Social Learning Against Data Falsification in Sensor Networks
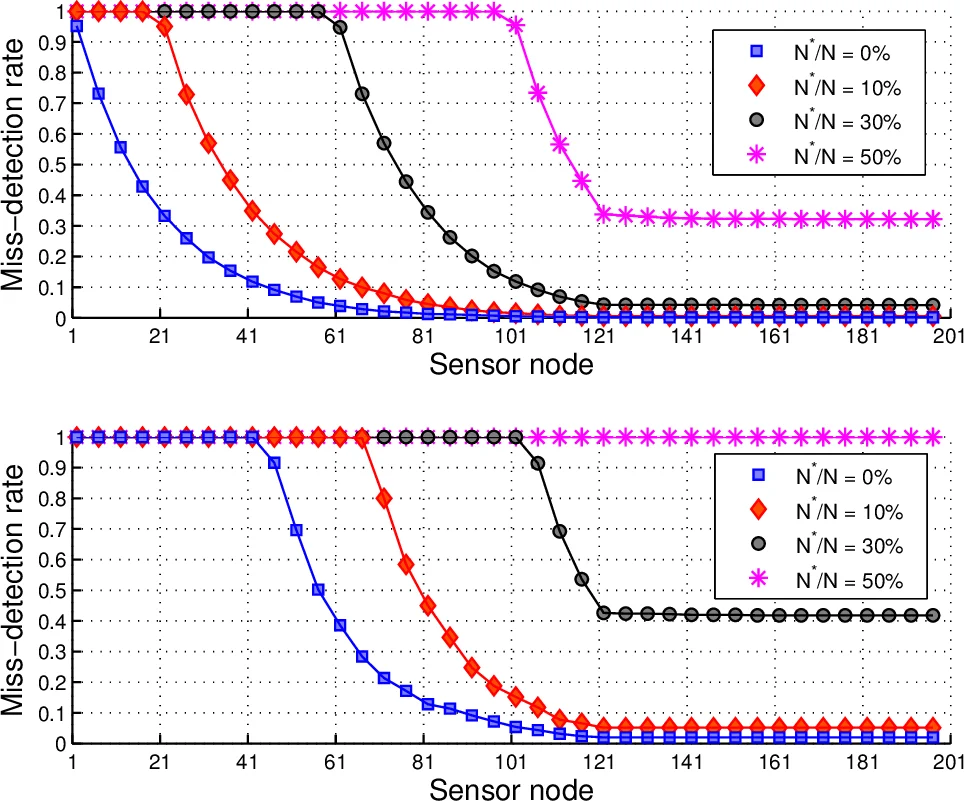
Although surveillance and sensor networks play a key role in Internet of Things, sensor nodes are usually vulnerable to tampering due to their widespread locations. In this letter we consider data falsification attacks where an smart attacker takes control of critical nodes within the network, including nodes serving as fusion centers. In order to face this critical security thread, we propose a data aggregation scheme based on social learning, resembling the way in which agents make decisions in social networks. Our results suggest that social learning enables network resilience, even when a significant portion of the nodes have been compromised by the attacker. Finally, we show the suitability of our scheme to sensor networks by developing a low-complexity algorithm to facilitate the social learning data fusion rule in devices with restricted computational power.
💡 Research Summary
The paper addresses a critical vulnerability in distributed sensor networks used for surveillance in the Internet of Things: data‑falsification (Byzantine) attacks in which an adversary gains control of a subset of sensor nodes, possibly including the fusion center (FC). Traditional detection schemes rely on a central FC that aggregates sensor reports; if the FC is compromised, the entire network’s inference capability collapses, creating a single point of failure. To overcome this limitation, the authors propose a novel data‑aggregation mechanism inspired by social learning, a concept from economics and sociology that describes how agents sequentially combine private observations with the decisions of earlier agents.
System model
- A network of N sensors each produces a measurement (S_n) (continuous or discrete) that is conditionally independent given the binary hypothesis (W\in{0,1}) (presence or absence of an attack).
- Each sensor broadcasts a single binary decision (X_n) after observing its own measurement and all previously broadcast decisions (X_{1},\dots,X_{n-1}).
- The decision rule is a function (\pi_n(S_n,X_{1:n-1})).
- An adversary controls (N^*) Byzantine nodes, knows the exact ordering of the sensors, and can set their transmitted bits arbitrarily. The attacker is topology‑aware and can target the most critical nodes (including the FC).
Social‑learning based fusion rule
The authors adopt a Bayesian decision rule for honest nodes:
\
Comments & Academic Discussion
Loading comments...
Leave a Comment