High Capacity, Secure (n, n/8) Multi Secret Image Sharing Scheme with Security Key
The rising need of secret image sharing with high security has led to much advancement in lucrative exchange of important images which contain vital and confidential information. Multi secret image sharing system (MSIS) is an efficient and robust method for transmitting one or more secret images securely. In recent research, n secret images are encrypted into n or n+ 1 shared images and stored in different database servers. The decoder has to receive all n or n+1 encrypted images to reproduce the secret image. One can recover partial secret information from n-1 or fewer shared images, which poses risk for the confidential information encrypted. In this proposed paper we developed a novel algorithm to increase the sharing capacity by using (n, n/8) multi-secret sharing scheme with increased security by generating a unique security key. A unrevealed comparison image is used to produce shares which makes the secret image invulnerable to the hackers
💡 Research Summary
The paper proposes a novel multi‑secret image sharing (MSIS) scheme that dramatically improves sharing capacity while adding an extra layer of security. Traditional (n, n) or (n, n + 1) visual cryptography methods require n shares to reconstruct n secret images, and even n − 1 shares may leak partial information. The authors introduce an (n, n/8) scheme: eight secret images are encoded into a single “meaningless” share, thus reducing the number of transmitted shares by a factor of eight.
The cornerstone of the design is a “comparison image” that is never sent together with the shares. From the first row of this image the algorithm extracts the remainders of each pixel value divided by 8, discarding duplicates until all eight distinct values (0‑7) are collected. These eight numbers, ordered as they appear, constitute a security key that determines the order in which the eight bit‑planes (MSB, LSB, etc.) of the comparison image are processed.
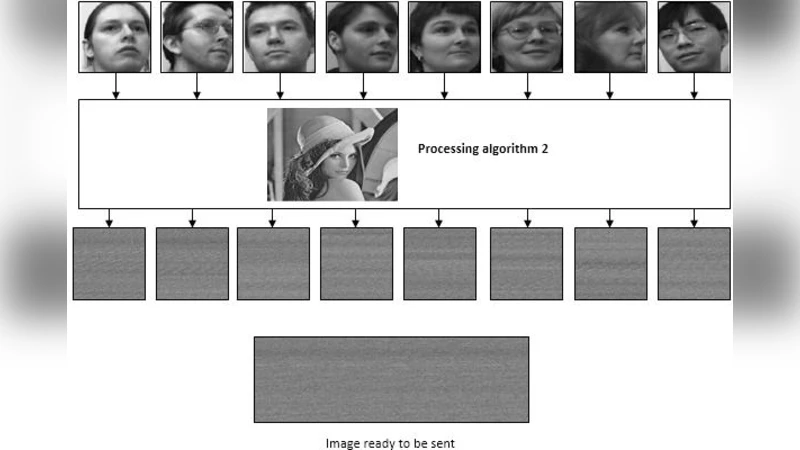
Encryption (Algorithm 2) proceeds as follows: the comparison image is bit‑sliced according to the key, each plane is linearised and concatenated into a matrix L₁. A secret image is also linearised into a binary stream L₂. After size‑matching (truncating or zero‑padding), L₁ and L₂ are XOR‑combined to produce L₃. L₃ is reshaped into an 8‑bit binary image I₃. Repeating this for eight secret images yields eight binary images; the eight bits at the same pixel location across these images are packed into a single 8‑bit gray‑scale pixel, forming the final share I₄. I₄ contains no perceptible information about any individual secret image.
Decryption (Algorithm 3) reverses the process. The receiver, who already knows the comparison image, regenerates the same security key (Algorithm 1). I₄ is decomposed into eight binary images, each is linearised to L₅, XOR‑ed with the key‑derived L₁ to obtain L₆, and finally reshaped back into the original secret images. Because the operations are purely XOR‑based and lossless, the recovered images are identical to the originals; experimental results report SSIM = 1.0, PSNR = ∞, RMSE = 0 for all eight images.
The authors evaluate the scheme on eight grayscale face images from the AT&T database, using “Lena.jpg” as the comparison image. They demonstrate an eight‑fold increase in sharing capacity compared with conventional (n, n) schemes, and claim that the separation of the comparison image (delivered via a secure out‑of‑band channel such as person‑to‑person communication) prevents any partial information leakage from the transmitted share alone.
A comparative table shows that the proposed method achieves: (i) sharing capacity 8 × higher, (ii) no pixel expansion, (iii) lossless recovery, (iv) increased randomness via a security key rather than simple reverse‑bit operations.
Despite these advantages, the approach has notable limitations. The security of the entire system hinges on the secrecy of the comparison image; if an adversary obtains it, the XOR key is revealed and all secrets become recoverable. The key generation relies only on the first row of the comparison image, making it vulnerable to any tampering of that row. The current implementation is demonstrated only for grayscale images; extending it to color images may require additional handling of three channels. The security analysis focuses on the absence of partial leakage but does not provide formal proofs against chosen‑plaintext or differential attacks. Moreover, performance metrics such as computational time, memory usage, and scalability to high‑resolution video streams are not reported, leaving open questions about real‑time applicability.
In summary, the paper contributes a high‑capacity (n, n/8) MSIS framework that leverages a comparison‑image‑derived security key to achieve lossless, eight‑fold compressed secret sharing. It offers a promising direction for secure bulk image or video transmission, provided that future work addresses key distribution robustness, color image support, comprehensive cryptographic security proofs, and performance optimization for practical deployment.
Comments & Academic Discussion
Loading comments...
Leave a Comment