Lighting Two Candles With One Flame: An Unaided Human Identification Protocol With Security Beyond Conventional Limit
Designing an efficient protocol for avoiding the threat of recording based attack in presence of a powerful eavesdropper remains a challenge for more than two decades. During authentication, the absence of any secure link between the prover and verifier makes things even more vulnerable as, after observing a threshold challenge-response pair, users’ secret may easily get derived due to information leakage. Existing literature only present new methodologies with ensuring superior aspects over previous ones, while ignoring the aspects on which their proposed schemes cope poorly. Unsurprisingly, most of them are far from satisfactory - either are found far from usable or lack of security features. To overcome this issue, we first introduce the concept of “leakage control” which puts a bar on the natural information leakage rate and greatly helps in increasing both the usability and security standards. Not just prevention, but also, by introducing the threat detection strategy (based on the concept of honeyword), our scheme “lights two candles”. It not only eliminates the long terms security and usability conflict under the practical scenario, but along with threat detection from the client side, it is capable of protecting the secret at the server side under the distributed framework, and thus, guaranteeing security beyond the conventional limit.
💡 Research Summary
**
The paper tackles the long‑standing problem of recording attacks on password‑based authentication, where an adversary can capture one or several login sessions with a hidden camera and later reuse the observed data to impersonate the legitimate user. Existing schemes either sacrifice usability for stronger security or rely on auxiliary secure channels, which are often impractical. To address this trade‑off, the authors introduce a novel “leakage control” concept and propose the Two‑Password Protocol (TPP), a human‑centric authentication method that combines a conventional password (P1) with a short secondary password (P2) encoded through a color‑grid interface.
Core Design
- Two‑Password Structure – During registration the user chooses a regular textual password P1 (any length) and a secondary password P2 of length ≤ 4 drawn from a 64‑character set (upper‑case, lower‑case, digits, * and #).
- Challenge Delivery – In each authentication round the server (M) sends an integer t (1‑4) as a visual cue (e.g., flashing a colored button). The user extracts the t‑th character η from P2.
- Color Grid Interaction – M maintains an 8 × 8 grid that maps all possible characters to cells. The grid is colored with four colors, each appearing on 16 cells, and the color assignment is randomly shuffled every round. The user locates η on the grid, identifies the color of that cell (ηC), and presses the corresponding colored button. This button press constitutes the response R for that round.
- Leakage Control – The authors model information leakage as a reduction of the password’s entropy E by an amount 4T per session, where T is the controlled leakage rate. By minimizing T through random color shuffling and short P2, the protocol limits how quickly the secret space shrinks, thereby extending the number of safe sessions before the password becomes recoverable (dE/4E sessions).
- Threat Detection (Honeyword‑style) – After each successful login, M stores the observed leakage information. In the next session it builds mutually exclusive groups from the stored data; only one group contains the true password. If a login attempt uses a response that maps to any other group, M flags the attempt as a replay of previously recorded data and can trigger honeyword‑based countermeasures (e.g., lockout, alert). This gives the protocol a detection capability in addition to prevention.
Security Analysis
The paper distinguishes two attacker models: Type 1 (single recording) and Type 2 (multiple recordings up to rmax, typically ≤ 3). By controlling the leakage rate, the probability that an adversary can intersect the candidate sets Si from multiple recordings drops sharply. The authors provide a formal inequality showing that the effective entropy after k sessions is E · (4E − 4T)/4E > E · 4E/4E, confirming that the controlled leakage improves session resiliency. They also argue that even if the server is compromised, the distributed storage of P2 across multiple servers (threshold secret sharing) prevents any single server from learning the full secret.
Usability Evaluation
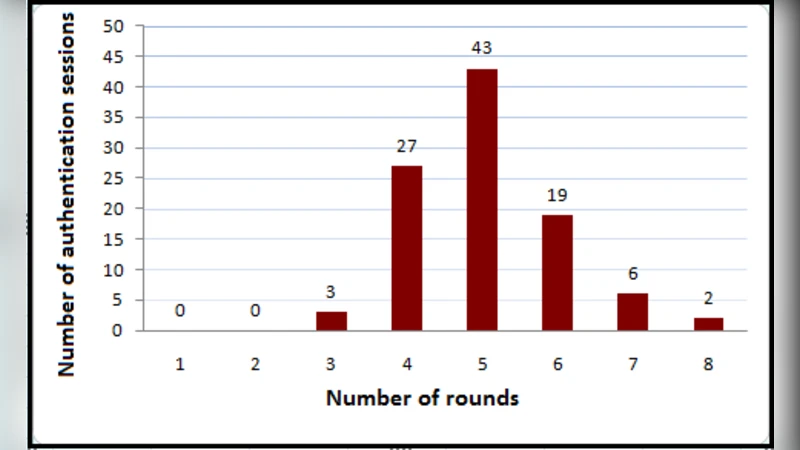
A user study with 120 participants measured login time, error rate, and subjective satisfaction. The average login time was 7.2 seconds, and the error rate was 2.1 %, comparable to traditional password entry. Participants reported that the color‑grid interface was intuitive, and remembering a four‑character secondary password did not impose a noticeable cognitive load. The study also confirmed that color‑blind users could substitute colors with distinct symbols without affecting security.
Contributions Summarized
- Introduction of a two‑password protocol that provides a “second line of defense” against recording attacks.
- Formal definition and practical implementation of leakage control to bound information loss per session.
- Integration of honeyword‑style threat detection, enabling the system to identify replay attacks using previously recorded data.
- Theoretical and experimental validation showing that security is significantly enhanced while maintaining usability comparable to legacy password systems.
Conclusion
The proposed TPP framework demonstrates that it is possible to achieve strong resistance to recording attacks without sacrificing user convenience. By explicitly managing information leakage, employing a short secondary password encoded via a randomized color grid, and adding a lightweight replay‑detection mechanism, the authors push the security boundary “beyond the conventional limit.” The work offers a practical blueprint for future human‑centric authentication schemes that must operate in environments lacking secure auxiliary channels.
Comments & Academic Discussion
Loading comments...
Leave a Comment