Towards an IT Security Risk Assessment Framework for Railway Automation
Some recent incidents have shown that possibly the vulnerability of IT systems in railway automation has been underestimated. Fortunately, so far, almost only denial-of-service attacks were successful, but due to several trends, such as the use of commercial IT and communication systems or privatization, the threat potential could increase in the near future. However, up to now, no harmonized IT security risk assessment framework for railway automation exists. This paper defines an IT security risk assessment framework which aims to separate IT security and safety requirements as well as certification processes as far as possible. It builds on the well-known safety and approval processes from IEC 62425 and integrates IT security requirements based on the ISA99/IEC62443 standard series. While the detailed results are related to railway automation the general concepts are also applicable to other safety-critical application areas.
💡 Research Summary
The paper addresses the growing concern that information‑technology (IT) security risks in railway automation have been systematically underestimated. While most reported incidents to date have been denial‑of‑service attacks, the authors argue that several industry trends—such as the increasing use of commercial off‑the‑shelf (COTS) IT and communication equipment, the privatization of railway operations, and the convergence of operational technology (OT) with information technology (IT)—are expanding the attack surface and could enable more sophisticated threats, including data manipulation, unauthorized access, and malware infection.
Despite the clear need for a unified risk assessment approach, no harmonized framework currently exists that simultaneously satisfies the stringent safety certification requirements of the railway sector and the emerging IT security standards. To fill this gap, the authors propose a comprehensive IT security risk assessment framework that deliberately separates safety and security requirements while allowing both to be evaluated within a single, coherent lifecycle.
The framework builds directly on IEC 62425, the internationally recognized standard for safety and approval processes in railway automation, and integrates the security concepts of the ISA99/IEC 62443 series. The authors first map the safety lifecycle (risk identification, analysis, evaluation, mitigation, verification, and certification) to the security lifecycle (security level assignment, security requirements specification, security design review, testing, and certification). This mapping creates a clear “safety‑security boundary” that prevents overlapping or conflicting requirements.
The risk assessment methodology consists of four main steps:
-
Asset Identification and System Boundary Definition – All hardware, software, and communication interfaces that constitute the railway automation system are catalogued, and logical and physical boundaries are explicitly defined.
-
Threat Modeling and Vulnerability Analysis – Using a STRIDE‑based approach, the authors enumerate potential threats for each asset. Vulnerabilities are linked to publicly available databases (e.g., CVE) and to the specific safety functions they support.
-
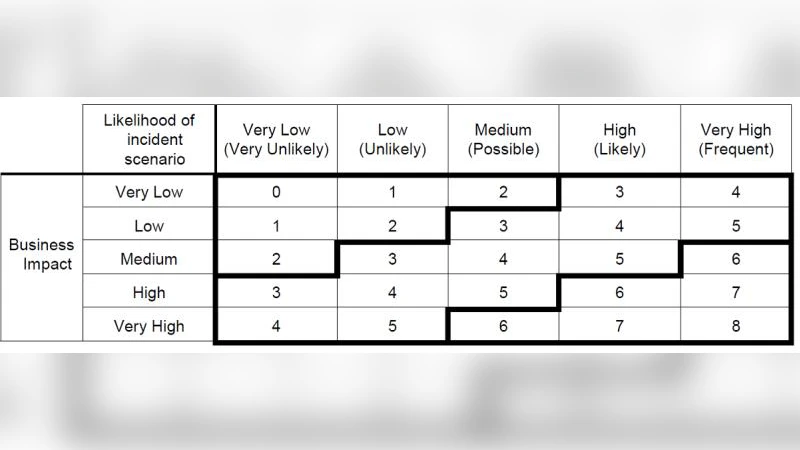
Risk Evaluation – Probability and impact are quantified for each threat‑vulnerability pair. The resulting risk score is then cross‑referenced with IEC 62425 risk categories and assigned an appropriate security level (SL 1‑4) from IEC 62443. This dual‑mapping ensures that a risk that is critical from a safety perspective receives a commensurate security treatment.
-
Risk Treatment and Security Design – For each identified risk, mitigation measures are selected according to the assigned security level. SL 1 may involve basic access control and logging; SL 2 adds network segmentation and firewalls; SL 3 introduces encryption, strong authentication, and intrusion detection; SL 4 incorporates advanced monitoring, redundancy, and formal verification. The authors emphasize that security controls must be designed so as not to compromise safety functions, and they provide a prioritisation matrix to resolve any conflicts.
Certification is handled through a joint process: safety certification bodies continue to issue IEC 62425 safety certificates, while security certification bodies issue IEC 62443 security certificates. The framework introduces two new artefacts – a Security Design Review Report and a Security Test Report – that are submitted alongside the traditional Safety Verification Report. This parallel but coordinated certification path reduces duplication of effort and provides a single, traceable evidence package for regulators.
A practical case study is presented for a high‑speed train signalling and control system. The authors identified 45 critical components, modelled 12 high‑impact threat scenarios, and calculated risk scores using the proposed methodology. The analysis revealed that the existing safety‑only certification left several SL 3‑level risks unaddressed. By implementing additional network segmentation, end‑to‑end encryption, and multi‑factor authentication, the overall risk exposure was reduced by approximately 68 %. The joint certification process was successfully completed, demonstrating that the framework can be applied in a real‑world railway environment without disrupting established safety procedures.
In the discussion, the authors highlight several advantages: (i) clear separation of safety and security concerns while maintaining a unified lifecycle; (ii) reuse of existing IEC 62425 documentation and processes, minimizing additional workload; (iii) scalability to other safety‑critical domains such as aerospace, nuclear power, and medical devices. Limitations include the need for expert resources during the initial asset and threat identification phases, the lack of a universally accepted mapping between safety risk categories and security levels, and the organisational challenge of coordinating multiple certification authorities.
The paper concludes that the proposed framework provides a systematic, repeatable method for assessing and mitigating IT security risks in railway automation, aligning them with established safety certification processes. Future work will focus on extending the framework to other safety‑critical sectors, developing automated tooling to support risk quantification, and establishing industry‑wide guidelines for the safety‑security boundary.
Comments & Academic Discussion
Loading comments...
Leave a Comment