement noise covariance matrix, R l , is obtained through the measurements in the recei ver . Detailed explanation of how to obtain the state and measurement cov ariance matrices, Q l and R l , is provided in Section V. It should be noted that the state covariance Q l only depends on the victim receiver’ s clock behavior and does not change under spoofing. Howe ver , the measurement cov ariance matrix, R l , e xperiences contrac- tion. The reason is that to ensure that the victim receiver maintains lock to the fake signals, the spoofer typically applies a power advantage over the real incoming GPS signals at the victim recei ver’ s front end [17]. Comparing (5), (6) and (7), TSAs which do not alter the position and velocity transfer the attack on pseudoranges and pseudorange rates directly to clock bias and clock drift. Thus, it holds that s ˙ ρ = cs b and ˙ s ˙ ρ = cs ˙ b . B. Attack Detection Let l = k , . . . , k + L − 1 define the time index within the observation window of length L , where k is the running time index. The solution to the dynamical model of (6) and (7) is obtained through stacking L measurements and forming the following optimization problem: ( ˆ x , ˆ s ) = argmin x , s ( 1 2 k + L − 1 X l = k k y l − Hx l − c l k 2 R − 1 l + 1 2 k + L − 1 X l = k k x l +1 − Fx l − s l k 2 Q − 1 l + k + L − 1 X l = k λ k Ds l k 1 ) (8) where k x k 2 M = x T Mx , ˆ x = [ ˆ x 1 , . . . , ˆ x L ] T are the estimated states, ˆ s = [ ˆ s 1 , . . . , ˆ s L ] T are the estimated attacks, λ is a regularization coefficient, and D is an L × 2 L total v ariation matrix which forms the v ariation of the signal over time as [42] D = − 1 0 1 0 . . . 0 0 − 1 0 1 . . . 0 . . . . . . . . . . . . . . . . . . 0 . . . 0 − 1 0 1 . (9) The first term is the weighted residuals in the measurement equation, and the second term is the weighted residuals of the state equation. The last re gularization term promotes sparsity ov er the total variation of the estimated attack. In (8), the clock bias and clock drift are estimated jointly with the attack. Here, the model of the two introduced attacks should be considered. In T ype I attack, a step attack is applied over the pseudoranges. The solution to the clock bias equiv alently experiences a step at the attack time. The term k Ds l k 1 = P k + L − 1 l = k +1 | s b [ l ] − s b [ l − 1] | + | s ˙ b [ l ] − s ˙ b [ l − 1] | indicates a rise as it tracks the significant differences between two subsequent time instants. If the magnitude of the estimated attack in two adjacent times does not change significantly , the total variation of the attack is close to zero. Otherwise, in the presence of an attack, the total variation of the attack includes a spike at the attack time. In T ype II attack, the total variation of the attack does not show significant changes as the attack magnitude is small at the beginning and the sparsity is not evident initially . Although we explained why it is meaningful to expect only few nonzero entries in the total variation of the attacks in general, this is not a necessary condition for capturing the attacks during initial small total variation magnitudes. This means that explicit modeling of the attacks in (6) and estimation through (8) does not require the attacks to exhibit sparsity over the total v aria- tion. Furthermore, when the bias and bias drift are corrected using the estimated attack (we will provide one mechanism in Section IV -C), sparsity over the total v ariation appears for subsequent time instants. In these time instants, the attack appears to be more prominent, and in effect, the low dynamic behavior of the attack is magnified, a fact that facilitates the attack detection and will also be verified numerically . This effect is a direct consequence of (8) and the correction scheme discussed in the next section. The optimization problem of (8) boils do wn to solving a simple quadratic program. Specifically , the epigraph trick in con vex optimization can be used to transform the ` 1 -norm into linear constraints [43]. The observation window L slides for a lag time T lag < L , which can be set to T lag = 1 for real- time operation. The next section details the sliding window operation of the algorithm, and elaborates on how to use the solution of (8) in order to provide corrected bias and drift. C . State Correction In observation windo w of length L , the estimated attack ˆ s is used to compensate the impact of the attack on the clock bias, clock drift, and measurements. Revisiting the attack model in (6), the bias at time l + 1 depends on the clock bias and clock drift at time l . This depen- dence successi vely traces back to the initial time. Therefore, any attack on the bias that occurred in the past is accumulated through time. A similar observ ation is v alid for the clock drift. The clock bias at time l is therefore contaminated by the cumulativ e ef fect of the attack on both the clock bias and clock drift in the pre vious times. The correction method takes into account the previously mentioned effect and modifies the bias and drift by subtracting the cumulati ve outcome of the clock bias and drift attacks as follows: c ˜ b u [ l ] ˜ ρ [ l ] = c ˆ b u [ l ] ρ [ l ] − l X l 0 = k ˆ s b [ l 0 ] − l − 1 X l 0 = k ˆ s ˙ b [ l 0 ]∆ t ! 1 c ˜ ˙ b u [ l ] ˜ ˙ ρ [ l ] ! = c ˆ ˙ b u [ l ] ˙ ρ [ l ] ! − l X l 0 = k ˆ s ˙ b [ l 0 ] ! 1 (10) where ˜ b u and ˜ ˙ b u are respectiv ely the corrected clock bias and clock drift, ˜ ρ and ˜ ˙ ρ are respectiv ely the corrected pseudorange and pseudorange rates, and 1 is an all one vector of length N + 1 . In (10), l = 1 , . . . , L for the first observ ation windo w ( k = 1 ) and k + L − T lag ≤ l ≤ k + L − 1 for the observation windows afterwards. This ensures that the measurements and states are not doubly corrected. The corrected measurements are used for solving (8) for the ne xt observation window . The overall attack detection and modification procedure is illustrated in Algorithm 1. After the recei ver collects L measurements, problem (8) is solv ed. Based on the estimated attack, the clock bias and clock drift are cleaned using (10). This process is repeated for a sliding window and only the clock bias and drift of the time instants that have not been cleaned previously are corrected. In another words, there is no duplication of modification o ver the states. The proposed technique boils do wn to solving a simple quadratic program with only few variables and can thus be performed in real time. For example, ef ficient implementations of quadratic programming solvers are readily av ailable in low- lev el programming languages. The implementation of this technique in GPS receiv ers and electronic de vices is thus straightforward and does not necessitate creating new libraries. V . N U M E R I C A L R E S U L T S W e first describe the data collection device and then assess three representative detection schemes in the literature that fail to detect the TSA attacks. These attacks mislead the clock bias and clock drift, while maintaining correct location and velocity estimates. The performance of our detection and modification technique o ver these attacks is illustrated afterwards. Algorithm 1 : TSA Rejection and Mitigation (TSARM) 1: Set k = 1 2: while T rue do 3: Batch y l ∀ l = k , . . . , k + L − 1 4: Construct H , c l , F ∀ l = k , . . . , k + L − 1 5: Compute Q l and R l (details pro vided in Section V) 6: Estimate ˆ x , ˆ s via (8) 7: Assign c ˆ b u [ l ] = ˆ x [ m ] , m = 2 l − 1 and c ˆ ˙ b u [ l ] = ˆ x [ m ] , m = 2 l ∀ l = k , . . . , k + L − 1 8: Assign ˆ s b [ l ] = ˆ s [ m ] , m = 2 l − 1 and ˆ s ˙ b [ l ] = ˆ s [ m ] , m = 2 l ∀ l = k , . . . , k + L − 1 9: Modify ˆ b u [ l ] , ˆ ˙ b u [ l ] , ρ [ l ] and ˙ ρ [ l ] via (10) ∀ l = 1 , . . . , L for the first windo w and k + L − T lag ≤ l ≤ k + L − 1 for the windows afterwards 10: Set y l = ˜ ρ [ l ] ˜ ˙ ρ [ l ] ∀ l = k , . . . , k + L − 1 11: Output t UTC R [ l ] = t R [ l ] − ˜ b u [ l ] − ∆ t U T C ∀ l = k , . . . , k + L − 1 to the user for time stamping 12: Slide the observation window by setting k = k + T lag 13: end while A. GPS Data Collection Device A set of real GPS signals has been recorded with a Google Nexus 9 T ablet at the Uni versity of T exas at San Antonio on June, 1, 2017. 3 The ground truth of the position is obtained through taking the median of the WLS position estimates for a stationary device. This device has been recently equipped with a GPS chipset that provides raw GPS measurements. An android application, called GNSS Logger , has been released along with the post-processing MA TLAB codes by the Google Android location team [38]. Of interest here are the two classes of the Android.location package. The GnssClock 4 provides the GPS receiver clock properties and the GnssMeasurement 5 provides the measurements from the GPS signals both with sub-nanosecond accuracies. T o obtain the pseudorange measurements, the transmission time is subtracted from the time of reception. The function getReceivedSvTimeNanos() provides the transmission time of the signal which is with respect to the current GPS week (Saturday-Sunday midnight). The signal reception time is av ailable using the function getTimeNanos() . T o translate the receiver’ s time to the GPS time (and GPS time of week), the package provides the difference between the de vice clock time and GPS time through the function getFullBiasNanos() . The receiv er clock’ s cov ariance matrix, Q l , is dependent on the statistics of the device clock oscillator . The follo wing 3 Our data is availab le at: https://github .com/Alikhalaj2006/UTSA GPS DA T A.git 4 https://dev eloper .android.com/reference/android/location/ GnssClock.html (accessed F eb. 20, 2017). 5 https://dev eloper .android.com/reference/android/location/ GnssMeasurement.html (accessed Feb . 20, 2017). 0 50 100 150 200 250 300 350 400 Time(s) -2 -1 0 1 Bias (m) 10 5 EKF Normal EKF Spoofed Anti-Spoofing PF 0 50 100 150 200 250 300 350 400 Time(s) -66 -64 -62 -60 Drift (m/s) EKF Normal EKF Spoofed Fig. 3. The effect of T ype II attack on the EKF and the anti-spoofing par ticle filter [27] on (a) clock bias and (b) clock drift. The attack started at t = 30 s . Panel (b) does not include the drift. 0 50 100 150 200 (a) -500 0 500 No attack 0 50 100 150 200 (b) -1000 0 1000 Inconsistent attack Attack started 0 50 100 150 200 (c) Time (s) -500 0 500 Consistent attack Attack started Fig. 4. P erformance of hypothesis testing based on statistic (V -B) [28] under T ype I attack for different false alar m probabilities: (a) No attack, (b) inconsistent attack, (c) consistent attac k. model is typically adopted: Q l = c 2 σ 2 b ∆ t + c 2 σ 2 ˙ b ∆ t 3 3 c 2 σ 2 ˙ b ∆ t 2 2 c 2 σ 2 ˙ b ∆ t 2 2 c 2 σ 2 ˙ b ∆ t ! (11) where σ 2 b = h 0 2 and σ 2 ˙ b = 2 π 2 h − 2 ; and we select h 0 = 8 × 10 − 19 and h − 2 = 2 × 10 − 20 [44, Chap. 9]. For calculating the measurement cov ariance matrix, R l , the uncertainty of the pseuodrange and pseudorange rates are used. These uncertain- ties are av ailable from the device together with the respectiv e measurements. 5 In the experiments, we set λ = 5 × 10 − 10 , because the distance magnitudes are in tens of thousands of meters. The estimated clock bias and drift through EKF in normal operation is considered as the ground truth for the subsequent analysis. In what follows, reported times are local. B. F ailure of Pr ior Work in Detecting Consistent Attac ks This section demonstrates that three relev ant approaches from T able I may fail to detect consistent attacks, that is, attacks where s ρ is the integral of s ˙ ρ in (4). The performance of the EKF and the anti-spoofing particle filter of [27] subject to a T ype II attack is reported first. The perturbations ov er GPS measurements are the same as in Fig. 2 and are used as input to the EKF and the particle filter . The attack starts at t = 30 s . Fig. 3 depicts the ef fect of attack on the clock bias and drift. The EKF on the dynamical model in (6) and (7) blindly follows the attack after a short settling time. The anti-spoofing particle filter only estimates the clock bias and assumes the clock drift is known from WLS. Similarly to the EKF , the particle filter is not able to detect the consistent spoofing attack. The maximum dif ference between the receiver estimated position obtained from the EKF on (3) under T ype II attack and under normal operation is x diff = 67 m , y diff = 112 m , and z diff = 71 m . The position estimate has thus not been considerably altered by the attack. The third approach to be ev aluated has been proposed in [28] and monitors the statistics of the receiv er clock, as a typical spoofing detection technique [33]. Consid- ering that off-the-shelf GPS receiv ers compute the bias at re gular ∆ t interv als, a particular approach is to es- timate the GPS time after k time epochs, and con- firm that the time elapsed is indeed k ∆ t [28]. T o this end, the following statistic can be formulated: D ( k ) = h t GP S R ( k ) − t GP S R (1) − ( k − 1)∆ t − P k k 0 =1 ˆ ˙ b [ k 0 ]∆ t i c. The test statistic D is normally distributed with mean zero when there is no attack and may hav e nonzero mean depending on the attack, as will be demonstrated shortly . Its v ariance needs to be estimated from a few samples under normal operation. The detection procedure relies on statistical hypothesis testing. For this, a false alarm probability , P F A , is defined. Each P F A corresponds to a threshold γ to which D ( k ) is compared against [45, Chap. 6]. If |D ( k ) | ≥ γ , the receiv er is considered to be under attack. The result of this method is shown in Fig. 4 for different false alarm probabilities. Fig. 4 (a) depicts D ( k ) when the system is not under attack. The time signature lies between the thresholds only for low false alarm probabilities. The system can detect the attack in case of an inconsistent T ype I attack, in which s ρ , is not the integration of perturbations over pseudorange rates, s ˙ ρ , and only pseudoranges are attacked. Fig. 4 (b) shows that the attack is detected right away . Howe ver , for smart attacks, where the spoofer maintains the consistency between the pseudorange and pseudorange rates, Fig. 4 (c) illustrates that the signature D ( k ) fails to detect the attack. This example shows that the statistical beha vior of the clock can remain untouched under smart spoofing attacks. In addition, ev en if an attack is detected, the previous methods cannot pro vide an estimate of the attack. C . Spoofing Detection on T ype I Attac k Fig. 5 shows the result of solving (8) using the GPS measurements perturbed by the T ype I attack of Fig. 1. The spoofer has the capability to attack the signal in a v ery short time so that the clock bias experiences a jump at t = 30 s . The estimated total variation of bias attack renders a spike right at the attack time. The modification procedure of (10) corrects the clock bias using the estimated attack. 1 5 10 15 20 25 30 35 40 45 50 (a) -10000 0 10000 Bias (m) Attack started Bias Spoofed Bias Normal 1 5 10 15 20 25 30 35 40 45 50 (b) -10000 -5000 0 5000 Bias TV (m) Attack started 1 5 10 15 20 25 30 35 40 45 50 (c) -1 0 1 Drift TV (m/s) Attack started 1 5 10 15 20 25 30 35 40 45 50 (d) Time (s) -5000 0 5000 MBias (m) Attack started Bias Modified Bias Normal Fig. 5. The result of attack detection and modification ov er a T ype I attack that star ted at t = 30 s . F rom top to bottom: (a) Nor mal cloc k bias (blue) and spoof ed bias (red), (b) total variation of the estimated bias attack ˆ s b , (c) total variation of the estimated drift attack ˆ s ˙ b , and (d) tr ue bias (blue) and modified bias (magenta). 0 50 100 150 200 250 300 350 400 (a) -300000 -200000 -100000 0 100000 2 Normal 2 Attacked 5 Normal 5 Attacked 6 Normal 6 Attacked 12 Normal 12 Attacked Attack started 0 50 100 150 200 250 300 350 400 (b) Time (s) -1000 -500 0 450 2 Normal 2 Attacked 5 Normal 5 Attacked 6 Normal 6 Attacked 12 Normal 12 Attacked Attack started Fig. 6. Compar ison of (a) normal pseudorange change ( ρ ( k ) − ρ (1) ) and spoofed pseudoranges change ( ρ s ( k ) − ρ s (1) ), and (b) normal pseudorange rates ( ˙ ρ ) and spoofed pseudorange rates ( ˙ ρ s ) under T ype II attack f or some of the visible satellites. The attac k star ted at t = 30 s . D . Spoofing Detection on T ype II Attack The impact of T ype II attack on the pseudoranges and pseuodrange rates is shown in Fig. 6. Specifically , Fig. 6 (a) illustrates the normal and spoofed pseudorange changes with respect to their initial value at t = 0 s for some of the visible satellites in the recei ver’ s view . Fig. 6 (b) depicts the corresponding pseudorange rates. The tag at the end of each line indicates the satellite ID and whether the pseudorange (or pseudorange rate) corresponds to normal operation or operation under attack. The spoofed pseudoranges di verge quadratically starting at t = 30 s following the T ype II attack. For the T ype II attack, Algorithm 1 is implemented for an sliding windo w with L = 50 s with T lag = 10 s . Fig. 7 shows the attack ed clock bias starting at t = 30 s . Since the attack magnitude is small at initial times of the spoofing, neither the estimated attack ˆ s b nor the total variation do not 1 5 10 15 20 25 30 35 40 45 50 (a) -10000 0 10000 Bias (m) Attack started Bias Spoofed Bias Normal 1 5 10 15 20 25 30 35 40 45 50 (b) -200 0 200 Bias TV(m) Attack started 1 5 10 15 20 25 30 35 40 45 50 (c) -1 0 1 Drift TV (m/s) Attack started 1 5 10 15 20 25 30 35 40 45 50 (d) Time (s) -5000 0 5000 MBias (m) Attack started Bias Modified Bias Normal Fig. 7. The result of attack detection and modification ov er T ype II attack for t = 1 s through t = 50 s . The attack star ted at t = 30 s . F rom top to bottom: (a) Normal clock bias (blue) and spoofed bias (red), (b) estimated bias attack ˆ s b , (c) total variation of the estimated bias attack, and (d) true bias (blue) and modified bias (magenta). 11 15 20 25 30 35 40 45 50 55 60 (a) -10000 0 10000 Bias (m) Attack started Bias Spoofed Bias Normal 11 15 20 25 30 35 40 45 50 55 60 (b) -2000 0 2000 Bias TV(m) Attack started 11 15 20 25 30 35 40 45 50 55 60 (c) -2 0 2 Drift TV (m/s) Attack started 11 15 20 25 30 35 40 45 50 55 60 (d) Time (s) -5000 0 5000 MBias (m) Attack started Bias Modified Bias Normal Fig. 8. The result of attack detection and modification ov er T ype II attack f or t = 11 s through t = 60 s . F rom top to bottom: (a) Normal clock bias (blue) and spoof ed bias (red), (b) estimated bias attack ˆ s b , (c) total variation of the estimated bias attack, and (d) true bias (blue) and modified bias (magenta). show significant values. The procedure of sliding window is to correct the current clock bias and clock drift for all the times that ha ve not been modified previously . Hence, at the first run the estimates of the whole windo w are modified. Fig. 8 shows the estimated attack and its corresponding total variation after one T lag . As is obvious from the figure, the modification of the previous clock biases transforms the lo w dynamic behavior of the spoofer to a large jump at t = 50 s which facilitates the detection of attack through the total variation component in (8). The clock bias and drift hav e been modified for the pre vious time instants and need to be cleaned only for t = 50 s − 60 s . 10 20 30 40 50 60 70 L 200 400 600 800 1000 1200 RMSE (m) Fig. 9. The RMSE of TSARM for v ar ious values of L and T lag . E. Analysis of the Results Let K be the total length of the observation time (in this experiment, K = 386 ). The root mean square error (RMSE) is introduced: RMSE = c K q P K − 1 k =0 ( ˜ b u [ k ] − ˇ b u [ k ]) 2 , which shows the average error between the clock bias that is output from the spoofing detection technique, ˜ b u , and the estimated clock bias from EKF under normal operation, ˇ b u , which is considered as the ground truth. Comparing the results of the estimated spoofed bias from the EKF and the normal bias shows that RMSE EKF = 3882 m . This error for the anti- spoofing particle filter is RMSE PF = 3785 m . Ha ving applied TSARM, the clock bias has been modified with a maximum error of RMSE TSARM = 258 m . Fig. 9 illustrates the RMSE of TSARM for a range of values for the window size, L , and the lag time, T lag . When the observation window is smaller , fe wer measurements are used for state estimation. On the other hand, when L exceeds 40 s , the number of states to be estimated grows although more measurements are employed for estimation. The numerical results illustrate that (6) models the clock bias and drift attacks effecti vely , which are subsequently estimated using (8) and corrected through (10). V I . C O N C L U D I N G R E M A R K S A N D F U T U R E W O R K This work discussed the research issue of time synchro- nization attacks on devices that rely on GPS for time tag- ging their measurements. T wo principal types of attacks are discussed and a dynamical model that specifically models these attacks is introduced. The attack detection technique solves an optimization problem to estimate the attacks on the clock bias and clock drift. The spoofer manipulated clock bias and drift are corrected using the estimated attacks. The proposed method detects the behavior of spoofer ev en if the measurements inte grity is preserved. The numerical results demonstrate that the attack can be largely rejected, and the bias can be estimated within 0 . 86 µ s of its true value, which lies within the standardized accuracy in PMU and CDMA applications. The proposed method can be implemented for real-time operation. In the present work, the set of GPS signals are obtained from an actual GPS recei ver in a real en vironment, but the attacks are simulated based on the characteristics of real spoofers reported in the literature. Experimentation on the behavior of the proposed detection and mitigation approach under real spoofing scenarios is the subject of future research. R E F E R E N C E S [1] “Energy .gov , Office of Electricity Delivery & Energy Reliability , ” http: //energy .gov/oe/services/technology- development/smart- grid, accessed: 2016-08-08. [2] “Gps.gov , Of ficial U.S. government information about the Global Positioning System (GPS) and related topics, ” http://www .gps.gov/applications/timing/. [3] B. W . Parkinson, J. J. Spilker , P . Axelrad, and P . Enge, Global P osition- ing System: Theory and Applications . American Institute of Aeronautics and Astronautics, 1996, vol. I. [4] ——, Global P ositioning System: Theory and Applications . American Institute of Aeronautics and Astronautics, 1996, vol. II. [5] P . Misra and P . Enge, Global P ositioning System: Signals, Measurements, and P erformance , 2nd ed. Ganga-Jamuna Press, Lincoln MA, 2006. [6] I. Y aesh and U. Shaked, “Neuro-adaptive h inf inity estimation and its application to improv ed tracking in GPS receivers, ” IEEE T rans. Ind. Electr on. , vol. 56, no. 3, pp. 642–647, Mar . 2009. [7] X. Li and Q. Xu, “ A reliable fusion positioning strategy for land vehicles in GPS-denied en vironments based on low-cost sensors, ” IEEE T rans. Ind. Electr on. , vol. 64, pp. 3205–3215, Apr . 2017. [8] “Electric sector failure scenarios and impact analyses - version 3.0, ” Electric Po wer Research Institute, T ech. Rep., Dec. 2015. [9] D. Schmidt, K. Radke, S. Camtepe, E. Foo, and M. Ren, “ A survey and analysis of the GNSS spoofing threat and countermeasures, ” ACM Computer Surve y , vol. 48, no. 4, pp. 64:1–64:31, May 2016. [10] B. Moussa, M. Debbabi, and C. Assi, “Security assessment of time synchronization mechanisms for the smart grid, ” IEEE Commun. Surve ys T ut. , vol. 18, no. 3, pp. 1952–1973, thirdquarter 2016. [11] D. P . Shepard, T . E. Humphreys, and A. A. Fansler , “Ev aluation of the vulnerability of phasor measurement units to GPS spoofing attacks, ” Int. J. Crit. Infrastruct. Protect. , vol. 5, pp. 146–153, Dec. 2012. [12] Z. Zhang, S. Gong, A. D. Dimitrovski, and H. Li, “Time synchronization attack in smart grid: Impact and analysis, ” IEEE T rans. Smart Grid , vol. 4, no. 1, pp. 87–98, Mar . 2013. [13] X. Jiang, J. Zhang, B. J. Harding, J. J. Makela, and A. D. Dominguez- Garc ´ ıa, “Spoofing GPS receiver clock offset of phasor measurement units, ” IEEE T rans. P ower Systems , vol. 28, pp. 3253–3262, Aug. 2013. [14] P . Risbud, N. Gatsis, and A. T aha, “ Assessing power system state estimation accuracy with GPS-spoofed PMU measurements, ” in IEEE T rans. Smart Grid , to be published. [15] T . Nighswander , B. Ledvina, J. Diamond, R. Brumley , and D. Brumley , “GPS software attacks, ” in Proc. of the ACM Conf. on Comput. and Commun. Security , Oct. 2012, pp. 450–461. [16] N. O. T ippenhauer, C. P ¨ opper , K. B. Rasmussen, and S. ˇ Capkun, “On the requirements for successful GPS spoofing attacks, ” in Pr oc. of the 18th ACM Conf. on Comput. and Commun. Security , Oct. 2011, pp. 75–86. [17] K. D. W esson, J. N. Gross, T . E. Humphreys, and B. L. Evans, “GNSS signal authentication via power and distortion monitoring, ” IEEE T rans. on Aer os. and Elect. Systems , vol. PP , no. 99, pp. 1–1, 2017. [18] M. L. Psiaki and T . E. Humphreys, “GNSS spoofing and detection, ” Pr oc. of the IEEE , vol. 104, no. 6, pp. 1258–1270, June 2016. [19] P . Papadimitratos and A. Jov anovic, “GNSS-based Positioning: Attacks and Countermeasures, ” in Pr oc. of the IEEE Military Commun. Conf. , San Diego, CA, USA, Nov . 2008, pp. 1–7. [20] Q. Zeng, H. Li, and L. Qian, “GPS spoofing attack on time synchro- nization in wireless networks and detection scheme design, ” in IEEE Military Communications Conference , Oct. 2012, pp. 1–5. [21] Y . Fan, Z. Zhang, M. Trinkle, A. D. Dimitrovski, J. B. Song, and H. Li, “ A cross-layer defense mechanism against GPS spoofing attacks on PMUs in smart grids, ” IEEE Tr ans. Smart Grid , v ol. 6, no. 6, pp. 2659–2668, Nov . 2015. [22] A. Ranganathan, H. ´ Olafsd ´ ottir , and S. Capkun, “SPREE: A spoofing resistant GPS recei ver , ” in Pr oc. of the 22Nd Annual Int. Conf . on Mobile Comput. and Netw . , 2016, pp. 348–360. [23] D. Chou, L. Heng, and G. X. Gao, “Robust GPS-based timing for phasor measurement units: A position-information-aided approach, ” in Pr oc. of the 27th Int. T ech. Meeting of The Sat. Division of the Institute of Navigation , Sept. 2014, pp. 1261 – 1269. [24] Y . Ng and G. X. Gao, “ Advanced multi-receiver position-information- aided vector tracking for robust GPS time transfer to PMUs, ” in Proc. of the Institute of Navigation GNSS+ Conf. (ION GNSS+ 2015) , Sept. 2015, pp. 3443 – 3448. [25] D.-Y . Y u, A. Ranganathan, T . Locher, S. ˇ Capkun, and D. Basin, “Short paper: Detection of GPS spoofing attacks in power grids, ” in Proc. of the ACM Conf. on Security and Privacy in W ir eless Mobile Netw . , 2014, pp. 99–104. [26] K. Jansen, N. O. Tippenhauer , and C. P ¨ opper , “Multi-receiver GPS spoofing detection: Error models and realization, ” in Proc. of the 32nd Annual Conf. on Comput. Security Appl. , 2016, pp. 237–250. [27] S. Han, D. Luo, W . Meng, and C. Li, “ A novel anti-spoofing method based on particle filter for GNSS, ” in Proc. of the IEEE Int. Conf. on Commun. (ICC) , June 2014, pp. 5413–5418. [28] F . Zhu, A. Y oussef, and W . Hamouda, “Detection techniques for data- lev el spoofing in GPS-based phasor measurement units, ” in Proc. of the 2016 Int. Conf. on Selected T opics in Mobile W ir eless Netw . (MoWNeT) , Apr . 2016, pp. 1–8. [29] D. P . Shepard and T . E. Humphreys, “Characterization of receiv er response to a spoofing attacks, ” in Proc. of the 24th Int. T ech. Meeting of The Sat. Division of the Institute of Navigation (ION GNSS 2011) , Portland, OR, Sept. 2011, pp. 2608 – 2618. [30] T . E. Humphreys, B. M. Ledvina, M. L. Psiaki, B. W . O’Hanlon, and P . M. Kintner, “ Assessing the spoofing threat: Development of a portable GPS ci vilian spoofer, ” in Pr oc. of the 21st Int. T ech. Meeting of the Sat. Division of The Institute of Navigation (ION GNSS 2008) , Sa vannah, GA, Sept. 2008, pp. 2314–2325. [31] B. Motella, M. Pini, M. Fantino, P . Mulassano, M. Nicola, J. Fortuny- Guasch, M. W ildemeersch, and D. Symeonidis, “Performance assess- ment of low cost GPS receivers under civilian spoofing attacks, ” in 5th ESA W orkshop on Sat. Nav . T ech. and Eur opean W orkshop on GNSS Signals and Signal Pr oc. , Dec. 2010, pp. 1–8. [32] P . T eunissen, “Quality control in integrated navigation systems, ” IEEE Aer os. and Elect. Sys. Magazine , vol. 5, pp. 35 – 41, July 1990. [33] L. Heng, J. J. Makela, A. D. Dominguez-Garc ´ ıa, R. B. Bobba, W . H. Sanders, and G. X. Gao, “Reliable GPS-based timing for power systems: A multi-layered multi-receiver architecture, ” in P ower and Ener gy Conf. at Illinois (PECI) , Feb. 2014, pp. 1–7. [34] L. Heng, D. B. W ork, and G. X. Gao, “GPS signal authentication from cooperativ e peers, ” IEEE T rans. on Intell. T ransportation Syst. , vol. 16, no. 4, pp. 1794–1805, Aug. 2015. [35] D. Radin, P . F . Swaszek, K. C. Seals, and R. J. Hartnett, “GNSS spoof detection based on pseudoranges from multiple receivers, ” in Pr oceedings of the 2015 International T echnical Meeting of The Institute of Navigation , Jan. 2015, pp. 657–671. [36] C. Masreliez and R. Martin, “Rob ust Bayesian estimation for the linear model and robustifying the Kalman filter , ” IEEE Tr ans. Autom. Contr ol , vol. 22, no. 3, pp. 361–371, June 1977. [37] S. Farahmand, G. B. Giannakis, and D. Angelosante, “Doubly robust smoothing of dynamical processes via outlier sparsity constraints, ” IEEE T rans. Signal Process. , vol. 59, pp. 4529–4543, Oct. 2011. [38] “ Android GNSS, ” https://developer .android.com/guide/topics/sensors/ gnss.html, accessed: 2017-02-20. [39] “IEEE standard for synchrophasor measurements for power systems, ” IEEE Std C37.118.1-2011 (Revision of IEEE Std C37.118-2005) , pp. 1–61, Dec. 2011. [40] “Model 1088b GPS satellite clock (40 ns), ” http://www .arbiter .com/ catalog/product/model- 1088b- gps- satellite- precision- time- clock- 40ns. php, accessed: 2017-02-20. [41] Z. Zhang, S. Gong, A. D. Dimitrovski, and H. Li, “Time synchronization attack in smart grid: Impact and analysis, ” IEEE T rans. on Smart Grid , vol. 4, no. 1, pp. 87–98, March 2013. [42] F . I. Karahanoglu, . Bayram, and D. V . D. V ille, “ A signal processing ap- proach to generalized 1-D total variation, ” IEEE T rans. Signal Process. , vol. 59, no. 11, pp. 5265–5274, Nov . 2011. [43] S. Boyd and L. V andenberghe, Conve x Optimization . Cambridge Univ ersity Press, 2004. [44] R. G. Brown and P . Y . C. Hwang, Intr oduction to random signals and applied Kalman filtering: with MATLAB exer cises and solutions; 3rd ed. New Y ork, NY : W iley , 1997. [45] S. M. Kay , Fundamentals of Statistical Signal Pr ocessing, V olume II: Detection Theory . Prentice-Hall Inc, 1993. Ali Khalajmehrabadi (S’16) received the B.Sc. degree from the Babol Noshir vani University of T echnology , Iran, in 2010, and the M.Sc. degree from Univ ersity T echnology Malaysia, Mala ysia, in 2012, where he w as aw arded the Best Gradu- ate Student Aw ard. He is currently pursuing the Ph.D . degree with the Depar tment of Electr ical and Computer Engineer ing, Univ ersity of T exas at San Antonio. His research interests include in- door localization and navigation systems, collab- orativ e localization, and global navigation satel- lite system. He is a Student Member of the Institute of Navigation and the IEEE. Nikolaos Gatsis (S’04-M’05) received the diploma (with Hons.) degree in electrical and computer engineering from the University of Pa- tras, Greece, in 2005, and the M.Sc. degree in electrical engineering and the Ph.D . degree in electrical engineering with minor in mathematics from the University of Minnesota, in 2010 and 2012, respectively . He is currently an Assistant Professor with the Depar tment of Electr ical and Computer Engineer ing, University of T e xas at San Antonio. His research interests lie in the areas of smar t power grids, communication networks, and cyberphysical systems, with an emphasis on optimal resource management and sta- tistical signal processing. He has co-organized symposia in the area of smar t grids in IEEE GlobalSIP 2015 and IEEE GlobalSIP 2016. He has also ser ved as a co-guest editor for a special issue of the IEEE Jour nal on Selected T opics in Signal Processing on cr itical infrastructures. David Akopian (M’02-SM’04) received the Ph.D . degree in electrical engineer ing in 1997. He is a Prof essor with the University of T exas at San Antonio . He was a Senior Research En- gineer and a Specialist with Nokia Cor poration from 1999 to 2003. F rom 1993 to 1999, he was a Researcher and an Instructor with the T ampere Univ ersity of T echnology , Finland. He has authored and coauthored over 30 patents and 140 pub lications. His current research inter- ests include digital signal processing algor ithms for communication and na vigation receivers, positioning, dedicated hardware architectures and platforms for software defined radio and communication technologies for healthcare applications. He ser ved in organizing and program committees of many IEEE conferences and co-chairs annual SPIE Multimedia on Mobile De vices conf erences. His research has been suppor ted by the National Science Foundation, National Institutes of Health, USAF , U .S. Navy , and T exas f oundations. Ahmad F . T aha (S’07–M’15) received the B.E. and Ph.D . degrees in Electrical and Computer Engineering from the Amer ican University of Beirut, Lebanon in 2011 and Purdue University , West Lafa yette, Indiana in 2015. In Summer 2010, Summer 2014, and Spring 2015 he was a visiting scholar at MIT , University of T oronto , and Argonne National Laboratory . Currently he is an assistant professor with the Depar tment of Electr ical and Computer Engineering at The University of T e xas, San Antonio. Dr. T aha is in- terested in understanding how comple x cyber-physical systems operate, behav e, and misbehav e . His research focus includes optimization and control of power system, obser ver design and dynamic state estimation, and cyber-security .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment