Proof-Labeling Schemes: Broadcast, Unicast and In Between
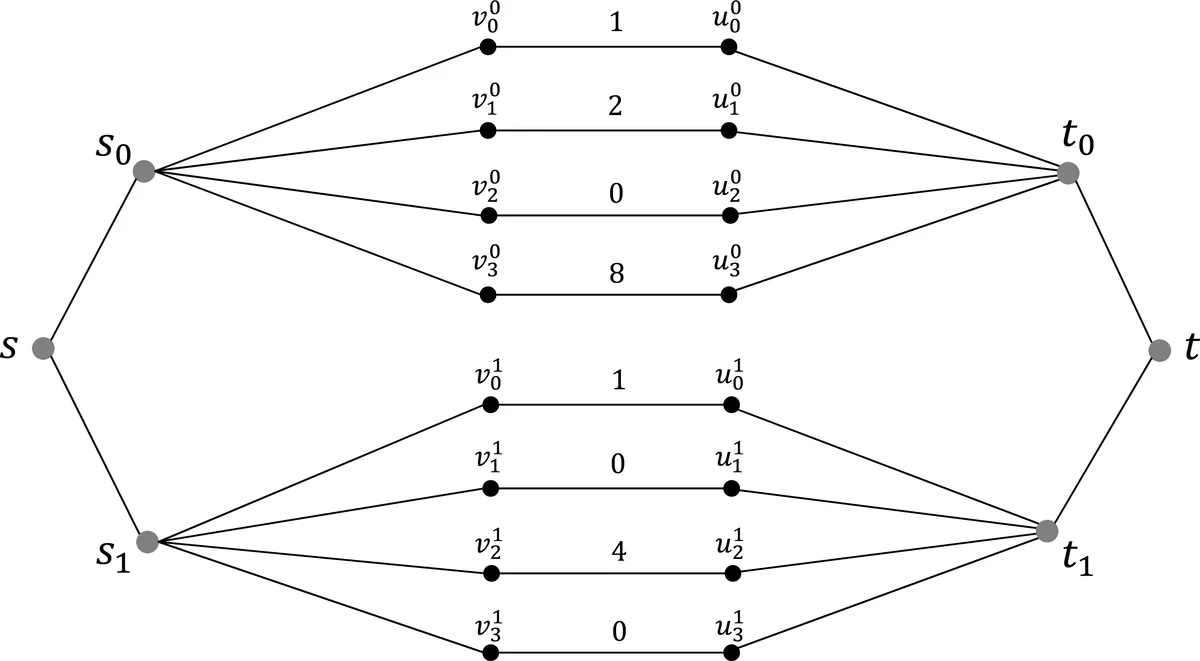
We study the effect of limiting the number of different messages a node can transmit simultaneously on the verification complexity of proof-labeling schemes (PLS). In a PLS, each node is given a label, and the goal is to verify, by exchanging messages over each link in each direction, that a certain global predicate is satisfied by the system configuration. We consider a single parameter r that bounds the number of distinct messages that can be sent concurrently by any node: in the case r=1, each node may only send the same message to all its neighbors (the broadcast model), in the case r is at least Delta, where Delta is the largest node degree in the system, each neighbor may be sent a distinct message (the unicast model), and in general, for r between 1 and Delta, each of the r messages is destined to a subset of the neighbors. We show that message compression linear in r is possible for verifying fundamental problems such as the agreement between edge endpoints on the edge state. Some problems, including verification of maximal matching, exhibit a large gap in complexity between r=1 and r>1. For some other important predicates, the verification complexity is insensitive to r, e.g., the question whether a subset of edges constitutes a spanning-tree. We also consider the congested clique model. We show that the crossing technique for proving lower bounds on the verification complexity can be applied in the case of congested clique only if r=1. Together with a new upper bound, this allows us to determine the verification complexity of MST in the broadcast clique. Finally, we establish a general connection between the deterministic and randomized verification complexity for any given number r.
💡 Research Summary
The paper investigates how limiting the number of distinct messages a node can send in a single round—captured by a single parameter r—affects the verification complexity of proof‑labeling schemes (PLS). In the classic CONGEST model a node may send a different message to each neighbor (unicast). The authors introduce the MCast(r) model, where each node may send at most r different messages per round. When r = 1 the model reduces to broadcast (all neighbors receive the same message); when r ≥ Δ (Δ being the maximum degree) it coincides with the unicast model; intermediate values interpolate between the two extremes. This abstraction reflects real‑world constraints such as a limited number of network interfaces.
Two fundamental building blocks are presented. First, a “minimizing orientation” technique orients edges so that the out‑degree of any node is at most 2·α(G), where α(G) is the arboricity of the graph. This orientation allows any edge‑centric predicate to be verified in MCast(2α) using only one distinct message per outgoing edge. Second, a “color addressing” method colors the graph with O(Δ²) colors so that each neighbor of a node receives a unique color; the color (encoded in O(log Δ) bits) replaces the neighbor’s identifier when bundling several sub‑messages, thereby keeping the overhead low.
Using these tools the authors derive tight upper and lower bounds for several canonical problems:
-
Edge Agreement (EA). Each incident edge carries a b‑bit string that must be identical at both endpoints. The authors prove κ(EA)·r = Θ(α(G)·b). Hence the verification message size κ scales inversely with r; increasing r compresses the certificates linearly.
-
Maximum Flow (MF). For a flow network the verification complexity satisfies κ(MF)·r = Θ(α(G)·log f_max), where f_max is the largest flow value on any edge. Again, the product of message size and r is governed by arboricity.
-
Maximal Matching Verification (MV). In the broadcast setting (r = 1) the authors show a lower bound of Θ(log Δ) bits, while with just r = 2 the complexity drops to O(1) bits. This demonstrates a dramatic gap: a small increase in r can yield exponential savings for matching verification.
-
Spanning‑Tree and Vertex‑Biconnectivity. These structural predicates are shown to be insensitive to r; both deterministic and randomized schemes require only Θ(log n) bits regardless of the number of distinct messages allowed.
The paper also examines the congested clique. It proves that the classic “crossing” lower‑bound technique applies only in the broadcast clique (r = 1). Combining this with a new upper‑bound construction, the authors obtain a tight Θ(log n + log w_max) bound for MST verification in the broadcast clique, where w_max is the maximum edge weight. This resolves the previously open question of lower bounds for verification in the clique model.
Finally, the authors extend the deterministic–randomized relationship to any fixed r. They show that from a deterministic PLS with verification complexity κ_d one can build a randomized PLS with complexity O(log κ_d), and conversely a randomized PLS with complexity κ_r yields a deterministic scheme of size O(2^{κ_r}). Thus, for a given r, randomization can provide an exponential reduction in certificate size.
Overall, the work provides a systematic analysis of how a single communication‑budget parameter r interacts with graph‑structural parameters (arboricity, degree, flow magnitude) to determine the optimal verification complexity of a wide range of distributed predicates. The results give both theoretical insight and practical guidance for designing efficient verification protocols in networks where the number of simultaneous distinct messages is inherently limited.
Comments & Academic Discussion
Loading comments...
Leave a Comment