Application of Machine Learning for Channel based Message Authentication in Mission Critical Machine Type Communication
The design of robust wireless communication systems for industrial applications such as closed loop control processes has been considered manifold recently. Additionally, the ongoing advances in the area of connected mobility have similar or even hig…
Authors: Andreas Wein, Michael Karrenbauer, Raja Sattiraju
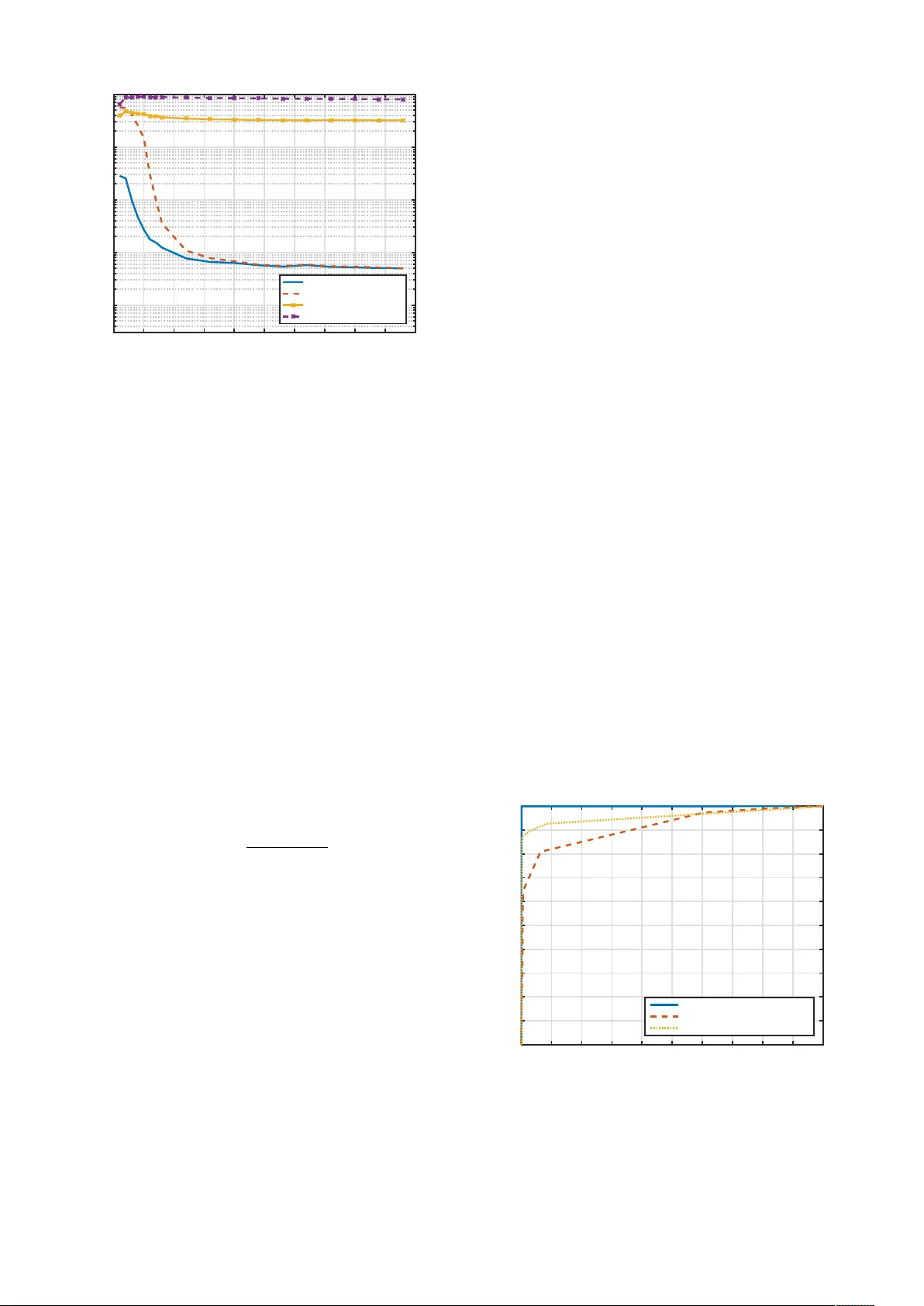
Application of Machine Learning for Channel based Message Authentication in Mission Critical Machine T ype Communication Andreas W einand, Michael Karrenbauer , Raja Sattiraju, Hans D. Schotten Institute for W ireless Communication and Navigation Univ ersity of Kaiserslautern, Germany Email: { weinand, karrenbauer , sattiraju, schotten } @eit.uni-kl.de Abstract —The design of rob ust wireless communication sys- tems for industrial applications such as closed loop contr ol processes has been considered manifold recently . Additionally , the ongoing advances in the area of connected mobility hav e similar or even higher r equirements r egarding system reliability and a vailability . Beside unfulfilled r eliability requir ements, the av ailability of a system can further be reduced, if it is under attack in the sense of violation of information security goals such as data authenticity or integrity . In order to guarantee the safe operation of an application, a system has at least to be able to detect these attacks. Though there are numerous techniques in the sense of con ventional cryptography in order to achiev e that goal, these ar e not always suited for the requir ements of the applications mentioned due to resour ce inefficiency . In the pr esent work, we show how the goal of message authenticity based on physical lay er security (PHYSEC) can be achie ved. The main idea for such techniques is to exploit user specific characteristics of the wireless channel, especially in spatial domain. Additionally , we show the performance of our machine learning based appr oach and compare it with other existing approaches. I . I N T RO D U C T I O N Currently , there are two major developments in the area of wireless systems regarding highly safety critical applica- tions such as closed loop control applications in the area of industrial systems ([1]) and network based autonomous driving functions in the area of vehicular systems. These hav e much higher requirements regarding reliability , a vailability and also latency compared to common applications, such as e.g. media streaming or web browsing over IEEE 802.11 based wireless systems or today’ s cellular 4G L TE networks. Another important requirement in the area of mission critical machine type communication (MC-MTC) is the fact, that secure trans- mission of data has to be taken into account. Due to the sensitiv e information transmitted in the mentioned scenarios, it is necessary to guarantee a high degree of information security . Especially confidentiality , authenticity , as well as integrity of the transmitted data has to be ensured to prohibit a wide range of possible passive and acti ve cyber attacks. For this purpose, This is a preprint, the full paper has been published in Proceedings of 23th European W ireless Conference (European Wireless 2017), c 2017 IEEE. Personal use of this material is permitted. Howe ver , permission to use this material for any other purposes must be obtained from the IEEE by sending a request to pubs-permissions@ieee.org. encryption of transmitted messages is necessary in order to be sure of the confidentiality of the respecti ve payload and authentication of the originator as well as integrity checking of received messages have to be ensured before they are consumed and processed by a safety critical application. Although there are conv entional cryptography techniques to ensure authenticity as well as integrity of message payload, these require a not negligible amount of resources. Especially they lead to increase in message size due to the fact that, for example message authentication codes (MAC), which are com- monly used in deployed systems (e.g. in IEEE 802.15.4 based systems), add a cryptographic check sum to the actual message payload. The recommendation of the Internet Engineering T ask Force is to either use a CMA C (cipher based MA C), e.g. based on a AES-128 block cipher , or a HMAC which is based on a cryptographic hash function. For AES-128 based CMAC a maximum shortening to 64 Bit is recommended [2], while for HMA C a minimum MA C size of 80 Bit is recommended [3]. If we now assume that the payload of a MC-MTC packet in the uplink has a length of 400 Bit (the dimension of this assumption is e.g. confirmed by [1] and [4]), then the overhead and with this the additional latency introduced in case of a AES-128 based CMA C of 64 Bit length would be 13 . 8% . Another important issue is, that key based schemes such as MA C are only able to protect the message payload from the mentioned attacks. An attacker is still able to perform attacks such as address spoofing, or even worse, record a message and replay it after a while (if counters are used to prohibit that, additional latency is added as well). Due to these drawbacks, another idea is to check for message authenticity at a lower lev el by taking physical properties of the radio link signal into account. In this work, we focus on a keyless approach in order to achie ve that goal based on estimating the wireless channel and detection of different users based on that. As mentioned, MC-MTC is considered here, for which it is assumed that frequent and periodic data transmissions (e.g. once per ms [1], [4]) and with this channel estimation at the same rate is av ailable. For experimental ev aluation, we consider an OFDM system and based on the respectiv e frequency domain channel estimations, we decide from which source a receiv ed data packet was transmitted. The remainder of the work is organized as follows. In section II we giv e a short overvie w on related work with respect to previous considered approaches and in section III we describe the system model. The machine learning approach for physical layer based message authentication is presented in section IV. In section V we present the results of our work in form of an experimental ev aluation of the considered approach and section VI finally concludes the paper . I I . R E L A T E D W O R K Sev eral approaches on exploiting the wireless channel for security purposes, also kno wn as PHYSEC, hav e been in ves- tigated recently . In [5] a good overvie w on this topic is gi ven. While many works have focused on extracting secret keys between two communicating devices, such as [6], [7], [8], the focus of our work is on guaranteeing secure transmission with respect to authenticity of data packets from one device to another . One of the first works considering that idea has been for e xample [9], where an approach based on channel measurements and hypothesis testing is presented for static scenarios and is later in [10] e xtended to time-variant sce- narios. Though the results of these works are plausible, they are obtained from simulations of the wireless channel only . Therefore, in our work we will focus on real world channels. In [11], two approaches based on machine learning, Support V ector Machine and Linear Fisher Discriminant Analysis, are presented. The approach considered in [12] is similar to our approach, as they propose a CSI-based authentication method. Howe ver , they consider a single carrier system, while we will focus on a multi carrier system in our work. The second approach considered in [12] is whiteness of residuals testing. In [13] an RSSI-based approach for body area networks is presented. The work in [14] considers a multilayer approach based on OFDM to guarantee authentication of TCP packets. A Gaussian Mixture Model based technique in combination with e xploitation of the channel responses for dif ferent antenna modes is considered in [15]. In [16] a MIMO OFDM system is considered and a generalized likelihood ratio test is used as detection method. Further , the authors derive information theoretic bounds for the channel based detection problem. The authors in [17] consider a cellular Internet-of-Things system and propose a scheme for channel based message authentication of nodes with the help of anchor nodes, which are assumed to have set up trust to the concentrator node before. I I I . S Y S T E M M O D E L In this section we describe the system model and the channel model considered in our work. Further, the attacker model is introduced. A. Communication Model W e consider two users, Alice and Bob, who w ant to exchange authenticated messages with each other over a public channel. A third user Eve, who is an adversarial user, tries to inject illegal messages masqueraded as one of the legal users Alice or Bob. Fig. 1 shows the possible message flows for all considered users. Messages transmitted by users are denoted with x u and messages received by users with y u , where u denotes user Alice ( u = A ), Bob ( u = B ) or Eve ( u = E ). Fig. 1: System Model B. Channel Model and Channel Estimation In our work, we focus on channel state information (CSI), which is e.g. computed at the receiv er side in form of a frequency domain channel estimation. The main idea for all PHYSEC based techniques is to make use of the fast spatial decorrelation property of the wireless channel. For that purpose, the users need to be able estimate the channel to each other . The recei ved signal at a user u i is y u i = H u i u j x u j + n u i u j (1) with H u i u j = [ h 0 u i u j , . . . , h M − 1 u i u j ] (2) being the M -dimensional channel matrix of the frequency- selectiv e SISO fading channel between user u i and u j (trans- mitter) and h ` u i u j being the gain of the ` -th sample in frequency domain ( ` = 0 , . . . , M − 1 ). It can be estimated as ˆ H u i u j = H u i u j + u i u j (3) by user u i . Due to noise n u i u j which is modelled as a gaussian random v ariable with zero mean and variance σ 2 n u i u j the channel estimation is not perfect and errors u i u j occur . C. Attacker Model A typical scenario for an attacker Eve is, that he is at a spatially different location compared to Bob and Alice (we assume a distance of more than the wav elength of the transmitted signal respectively) and uses adv anced equipment such as directed antennas and high sensiti vity receivers in order to maximize the cov erage to his benefit. W e also assume perfect knowledge of the underlying communication protocol at Eve to run acti ve attacks such as masquerade attacks, replay attacks or address spoofing attacks by introducing messages x E . It is further assumed, that Eve is able to eavesdrop on ongoing transmissions of Alice ( y E = H EA x A + n EA ) and Bob ( y E = H EB x B + n EB ) and estimate the respectiv e channels H EA and H EB . With this information, Eve is able to manipulate its injected messages x E with a pre-processing filter G E in such a way , that the channel between the legal users is imitated. For this work we assume that G E = 1 and with this H AE 6 = H AB and H BE 6 = H BA . It is not assumed that Eve is gaining physical access to Alice or Bob to accomplish inv asiv e attacks such as hardware modification. Further , other active attacks such as Denial-of-Service attacks due to jamming are not considered as well. It is assumed, that the legal communicating participants Bob and Alice have already carried out initial user authentication to each other and have set up trust in a secure way . Attacks on the initial authentication stage are not considered. I V . M A C H I N E L E A R N I N G A N D C H A N N E L B A S E D A U T H E N T I C A T I O N In this section, we sho w ho w channel based message authen- tication with the help of machine learning can be achiev ed. In general, all machine learning algorithms contain two stages. In the first stage, the respectiv e algorithm needs to be trained to the kind of data it is intended to estimate. In our case, this data are channel estimations taken on received data packets. If we now consider the users Alice and Bob again, e.g. Bob wants to transmit authenticated messages to Alice. Alice will estimate the channel as ˆ H AB ( k ) during the training phase for each of the T recei ved messages y A ( k ) , k = 0 , . . . , T − 1 . In this stage we also assume, that the acquired data is labeled. This means that the messages x B sent by Bob contain cryptographic information from higher layers (e.g. certificates) in order to authenticate to Alice initially during that stage. The acquired data ˆ H AB ( k ) and the respectiv e labels are fed to the training procedure of the machine learning algorithm. In the second stage, the trained model is used in order to make a decision on further receiv ed messages y A ( m ) at time m . If Alice estimates the channel now as ˆ H ( m ) , there are two hypothesis, either H 0 : y A ( m ) w as sent b y Bob , or H 1 : y A ( m ) w as not sent b y Bob . (4) In case of hypothesis H 0 ˆ H ( m ) = H AB ( m ) + AB ( m ) , (5) and in case of hypothesis H 1 ˆ H ( m ) 6 = H AB ( m ) + AB ( m ) . (6) Due to temporal variations in the channel H AB , these need to be somehow considered in the second stage. Otherwise it is no t possible to distinguish between channel variations and messages introduced by an attacker anymore at some point. There are two possibilities in order to achiev e that goal, either the machine learning algorithm needs to be updated regularly , or instead of this, the difference of the current channel estimate to the previous one ∆ ˆ H ( m ) = ˆ H ( m ) − ˆ H ( m − 1) (7) is used as input data for the machine learning algorithm. In the first case, the model update interv al should be belo w the channel coherence time T c of the H AB channel in order to catch up with these variations. Whereas in both cases, the temporal dif ference between two subsequent channel estima- tions should always be below T c . Fig. 2 shows all steps of the general procedure described abov e. Fig. 2: Channel based Message Authentication using Machine Learning Every machine learning estimator has basically two main performance indicators, the detection probability P D and the false alarm rate P F A . In our case, the detection probability P D = p ( H 1 | ˆ H ( m ) due to x E ) (8) denotes the probability of detecting Eve as the transmitter of y A ( m ) under the condition that it was truly sent by Eve and the false alarm rate P F A = p ( H 1 | ˆ H ( m ) due to x B ) (9) denotes the probability of detecting Eve as the transmitter of y A ( m ) under the condition that it was truly sent by Bob. Both performance metrics need to be considered jointly , as they can not be optimized independently . The relation of both can be shown in a receiv er operating characteristic (ROC) curve. V . R E S U LT S In this section we describe our setup for the experimental ev aluation and sho w the results of our work. Further, we compare them with results of related work. A. Experimental setup T o ev aluate our concepts, we use USRP N210 SDR plat- forms from Ettus Research with SBX daughterboards. W e use GNURadio OFDM transmitter and receiv er blocks to process data packets and perform channel estimation on each received data packet. A setup with an FFT size of 64 is considered and 48 activ e subcarriers. The cyclic prefix length is 16 samples at a baseband sample rate of 3 . 125 MSps, whereas the carrier frequency is 2 . 45 GHz. For each recei ved data packet, the 0 5 10 15 20 25 30 35 40 45 50 feature dimension 10 -4 10 -3 10 -2 10 -1 10 0 misdetection rate GMM Method, FAR=0.01 GMM Method, FAR=0.001 MSE Method, FAR=0.01 MSE Method, FAR=0.001 Fig. 3: Misdetection rate for different false alarm rates initial channel taps are calculated based on the kno wn Schmidl and Cox preamble [18] which is also used to calculate the frequency of fset at the receiv er (actually this preamble consists of two OFDM symbols). In each message, this preamble is followed by 37 data symbols yielding a time resolution of 998.4 µ s for the channel estimations. As a first step, we consider a static setup where all participants do not mov e during transmitting and receiving. The environment is a mixed office/lab area with a lot of objects and metal walls. Due to this we assume that at least some amount of multipath prop- agation is existing and with this frequency selective channels. W e record data for several dif ferent locations of Bob and Eve respectively , yielding multiple different constellations of Bob-Alice and Eve-Alice pairs. W e choose Gaussian Mixture Model (GMM) based clus- tering as detection method in order to authenticate received messages. W e considered a block size of N = 1000 data sets in order to update the GMM, whereas one block is used for training the model and 99 blocks are used in order to test it. The attack intensity was kept at 50% . W e use the magnitude of normalized channel estimations F ( m ) = ˆ H ( m ) M − 1 P ` =0 ˆ h ` ( m ) (10) as input data (feature) for the GMM estimator . B. P erformance of GMM based Clustering Fig. 3 shows the probability of misdetection P MD = 1 − P D (11) or misdetection rate (MDR) in dependence of the number of estimated subcarriers M used for the detection. The influence of the accuracy of the channel estimation in the sense of different dimensions of the feature vector F ( m ) can be seen, as for increasing values of M the MDR overall drops. If only M = 4 subcarriers (equally spaced) are considered, the MDR of the GMM method is at 25 . 68% at a false alarm rate of 0 . 1% and at 0 . 47% at a false alarm rate of 1% . For the case of M = 16 subcarriers (equally spaced) considered, the MDR decreases by 99 . 67% to 0 . 08% at a false alarm rate of 0 . 1% and by 85 . 11% to 0 . 07% at a false alarm rate of 1% . In case of the MSE based detection method from [19], the MDR is at 43 . 03% in case of M = 4 and 1% false alarm rate, which is an increase of 9055 . 32% compared to the GMM method and in case of a false alarm rate of 0 . 1% , the MDR is at 89 . 21% , which is an increase of 247 . 39% compared to the GMM method. In case of M = 16 , the MDR of the MSE based method is at 33 . 62% at a false alarm rate of 1% , which is an increase of 479 . 29% compared to the GMM method. For a false alarm of 0 . 1% the MDR is at 85 . 36% , which is an increase of 1066% compared to the GMM method. Fig. 4 shows the influence of the updating process within the GMM based clustering method. If the updating process of the model is switched off, the detection rate decreases significantly . At a false alarm rate of 1% , the detection rate for GMM based detection without updating is at 88 . 06% , which is a performance loss of 11 . 9% compared to the GMM based detection with updating. Howe ver , the GMM based method without updating still outperforms the MSE based method ( 65 . 78% detection rate) by a 33 . 87% higher detection rate. For a false alarm rate of 0 . 1% , the MSE method performance loss is e ven worse as the detection rate decreases to 17 . 69% which is 79 . 53% less compared to the GMM method without updating ( 86 . 43% detection rate) and 82 . 3% less compared to the GMM method with updating ( 99 . 96% detection rate). The performance loss for the GMM method without updating compared to the GMM method with updating is 13 . 54% . C. Discussion of Results The experimental ev aluation of our method sho ws us ba- sically two things. The first one is, that the performance of our GMM based clustering method increases as the dimension of the considered feature, which is in our case the number 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 false alarm rate 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 detection rate GMM Method, M=48, w/ Updating MSE Method, M=48 GMM Method, M=48, w/o Updating Fig. 4: GMM based method with und without updating T ABLE I: Performance of related work (selection) W ork Detection Method Feature max. P D min. P F A [15] GMM Antenna Mode 99 . 9% 0 . 4% [11] SVM, LFDA RSSI, TOA, CC 95% 1% [12] NPHT CIR (TD) 99 . 9% 1% [10] NPHT CIR (FD) 99% 1% Here GMM CIR (FD) 99 . 96% 0 . 1% of equally spaced estimated frequency points M for each re- ceiv ed message, also increases (with this the misdetection rate decreases). Howe ver , if the model that classifies the input data is not updated (or a method that does not consider updating of the classifier during operation is used), the performance is decreased, which leads to the conclusion that only classifiers which allow for online updating fulfill the needs for the channel based authentication approach. If we compare our GMM based approach with related ones (see T ab . I), the performance of it is similar to them, though some of them use different features that are fed to the detection method (which as well differs from our detection method in some cases). Overall, our approach performs comparable to the approaches of the related work, and compared to e.g. [11] ev en slightly better for the detection rate ( 5 . 22% higher) and in case of the false alarm rate ( 90% lower), the performance is better as well. V I . C O N C L U S I O N A N D F U T U R E W O R K Our proposed method of taking user specific channel charac- teristics in form of the frequency domain OFDM channel esti- mation into account in order to identify and authenticate them seems to be a promising technique in order to achie ve that goal in a very efficient way . Especially for MC-MTC messages, the application of channel based message authentication can lead to reduced transmission latency . Further, the combination of both, MC-MTC and channel based authentication is essen- tial considering system efficiency , as both rely on frequent transmission of data packets. W ith this, frequent channel estimations are available, which can be reused with little to no further effort. Though the maximum achieved detection rate is high at 99 . 96% , the method needs still to be improved in order to get more reliable decisions. For that purpose, additional features within the detection process such as RSSI or TO A might be helpful. Further, the tradeof f between complexity and performance of the detection method is an issue that needs to be addressed in future work. Therefore additional detection methods could be in vestigated. T o gain robustness due to errors in channel estimation induced by noise, approaches such as in [20] might be suited in order to reduce this ef fect based on pre- processing of channel estimates. Additionally we also want to focus on a mobile setup with little to moderate velocities in order to verify that the method also works well under these conditions. A C K N O W L E D G M E N T A part of this work has been supported by the Federal Ministry of Education and Research of the Federal Repub- lic of Germany (BMBF) in the framew ork of the project 16KIS0267 HiFlecs. The authors would like to acknowledge the contributions of their colleagues, although the authors alone are responsible for the content of the paper which does not necessarily represent the project. R E F E R E N C E S [1] C. Bockelmann, A. Dekorsy , A. Gnad, L. Rauchhaupt, A. Neumann, D. Block, U. Meier , J. Rust, S. Paul, F . Mackenthun, A. W einand, H. Schotten, J. Siemons, T . Neugebauer , and M. Ehlich, “Hiflecs: Innov ative technologies for low-latency wireless closed- loop industrial automation systems, ” May 2017. [2] RFC 4493, The AES-CMAC Algorithm , 2006. [3] RFC 2104, HMAC: Ke yed-Hashing for Message Authentication , 1997. [4] N. C. Y . Osman, Y .-P . E. W ang, N. A. Johansson, N. Brahmi, S. A. Ashraf, and J. Sachs, “ Analysis of ultra-reliable and low-latency 5g communication for a factory automation use case, ” in IEEE International Confer ence on Communication workshop , 2015. [5] E. Jorswieck, S. T omasin, and A. Sezgin, “Broadcasting into the uncer- tainty: Authentication and confidentiality by physical-layer processing, ” Pr oceedings of the IEEE , vol. 103, no. 10, pp. 1702–1724, Oct 2015. [6] R. Guillaume, F . Winzer , A. Czylwik, C. T . Zenger , and C. Paar , “Bringing phy-based ke y generation into the field: An ev aluation for practical scenarios, ” in IEEE V ehicular T ec hnology Conference (VTC F all) , 2015. [7] C. T . Zenger, M.-J. Chur , J.-F . Posielek, C. Paar , and G. W under , “ A novel key generating architecture for wireless low-resource devices, ” in International W orkshop on Secure Internet of Things (SIoT) , 2014. [8] A. Ambekar , M. Hassan, and H. D. Schotten, “Improving channel reciprocity for effectiv e key management systems, ” in International Symposium on Signals, Systems and Electr onics (ISSSE), P otsdam, Germany , 2012. [9] L. Xiao, L. Greenstein, N. Mandayam and W . Trappe, “Fingerprints in the ether: Using the physical layer for wireless authentication, ” in IEEE International Conference on Communications (ICC) , 2007. [10] L. Xiao, L. Greenstein, N. Mandayam, and W . T rappe, “Using the physical layer for wireless authentication in time-variant channels, ” IEEE T ransactions on Wir eless Communications , vol. 7, no. 7, pp. 2571–2579, 2008. [11] C. Pei, N. Zhang, X. S. Shen, and J. W . Mark, “Channel-based physi- cal layer authentication, ” in IEEE Global Communications Conference (GLOBECOM) , 2014. [12] J. K. T ugnait and H. Kim, “ A channel-based hypothesis testing approach to enhance user authentication in wireless networks, ” in International Confer ence on COMmunication Systems and NET works (COMSNETS 2010) , 2010. [13] L. Shi, M. Li, S. Y u, and J. Y uan, “Bana: Body area network authen- tication exploiting channel characteristics, ” IEEE Journal on Selected Ar eas in Communications , vol. 31, no. 9, pp. 1803–1816, 2013. [14] A. Refaey , W . Hou, and K. Loukhaoukha, “Multilayer authentication for communication systems based on physical-layer attributes, ” Journal of Computer and Communications , vol. 2, no. 8, pp. 64–75, 2014. [15] N. Gulati, R. Greenstadt, K. R. Dandekar, and J. M. W alsh, “Gmm based semi-supervised learning for channel-based authentication scheme, ” in IEEE V ehicular T ec hnology Confer ence (VTC F all) , 2013. [16] P . Baracca, N. Laurenti, and S. T omasin, “Physical layer authentication over mimo fading wiretap channels, ” IEEE T ransactions on W ir eless Communications , vol. 11, no. 7, pp. 2564–2573, July 2012. [17] G. Caparra, M. Centenaro, N. Laurenti, S. T omasin, and L. V angelista, “Energy-based anchor node selection for iot physical layer authentica- tion, ” in 2016 IEEE International Confer ence on Communications (ICC) , May 2016, pp. 1–6. [18] T . M. Schmidl and D. C. Cox, “Robust frequency and timing synchro- nization for ofdm, ” IEEE T ransactions on Communications , vol. 45, no. 12, pp. 1613–1621, 1997. [19] A. W einand, A. Ambekar , M. Karrenbauer, and H. D. Schotten, “Pro- viding physical layer security for mission critical machine type com- munication, ” in 2016 IEEE 21st International Conference on Emerging T echnologies and F actory Automation (ETF A) , Sept 2016. [20] A. Ambekar and H. D. Schotten, “Enhancing channel reciprocity for effecti ve key management in wireless ad-hoc networks, ” in IEEE V ehic- ular T echnolo gy Conference (VTC Spring) , 2014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment