A Model for Enhancing Human Behaviour with Security Questions: A Theoretical Perspective
Security questions are one of the mechanisms used to recover passwords. Strong answers to security questions (i.e. high entropy) are hard for attackers to guess or obtain using social engineering techniques (e.g. monitoring of social networking profiles), but at the same time are difficult to remember. Instead, weak answers to security questions (i.e. low entropy) are easy to remember, which makes them more vulnerable to cyber-attacks. Convenience leads users to use the same answers to security questions on multiple accounts, which exposes these accounts to numerous cyber-threats. Hence, current security questions implementations rarely achieve the required security and memorability requirements. This research study is the first step in the development of a model which investigates the determinants that influence users’ behavioural intentions through motivation to select strong and memorable answers to security questions. This research also provides design recommendations for novel security questions mechanisms.
💡 Research Summary
The paper addresses the longstanding tension between security and memorability in password‑recovery security questions. Strong answers (high entropy) resist guessing and social‑engineering attacks but are hard for users to remember, leading many to adopt weak, low‑entropy answers or reuse the same answer across multiple services. This behavior dramatically expands attack surfaces. To remedy this, the authors develop a theoretical model that explains what motivates users to choose answers that are both strong and memorable.
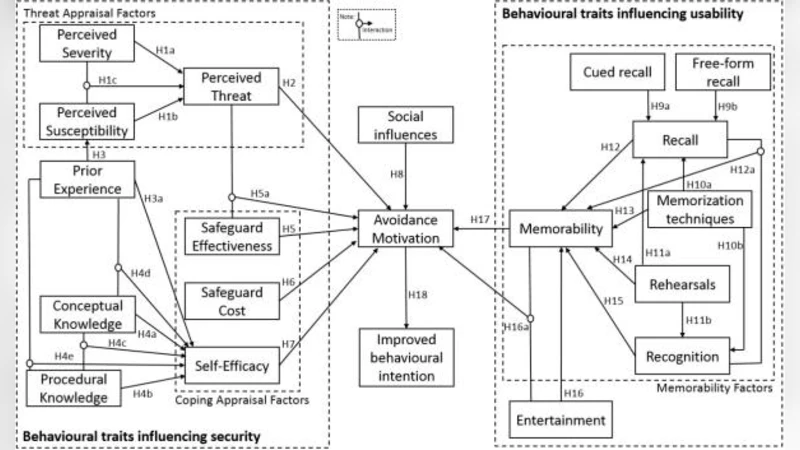
The model integrates Protection Motivation Theory (PMT) and the Technology Acceptance Model (TAM) and adds six contextual variables: perceived privacy risk, social norms, self‑efficacy, cognitive load, perceived usefulness, and cost perception (time/effort). Ten hypotheses are formulated, linking threat perception, vulnerability, response efficacy, and cost to the intention to select strong answers, while cognitive load and privacy concerns act as negative moderators.
Data were collected via an online questionnaire from 452 adult internet users. Items were adapted from validated scales and measured on a 7‑point Likert scale. Structural Equation Modeling (SEM) was used to test the hypotheses. Key findings include: (1) higher threat and vulnerability perception positively influence the intention to use strong answers; (2) cognitive load significantly reduces perceived usefulness, thereby lowering adoption intention; (3) privacy concerns deter strong answers, but this effect is mitigated by strong social norms and high self‑efficacy; (4) cost perception (time/effort) is the strongest negative predictor across the model; and (5) memorability (ease of recall) positively correlates with perceived usefulness, encouraging adoption of stronger answers when they are easy to remember.
Based on these results, the authors propose concrete design recommendations for future security‑question mechanisms:
- Multi‑stage questioning – present a simple initial query and reveal additional hints or follow‑up questions only after the user responds, spreading cognitive load across steps.
- Personalized question generation – use algorithms that mine a user’s own digital footprint (e.g., social‑media activity, calendar events, hobbies) to create context‑specific questions, reducing privacy anxiety while preserving answer uniqueness.
- Memory‑aid tools – associate answers with images, narratives, or mnemonic devices, allowing users to retain high‑entropy answers without sacrificing recall.
- Social‑norm interventions – run awareness campaigns that highlight the importance of strong answers and encourage peer endorsement, thereby boosting self‑efficacy and normative pressure.
- Cost‑reduction features – implement secure auto‑save and recovery aids that minimize the time and effort required to manage answers, lowering the perceived cost barrier.
In sum, the study offers the first comprehensive, theory‑driven examination of the determinants shaping users’ behavioral intentions regarding security‑question answers. By empirically validating a hybrid PMT‑TAM model and translating its insights into actionable design guidelines, the paper provides both academic and practical foundations for building security‑question systems that achieve a better balance between protection and usability.
Comments & Academic Discussion
Loading comments...
Leave a Comment