Linking Received Packet to the Transmitter Through Physical-Fingerprinting of Controller Area Network
The Controller Area Network (CAN) bus serves as a legacy protocol for in-vehicle data communication. Simplicity, robustness, and suitability for real-time systems are the salient features of the CAN bus protocol. However, it lacks the basic security features such as massage authentication, which makes it vulnerable to the spoofing attacks. In a CAN network, linking CAN packet to the sender node is a challenging task. This paper aims to address this issue by developing a framework to link each CAN packet to its source. Physical signal attributes of the received packet consisting of channel and node (or device) which contains specific unique artifacts are considered to achieve this goal. Material and design imperfections in the physical channel and digital device, which are the main contributing factors behind the device-channel specific unique artifacts, are leveraged to link the received electrical signal to the transmitter. Generally, the inimitable patterns of signals from each ECUs exist over the course of time that can manifest the stability of the proposed method. Uniqueness of the channel-device specific attributes are also investigated for time- and frequency-domain. Feature vector is made up of both time and frequency domain physical attributes and then employed to train a neural network-based classifier. Performance of the proposed fingerprinting method is evaluated by using a dataset collected from 16 different channels and four identical ECUs transmitting same message. Experimental results indicate that the proposed method achieves correct detection rates of 95.2% and 98.3% for channel and ECU classification, respectively.
💡 Research Summary
The paper addresses a fundamental security weakness of the Controller Area Network (CAN) bus: the lack of built‑in message authentication, which makes it vulnerable to spoofing attacks. Because CAN frames contain no identifier that proves the origin of a message, any node on the bus can impersonate any other node, opening a wide attack surface for both internal and external adversaries. Existing countermeasures—cryptographic MACs, hash‑based authentication, or clock‑skew fingerprinting—either impose prohibitive overhead on the low‑bandwidth, real‑time CAN bus or suffer from environmental sensitivity.
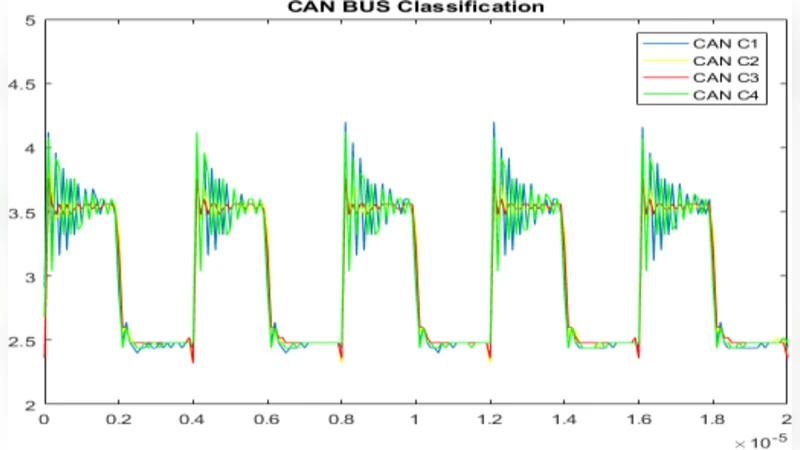
To overcome these limitations, the authors propose a physical‑layer fingerprinting framework that links a received CAN packet to its transmitter (both the Electronic Control Unit, ECU, and the physical channel) by exploiting minute, device‑specific artifacts present in the analog voltage waveform. The core idea is that each ECU’s digital driver circuitry and each cable’s construction (material, geometry, manufacturing tolerances) imprint a unique impulse response on the transmitted signal. Mathematically, the received signal at the fingerprinting unit is modeled as
y₍ᵢⱼ₎(t) = hⱼ(t) * Sᵢ(t)
where Sᵢ(t) is the voltage waveform generated by ECU i, hⱼ(t) is the impulse response of physical channel j, and * denotes convolution. Even when the same CAN identifier and data payload are transmitted, the combination of Sᵢ and hⱼ yields subtly different waveforms that can be captured and analyzed.
The experimental setup consists of four identical Arduino‑based ECUs equipped with MCP2515 CAN controllers and MCP2551 transceivers. Three commercially used automotive cable families—GXL, TXL, and SAE J1939‑15—are employed at six lengths (0.5 m to 5 m), creating 18 distinct channel configurations. An oscilloscope with 2 GSa/s sampling rate records the voltage at the input of a dedicated “PhyFin” unit for each transmission. For each channel‑ECU pair, 144 000 samples (3600 frames × 40 samples per frame) are collected under constant temperature and supply voltage, ensuring that observed variations stem from intrinsic hardware differences rather than environmental noise.
Feature extraction proceeds in two stages. First, a library (LibXtract) computes 40 raw statistical descriptors in both time and frequency domains. Then, the FEAST toolbox ranks these descriptors using joint mutual information (JMI) to select the most discriminative subset. The final feature vector contains 11 dimensions: six time‑domain statistics (maximum, minimum, mean, variance, skewness, kurtosis) and five frequency‑domain metrics (spectral standard deviation, spectral skewness, spectral kurtosis, spectral centroid, and Irregularity‑K).
These 11‑dimensional vectors feed a multilayer perceptron (MLP) neural network. Separate classifiers are trained for channel identification (16 classes) and ECU identification (4 classes). The dataset is randomly split, with 65 % used for training and 35 % for testing. Classification accuracy serves as the primary performance metric.
Results show that the channel classifier achieves 95.2 % accuracy, while the ECU classifier reaches 98.3 % accuracy. The high scores demonstrate that the physical‑layer artifacts are both stable over time and sufficiently distinct across different cables and ECUs, even when the ECUs are nominally identical and transmit identical CAN frames. The authors also discuss the practical implications: a malicious node that injects a spoofed message from an unauthorized ECU or via a different cable will produce a waveform that does not match the legitimate fingerprint, enabling detection by an intrusion detection system (IDS).
The paper concludes with several avenues for future work. First, robustness against real‑world variations—temperature swings, supply voltage fluctuations, electromagnetic interference, and aging of components—must be evaluated. Second, the computational load of the neural network should be assessed for real‑time deployment on automotive ECUs or dedicated security modules. Third, integration with higher‑layer authentication schemes could provide defense‑in‑depth, combining cryptographic guarantees with physical fingerprinting. Finally, scaling the approach to larger networks with dozens of ECUs and heterogeneous cable types will require more sophisticated feature selection and possibly hierarchical classification strategies.
Overall, the study provides compelling evidence that physical‑layer fingerprinting can serve as a lightweight, hardware‑rooted method for authenticating CAN messages, complementing existing security mechanisms and moving automotive networks a step closer to the resilience required for modern connected vehicles.
Comments & Academic Discussion
Loading comments...
Leave a Comment