A secure approach for embedding message text on an elliptic curve defined over prime fields, and building EC-RSA-ELGamal Cryptographic System
This paper presents a new probabilistic approach to embedding message text on an elliptic curve, by using the concept of the RSA Algorithm and its security, and such approach allows us discovering the message from the point, only according to the security of the RSA Algorithm. By mixing between the concept of this approach and the concept of EC-ELGamal Cryptographic System, we have built a cryptographic System and we named it ‘EC-RSA-ELGamal’
💡 Research Summary
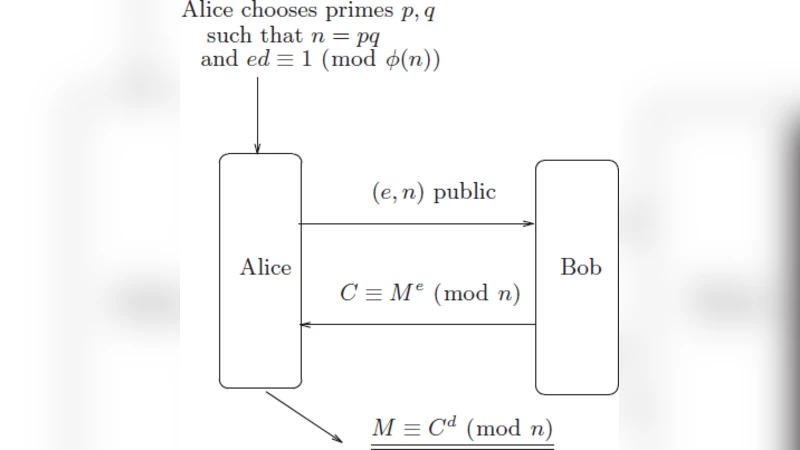
The paper proposes a novel cryptographic construction called “EC‑RSA‑ElGamal” that combines the security of RSA with that of elliptic‑curve ElGamal. The authors begin by reviewing the fundamentals of symmetric and asymmetric cryptography, emphasizing that RSA’s security rests on the Integer Factorization Problem (IFP) while elliptic‑curve cryptosystems rely on the Elliptic Curve Discrete Logarithm Problem (ECDLP). They then present the algebraic definition of an elliptic curve over a prime field p, together with the group law (point addition and doubling) that underpins all elliptic‑curve operations.
The paper critiques the classic Koblitz‑style “message‑to‑point” mapping, which simply searches for an x‑coordinate of the form x = M·K + j that satisfies the curve equation. Although this method easily produces a point, it also makes the reverse mapping (point → message) trivial, which the authors deem insecure. To address this, they introduce a probabilistic embedding that incorporates RSA encryption. The embedding proceeds as follows:
- Choose two distinct primes q and r and compute the RSA modulus n = q·r.
- Generate an RSA key pair (e, n) and d such that e·d ≡ 1 (mod φ(n)).
- Encrypt the plaintext integer M with the RSA public exponent: x = M^e (mod n).
- Test whether this x is a valid x‑coordinate on the chosen elliptic curve y² = x³ + ax + b (mod p). If it is, compute the corresponding y (e.g., via a modular square‑root algorithm) and obtain the point P = (x, y). If not, select a different RSA exponent or a different pair (q, r) and repeat.
Decryption requires the RSA private exponent d. The receiver extracts the x‑coordinate from the transmitted point, computes M = x^d (mod n), and thus recovers the original message. Because the mapping depends on the secret RSA exponent, an adversary who only sees the point cannot recover M without solving either the RSA problem (i.e., factoring n) or the elliptic‑curve problem (finding a valid x‑coordinate). Consequently, the scheme’s security is claimed to rest on both IFP and ECDLP.
The authors then embed this RSA‑based embedding into the standard EC‑ElGamal encryption framework. In the combined system, the RSA‑derived point P acts as the plaintext point for EC‑ElGamal. The sender selects a random scalar k, computes the usual ElGamal ciphertext pair (C1 = k·G, C2 = P + k·Y) where G is a base point and Y = a·G is the receiver’s public key, and transmits (C1, C2). The receiver first performs the usual EC‑ElGamal decryption to recover P, then applies the RSA private exponent to the x‑coordinate of P to obtain M.
Two numerical examples illustrate the process. In the first, the curve y² = x³ + 71x + 602 over p = 1009 is used, with RSA parameters q = 23, r = 43, n = 989, e = 5. The plaintext M = 439 produces x = 354, which is a valid curve coordinate, yielding the point (354, 88). Decryption with d = 185 recovers M. The second example repeats the same embedding but adds the EC‑ElGamal layer, showing the full ciphertext point Q and the subsequent recovery of M through both elliptic‑curve and RSA operations.
In the discussion, the authors acknowledge several practical limitations. The RSA modulus n must be at least 1024 bits for contemporary security, which forces p to be comparably large if the condition M < n < p is to hold. However, efficient elliptic‑curve operations typically use much smaller primes (e.g., 256‑384 bits). This mismatch leads to high computational cost and large key sizes. Moreover, the probabilistic embedding succeeds with probability at most ½ per RSA trial, potentially requiring many repetitions. The scheme also relies on secure distribution of the RSA private exponent, effectively re‑introducing the key‑management challenges of RSA into an elliptic‑curve setting. Finally, the paper provides no formal security proof, no analysis of side‑channel or chosen‑ciphertext attacks, and no discussion of point‑collision issues (different messages mapping to the same x‑coordinate).
The authors conclude that while the idea of combining two hard problems is conceptually appealing, substantial work remains to make the construction practical. Future research directions include optimizing parameter selection to decouple n and p, improving the embedding efficiency (e.g., using deterministic hash‑to‑curve methods), and providing a rigorous security reduction that quantifies the combined hardness of IFP and ECDLP.
Comments & Academic Discussion
Loading comments...
Leave a Comment