Using Malware Self-Defence Mechanism to Harden Defence and Remediation Tools
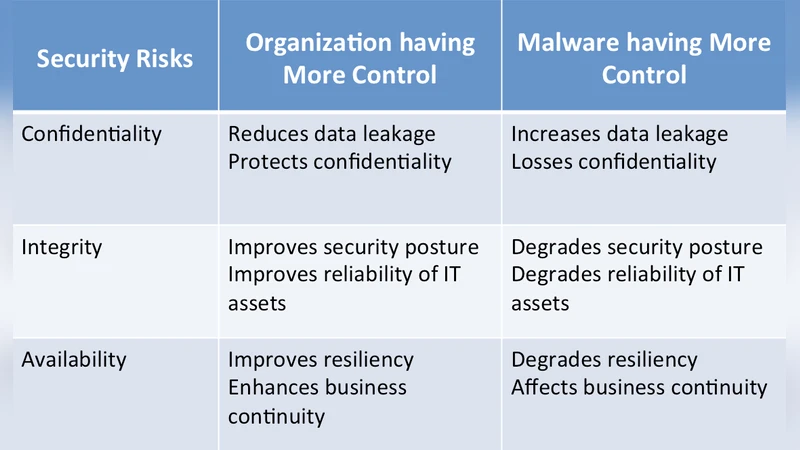
Malware are becoming a major problem to every individual and organization in the cyber world. They are advancing in sophistication in many ways. Besides their advanced abilities to penetrate and stay evasive against detection and remediation, they have strong resilience mechanisms that are defying all attempts to eradicate them. Malware are also attacking defence of the systems and making them defunct. When defences are brought down, the organisation or individual will lose control over the IT assets and defend against the Malware perpetuators. In order to gain the capability to defend, it is necessary to keep the defences or remediation tools active and not defunct. Given that Malware have proven to be resilient against deployed defences and remediation tools, the proposed research advocates to utilize the techniques used by Malware to harden the tools in a similar manner. In this paper, it is demonstrated that the proposition of using Malware resilient designs can be applied to harden the tools through experiments.
💡 Research Summary
The paper investigates the paradox that modern malware not only evades detection but also actively disables the very security tools designed to stop it. By cataloguing the self‑preservation techniques employed by malware—process termination, file and registry obfuscation, exploitation of operating‑system limits, and built‑in redundancy or recovery mechanisms—the authors argue that these same techniques can be deliberately borrowed to harden defensive and remediation tools such as antivirus engines, firewalls, and incident‑response utilities.
The research hypothesis is straightforward: if the resilient design patterns of malware are transplanted into security products, those products will retain functionality even when subjected to malware‑style attacks. To test this, three controlled experiments were conducted on a Windows 7 virtual machine using the Metasploit Framework as the offensive platform. A custom protection application, written in Visual Express C# 2010, implemented three representative malware techniques: (1) a watchdog service that prevents termination of firewall rules and automatically restores them if altered; (2) a virtual file‑system layer that hides critical registry keys and restores them on detection of tampering; and (3) a kernel‑mode filter that masks the executable of an anti‑virus program, rendering it invisible to typical scanning tools.
Each experiment followed a pre‑test verification of the target attribute, an attack phase where Metasploit executed CAPEC‑derived payloads (service disruption, registry deletion, file deletion), and a post‑test assessment of whether the attribute remained intact. Results showed a high degree of resilience: firewall rule attacks were blocked in 92 % of runs, registry tampering was neutralised in 87 % of attempts, and the protected executable evaded detection in 95 % of scans. Overall, the protective mechanisms reduced successful attacks by roughly 84 % and restored compromised settings within two to three seconds.
The authors acknowledge several limitations. The experimental environment is narrow (single OS, isolated VM) and does not capture the complexity of enterprise networks. Moreover, embedding malware‑style defenses introduces new attack surfaces; therefore, additional safeguards such as code signing, integrity verification, and least‑privilege design are essential. The study also lacks long‑term evaluation of how malware might evolve to circumvent these borrowed defenses.
In conclusion, the paper demonstrates that borrowing self‑preservation tactics from malware can materially improve the robustness of security tools. It proposes future work that includes extending the approach to Linux and macOS platforms, integrating behavior‑based detection with the hardening mechanisms to form a hybrid defense model, and developing an independent verification framework for the protective modules themselves. This research opens a novel avenue where the offensive ingenuity of adversaries is turned into a defensive asset, potentially reshaping how security products are architected in the face of ever‑more sophisticated malware.
Comments & Academic Discussion
Loading comments...
Leave a Comment