Mixed basis quantum key distribution with linear optics
Two-qubit quantum codes have been suggested to obtain better efficiency and higher loss tolerance in quantum key distribution. Here, we propose a two-qubit quantum key distribution protocol based on a mixed basis consisting of two Bell states and two states from the computational basis. All states can be generated from a single entangled photon pair resource by using local operations on only one auxiliary photon. Compared to other schemes it is also possible to deterministically discriminate all states using linear optics. Additionally, our protocol can be implemented with today’s technology. When discussing the security of our protocol we find a much improved resistance against certain attacks as compared to the standard BB84 protocol.
💡 Research Summary
**
The paper introduces a novel quantum key distribution (QKD) protocol that leverages a mixed basis composed of two Bell states (|Ψ⁻⟩ and |Ψ⁺⟩) and two computational‑basis product states (|HH⟩ and |VV⟩). The key idea is that all four orthogonal states can be generated from a single entangled photon pair source (producing |Ψ⁻⟩) by applying only local linear‑optical operations on the traveling photon. This eliminates the need for multiple entangled sources or nonlinear optical elements, dramatically simplifying the experimental setup.
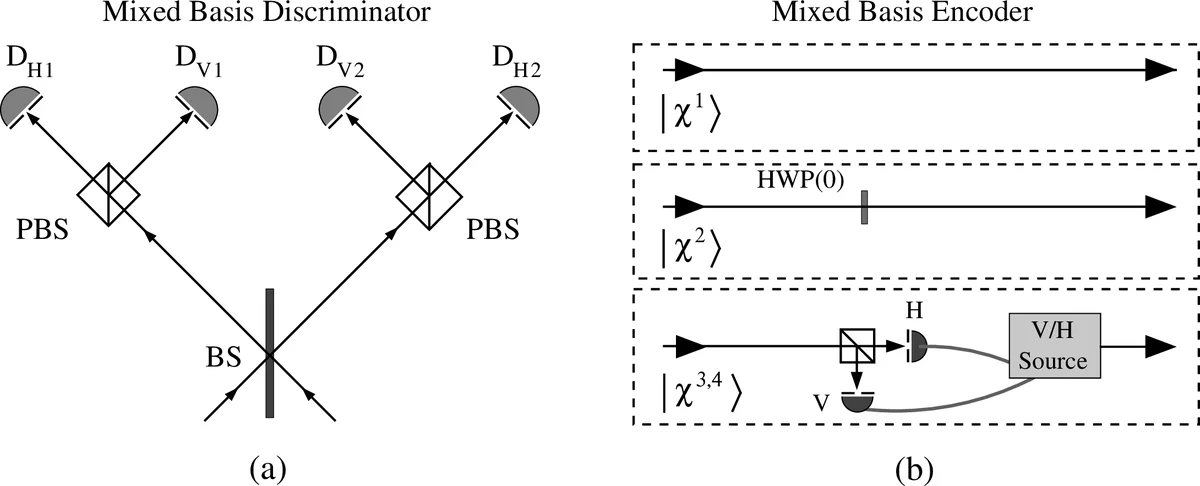
State preparation is achieved as follows: Bob generates the |Ψ⁻⟩ pair and sends one photon (the “travel photon”) to Alice while retaining the other (the “home photon”) in a quantum delay line. Alice, using a compact encoder that consists of a half‑wave plate, a polarizing beam splitter (PBS), and an auxiliary on‑demand single‑photon source, can transform the travel photon into any of the four mixed‑basis states. The Bell states are obtained deterministically by inserting or omitting a half‑wave plate that flips the vertical polarization. The product states |HH⟩ and |VV⟩ are generated in a heralded fashion: Alice measures the polarization of the incoming photon with a PBS, which projects Bob’s home photon into the opposite polarization; she then replaces the measured photon with a fresh auxiliary photon of the required polarization.
After encoding, Alice returns the photon to Bob. Bob combines the returned photon with his stored home photon in a mixed‑basis discriminator that uses only a non‑polarizing beam splitter (BS), two PBSs, and photon‑number‑resolving detectors (PNRDs). The discriminator exploits Hong‑Ou‑Mandel interference: identical‑polarization product states bunch at the BS and exit the same port, while the Bell states exhibit characteristic splitting patterns at the PBSs. Consequently, each of the four states produces a unique detection signature, allowing deterministic, unambiguous discrimination without any nonlinear optics.
The protocol proceeds in rounds. After each round, Alice and Bob announce over a classical channel whether they inserted their respective half‑wave plates (aligned to π/8, i.e., Hadamard gates). When both plates are present or both absent, they are said to be using the “same basis”; when only one plate is present, they are in “different bases.” The data obtained in different‑basis rounds serve as a control channel to estimate the quantum bit error rate (QBER) and to detect eavesdropping. If the QBER stays below the protocol’s tolerance threshold, the bits from same‑basis rounds are subjected to error correction and privacy amplification to produce the final secret key.
Security analysis shows several advantages over the standard BB84 protocol. First, the mixed basis increases the alphabet size from two to four symbols, raising the tolerable QBER from the BB84 limit (~11 %) to about 22.7 % (the theoretical limit for a four‑state protocol). Second, the protocol is robust against the Nguyen attack, a known vulnerability of the original “ping‑pong” direct‑communication scheme, because Eve cannot deterministically distinguish the Bell states without disturbing the system. The deterministic linear‑optical discrimination also prevents attacks that rely on measurement‑induced ambiguities. Moreover, the use of only linear optics makes the scheme less susceptible to implementation loopholes associated with nonlinear components.
Practical feasibility is emphasized. Current technology provides high‑efficiency superconducting nanowire single‑photon detectors (SNSPDs) and transition‑edge sensors capable of photon‑number resolution, as well as on‑demand single‑photon sources at telecom wavelengths. Simulations indicate that, even with realistic channel losses (e.g., 0.2 dB/km fiber attenuation), the protocol can generate secret keys over distances up to ~30 km with a key rate on the order of 10⁻³ bits per pulse. The requirement for only a single entangled photon source and a handful of passive linear components makes the scheme attractive for near‑term deployment in metropolitan quantum networks.
In summary, the authors present a QKD protocol that (1) uses a mixed Bell‑product basis to encode four orthogonal states, (2) generates all states from a single entangled pair via local linear optics, (3) discriminates the states deterministically with a simple BS‑PBS‑PNRD setup, (4) offers higher loss tolerance and stronger resistance to known attacks compared with BB84, and (5) can be realized with existing photonic technology. The work opens a pathway toward high‑capacity, robust quantum communication without the need for complex nonlinear optical hardware.
Comments & Academic Discussion
Loading comments...
Leave a Comment