Taxonomy of Digital Forensics: Investigation Tools and Challenges
In today’s world of computers, any kind of information can be made available within few clicks for different endeavors. The information may be tampered by changing the statistical properties and can be further used for criminal activities. These days, Cyber crimes are happening at a very large scale, and possess big threats to the security of an individual, firm, industry and even to developed countries. To combat such crimes, law enforcement agencies and investment institutions are incorporating supportive examination policies, procedures and protocols to address the complete investigation process. The paper entails a detailed review of several cyber crimes followed by various digital forensics processes involved in the cyber crime investigation. Further various digital forensics tools with detail explanation are discussed with their advantages, disadvantages, challenges, and drawbacks. A comparison among all the selected tools is also presented. Finally the paper recommends the need of training programs for the first res ponder and judgement of signature based image authentication.
💡 Research Summary
The paper provides a comprehensive review of digital forensics in the context of today’s rapidly expanding cyber‑crime landscape. It begins by outlining the growing prevalence of various cyber offenses—including hacking, ransomware, phishing, distributed denial‑of‑service attacks, data theft, and AI‑generated forgeries—and explains how perpetrators manipulate statistical properties of data to conceal or falsify evidence. Recognizing the need for systematic investigative procedures, the authors describe how law‑enforcement agencies and financial institutions are adopting formal policies, protocols, and standard operating procedures to guide the entire forensic lifecycle.
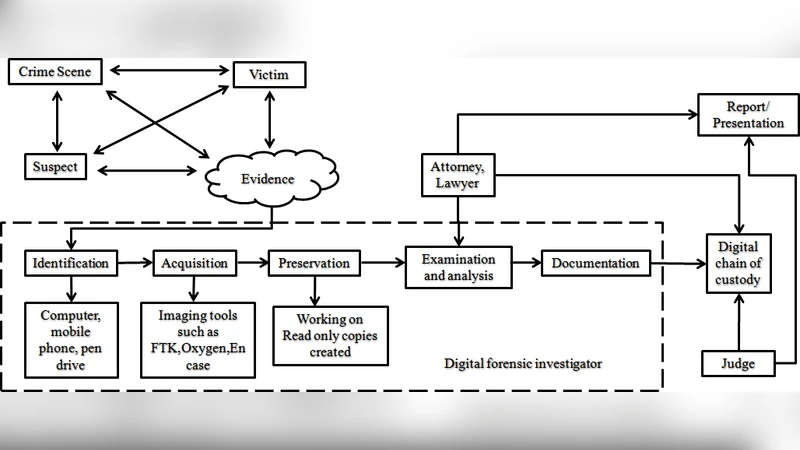
The core of the manuscript is a taxonomy that divides the forensic process into four distinct phases: evidence acquisition, preservation, analysis, and reporting. In the acquisition stage, the paper surveys both hardware‑based and software‑based tools for creating bit‑for‑bit disk images, memory dumps, network captures, and mobile device extractions. Commercial solutions such as FTK Imager and EnCase are compared with open‑source utilities like dd and Guymager, highlighting trade‑offs between user‑friendly interfaces, automation capabilities, licensing costs, and extensibility. Preservation is addressed through the use of cryptographic hash functions (SHA‑256, MD5) to guarantee data integrity and the maintenance of a chain‑of‑custody log that satisfies legal admissibility requirements.
The analysis phase receives the most detailed treatment. The authors enumerate the major forensic sub‑domains—file‑system reconstruction, registry parsing, log analysis, encrypted data recovery, volatile memory forensics, network traffic reconstruction, and mobile forensics—and map each sub‑domain to representative tools. For example, Autopsy and X‑Ways are discussed for disk‑level investigations, Volatility for RAM analysis, Wireshark for packet‑level inspection, and Cellebrite UFED or Oxygen Forensic Suite for smartphone data extraction. For each tool, the paper lists supported operating systems, file‑format coverage, scripting or plugin capabilities, reporting features, and known limitations such as poor support for newer file systems (APFS, ReFS), performance bottlenecks on large data sets, and the steep learning curve associated with advanced command‑line options.
A comparative matrix is presented that scores tools across criteria including cost, platform compatibility, forensic‑format support, automation level, community support, and availability of training resources. This matrix serves as a decision‑making aid for practitioners who must select the most appropriate solution based on case requirements, budget constraints, and organizational expertise.
Beyond technical considerations, the paper identifies several systemic challenges confronting digital forensics today. Technically, investigators struggle with evidence collection in cloud and virtualized environments, decryption of increasingly sophisticated encryption schemes, and authentication of AI‑generated media. From a human‑resource perspective, there is a shortage of skilled analysts, a lack of standardized curricula, and the continual need for up‑skilling as tools evolve. Legally and ethically, cross‑border evidence sharing, privacy protection, and the risk of evidence tampering demand robust governance frameworks.
To address these gaps, the authors propose a set of recommendations. First, they advocate the implementation of signature‑based image authentication mechanisms and automated integrity‑verification pipelines to provide rapid, reliable initial assessments of seized media. Second, they call for the development of formal training programs and certification pathways that target first responders and junior analysts, emphasizing hands‑on experience with both commercial and open‑source platforms. Third, they suggest fostering hybrid solutions that combine the stability of commercial products with the flexibility of open‑source modules, all aligned with international standards such as ISO/IEC 27037. Finally, they recommend ongoing research into forensic modules tailored for cloud services, containerized workloads, and emerging mobile operating systems.
In conclusion, the paper argues that while digital forensics tools have matured considerably, the dynamic nature of cyber threats, the diversification of data environments, and the scarcity of qualified personnel necessitate continuous tool evolution, standardized processes, and comprehensive education. By adopting the proposed strategies, the forensic community can improve the efficiency, reliability, and legal defensibility of investigations, thereby strengthening overall cyber‑security resilience.
Comments & Academic Discussion
Loading comments...
Leave a Comment