Viden: Attacker Identification on In-Vehicle Networks
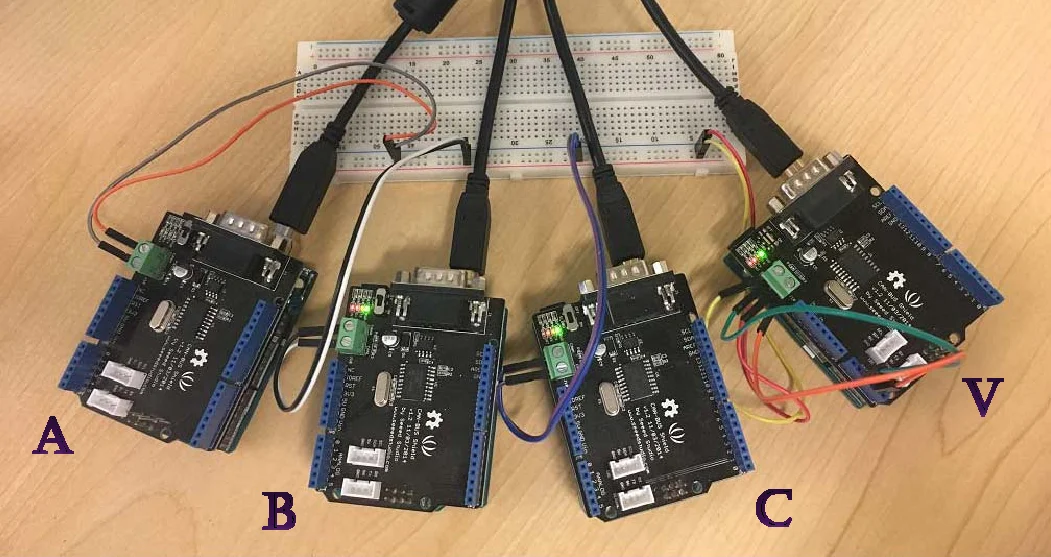
Various defense schemes — which determine the presence of an attack on the in-vehicle network — have recently been proposed. However, they fail to identify which Electronic Control Unit (ECU) actually mounted the attack. Clearly, pinpointing the attacker ECU is essential for fast/efficient forensic, isolation, security patch, etc. To meet this need, we propose a novel scheme, called Viden (Voltage-based attacker identification), which can identify the attacker ECU by measuring and utilizing voltages on the in-vehicle network. The first phase of Viden, called ACK learning, determines whether or not the measured voltage signals really originate from the genuine message transmitter. Viden then exploits the voltage measurements to construct and update the transmitter ECUs’ voltage profiles as their fingerprints. It finally uses the voltage profiles to identify the attacker ECU. Since Viden adapts its profiles to changes inside/outside of the vehicle, it can pinpoint the attacker ECU under various conditions. Moreover, its efficiency and design-compliance with modern in-vehicle network implementations make Viden practical and easily deployable. Our extensive experimental evaluations on both a CAN bus prototype and two real vehicles have shown that Viden can accurately fingerprint ECUs based solely on voltage measurements and thus identify the attacker ECU with a low false identification rate of 0.2%.
💡 Research Summary
The paper introduces Viden, a novel attacker‑identification framework for in‑vehicle networks, specifically targeting the Controller Area Network (CAN) bus. While many recent intrusion‑detection systems (IDS) can detect that an attack is occurring, they cannot pinpoint which Electronic Control Unit (ECU) is responsible. Viden fills this gap by exploiting subtle, hardware‑level voltage differences among ECUs.
System and Threat Model
The authors assume a vehicle equipped with a conventional IDS and a fingerprinting device (Viden). An adversary controls a previously installed ECU (remotely compromised) and injects malicious CAN frames. The threat model includes three adversary types: naïve (no knowledge of fingerprinting), timing‑aware (aware of clock‑skew based fingerprinting), and timing‑voltage‑aware (aware of both timing and voltage fingerprinting). The adversary may attempt arbitrary impersonation or targeted impersonation of another ECU to hide its identity.
Viden Architecture
Viden operates in four stages:
-
Voltage Sampling – Simultaneous measurement of CAN‑High (CANH) and CAN‑Low (CANL) lines at a modest 50 kSamples/s, far lower than prior high‑speed approaches.
-
ACK Learning – In a CAN frame, the ACK slot is driven by all ECUs except the transmitter. Viden learns an ACK voltage threshold and discards samples that fall below this level, ensuring that only the true transmitter’s voltage is used for fingerprinting.
-
Voltage Instances – After ACK filtering, each message ID yields a set of voltage features (mean, variance, min/max, etc.) called voltage instances.
-
Voltage Profiles (Fingerprints) – Voltage instances are fed into a Recursive Least Squares (RLS) adaptive filter. RLS updates each ECU’s voltage profile online, allowing the system to track gradual changes caused by temperature, battery voltage, aging, or intentional adversarial manipulation.
Key Advantages
- Message‑field agnostic: Viden does not rely on specific CAN IDs or payload fields, making it compatible with any CAN traffic.
- Low hardware cost: The modest sampling rate and lack of need for specialized high‑speed ADCs keep implementation inexpensive.
- Adaptability: Online RLS learning continuously refines fingerprints, unlike prior batch‑learning schemes that become stale when environmental conditions shift.
- Broad applicability: No assumptions about CAN bus speed (125 kbps–1 Mbps) or identifier format (11‑bit or 29‑bit) are required, facilitating deployment on legacy and future vehicles.
Experimental Evaluation
Viden was implemented on a laboratory CAN prototype and on two production vehicles. The authors collected voltage data from multiple ECUs under normal operation to build baseline profiles, then launched attacks where a compromised ECU injected malicious frames while attempting to masquerade as other ECUs. Results show:
- Distinct voltage profiles for each ECU, statistically separable even after long‑term operation.
- False identification rate (mis‑attributing the attacker) of only 0.2 % when evaluating over thousands of attack messages.
- Robustness against all three adversary types; even a timing‑voltage‑aware attacker who deliberately perturbs its output voltage could not evade detection because RLS quickly adapts and still distinguishes the anomalous pattern.
Comparison with Prior Work
Earlier fingerprinting methods relied on clock‑skew (e.g., CIDS) or high‑speed voltage sampling combined with batch‑trained classifiers (SVM). Those approaches suffer from (i) dependence on periodic message transmission, (ii) inability to handle dynamic environmental changes, and (iii) requirement for high‑speed hardware and specific CAN frame formats. Viden overcomes these limitations through ACK‑based filtering, low‑rate sampling, and online adaptive learning, achieving higher accuracy with far lower deployment cost.
Limitations and Future Directions
The current design focuses exclusively on CAN; extending the concept to other automotive buses such as FlexRay or Automotive Ethernet will require new voltage‑modeling techniques. Extreme temperature or voltage conditions may affect ADC precision, suggesting the need for further robustness testing. Finally, sophisticated adversaries could attempt to mimic the voltage profile of a target ECU; integrating statistical anomaly detection on the sequence of voltage instances could further harden the system.
Conclusion
Viden demonstrates that voltage‑based fingerprinting, when combined with ACK filtering and recursive adaptive learning, can reliably identify the exact ECU responsible for a malicious CAN transmission. The framework achieves a sub‑0.2 % false identification rate, operates with inexpensive hardware, and adapts to environmental variations, making it a practical complement to existing IDS solutions. By providing precise attacker attribution, Viden enables rapid forensic analysis, targeted ECU isolation, and efficient security patching, representing a significant step forward in automotive cyber‑security.
Comments & Academic Discussion
Loading comments...
Leave a Comment