Forensic Investigation of P2P Cloud Storage: BitTorrent Sync as a Case Study
Cloud computing has been regarded as the technology enabler for the Internet of Things (IoT). To ensure the most effective collection of IoT-based evidence, it is vital for forensic practitioners to possess a contemporary understanding of the artefacts from different cloud services. In this paper, we seek to determine the data remnants from the use of BitTorrent Sync version 2.0. Findings from our research using mobile and computer devices running Windows 8.1, Mac OS X Mavericks 10.9.5, Ubuntu 14.04.1 LTS, iOS 7.1.2, and Android KitKat 4.4.4 suggested that artefacts relating to the installation, uninstallation, log-in, log-off, and file synchronisation could be recovered, which are potential sources of IoT forensics. We also present a forensically sound investigation methodology for BitTorrent Sync.
💡 Research Summary
The paper addresses a growing gap in digital forensics concerning peer‑to‑peer (P2P) cloud storage services, using BitTorrent Sync (BTS) version 2.0 as a representative case. While most existing forensic research focuses on centralized cloud platforms that retain server‑side logs, P2P solutions lack a single authoritative data source, making evidence collection challenging. To bridge this gap, the authors designed a comprehensive experimental framework that spans five operating systems: Windows 8.1, macOS Mavericks 10.9.5, Ubuntu 14.04.1 LTS, iOS 7.1.2, and Android KitKat 4.4.4. For each platform, they performed a controlled sequence of actions—installation, initial configuration, multiple file‑synchronisation scenarios, repeated login and logout, and final uninstallation—while capturing full disk images, volatile memory dumps, and network traffic.
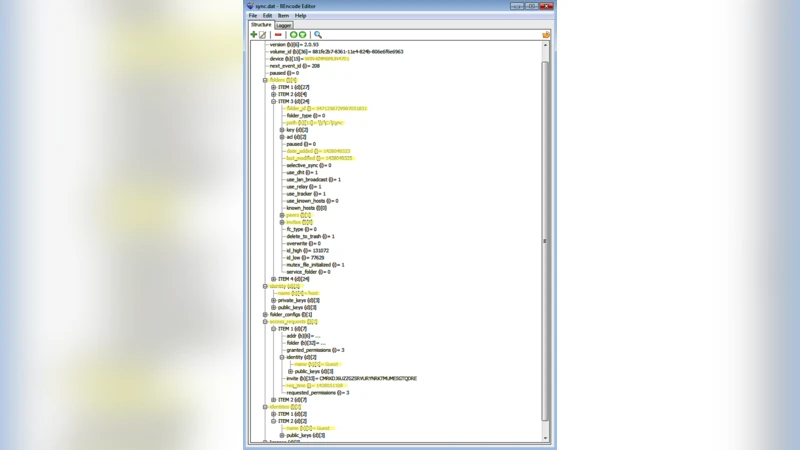
Data acquisition employed industry‑standard tools such as FTK Imager for disk imaging, Volatility for memory analysis, and Cellebrite UFED together with Android Debug Bridge for mobile devices. The authors then parsed a variety of artefacts: Windows registry keys (e.g., HKEY_CURRENT_USER\Software\BitTorrent Sync), application‑specific directories (%ProgramFiles% and %AppData% paths), macOS property‑list files, Linux configuration folders, SQLite databases on Android, and iOS Keychain entries. Log files—sync.log, sync_debug.log, and platform‑specific system logs—were examined for timestamps, peer identifiers, error codes, and file‑transfer metadata.
Key findings reveal that BTS leaves a rich trail across all examined platforms. On Windows, installation creates registry entries, a program folder, and a roaming AppData directory containing configuration files and detailed sync logs. macOS stores equivalent data under ~/Library/Application Support/BitTorrent Sync and records additional Spotlight indexing information. Ubuntu’s ~/.config/BitTorrent Sync directory and syslog entries capture similar artefacts, while package‑manager logs provide a reliable record of installation and removal events. Mobile devices are not exempt: iOS retains a sync.db SQLite database, log files, and authentication tokens in the Keychain; Android keeps shared preferences, a database of shared folder metadata, and logcat entries that expose service start/stop events. Importantly, even after uninstallation, remnants persist in file‑system journals (e.g., $MFT, $LogFile on NTFS, inode journals on ext4) and in deleted‑file shadows, allowing forensic reconstruction of prior BTS activity.
Based on these observations, the authors propose a structured “IoT‑focused BitTorrent Sync investigation methodology.” The workflow consists of six stages: (1) acquisition of disk, memory, and network captures; (2) file‑system metadata analysis to build a timeline of file creation, modification, and deletion; (3) extraction of registry, plist, and SharedPreferences data to uncover configuration and authentication details; (4) parsing of log files and SQLite databases for synchronisation events and peer communication; (5) reconstruction of network traffic, focusing on BTS’s default ports (3000‑3005) and DHT traffic to identify peer IPs and transferred file hashes; and (6) integration of all artefacts into a coherent, court‑admissible timeline with a maintained chain of custody. This methodology is deliberately platform‑agnostic, enabling investigators to apply it to any P2P cloud storage solution where central logs are unavailable.
The paper concludes by emphasizing that P2P cloud services, despite their decentralized nature, generate abundant forensic artefacts throughout their lifecycle—installation, login, synchronisation, and removal. By systematically collecting and analysing these artefacts, investigators can obtain reliable evidence suitable for legal proceedings. The authors also outline future research directions, including comparative studies of other P2P sync tools (e.g., Resilio Sync, Syncthing), techniques for decrypting encrypted synchronisation payloads, and the development of automated, real‑time network‑monitoring tools to capture P2P traffic as it occurs. Overall, this work provides a foundational reference for forensic practitioners confronting the challenges posed by emerging IoT‑centric, peer‑to‑peer cloud storage environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment