Breaking Mignottes Sequence Based Secret Sharing Scheme Using SMT Solver
The secret sharing schemes are the important tools in cryptography that are used as building blocks in many secured protocols. It is a method used for distributing a secret among the participants in a manner that only the threshold number of participants together can recover the secret and the remaining set of participants cannot get any information about the secret. Secret sharing schemes are absolute for storing highly sensitive and important information. In a secret sharing scheme, a secret is divided into several shares. These shares are then distributed to the participants one each and thus only the threshold (t) number of participants can recover the secret. In this paper we have used Mignotte’s Sequence based Secret Sharing for distribution of shares to the participants. A (k, m) Mignotte’s sequence is a sequence of pair wise co-prime positive integers. We have proposed a new method for reconstruction of secret even with t-1 shares using the SMT solver.
💡 Research Summary
The paper revisits the classic Mignotte‑sequence secret‑sharing scheme and demonstrates that it is vulnerable to reconstruction attacks even when fewer than the prescribed threshold of shares are available. A (k, m) Mignotte sequence consists of pairwise‑coprime positive integers a₁ < a₂ < … < a_m. For a chosen threshold t, the product of the smallest t moduli, M = ∏{i=1}^{t} a_i, and the product of the largest (t‑1) moduli, L = ∏{i=m‑t+2}^{m} a_i, define a range (L, M) within which the secret S must lie. Each participant receives a share s_i = S mod a_i. Traditional reconstruction requires t shares and the Chinese Remainder Theorem (CRT) to recover S exactly.
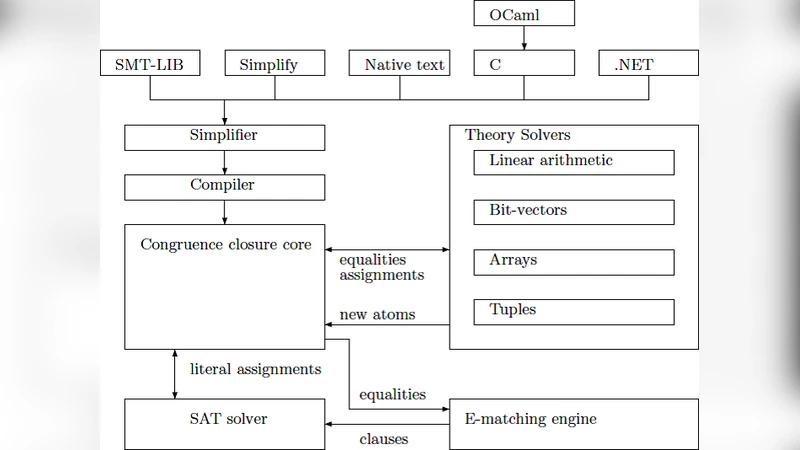
The authors point out that the Mignotte construction is not a perfect secret‑sharing scheme: t‑1 shares already constrain S to a relatively narrow interval, leaking information. To exploit this leakage, they formulate the reconstruction problem as a set of integer constraints and feed it to an SMT (Satisfiability Modulo Theories) solver, specifically Z3. The constraint system consists of: (1) 0 ≤ x < M, (2) x mod a_{i_j} = s_{i_j} for each of the t‑1 known shares, and (3) L < x < M. These constraints combine linear arithmetic with modular arithmetic, both of which are natively supported by modern SMT engines.
By invoking Z3, the solver searches for integer models that satisfy all constraints. In the experimental section the authors test small parameter sets (e.g., m = 5, t = 3) and show that, in many instances, the constraint system admits a unique solution, which is precisely the original secret. The attack succeeds quickly because the interval (L, M) is often small when the moduli a_i are modest in size; the SMT solver can prune the search space efficiently and converge on the unique solution.
The paper discusses two important observations. First, the security of the Mignotte scheme heavily depends on the magnitude of the chosen moduli. If the a_i are large (e.g., 1024‑bit integers), the interval between L and M becomes astronomically wide, and the SMT solver’s search space explodes, rendering the attack impractical with current technology. Second, the authors note that their evaluation is limited to relatively small instances; they do not provide a thorough performance analysis for cryptographically sized parameters.
From a cryptographic perspective, the work highlights a structural flaw: Mignotte’s construction does not achieve information‑theoretic secrecy. An adversary with t‑1 shares can gain non‑trivial knowledge about the secret, and with modest computational effort (an SMT solver) can often recover it outright. The authors therefore recommend abandoning Mignotte‑based sharing in favor of schemes that are provably perfect, such as Shamir’s polynomial‑based secret sharing, which guarantees that any set of fewer than t shares yields zero information about the secret.
If a practitioner wishes to retain a Mignotte‑style scheme, the paper suggests two mitigations: (i) choose the moduli sufficiently large to make the (L, M) interval infeasible to search, and (ii) add random padding or auxiliary secret‑sharing layers to mask the underlying integer constraints. However, these work‑arounds essentially transform the scheme into a different construction and undermine the original simplicity that made Mignotte attractive.
In conclusion, the authors provide a concrete, formal demonstration that SMT solvers constitute a powerful new attack vector against non‑perfect secret‑sharing schemes. Their methodology not only breaks the specific Mignotte instance studied but also serves as a template for analyzing other integer‑based sharing protocols. The paper thus serves as a cautionary tale for cryptographers: even classical schemes must be re‑examined under modern automated reasoning tools, and designers should prefer schemes with proven information‑theoretic security guarantees.
Comments & Academic Discussion
Loading comments...
Leave a Comment