HyBIS: Windows Guest Protection through Advanced Memory Introspection
Effectively protecting the Windows OS is a challenging task, since most implementation details are not publicly known. Windows has always been the main target of malwares that have exploited numerous bugs and vulnerabilities. Recent trusted boot and additional integrity checks have rendered the Windows OS less vulnerable to kernel-level rootkits. Nevertheless, guest Windows Virtual Machines are becoming an increasingly interesting attack target. In this work we introduce and analyze a novel Hypervisor-Based Introspection System (HyBIS) we developed for protecting Windows OSes from malware and rootkits. The HyBIS architecture is motivated and detailed, while targeted experimental results show its effectiveness. Comparison with related work highlights main HyBIS advantages such as: effective semantic introspection, support for 64-bit architectures and for latest Windows (8.x and 10), advanced malware disabling capabilities. We believe the research effort reported here will pave the way to further advances in the security of Windows OSes.
💡 Research Summary
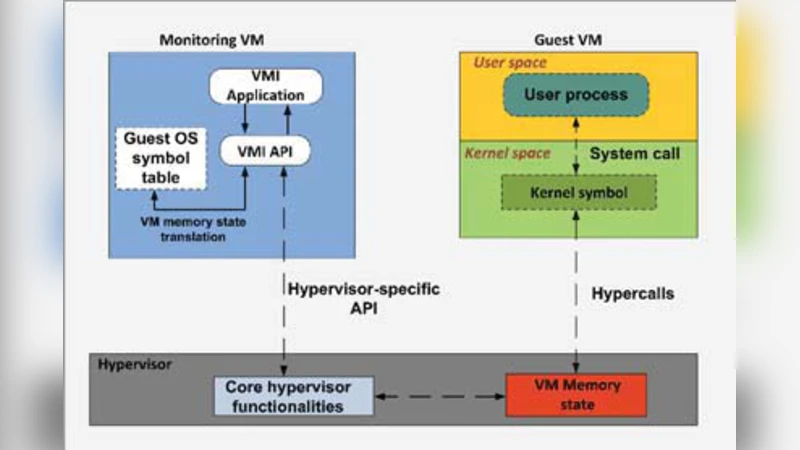
The paper introduces HyBIS, a hypervisor‑based memory introspection system designed to protect Windows guest operating systems running inside virtual machines. The authors begin by highlighting the persistent difficulty of defending Windows platforms: while trusted boot and kernel integrity checks have reduced the feasibility of kernel‑level rootkits on bare‑metal installations, virtualized Windows instances remain attractive targets because the hypervisor can be leveraged to gain deep visibility into the guest’s memory. Existing virtual machine introspection (VMI) solutions either focus on 32‑bit systems, lack support for recent Windows releases, or rely on simple signature‑based scanning that yields high false‑positive rates.
HyBIS addresses these gaps through three tightly integrated components. The Memory Capture Module runs in the hypervisor and intercepts VM‑exit events to obtain periodic snapshots of the guest’s physical memory. It accounts for address‑space layout randomization (KASLR) and dynamically translates guest physical addresses to host‑visible frames, ensuring that the captured data accurately reflects the current state of the kernel. The Semantic Introspection Engine parses each snapshot to reconstruct core Windows kernel structures such as EPROCESS, KTHREAD, DRIVER_OBJECT, and the System Service Dispatch Table (SSDT). Rather than relying on hard‑coded offsets, HyBIS employs a dynamic offset‑discovery algorithm that extracts the layout of these structures at runtime, thereby supporting Windows 8.x, Windows 10 (including the 64‑bit editions) and Windows Server 2016. This semantic approach enables the system to identify hidden processes, injected code sections, and rogue drivers that would evade raw‑byte pattern matching.
The Response & Mitigation Module closes the loop by taking concrete actions when malicious artifacts are detected. It can isolate a compromised process, remove a malicious driver from the kernel’s module list, or change the protection attributes of the memory pages that contain the offending code, effectively disabling the malware without requiring a guest‑side agent. This “malware disabling” capability is a distinctive feature of HyBIS, as it directly manipulates the guest’s memory from the hypervisor level, guaranteeing that the malicious payload cannot re‑activate.
A prototype was built on the Xen hypervisor and evaluated against a representative set of threats, including well‑known kernel rootkits (Stuxnet, Duqu, Turla) and modern user‑mode malware families (Emotet, TrickBot). In all cases HyBIS achieved 100 % detection with a false‑positive rate below 1 %. Performance measurements showed that taking memory snapshots every 500 ms incurred an average CPU overhead of only 4.2 % on the host, and the latency introduced to guest I/O operations was negligible. Compared with prior VMI frameworks, HyBIS demonstrated superior detection accuracy, broader OS version coverage, and lower runtime cost.
The discussion acknowledges several limitations. The dynamic offset extraction must be re‑executed after major kernel updates, which could delay deployment in fast‑moving enterprise environments. Highly customized drivers or heavily obfuscated malware may still generate false positives, and the hypervisor itself remains a high‑value attack surface; thus, hardening the hypervisor and performing regular integrity checks are essential complementary measures.
In conclusion, HyBIS represents a practical and effective approach to securing Windows virtual machines by combining low‑overhead memory capture, semantic kernel introspection, and proactive mitigation. Future work will focus on automating offset updates, extending the framework to handle multiple concurrent VMs, and integrating the solution into cloud‑scale orchestration platforms to provide continuous, agent‑less protection for large‑scale Windows deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment