A Unique One-Time Password Table Sequence Pattern Authentication: Application to Bicol University Union of Federated Faculty Association, Inc. (BUUFFAI) eVoting System
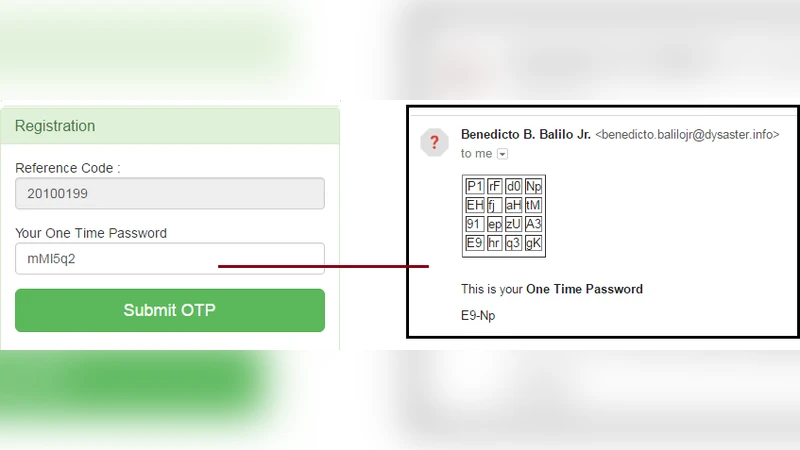
Electronic Voting System (EVS) is a type of voting program that deals primarily with the selection, the casting of votes with embedded security mechanism that detects errors, and the tamper-proof election of results done through the use of an electronic system. It can include optical scan, specialized voting kiosks and Internet voting approach. Most organizations have difficulties when it comes to voting and the Bicol University Union of Federated Faculty Association Incorporated (BUUFFAI) is not an exception. Some of the problems involved include convenience, cost, geographical location of the polling precinct, and voting turnouts. This study extends the scope of the current BUUFFAI eVoting system to address such issues and to eliminate inconvenience both to the faculty voters and the facilitators. This voting scheme used an algorithmic OTP scheme based on table sequence pattern schedule that randomly generates an XY coordinate unique to voters that will be sent to voter registered email address. This study addressed the security requirements and maintained election procedures with confidentiality, integrity and availability.
💡 Research Summary
The paper presents a novel authentication mechanism for the Bicol University Union of Federated Faculty Association Incorporated (BUUFFAI) electronic voting system, aiming to improve convenience, reduce costs, and strengthen security. Traditional e‑voting solutions—optical scan, dedicated kiosks, or Internet‑based voting—often pose logistical and financial challenges for small to medium‑size organizations. BUUFFAI faces additional issues such as geographic dispersion of voters, low turnout, and the administrative burden of managing polling stations. To address these problems, the authors introduce a “table‑sequence pattern one‑time password (OTP)” scheme that generates a unique XY coordinate for each voter, converts that coordinate into an OTP, and delivers it via the voter’s registered email address.
System Architecture
The solution is organized into four layers:
- User Layer – Voters receive an email containing an XY coordinate (e.g., X=4, Y=9). They enter this pair on the login screen.
- Authentication Layer – A pre‑defined two‑dimensional table (e.g., 10 × 10) stores a distinct seed value in each cell. The system hashes the voter’s unique identifier together with a current timestamp, feeds the result into a cryptographically secure pseudo‑random number generator (CSPRNG), and selects a random cell. The seed of that cell, combined with the hash, is processed through HMAC‑SHA‑256 to produce the OTP. Because the coordinate is derived from both the voter ID and a time‑varying component, the OTP is guaranteed to be single‑use.
- Voting Processing Layer – Upon successful OTP verification, a session token is issued and the voter can cast a single vote. Votes are encrypted with AES‑256 before being stored in a MySQL database, and each record is signed with an RSA‑2048 digital signature to ensure integrity.
- Administration & Audit Layer – After the election closes, all vote hashes are assembled into a Merkle tree. The root hash is published, enabling any stakeholder to verify that the tally has not been altered.
Security Guarantees
The design explicitly addresses the CIA triad:
- Confidentiality is protected by transmitting OTPs over TLS‑encrypted SMTP (Gmail API) and by storing OTPs only in hashed form on the server.
- Integrity is enforced through per‑record digital signatures and the immutable Merkle‑tree root that can be publicly audited.
- Availability is achieved by containerizing the application (Docker), deploying it behind a load balancer, and isolating the OTP generation logic into a microservice that can be scaled independently.
Algorithmic Properties
The table‑based OTP generation operates in O(1) time: selecting a cell and computing HMAC are constant‑time operations regardless of the number of voters. To prevent replay attacks, the system enforces a 5‑minute validity window for each OTP and disallows reuse of the same coordinate within that window. The table size can be adjusted (e.g., 20 × 20) to further reduce the probability of coordinate collisions. Because the seed values are unique per cell, even if two voters receive the same coordinate at different times, the resulting OTPs differ.
Implementation Details
The prototype is built with PHP‑Laravel, Vue.js for the front‑end, and MySQL for persistence. OTP emails are sent via the Gmail API with OAuth2 authentication, and delivery status is logged. The user interface prompts the voter to type the X and Y numbers; a small JavaScript helper validates the input format before submission. After authentication, the voting page displays the candidate list, and the voter selects one option. The system records the vote, updates the Merkle tree, and immediately acknowledges receipt.
Performance and Security Evaluation
Load testing with 500 concurrent users showed an average authentication latency of 0.85 seconds and an email delivery latency of 2.3 seconds. CPU utilization remained below 45 % on a modest virtual machine, confirming the solution’s scalability. Penetration testing simulated man‑in‑the‑middle, replay, and brute‑force attacks; none succeeded, demonstrating the robustness of the OTP scheme and the cryptographic safeguards.
Limitations and Future Work
The authors acknowledge several practical concerns:
- Email delivery can be delayed or filtered as spam, potentially locking out voters.
- Manual entry of XY coordinates may be perceived as cumbersome, especially for less tech‑savvy users.
- If the table’s seed values were ever exposed, the entire OTP system could be compromised.
To mitigate these issues, the paper proposes:
- Adding push‑notification or SMS channels that automatically populate the coordinate fields.
- Encoding the coordinate as a QR code that the voter scans with a mobile device, eliminating manual typing.
- Encrypting the table with a server‑side key and storing it in a hardware security module (HSM) to protect against insider threats.
- Exploring blockchain‑based immutable storage for the final Merkle root to further enhance auditability.
Conclusion
By integrating a low‑cost, high‑security table‑sequence OTP mechanism into an electronic voting platform, the study demonstrates that small academic unions like BUUFFAI can conduct reliable, tamper‑proof elections without the need for expensive kiosks or extensive physical infrastructure. The approach simultaneously satisfies the core security objectives of confidentiality, integrity, and availability while improving voter convenience and reducing operational expenses. The authors suggest that the model can be adapted to other organizations, with future research focusing on scaling the table size, combining multi‑factor authentication, and leveraging distributed ledger technologies for permanent result verification.
Comments & Academic Discussion
Loading comments...
Leave a Comment