Cloud computing has been regarded as the technology enabler for the Internet of Things (IoT). To ensure the most effective collection of IoT-based evidence, it is vital for forensic practitioners to possess a contemporary understanding of the artefacts from different cloud services. In this paper, we seek to determine the data remnants from the use of BitTorrent Sync version 2.0. Findings from our research using mobile and computer devices running Windows 8.1, Mac OS X Mavericks 10.9.5, Ubuntu 14.04.1 LTS, iOS 7.1.2, and Android KitKat 4.4.4 suggested that artefacts relating to the installation, uninstallation, log-in, log-off, and file synchronisation could be recovered, which are potential sources of IoT forensics. We also present a forensically sound investigation methodology for BitTorrent Sync.
Deep Dive into Forensic Investigation of P2P Cloud Storage: BitTorrent Sync as a Case Study.
Cloud computing has been regarded as the technology enabler for the Internet of Things (IoT). To ensure the most effective collection of IoT-based evidence, it is vital for forensic practitioners to possess a contemporary understanding of the artefacts from different cloud services. In this paper, we seek to determine the data remnants from the use of BitTorrent Sync version 2.0. Findings from our research using mobile and computer devices running Windows 8.1, Mac OS X Mavericks 10.9.5, Ubuntu 14.04.1 LTS, iOS 7.1.2, and Android KitKat 4.4.4 suggested that artefacts relating to the installation, uninstallation, log-in, log-off, and file synchronisation could be recovered, which are potential sources of IoT forensics. We also present a forensically sound investigation methodology for BitTorrent Sync.
Note: This is authors accepted copy – for final article please refer to : Teing, Y.-Y., Ali, D., Choo, K.-K. R., &
Yang, M. (2016). Forensic investigation of P2P cloud storage services and backbone for IoT networks: BitTorrent
Sync as a case study. Computers and Electrical Engineering, (2016).
http://doi.org/http://dx.doi.org/10.1016/j.compeleceng.2016.08.020
Forensic Investigation of P2P Cloud Storage: BitTorrent Sync as a Case Study
Teing Yee Yang1, Ali Dehghantanha2, Kim-Kwang Raymond Choo3, Zaiton Muda1
1 Department of Computer Science, Faculty of Computer Science and Information Technology, Universiti Putra
Malaysia, UPM Serdang, Selangor, Malaysia
2 The School of Computing, Science & Engineering, Newton Building, University of Salford, Salford, Greater
Manchester, United Kingdom
3 Information Assurance Research Group, University of South Australia, Adelaide, South Australia, Australia.
Abstract
Cloud computing has been regarded as the technology enabler for the Internet of Things (IoT). To ensure the most
effective collection of IoT-based evidence, it is vital for forensic practitioners to possess a contemporary
understanding of the artefacts from different cloud services. In this paper, we seek to determine the data remnants
from the use of BitTorrent Sync version 2.0. Findings from our research using mobile and computer devices running
Windows 8.1, Mac OS X Mavericks 10.9.5, Ubuntu 14.04.1 LTS, iOS 7.1.2, and Android KitKat 4.4.4 suggested
that artefacts relating to the installation, uninstallation, log-in, log-off, and file synchronisation could be recovered,
which are potential sources of IoT forensics. We also present a forensically sound investigation methodology for
BitTorrent Sync.
Keywords: Internet of Things Forensics; Cloud Forensics; P2P Cloud Investigation; Computer Forensics; Mobile
Forensics; Bittorrent.
Introduction
The Internet of things (IoT) has been the focus of researchers and practitioners in recent years, due to the
increasing popularity of internet connected devices. Gartner (2014a) forecasted the number of IoT devices to reach
26 billion by 2019. Similarly, the International Data Corporation (IDC) (2014) predicted that the IoT devices to hit
30 billion by 2020, amounting to USD3.04 trillion. Since the IoT devices are equipped with low storage and
computational capability (Zawoad, 2015), the IDC (2014a) predicted that 90% of all IoT data will be hosted on
cloud service provider platforms by 2019 as cloud computing reduces the complexity of supporting IoT data
blending.
Although cloud computing is often being credited for enabling promising and cost-competitive storage
solutions for the IoT, it is subject to potential abuse by both traditional and cyber miscreants in the meantime (Choo,
2008). Potential crimes related to cloud computing include information theft (Choo, 2010; Symantec, 2011; Duke,
2014), malicious software distribution (Shado, 2014), denial of service attacks (DDoS) (Lemos, 2010; Peterson,
2013), industrial espionage, copyright infringement, and storage of illegal materials (e.g. child exploitation
materials, and terrorism materials).
Since a public cloud storage infrastructure may constitute cloud servers located in one or more data centers
and jurisdictions, the forensic community is often subject to various legal challenges (Taylor et al., 2011; Chung et
al 2012; Grispos, Storer, and Glisson, 2013; Hooper, Martini, and Choo, 2013; NIST, 2014; Quick et al., 2014a;
Martini and Choo 2014a). Even in the event that the evidence could be identified, it would not be trivial to seize the
storage media (server) as it is likely to hold data belonging to other users (e.g. in a multi-tenancy cloud environment)
(ENISA, 2012).
Due to the rapid advancement of the IoT, it is imperative that forensic examiners are cognisant of the
different types of cloud products as well as an up-to-date understanding of the potential artefacts that could
potentially be recovered to inform the IoT investigations (Hale, 2013; Quick and Choo, 2013a, 2013b, 2014; Martini
and Choo, 2014c; Quick et al., 2014). Depending on the cloud storage solution in use, the client device can often
provide potential for alternative methods for recovery of the cloud artefacts (Farina et al., 2014; Scanlon et al.,
2014a; Scanlon et al., 2014b; Scanlon et al., 2015). Hence, in this paper, we seek to identify potential terrestrial
artefacts that may remain after the use of the newer BitTorrent Sync version 2.0. Similar to the approaches of Quick
and Choo (2013a, 2013b, 2014), we attempt to answer the following questions in this research:
1.
Does the act of file download or file upload using BitTorrent Sync cloud storage alter the file contents and
timestamps of the original files?
2.
What data can be found on a computer hard drive and memory after a user has used the BitTorrent Sync
client application and web application, and the loc
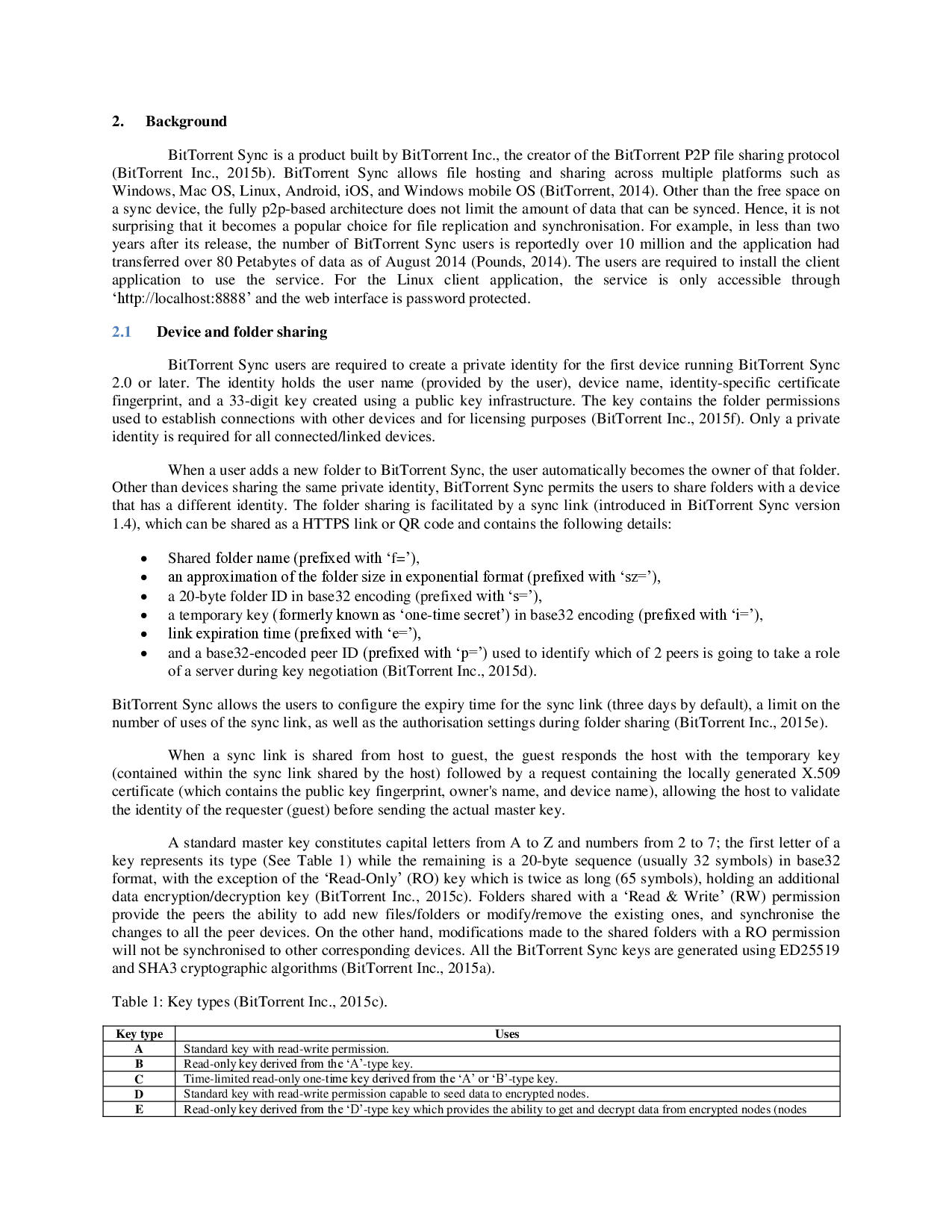
…(Full text truncated)…
This content is AI-processed based on ArXiv data.